dbsecurity
Transcript of dbsecurity

Database Security
Database SecurityKennesaw State University

Database Security
Overview
1) Introduction2) DB Security Plan3) Database Access Control4) DBMS Security: Patching5) DB Application: SQL injection, Inference
Threats6) Virtual Private Databases7) Oracle Label Security8) Inference Threats9) Encryption10) Auditing11) Datawarehouse12) Security Animations

Database Security
1) Introduction - Motivation
• “Securing the DB may be the single biggest action an organization can take to protect its assets”
David C. Knox“Effective Oracle Database 10g Security by
Design”, McGraw Hill, 2004.ISBN 0-07-223130-0

Database Security
• Database system security must worry about DB + … – Secure Database– Secure applications – Secure DBMS– Secure operating system in relation to
database system– Secure web server in relation to
database system– Secure network environment in relation
to database system
1) Introduction - Scope

Database Security
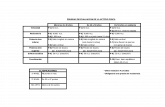
AUTHOR TEXT Publisher ISBN
Natan, Ron Ben2005
Implementing Database Security and Auditing
Elsevier Digital Press
1-5558-334-2
Afyouni, Hassan A., (2006)
Database Security and Auditing
Thompson Course Technology
0-619-21559-3
Knox, David (2004)
Effective Oracle Database 10g Security by Design
Oracle Press 0072231300
1) Introduction - Literature

Database Security
1) Introduction – Product Specific Books
• Oracle Advanced Security (previously Advanced Network Option), contains network encryption tools. Depending on the version of Oracle, it is available for no extra cost. It is for the enterprise edition.
• Best literature for OAS is Oracle Security Handbook by Marlene Theriault and Aaron Newman, McGraw-Hill.

Database Security
2) DB Security Plan
http://www.oreilly.com/catalog/orasec/chapter/ch07.html

Database Security
Which is the most complex program/form to implement?If a data type is changed in the Customers table, what programs/forms may need
modification?The Orders form accesses how many tables?
The Employees table is accessed by how many programs/forms?
2) DB Security Plan

Database Security
• DAC Versus MAC• Access Matrix Model:
Harrison-Ruzzo-Ullman– Authorized state: Q
= (S, O, A)– Conditions
(dependent)• Data• Time• Context• History
O1 Oj Om
S1 A[S1,O1] A[S1,Oj] A[S1,Om]
Si A[Si,O1] A[Si,Oj] A[Si,Om]
Sn A[Sn,O1] A[Sn,Oj] A[Sn,Om]
Subjects Objects
2) DB Security Plan

Database Security
2) DB Security Plan - Document User Administration
• Part of the administration process• Reasons to document:
– Provide a paper trail– Ensure administration consistency
• What to document:– Administration policies, staff and
management– Security procedures– Procedure implementation scripts or
programs– Predefined roles description

Database Security
3) DB Access Control
• Default Users and Passwords– Users, Passwords
• Default users/passwords– sys, system accounts – privileged, change default
password– Sa (MS-SQL Server)– scott account – well-known account/password,
change it- general password policies (length, domain,
changing, protection)• People Having too many privileges
– Privileges, Roles, Grant/Revoke• Privileges
– System - actions– Objects – data
• Roles (pre-defined and user-defined role)– Collections of system privileges (example: DBA role)
• Grant / Revoke– Giving (removing ) privileges or roles to (from) users

Database Security
3) DB Access Control - Default Passwords
• Easiest way to log into an Oracle database is to use a default account with a known password [Finnigin]
• http://www.petefinnigan.com/default/default_password_checker.htm
• This site has scripts that will identify all default users and lets you know if they still have their default passwords. You may download these scripts.

Database Security
3) DB Access Control - Password Cracking
• At http://www.toolcrypt.org/index.html there are tools that you can download to crack the passwords. You need to verify this against the DB, because you can be sure that the hacker has these tools.

Database Security
3) DB Access Control - Find all Privileges
• http://www.petefinnigan.com/find_all_privs.sql
• Script to find which privileges have been granted to a particular user. This scripts lists ROLES, SYSTEM privileges and object privileges granted to a user. If a ROLE is found -- then it is checked recursively.
• Output can be directed to the screen or to a file.

Database Security
3) DB Access Control - Check for DBA Role

Database Security
3) DB Access Control - How are privileges granted
• DBMS like Oracle has pre-defined roles (ex: DBA)
• You may also have user defined roles
Example1) Create Role AcctDept;2) Grant Select, Update on Orders to
AcctDept;3) Grant AcctDept to Smith, Jones;4) Grant DBA to Smith;
Grant all privileges on Orders to Smith;Grant select on Orders to Public;Revoke delete on Orders from smith;

Database Security
3) DB Access Control - Disable Account
CREATE USER smith identified by s9 default tablespace users;
ALTER USER scott ACCOUNT LOCK -- lock a user account
ALTER USER scott ACCOUNT UNLOCK; ALTER USER scott PASSWORD EXPIRE; -- Force new
pwd

Database Security
3) DB Access Control - Launch OEM
• Choose stand-alone for personal Oracle and login to oracle using a dba user/password

Database Security
3) DB Access Control - Connect to a Database
• On the left side of the screen, double click Network and then Databases to connect to the database you want o manage.

Database Security
3) DB Access Control - Maintain User Accounts
• Once you login, you may create users, roles and profiles as well as granting privileges to them through a GUI interface.

Database Security
3) DB Access Control - Profiles
• PROFILE clause: indicates the profile used for limiting database resources and enforcing password policies. Example:
• CREATE PROFILE app_user LIMIT SESSIONS_PER_USER UNLIMITED CPU_PER_SESSION UNLIMITED CPU_PER_CALL 3000 CONNECT_TIME 45 LOGICAL_READS_PER_SESSION DEFAULT LOGICAL_READS_PER_CALL 1000 PRIVATE_SGA 15K COMPOSITE_LIMIT 5000000;
• CREATE USER sidney IDENTIFIED BY out_standing1
DEFAULT TABLESPACE demo QUOTA 10M ON demo TEMPORARY TABLESPACE temp QUOTA 5M ON system PROFILE app_user PASSWORD EXPIRE;

Database Security
3) DB Access Control - Security MS-Access
• Two methods for securing a database:– set password to open
a database (system security);
– user-level security, to limit the parts of the database that a user can read or update (data security).

Database Security
3) DB Access Control - System Level: Open Exclusive

Database Security
3) DB Access Control - System Level Security (cont.)
DBA Sets password User is prompted every time he/she
opens the DB

Database Security
3) DB Access Control - MS-Access: User Level

Database Security
4) SECURE THE DBMS (Patch)
• Possible Holes in DBMS– http://technet.oracle.com/deploy/
security/alerts.htm (50+ listed)– Buffer overflow problems in DBMS code– Miscellaneous attacks (Denial of Service,
source code disclosure of JSPs, others)• Need for continual patching of DBMS
– Cost of not patchingWorms, virus, etc. SQL
slammer worm

Database Security
5) DB Applications
• “75 percent of hacks happen at the application” – Gartner “Security at the Application Level”.
• “The main battlefield between hackers and security professionals have moved from the network layer to the web applications”
Eric Marvets, “Microsoft Security Summit”, April 13, 2006, Atlanta, Georgia

Database Security
5) DB Applications - SQL Injection
• Web Application where1) User inputs text into a textbox2) Text used to build SQL Query dynamically3) Malicious input changes the nature of the queryExample: user inputs names into textbox
Name: Benjamin Franklin ' OR 1=1;SqlStr = “SELECT * FROM EMPLOYEE WHERE EMPLOYEE.Name = ” +
userInput
SqlStr = SELECT * FROM EMPLOYEEWHERE EMPLOYEE.Name =
'Benjamin Franklin' OR 1 = 1;
–Result: every row of the EMPLOYEE table will be returned

Database Security
SQL Injection - Solution
• Similar to Buffer overflow:validate user input.

Database Security
6) Virtual Private Databases
• May be implemented through Views in most DBMS
• In Oracle, you may create a policy that will be fired when an operation (Insert, Update, etc.) is performed by a certain user on a certain object.

Database Security
6) VPD, Example of Row Level Security w/ Views

Database Security
6) VPD with a Policy

Database SecurityVirtual Private Database Technology
USERSecurityPolicy
Where
Table
Predicate
Package
Step 1 Step 2
Step 3
Step 4
Step 5
Data access via Virtual Private Database will perform the following five steps:
1. User sends SQL to the database server.2. The associated table triggers a pre-defined security policy.3. The security policy returns a predicate.4. The SQL statement is modified according to the security policy.5. Secured data returns to user.
Virtual Private Database Technology
USERSecurityPolicy
Where
Table
Predicate
Package
Step 1 Step 2
Step 3
Step 4
Step 5
Data access via Virtual Private Database will perform the following five steps:
1. User sends SQL to the database server.2. The associated table triggers a pre-defined security policy.3. The security policy returns a predicate.4. The SQL statement is modified according to the security policy.5. Secured data returns to user.
http://bgoug.org/seminar-Velingrad-oct-2005/Presentations/Presentation_OLS.ppt

Database Security
6) VPD - Grant Execute on DBMS_RLS
• CONNECT TO ORACLE AS SYSDBA
SQL> connect sys as sysdbaEnter password: ******Connected.
SYSDBA creates a user called SECMAN (Security manager)
SQL> create user secman identified by s default tablespace users;
SYSDBA GRANTS EXECUTE ON DBMS_RLS TO SECMAN so this user can create the VPD
SQL> grant dba to secman;SQL> grant execute on dbms_rls to secman;
CONNECT AS SECMANSQL> connect secman/s;

Database Security
VPD - Definition
Ex.: SELECT * FROM Emp; -- becomes SELECT * FROM Emp where Emp.Name = User;

Database SecurityVirtual Private Database Technology
A VPD security model uses the Oracle dbms_rls package (RLS stands for row-level security) to implement the security policies and application contexts. This requires a policy that is defined to control access to tables and rows
http://bgoug.org/seminar-Velingrad-oct-2005/Presentations/Presentation_OLS.ppt

Database Security
6) VPD – Update Example
UPDATE mn668b14.Employees set ext = 777;1 row updated.
Connecting Policy, Table and Function

Database Security
6) VPD - Security Policy
-- create security policy BEGIN DBMS_RLS.drop_policy (object_schema => 'MN668B14', object_name => ' EmployeeUpdateOrderView', policy_name => 'EMP_UPDATE_ORDERS_POLICY'); END; BEGIN dbms_rls.add_policy ( object_schema => 'MN668B14', object_name => ' EmployeeUpdateOrderView ', policy_name => 'EMP_ORDERS_UPDATE__POLICY’, function_schema => 'MN668B14', policy_function => 'EMPUSER_ONLY', statement_types => 'SELECT,UPDATE,INSERT,DELETE', update_check => TRUE ); END;

Database Security
6) VPD - Summary
• VPD security provides a new way to control access to Oracle data.
• One Schema, several virtual schemas.
• Dynamic nature of a VPD. At runtime, DBMS modifies SQL statement to add security.
Burleson, Donald (2003), "Establish security policy with Oracle virtual private database",
http://www.dba-oracle.com/art_builder_vpd.htm

Database Security
7) Oracle Label Security (OLS)
• simulates multilevel db.
• Adds a field for each row to store the row’s sensitive label.
• Access is granted (or denied) comparing user’s identity and security clearance label with row’s sensitive label.

Database Security
7) OLS and Multilevel Security
• Information has different classifications• Users have different security clearances
• Purpose: separate data based on its classification
• Mandatory Access Control (MAC): security enforced by system and not by the user.
• Polyinstantiation: multiple rows with same PK. Instances distinguished by security level.

Database Security
7) Problem with Multilevel Security
• It is really multiple instantiations of single-level DBMS, which strongly degrades performance.
• Examples: Trusted Oracle, DB2 for z/OS, Informix OnLine/Secure, Sybase secure system

Database Security
7) Oracle Label Security:
• simulates multilevel db.
• Adds a field for each row to store the row’s sensitive label.
• Access is granted (or denied) comparing user’s identity and security clearance label with row’s sensitive label.
• Label contains LEVEL, GROUP and COMPARTMENT

Database Security
7) OLS & VPD
• Like VPD, OLS creates Policies
• A policy is a name that associates labels, rules, and authorizations.
• DBA defines a set of labels for data and users, along with authorizations for users and program units, that defines all access to objects.

Database Security
7) OLS LABEL has 3 Components
• level : mandatory, simple hierarchy• compartment optional, non-hierarchical • group optional, tree level hierarchy
• OLS compares the user security clearance with the sensitivity label assigned to the data.
• IF a label contains all 3 components, THENthe security clearance of the user >= the data sensitivity level, contain all compartments and at least one group.

Database Security
7) OLS - More on 3 components
• label has 3 components:
• a single level (sensitivity) ranking
• zero or more horizontal compartments
• zero or more hierarchical groups

Database Security
7) OLS – Column added
• When an Oracle Label Security policy, a column is added to the table that is protected by the policy. This policy label column contains the label information for each data row.
• DBA can choose to display or hide this column

Database Security
7) OLS - Levels

Database Security
7) OLS - Compartments

Database Security
7) OLS - Groups

Database Security
7) OLS & VPD
• FGAC = Fine Grained Access Control (A mechanism to implement Row level security in Oracle Database)
• OLS and VPD are the utilities which are used for FGAC.
• OLS: GUI tool
• ROW LEVEL SECURITY
• COLUMN LEVEL SECUITY in Oracle 9i, neither. use views. in Oracle 10g you can o column masking with VPD, but not with OLS.

Database Security
7) OLS Conclusion
• Built on top of VPD• Higher Level, more refined than VPD• Built around Row Level Security, Not much
for Column Level Security

Database Security
8) Inference Threat

Database Security
9) Encryption: overview
• Encrypting Data-in-transitAs it is transmitted between client-
server• Encrypting Data-at-rest
Storing data in the database as encrypted
Encrypting of Data is another layer of security (security in depth). It does not substitute other DB security techniques such as strong password.

Database Security
9) Encrypting Data-in-transit
For a Hacker to eavesdrop on a conversation and steal data, two things may occur1) Physically tap into the communications between
the db client & the db server2) Hacker must understand the communication stream in order to extract sensitive data.
In order to do this, what does the Hacker need ?

Database Security
Tools for packet sniffing
the Hacker needs to have • With a minimum understanding of TCP/IP +• Use one of many network protocol analyzer
that are freely available.
• Packet (formatted block of data transmitted by a Network).
• Sniffing: capturing and analyzing package(like dog sniffing).

Database Security
Minimum Understanding of TCP/IP
• Network Security book.Example: Roberta Bragg, Mark Rhodes-Ousley and Keith
Strassberg, Network Security; The Complete Reference.
• TCP/IP is well documented all over the web.
• Documentation describes the headers of the packet.

Database Security
9) Encryption - Where to run Network Analyzer Packet ?
• Client Machine that has access to the Database server
• Database Server

Database Security
Network Protocol Analyzer: examples
• Tcpdump: utility available as part of installation on most UNIX systems. Can be downloaded from http://www.tcpdump.org
• (windump). Windows counterpart. Available on some systems. Can be downloaded from http://windump.polito.it
• Wireshark (http://www.wireshark.org/download.html):world’s most famous NP Analyzer. Formerly Ethereal (www.ethereal.com).

Database Security
Implement Encryption,data-in-transit
Fortunately there are also many encryption techniques for data in transit:
• Database-specific features such as Oracle Advanced Security
• Connection-based metods (such as SSL)
• Secure tunnels (such as SSH)
• Relying on the operating Systems (IPSec Encryption)

Database Security
Secure Socket Layer (SSL)
• cryptographic protocols that provide secure communications on the Internet for such things as web browsing, e-mail, Internet faxing, instant messaging and other data transfers.
• You may enable SSL from within a DBMS.
• SQL-Server for example: Programs -> Microsoft SQL Server -> Server Network Utility, check the Force protocol Encryption checkbox. Then Stop and start SQL Server.
• Server also must be informed how it will derive encryption keys
• Note: make sure that your version of SSL is compatible with your version of MySQL (like in ODBC or JDBC).

Database Security
SSH Tunnels
• SSH used in many applications. Example: Substitute for FTP with encryption.
• From most DBMSs, you can set up SSH tunnels to encrypt database traffic by port forwarding (Encrypted session between client and server).
• Example: to connect Linux client machine of IP CCC.CCC.C.CCC to a MySQL instance installed on a server with IP address of SSS.SSS.S.SS listening in on port 3306 (default MySQL port).
• Ssh –L 1000:localhost:3306 SSS.SSS.S.SS –l mylogin –I ~/ .ssh id –N -g
• -L=port forwarding, Any connection attempted on port 1000 on the local machine should be forwarded to port 3306 on the server. Therefore any connection on port 1000 will go through encryption.

Database Security
IPSec
• Another Infrastructure option that protects the DB with encryption tools.
• IPSec is done by the OS so you need to encrypt all communications (can’t be selective).
• It operates at layer 3 of the OSI network (lower level).
Installing IPSec on Windows/XP• install IP Security Policy manager. Then from
Control Panel -> Administrative Tools, select IPSec

Database Security
Encrypting Data-at-rest
• There are two reasons to do this
– Protect it from DBAs.
– Protect from File or Disk Theft.

Database Security
Encrypting Data-at-rest
• Encrypting at Application LayerMust do it at multiple locations from within app.
Data can only be used from within application
• Encrypting at File System/Operating System Layerless flexible. Requires you to encrypt everything.
Performance degradesWeak for handling Disk Theft problem.
• Encrypting within Database– Usually, most practical option

Database Security
Encrypting at Application Layer
• Application Developers use a cryptographic library to encrypt such as Java Cryptographic Extensions (JCE) – set of APIs in the java.security and java.crypto packages

Database Security
Encryption at OS layer
• Windows implements the Encrypted File System (EFS) and you can use it for MS-SQL Server.
• Disadvantages ?

Database Security
Encryption within Database
• SQL Server 2005 you can access WindowsCryptoAPI through DB_ENCRYPT and DB_DECRYPT within T-SQL (similar to PL/SQL)
Can use DES, Triple DES and AES (symmetric keys)
• In ORACLE, you can access– DBMS_OBFUSCATION_TOOLKIT package
that implements DES and Triple DES

Database Security
Summary
• DB Encryption can be divided into Data-in-transit and Data-at-rest
• Encryption is useful as a last layer of defense (defense in depth). Should never be used as an alternative solution
• Encryption should be used only when needed
• Key Management is Key

Database Security
10) Auditing
• Need to be selective

Database Security
2 main types of auditing:
• Oracle-supplied auditing using AUDIT command. Results go to AUD$
• Trigger-based DML auditing
• Either way, DBA must monitor auditing table.
Auditing examples/scripts: • http://www.securityfocus.com/infocus/1689
• http://www.petefinnigan.com/papers/audit.sql

Database Security
Example of Audit command
• Must have audit system privileges• Only tracks in subsequent user sessions• Creates records in table AUD$ owned by
sys– You don’t query this table, you query
•Views such as DBA_AUDIT_TRAIL
• SQL> AUDIT Delete any table;• SQL> NOAUDIT delete any table;• SQL> AUDIT SELECT TABLE, UPDATE
TABLE; • SQL> AUDIT create session;

Database Security
When to audit
• When should we audit Oracle users ?– Basic set of auditing measures all the
time– Capture user access, use of system
privileges, changes to the db schema (DDL)
If company handles sensitive data (financial market, military, etc.) OR If there are suspicious activities concerning the DB or a user, specific actions should be done.

Database Security
Audit w/ Triggers (generic solution)
• Create a table that will contain audit information
• Create a trigger that inserts a row into the table every time a certain operation is created such as LOGON, LOGOFF, CREATE TABLE, DELETE, etc.

Database Security
11) Datawarehouses
• Traditionally queried only by upper management
• Encryption has not been an option due to performance implications
• Designed as Open systems, permitting exploratory approach
• Optimization techniques for quick responses

Database Security
Datawarehouse Trends & Problems
• Range of potential users are rapidly increasing• Number of security breaches are rapidly increasing• Legislation is addressing issue to protect personal
information• Statistical Databases and Inferences
User is allowed to see aggregatedata, but not individual rows. With malicious input, user infers the value of individual rows.

Database Security
DB Security Animations
• Adbc.kennesaw.edu -> Advanced Concepts -> Security
Referential IntegritySecurity MatrixRow level SecuritySQL Injection
Database InferenceDatabase Auditing
Encryption

Database Security
End of Lecture
End Of
Today’s
Lecture.