WinZip.ppt
Click here to load reader
-
Upload
technical-dude -
Category
Documents
-
view
1.065 -
download
1
Transcript of WinZip.ppt

ATTACKS ON WINZIP ENCRYPTION
Presenter:Sandhya Turaga

Agenda Introduction WinZip Encryption Architecture Security issues & Possible attacks Fixes to minimize these Attacks

What is WinZip
WinZip is a common compression utility on Microsoft windows machines.
Even though the encryption schemes used in WinZip are very secure, the implementation of these schemes in WinZip encryption makes it vulnerable to many side channel attacks and “man in the middle“ attacks.

WinZip Encryption Architecture
Compresses files using “enhanced deflate” method
Derives AES & HMAC-SHA1 keys from user’s password
Encrypts each of these compressed files using AES encryption scheme in CTR mode

WinZip Encryption Architecture (contd…)
Authenticates the resulting cipher text with HMAC-SHA1 key
Archives into WinZip archive

Possible Attacks
Information Leakage Possible Attacks using Metadata Attacks on filenames and file
extensions

(contd…)Possible Attacks
Protocol rollback attack Archives with encrypted and
unencrypted files Key collision and repeated key
streams Dictionary attacks

Information Leakage
Meta data appears in plain text in the archive
Metadata contains encrypted file’s original file name, length of the original plaintext file, length of the cipher text data

Possible Attacks using Metadata
The unencrypted metadata can give way to “man-in-the-middle” attack
Ex: An attack by changing original length of the file and the compression method
Alice Attacker Bob
Info.zip newInfo.zip

Attacks on filenames and extensions
An attacker can change the filename field of the main file record and central directory record since they both are unauthenticated.
This won’t affect the MAC at the end of the file.

Protocol rollback attack
The encryption utility using AE-2 should also be able to read files encrypted in AE-1.
Hence reads the unencrypted CRC field.
Winzip’s detailed logs contain corrupted CRC and the expected correct CRC.
This log message makes attacker’s life easy.

Archives with encrypted and unencrypted files
Winzip encrypts on a per file basis
The correct password would extract all encrypted and unencrypted files
Any file can be replaced by the attacker

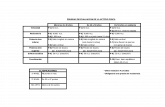
Key collision and repeated key streams
Salt length
Key size Encryption strength field
8 bytes 128 bits 01
12 bytes 192 bits 02
16 bytes 256 bits 03• WinZip takes the password and combines with Salt to generate the AES and HMAC-SHA1keys
• Collision ?

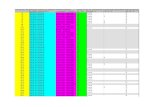
Key collision and repeated key streams (contd…)
Collision probability
64, 32
96, 48
128, 64
0
10
20
30
40
50
60
70
0 20 40 60 80 100 120 140
Salt length in bits
Nu
mb
er
of
En
cry
pti
on
s (
po
wer
of
2)

Dictionary attacks A “Salt” is used to make the exhaustive
search for pass-phrases impossible WinZip uses different salt value to encrypt
each file, thereby increasing probability of collision with limited number of salt values in the attackers dictionary
Ex: Salt length = 8 bytes and files encrypted per password ~ 232 then attacker needs to have 232 different salt values for HMAC-SHA1 dictionary

Fixes We can’t avoid these attacks totally
so we can only minimize the amount of attacks.
Encryption of Metadata Authenticating all the information
that the extractor will use when reconstructing the original data

Fixes (contd…) Diversifying the AES & HMAC-SHA1 keys Authenticating “central directory
records” and “main file records” Increase the salt length & Making the
initialization CTR value random Encrypt the entire “central data
directory records” and remove the metadata information from main file records.

Q/A Any Questions?

References 1. http://
www.winzip.com/aes_info.htm#non-files 2.
www.cse.ucsd.edu/users/tkohno/papers/WinZip/
3. http://www.winzip.com/whatsnew90.htm