The Mobility Challenge - Fran Rosch, SVP Mobility
-
Upload
symantec -
Category
Technology
-
view
121 -
download
3
description
Transcript of The Mobility Challenge - Fran Rosch, SVP Mobility

1
TheMobilityChallenge
Fran RoschSVP, Mobility

Trends Impacting Mobility
2
An App Centric World
Data is Everywhere
User Experience is Paramount
New Platforms,
New Devices
High Speed Networks Increasing (LTE)

Internet of Things
3
Everything is Connected

Innovators Blazing the Path
4
66% of innovators say mobility benefits outweigh mobility risks.
Innovators are achieving revenue objectives...84% of innovators pursue mobility by business drivers.
- Symantec’s 2013 State of Mobility Survey

Problem: Managing Access
5
Mobile Devices ApplicationsData Network
WiFi

6
Problem: Conflicting Views
?User IT Staff
Freedom, Privacy and Productivity
Simple, Secureand Reliable

7
Problem: Data Visibility and Protection
Data LeakageOwnership
Corporate
Personal
Cloud

8
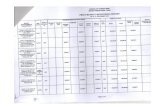
Problem: Malware
67% of enterprises are concerned with malware
attacks spreading from mobile
devices to internal networks
- Symantec 2012 State of Mobility Survey
28%Collect Data
24%Send
Content
7%Change Settings
16%Traditional
Threats
25%Track User
What Mobile Malware Does With Your Phone

9
Problem: Content Delivery
Bandwidth Issues

10
Manage and ProtectData Apps Devices

11
Authentication and Access
PKI
PasswordDirectory
Biometric

Secure Enterprise Store
12

Seamless Coexistence of Corporate and Personal
13
Allow Personal DevicesAccess to Corporate Information, Securely
Auto-configuration of Settings Like Wi-Fi, VPNLock and Wipe Specific Corporate Data Only
Privacy-AddressedNo Device Level Controls
No Monitoring of Device Apps or DataFocus on Corporate Data and Apps Versus Entire
Device
Personal Apps
Personal Data
Corporate Apps
Per-App Policies
Pinpoint Revocation

Secure Data
14
Policies
Deliver Alternative Productivity Solutions
Email Browser Editor File
Sharing

Threat Protection
15
Malware

Secure File Sharing
16
Encrypted and Secure

Implementing a Mobility Strategy
17
Plan for Multiple Use Cases
Provide Device Choice
Design Policies to Protect DataSupport Native User Experience
Single Point of Control

Comprehensive Mobility
18
User & App Access
App & Data
Protection
Device Management
Threat Protection
Secure File Sharing

Mobile Trusted Advisor
19