Surviving the Mobile Phenomenon: Identify At-Risk Mobile Devices Before it is Too Late
-
Upload
ibm-security -
Category
Technology
-
view
944 -
download
0
Transcript of Surviving the Mobile Phenomenon: Identify At-Risk Mobile Devices Before it is Too Late
© 2015 IBM Corporation
Surviving the Mobile Phenomenon: Identify At-Risk Mobile Devices Before it is Too Late
Jason Hardy Worldwide Market Segment Manager, Mobile Security IBM Security Shaked Vax Product Strategist, IBM Trusteer IBM Security
IBM Mobile Security
2 © 2015 IBM Corporation
by 2017 Mobile downloads will increase to
268 billion Gartner
by 2016 The number of smartphone users worldwide will surpass
2 billion
eMarketer
Enterprise mobile trends
“Enterprise mobility will continue to be one of the hottest topics in IT, and high on the list of priorities for all CIOs.”
Ovum
“IT organizations will dedicate at least 25% of their software budget to mobile application development, deployment, and management by 2017.”
IDC
3 © 2015 IBM Corporation
387new threats every minute or more than six every second McAfee
As mobile grows, so do security threats
“With the growing penetration of mobile devices in the enterprise, security testing and protection of mobile applications and data become mandatory.”
Gartner
“Enterprise mobility… new systems of engagement. These new systems help firms empower their customers, partners,
and employees with context-aware apps and smart products.” Forrester
Arxan
Top mobile devices and apps hacked 97% Android
87% iOS
4 © 2015 IBM Corporation
What concerns does this create for the enterprise?
Source: 2014 Information Security Media Group Survey, “The State of Mobile Security Maturity”
32% are concerned about fraudulent transactions
Only 18% can detect malware / jailbreaks
52% worry about application vulnerabilities
Only 23% have tamper-proofing capabilities
50% are content and data leakage are their top security concern
60% use secure containers for data security
57% say a lost or stolen device is top concern 60% use passcodes for device security
5 © 2015 IBM Corporation
MobileFirst Protect (MaaS360)
AppScan, Arxan, Trusteer M; bile SDK
IBM Mobile Security Framework
AirWatch, MobileIron, Good, Citrix, Microsoft, Mocana
HP Fortify, Veracode, Proguard CA, Oracle, RSA
• Manage multi-OS BYOD environment
• Mitigate risks of lost and compromised devices
• Separate enterprise and personal data
• Enforce compliance with security policies
• Distribute and control enterprise apps
• Build and secure apps and protect them “in the wild”
• Provide secure web, mobile, API access and identify device risk
• Meet authentication ease-of-use expectation
Extend Security Intelligence
• Extend security information and event management (SIEM) to mobile platform • Incorporate mobile log management, anomaly detection, configuration and vulnerability management
Manage Access and Fraud
Safeguard Applications and Data
Secure Content and Collaboration
Protect Devices
6 © 2015 IBM Corporation
IBM Mobile Security Portfolio
IBM Security Access Manager
IBM DataPower
Gateway IBM
BigFix
IBM MobileFirst
Platform
IBM MobileFirst
Protect MaaS360
IBM Security AppScan
Arxan Application Protection
for IBM Solutions
IBM QRadar Security
Intelligence Platform
IBM Security Trusteer
IBM Mobile
Security Services
7 © 2015 IBM Corporation
The mobile security challenge
Mobile malware is increasing
Mobile malware growth in just one year
2012 - 2013 Juniper Mobile Threat Report
614%
Mobile banking adoption rising
Phone users use mobile banking,
up 18% in one year 2014 – Federal Reserve Survey
33%
End users fall victim to mobile attacks
September, 2012
Your smartphone will (eventually) be hacked
March, 2013
‘Millions’ risk fraud and ID theft through mobile
November, 2013
Mobile: The Emerging Fraud Target Attackers Will Shift Their Focus, Expert Says
8 © 2015 IBM Corporation
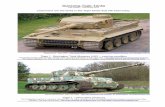
Malware is out there
H1’ 2015 infection rates
Source: Trusteer Mobile Malware Threat Report, July 2015
9 © 2015 IBM Corporation
Infection vector - Fake apps
Over 80,000 users have granted the apps permission
to run on their browser, despite the warning the games
will receive full access to a player’s web activity
12 © 2015 IBM Corporation
Example of underground price list
ITEM PURPOSE PRICE* PRICING MODEL
BOT ADMIN PANNEL
MANAGE A BOTNET $4000 DOWN + $500 MONTHLY FEES
TO RENT
MAZELTOV! MALWARING SPREADING $3000 SERVICE SPYWARE CYBER-ESPIONAGE $7,000 TO OWN BANKIR FINANCIAL INFORMATION
STEALER
$5000 TO OWN
X-iTmo SMS 2FA INTERCEPTOR $715 TO RENT (3 MONTHS)
*Prices In USD. Original prices are in USD or BTC
13 © 2015 IBM Corporation
Infection vectors of iPhones (without JailBreak)
! Apple provides an “Enterprise provisioning” (299$/y, valid credit card, D-U-N-S) ! Distributed mostly via link (email/webpage/SMS) or USB ! Legitimate use
– MDM providers and “alternative markets” to some degree – Other “alternative” markets (Emu4iOS, iNoCydia, …)
! Also used maliciously in APT/targeted attacks
Pop Quiz
Which of the below pop-ups
is legit?
14 © 2015 IBM Corporation
Account Takeover via a Criminal Mobile
Device
Cross-Channel Attacks
Compromised & Vulnerable Devices
Understanding the mobile risk landscape
Susceptible to suspicious apps &
mobile malware
Server-side device ID isn't effective for mobile
device
Credential theft from the desktop enables mobile
fraud
Mobile fraud risk vectors
Customer Criminal
15 © 2015 IBM Corporation
! Advanced Rooted or Jailbroken Devices ! New jailbreak techniques ! Jailbreak and roo:ng evasion
! Mobile Malware ! SMS interceptors ! Overlay aAacks ! Automated malware ! Device Rooters & Data stealers
! Suspicious applica:ons ! Unsecured wi-‐fi access
Detecting Vulnerable & Compromised Devices
16 © 2015 IBM Corporation
Example of mobile malware Real Financial Malware & Ransomware
Installing malicious app as “device admin”
App prevents user from deleting it
17 © 2015 IBM Corporation
Examples of mobile malware Screen Injec<on -‐ SVPENG
Overlay on Russian Bank Login Screen Overlay on Google Play
18 © 2015 IBM Corporation
! Server-side Device ID is not effective for mobile devices
! Mobile devices share many identical attributes ! Mobile devices have the same attributes: OS, browser, fonts etc..
! Cybercriminals can easily trick traditional device ID systems
Account takeover via a Criminal’s Mobile Device
18
Detecting criminal devices
19 © 2015 IBM Corporation
! Cybercriminals convince users to supply mobile phone number to install app on phone via malware or phishing
! Users install fake security applica:on and enter ac:va:on code
! Malware captures all SMS traffic, including OTP and forwards to fraudsters where fraudulent transfers via online and captured OTP need to bypass authen:ca:on
Cross-channel attacks
19
Coordinated attacks across PC and mobile
20 © 2015 IBM Corporation
Example of cross-channel attack
20
Coordinated attacks across PC and mobile
21 © 2015 IBM Corporation
IBM Security Trusteer Mobile Solution set
Backend Website Mob
ile Device
Your Mobile App
Trusteer Mobile SDK
TRX
API
Trusteer Pinpoint Criminal DetecAon
TRX
Cross Channel Risk
Factors
Trusteer Mobile SDK Persistent Device ID Device Risk Factors
• Jailbroken / Rooted Device • Malware Infec:on • Suspicious Geo-‐loca:on • Unpatched OS • Unsecure Wi-‐Fi connec:on • Suspicious Apps • Geo Loca:on • SIM ID • Device Face down
Trusteer Mobile Browser
Trusteer Mobile SDK
Customer-‐ provided Device ID, Risk Data
Customer Risk Engine / Web App
Criminal Device
Database
Customer
22 © 2015 IBM Corporation
Trusteer Mobile SDK
Seamless Authentication and Risk Detection
* Some limitation with iOS
! Persistent client-side device ID ! Geo location ! Malware detection ! Jailbroken/Rooted ! Suspicious applications ! Wi-Fi connection ! OS up-to-date ! SIM ID ! Device Face down
23 © 2015 IBM Corporation
• OS vulnerabilities detected • Unsecure Wi-Fi detected • Device is rooted • Device Face down
Low-risk detected
IBM Trusteer Mobile SDK
Example of access from a low-risk device
Disable Funds Payment Functionality
Mobile Banking App
24 © 2015 IBM Corporation
Unique device ID persistent over app and OS reinstallation
Determines device ID
• MAC • CPU • IMEI
• Battery ID • Chip ID
Example of first-time access
IBM Trusteer Mobile SDK
Mobile Banking App
Requires Out-of-Band Authentication
25 © 2015 IBM Corporation
• Overlay malware detected - svpeng
• Root hider detected
Overlay attack detected
Example of malware attack
25
IBM Trusteer Mobile SDK
Mobile Banking App Block Access
to Application
26 © 2015 IBM Corporation
Developing more secure mobile banking applications
Manage and enforce policy based on risk without customer impact
Control Maintenance Costs
Control Development Costs Time-to-Market Customer
Experience Compliance
Imperatives / Considerations
Allow Access
Authenticate Access
Block Access
Detect risks at the device, application, and session level
Device Risks • Malware infection • Rooted / jailbroken • Suspicious
applications • OS vulnerabilities
• Known criminal device
Application Risks • Application tampering • Fake applications • Overlay attacks
Session Risks • Unsecure Wi-Fi • Unusual geo location
• Eavesdropping • Pharming
27 © 2015 IBM Corporation
The IBM Mobile Banking Security solution
Policy Management and Control
Policy Definitions
Policy Enforcement
Simplified Development
Control Maintenance Costs
Control Development Costs Time-to-Market Customer
Experience Compliance
Imperatives / Considerations
IBM Trusteer Mobile SDK
IBM MobileFirst Foundation
Manage and enforce policy based on risk without customer impact
Detect risks at the device, application, and session level
28 © 2015 IBM Corporation
Fully integrated into the IBM MobileFirst Platform Development Environment
Enforce policy
Send risk Data to server
Device ID persistent over app
and OS
Integrated security library
Analyze risk data
29 © 2015 IBM Corporation
Security U
pdates
Trusteer Mobile Fraud Risk With ISAM Context based Access
Mob
ile D
evic
e
TRX
On / Off Premises Applications and Data
IBM Security Access Manager
TRX
Customer
Risk-based access with unique context from Trusteer including: • Jailbroken /Rooted • Jailbreak Hiders • Persistent Device ID • Malware Infection
• Unpatched OS • Unsecure Wi-Fi • Suspicious Apps
Your Mobile App
Trusteer Mobile SDK
Trusteer
Mobile Browser
Trusteer Mobile SDK
30 © 2015 IBM Corporation
Preventing non-secure browsers from connecting ! Decreasing the risk of malware, customize user experience & no
application changes required ! Simple policy can be authored that directs users to a page notifying them
that a secure browser is required
Mobile Chrome Browser (non-secure)
31 © 2015 IBM Corporation
Mobile malware & high-risk device detection and enforcement
! Reduce the risk of malware collecting sensitive data ! When connecting with registered web applications, Trusteer Mobile
Browser will transmit in the HTTP request details about the connecting mobile device
! IBM Security Access Manager for Mobile will extract the details into a set of context attributes that are ready to be included in a policy
32 © 2015 IBM Corporation
IBM MobileFirst Platform and IBM Trusteer solution highlights
Captures persistent device id and device, user and session risk factors
Comprehensive fraud protection across mobile banking apps
Fully integrated with your IBM MobileFirst Platform Environment formerly known as IBM Worklight
33 © 2015 IBM Corporation
www.ibm.com/security
© Copyright IBM Corporation 2014. All rights reserved. The information contained in these materials is provided for informational purposes only, and is provided AS IS without warranty of any kind, express or implied. IBM shall not be responsible for any damages arising out of the use of, or otherwise related to, these materials. Nothing contained in these materials is intended to, nor shall have the effect of, creating any warranties or representations from IBM or its suppliers or licensors, or altering the terms and conditions of the applicable license agreement governing the use of IBM software. References in these materials to IBM products, programs, or services do not imply that they will be available in all countries in which IBM operates. Product release dates and/or capabilities referenced in these materials may change at any time at IBM’s sole discretion based on market opportunities or other factors, and are not intended to be a commitment to future product or feature availability in any way. IBM, the IBM logo, and other IBM products and services are trademarks of the International Business Machines Corporation, in the United States, other countries or both. Other company, product, or service names may be trademarks or service marks of others.
Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to improper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security approach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM DOES NOT WARRANT THAT ANY SYSTEMS, PRODUCTS OR SERVICES ARE IMMUNE FROM, OR WILL MAKE YOUR ENTERPRISE IMMUNE FROM, THE MALICIOUS OR ILLEGAL CONDUCT OF ANY PARTY