IJART020
-
Upload
vikas-nagare -
Category
Documents
-
view
219 -
download
0
Transcript of IJART020
-
7/29/2019 IJART020
1/5
Available ONLINE www.ijart.org
IJART, Vol. 2 Issue 1, 2012,58-62
ISSN NO: 6602 3127 www.ijart.org Page | 58
ISSN NO: 6602 3127RRREEE SSS EEE AAA RRRCCC HHH AAA RRRTTT III CCC LLL EEE
Jamming Aware Energy Efficient Multicast Routing
In Mobile ADHOC NetworksD.Jayachandran,II ME CSE,The Kavery Engineering College.
A.Prabhu,AP/CSE,The Kavery Engineering College.
ABSTRACT
Multiple-path source routing protocols allow a data source node to distribute the total traffic among available
paths. In this article, we consider the problem of jamming-aware source routing in which the source nodeperforms traffic allocation based on empirical jamming statistics at individual network nodes. We formulate this
traffic allocation as a lossy network flow optimization problem using portfolio selection theory from financial
statistics. We show that in multi-source networks, this centralized optimization problem can be solved using adistributed algorithm based on decomposition in network utility maximization (NUM). We demonstrate the
networks ability to estimate the impact of jamming and incorporate these estimates into the traffic allocation
problem. Finally, we simulate the achievable throughput using our proposed traffic allocation method in severalscenarios.
Index terms: Wireless network, security, routing, node capture attack, HTTPS
1. INTRODUCTIONA mobile Ad hoc network (MANET) is a collection of
autonomous mobile nodes capable of communicatingwith each other via wireless links. Nodes in a
MANET have limited transmission range;
communication is achieved by making use of nodes to
forward packets to other nodes, which thereby have to
operate as routers. Finding a path between two
communication end points in an ad hoc network is
non trivial: node mobility results in highly dynamic
network topologies. These networks are rapidlydeployable, as they do not require any infrastructure
in place. MANETs are highly desirable in a variety of
scenarios: disaster recovery-where the entire
communication infrastructure might have been
destroyed, business meetings- where a group of
people have to share resources and communicate with
each other, communication over rugged terrain
where establishing infrastructure is not cost effective.Ad hoc networks can also be used to deploy
multimedia services; however efficient routing
protocols have to be developed before this can be
realized.The high node mobility, low bandwidth
wireless interfaces, limited battery power and
contention for a shared wireless medium makesdesigning routing protocols for ad hoc networks
difficult; any new routing protocol must take note of
these factors critically.
Several routing protocols have been proposed in ad
hoc networks. But none are proposed with security.
Our project addresses location aided routing with
security.
-
7/29/2019 IJART020
2/5
International Journal of Advanced Research in Technology Vol. 2 Issue 1, March 2012
ISSN NO: 6602 3127 www.ijart.org Page | 59
2. RELATED WORKPAMAS protocol that uses two different channels to
separate data and signaling. The Suresh Singh, Mike
Woo and C.S. Raghavendra presented several power-aware metrics that do result in energy-efficient routes.
The Minimum Total Transmission Power Routing
(MTPR) was initially developed to minimize the total
transmission power consumption of nodes
participating in the acquired route. The Min-Max
Battery Cost Routing (MMBCR) considers the
remaining power of nodes as the metric for acquiring
routes in order to prolong the lifetime of network.
C.K.Toh presented the Conditional Max-Min Battery
Capacity Routing (CMMBCR) protocol, which is a
hybrid protocol that tries to arbitrate between the
MTPR and the MMBCR. The several multipath
proactive routing protocols were developed. These
protocols use table-driven algorithms (link state or
distance vector) to compute multiple routes. But they
do not consider the power aware metrics and these
protocols generate excessive routing overhead andperform poorly because of their proactive nature. The
on-demand routing is the most popular approach in
the MANET. Instead of periodically exchanging route
messages to maintain a permanent route table of the
full topology, the on- demand routing protocols build
routes only when a node needs to send the data
packets to a destination. The standard protocols of this
type are the Dynamic Source Routing (DSR) routing.
However, these protocols do not support multipath.The several multipath on- demand routing protocols
were proposed. Some of the standard protocols are the
Ad hoc On- demand Multipath Distance Vector(AOMDV), the Split Multipath Routing (SMR), the
Multipath Source Routing (MSR) [13], the Ad hoc
On-demand Distance Vector Multipath Routing
(AODVM) and the Node- Disjoint Multipath Routing
(NDMR). These protocols build multiple routes based
on demand but they did not consider the power awaremetrics.
3. MY CONTRIBUTIONSThe allocation of traffic across multiple routing paths.
My contributions to this problem are as follow:
Formulate the problem of allocating traffic
across multiple routing paths in the presence
of jamming as a lossy network flow
optimization problem. We map the
optimization problem to that of asset
allocation using portfolio selection theory[12], [13].
Formulate the centralized traffic allocation
problem for multiple source nodes as a
convex optimization problem.
Show that the multi-source multiple-pathoptimal traffic allocation can be computed at
the source nodes using a distributed
algorithm based on decomposition in
network utility maximization (NUM) [14].
Propose methods which allow individual
network nodes to locally characterize the
jamming impact and aggregate this
information for the source nodes.Demonstrate that the use of portfolio
selection theory allows the data sources tobalance the expected data throughput with
the uncertainty in achievable traffic rates.
4. SYSTEM MODEL AND ASSUMPTIONS4.1 Network Model
The wireless network of interest can be represented by
a directed graph G = (N, E). The vertex set N
represents the network nodes, and an ordered pair (i,
j) of nodes is in the edge set E if and only if node j
can receive packets directly from node i. We assume
that all communication is unicast over the directededges in E, i.e. each packet transmitted by node i ! N
is intended for a unique node j ! N with (i, j) ! E. The
maximum achievable data rate, or capacity, of each
unicast link (i, j) ! E in the absence of jamming is
denoted by the pre predetermined constant rate cij in
units of packets per second. Each source node s in asubset S " N generates data for a single destination
node ds ! N. We assume that each source node s
constructs multiple routing paths to ds using a route
request process similar to those of the DSR [9] or
AODV [10] protocols. We let Ps = {ps1, . . . , ps Ls}
denote the collection of Ls loop-free routing paths for
source s, noting that these paths need not be disjoint
as in MP-DSR [11]. Representing each path ps! by a
subset of directed link set E, the sub-network of
interest to source s is given by the directed subgraph.
5. OPTIMAL JAMMING-AWARETRAFFIC ALLOCATION
In this section, we present an optimization framework
for jamming-aware traffic allocation to multiple
routing paths in Ps for each source node s ! S. Wedevelop a set of constraints imposed on traffic
allocation solutions and then formulate a utilityfunction for optimal traffic allocation by mapping the
problem to that of portfolio selection in finance.
Letting 's! denote the traffic rate allocated to path ps!
by the source node s, the problem of interest is thus
for each source s to determine the optimal Ls1 rate
allocation vector "s subject to network flow capacity
constraints using the available statistics !s and !s of
the end-to-end packet success rates under jamming.
-
7/29/2019 IJART020
3/5
International Journal of Advanced Research in Technology Vol. 2 Issue 1, March 2012
ISSN NO: 6602 3127 www.ijart.org Page | 60
5.1 Traffic Allocation Constraints
In order to define a set of constraints for the multiple-
path traffic allocation problem, we must consider the
source data rate constraints, the link capacity
constraints, and the reduction of traffic flow due to
jamming at intermediate nodes. The traffic rateallocation vector "s is trivially constrained to the
nonnegative orthant, i.e. "s * 0, as traffic rates are
non-negative.
5.2 Optimal Traffic Allocation Using Portfolio
Selection Theory
In order to determine the optimal allocation of traffic
to the paths in Ps, each source s chooses a utility
function Us("s) that evaluates the total data rate, or
throughput, successfully delivered to the destination
node ds. In defining our utility function Us("s), we
present an analogy between traffic allocation torouting paths and allocation of funds to correlated
assets in finance. In Markowitzs portfolio selection
theory [12], [13], an investor is interested in allocating
funds to a set of financial assets that have uncertain
future performance. The expected performance ofeach investment at the time of the initial allocation is
expressed in terms of return and risk. The return on
the asset corresponds to the value of the asset and
measures the growth of the investment. The risk of the
asset corresponds to the variance in the value of the
asset and measures the degree of variation or
uncertainty in the investments growth. Describe the
desired analogy by mapping this allocation of funds tofinancial assets to the allocation of traffic to routing
paths.We relate the expected investment return on the
financial portfolio to the estimated end-to-end successrates !s and the investment risk of the portfolio to the
estimated success rate covariance matrix !s. We note
that the correlation between related assets in the
financial portfolio corresponds to the correlation
between non-disjoint routing paths. The analogy
between financial portfolio selection and theallocation of traffic to routing paths is summarized
below.
6. AODV AND DSDV PROTOCOLIMPLEMENTATION
Wireless networks are characterized by a lack of
infrastructure, and by a random and quickly changing
network topology; thus the need for a robust dynamic
routing protocol that can accommodate such an
environment. To improve the packet delivery ratio of
Destination-Sequenced Distance Vector (DSDV)
routing protocol in mobile ad hoc networks with highmobility, a message exchange scheme for its invalid
route reconstruction is being used. Two protocols
AODV and DSDV simulated using Java simulationpackage and were compared in terms throughput, end
to end delay and packet faction delivery varying
number of nodes, speed and time. Simulation results
show that DSDV compared with AODV, DSDV
routing protocol consumes more bandwidth, because
of the frequent broadcasting of routing updates. While
the AODV is better than DSDV as it doesnt maintain
any routing tables at nodes which results in lessoverhead and more bandwidth. AODV perform better
under high mobility simulations than DSDV. Highmobility results in frequent link failures and the
overhead involved in updating all the nodes with the
new routing information as in DSDV is much more
than that involved AODV, where the routes are
created as and when required. AODV use on -demand
route discovery, but with different routingmechanisms. AODV uses routing tables, one route per
destination, and destination sequence numbers, a
mechanism to prevent loops and to determine
freshness of routes.When a source node wants to send
packets to a destination to which it does not have aroute, it initiates a Route Discovery by broadcasting a
ROUTE REQUEST. The node receiving a ROUTE
REQUEST checks whether it has a route to the
destination in its cache and also check if it is
misbehavior node or not. If it has, it sends a ROUTE
REPLY to the source including a source route, whichis the concatenation of the source route in the ROUTE
REQUEST and the cached route. If the node does not
have a cached route to the destination, it adds its
address to the source route and rebroadcasts the
ROUTE REQUEST. When the destination receives
the ROUTE REQUEST, it sends a ROUTE REPLY
containing the source route to the source. Each nodeforwarding a ROUTE REPLY stores the route starting
from itself to the destination. When the source
receives the ROUTE REPLY, it caches the source
route. If any node not sends acknowledgement then
we easily identified that is misbehavior node. So findout the alternative path and forwarding the data to the
destination.The Message transfer relates with that the
sender node wants to send a message to the
destination node after the path is selected also find out
that node is not a misbehavior node and status of the
destination node through is true. The receiver node
receives the message completely and then it send the
acknowledgement to the sender node also nearbynodes through the router nodes where it is received
the message.
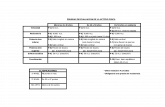
7. Simulation Result and Simulation SetupPlatform Windows XP
Java Sim Jist
Pause time 0, 20, 40, 80, 120, 160,
200
Simulation time 200 s
Number of nodes 50 wireless nodes
Traffic CBR(Constant Bit
Rate)
Simulation Area size 500 x 500 m
Transmission Range 250 m
-
7/29/2019 IJART020
4/5
International Journal of Advanced Research in Technology Vol. 2 Issue 1, March 2012
ISSN NO: 6602 3127 www.ijart.org Page | 61
The following metrics are used in this paper for the
analysis of AODV, DSR and DSDV routing
protocols.
i) Packet Delivery Ratio
ii) Average End to End Delayiii) Throughout
Packet delivery ratio The packet delivery ratio in
this simulation is defined as the ratio between the
number of packets sent by constant bit rate sources
(CBR, application layer) and the number of
received packets by the CBR sink at destination.
Routing Overhead It is the number of packet
generated by routing protocol during the simulation.
Average end-to-end delay of data packets
There are possible delays caused by buffering duringroute discovery latency, queuing at the interface
queue, retransmission delays at the MAC, and
propagation and transfer times. Once the time
difference between every CBR packet sent and
received was recorded, dividing the total time
difference over the total number of CBR packetsreceived gave the average end-to-end delay for the
received packets. This metric describes the packet
delivery time: the lower the end-to-end delay the
better the application performance.
Figure1. Packet delivery ratio versus pause time
for AODV, DSR and DSDV(Number of node = 50,
Area space = 500m x 500m)
Figure2. Routing overhead versus pause time for
AODV, DSR and DSDV (Number of node = 50,
Area space = 500m x 500m)
Figure3. Avg. end to end delay versus pause time
for AODV, DSR and DSDV (Number of node = 50,
Area space = 500m x 500m)
7. CONCLUSION AND FUTURE WORK
In this paper the analysis of adhoc routing protocol is
done in the above mentioned mobility and trafficpattern on different pause time. We analyzed that
when pause time set to 0 each of the routing protocols
obtained around 97% to 99% for packet delivery ratio
except DSDV which obtained 77%. DSR and AODV
reached approx 100% packet delivery ratio when
pause time equal to 200 while DSDV obtained only
approx 94% packet delivery ratio.
DSR and DSDV has low and stable routing overhead
as comparison to AODV that varies a lot. Avg. End to
End delay of DSDV is very high for pause time 0 but
it starts decreasing as pause time increases. DSR
performs well as having low end to end delay. Whenwe compare the three protocols in the analyzed
scenario we found that overall performance of DSR is
better than other two routing protocols.
DSDV routing protocol consumes more bandwidth,
because of the frequent broadcasting of routing
updates. While the AODV is better than DSDV as it
doesnt maintain any routing tables at nodes which
results in less overhead and more bandwidth. From
the above, chapters, it can be assumed that DSDV
routing protocols works better for smaller networksbut not for larger networks. So, my conclusion is that,
AODV routing protocol is best suited for generalmobile ad-hoc networks as it consumes less
bandwidth and lower overhead when compared with
DSDV routing protocol. AODV perform better under
high mobility simulations than DSDV. High mobility
results in frequent link failures and the overhead
involved in updating all the nodes with the new
routing information as in DSDV is much more than
that involved AODV, where the routes are created as
and when required. AODV use on - demand route
discovery, but with different routing mechanics.AODV uses routing tables, one route per destination,
and destination sequence numbers, a mechanism to
prevent loops and to determine freshness of routes.
-
7/29/2019 IJART020
5/5
International Journal of Advanced Research in Technology Vol. 2 Issue 1, March 2012
ISSN NO: 6602 3127 www.ijart.org Page | 62
Future work of this project We present a family of
energy-conserving flooding protocols capable of
supporting both reactive and proactive routing
approaches, as well as network applications that rely
on flooding. Based on realistic simulation models,
these protocols show significant energy-conserving
potential. Future work will focus on methods forbalancing the protocols overhead and relay
optimality to further enhance their efficiency.
8. REFERENCES1] Patrick Tague, Sidharth Nabar, James A. Ritcey,
and Radha Poovendran Jamming-Aware Traffic
Allocation for Multiple-Path Routing Using Portfolio
Selection, IEEE/ACM TRANSACTIONS ON
NETWORKING, VOL. 19, NO. 1, FEB 2011
2] I. F. Akyildiz, X. Wang, and W. Wang, Wireless
mesh networks: A survey, Computer Networks, vol.
47, no. 4, pp. 445487, Mar. 2005.[3] E. M. Sozer, M. Stojanovic, and J. G. Proakis,Underwater acoustic networks, IEEE Journal of
Oceanic Engineering, vol. 25, no. 1, pp. 7283, Jan.
2000.
[4] J. Bellardo and S. Savage, 802.11 denial-of-
service attacks: Real vulnerabilities and practical
solutions, in Proc. USENIX Security Symposium,
Washington, DC, Aug. 2003, pp. 1528.
[5] D. J. Thuente and M. Acharya, Intelligent
jamming in wireless networks with applications to
802.11b and other networks, in Proc. 25th IEEE
Communications Society Military Communications
Conference (MILCOM06), Washington, DC, Oct.2006, pp. 17.
[6] A. D. Wood and J. A. Stankovic, Denial of
service in sensor networks, IEEE Computer, vol. 35,
no. 10, pp. 5462, Oct. 2002.
[7] G. Lin and G. Noubir, On link layer denial of
service in data wireless LANs, WirelessCommunications and Mobile Computing, vol. 5, no.
3, pp. 273284, May 2005.
[8] W. Xu, K. Ma, W. Trappe, and Y. Zhang,
Jamming sensor networks: Attack and defense
strategies, IEEE Network, vol. 20, no. 3, pp. 4147,May/Jun. 2006.
[9] D. B. Johnson, D. A. Maltz, and J. Broch, DSR:The Dynamic Source Routing Protocol for Multihop
Wireless Ad Hoc Networks. Addison- Wesley, 2001,
ch. 5, pp. 139172.
[10] E. M. Royer and C. E. Perkins, Ad hoc on-demand distance vector routing, in Proc. 2nd IEEE
Workshop on mobile Computing Systems and
Applications (WMCSA99), New Orleans, LA, USA,
Feb. 1999, pp. 90100.