Data Link Layer-Megh
-
Upload
nanadithathomas5862 -
Category
Documents
-
view
220 -
download
0
Transcript of Data Link Layer-Megh
-
8/9/2019 Data Link Layer-Megh
1/93
Data Link Layer
-
8/9/2019 Data Link Layer-Megh
2/93
Physical: Describes the transmission of raw bits in terms of
mechanical and electrical issues.
Data Link: Describes how a shared communication channel can
be accessed, and how a data frame can be reliably transmitted.
Network: Describes how routing is to be done. Mostly needed insubnets.
Transport: The hardest one: generally offers connection-oriented
as well as connectionless services, and varying degrees of
reliability. This layer provides the actual network interface to
applications.
Application: Contains the stuff that users see: e-mail, remote
logins, the Webs exchange protocol, etc.
-
8/9/2019 Data Link Layer-Megh
3/93
Fig 1: Simplified representation of the data link andassociated layers
-
8/9/2019 Data Link Layer-Megh
4/93
The overall task of the data link layer is to make
the physical line appear error free to the higherlayers (this is usually called a virtual circuit).
Thus the higher layer of the protocol hierarchy
can pass data down to the lower layers and beable to assume that if the message reaches thedestination it will error free.
-
8/9/2019 Data Link Layer-Megh
5/93
DLLpurpose?
The goal of the data link layeris to provide reliable, efficient communication
between adjacent machines connected by a single
communication channel
1.Group the physical layer bit stream into units calledframes
2. Sender checksums the frame and sends checksumtogether with data. The checksum allows the receiver todetermine when a frame has been damaged in transit.
-
8/9/2019 Data Link Layer-Megh
6/93
3. Receiver recomputes the checksum and comparesit with the received value. If they differ, an errorhas
occurred and the frame is discarded.
4.P
erhaps return a positive or negativeacknowledgment to the sender.
5. Flow control. Prevent a fast sender from
overwhelming a slower receiver.
6. Error control
-
8/9/2019 Data Link Layer-Megh
7/93
P
lacement of DLLPlacement of the data link protocol.
-
8/9/2019 Data Link Layer-Megh
8/93
Routing
The network layer consists of routing
they are connected through point=to-point links
The router would really its packet to be sent
correctly, guaranteed,and in the order it was
issued. It is up to the data link to make unreliable
connections look perfect, or at least, fairly good
-
8/9/2019 Data Link Layer-Megh
9/93
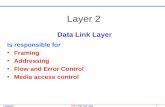
Data Link Layer Design Issues Services Provided to the
Network Layer
Framing
Error Control
Flow Control
-
8/9/2019 Data Link Layer-Megh
10/93
F
unctions of th
e Data Link Layer Provide service interface to the
network layer
Dealing with transmission errors
Regulating data flow
Slow receivers not swamped by fastsenders
-
8/9/2019 Data Link Layer-Megh
11/93
Functions of the Data Link Layer
(2)Relationship between packets and frames.
-
8/9/2019 Data Link Layer-Megh
12/93
Services Provided to Network
Layer(a) Virtual communication.
(b)Actual communication.
-
8/9/2019 Data Link Layer-Megh
13/93
Types of services provided to the
Network Layer
Unacknowledged Connectionless service
Acknowledged Connectionless service
Acknowledged Connection-Orientedservice
-
8/9/2019 Data Link Layer-Megh
14/93
Unacknowledged Connectionless
service
Losses are taken care of at higher layers
No recovering of lost or corrupted frame
Used on reliable medium like coax cables
or optical fiber, where the error rate is low.
Appropriate for voice, where delay is
worse than bad data.
-
8/9/2019 Data Link Layer-Megh
15/93
Acknowledged Connectionless
service
Useful on unreliable medium like wireless.
Acknowledgements add delays.
returns information a frame has safely arrived.
time-out, resend, frames received twice
Adding ack in the DLL rather than in the NL. Leaving it
for the NL is inefficient as a large message (packet) has
to be resent in that case in contrast to small frames here.
-
8/9/2019 Data Link Layer-Megh
16/93
Acknowledged Connection-
oriented service
Most reliable
Established connection before any data is sent.
Guaranteed service
Each frame sent is indeed received
Each frame is received exactly once
Frames are received in order
Special care has to be taken to ensure this in
connectionless services
-
8/9/2019 Data Link Layer-Megh
17/93
Placement of DLL
Placement of the data link protocol.
-
8/9/2019 Data Link Layer-Megh
18/93
Framing
Character Count
Flag bytes with byte stuffing
F
lag bytes with
bit stuffing
Physical layer coding violations
-
8/9/2019 Data Link Layer-Megh
19/93
Framing, character count
Uses a field in the header to specify the number of
characters in the frame when the Data Link Layer at
the destination sees the character count.
It knows how many character follow and hence
where the end of the frame is.
-
8/9/2019 Data Link Layer-Megh
20/93
Problem withFraming with CC
What if the count is garbled.
Even if with checksum, the receiver knows
that the frame is bad there is no way to tellwhere the next frame starts.
Asking for retransmission doesnt help
eith
er because th
e start of th
eretransmitted frame is not known
No longer used
-
8/9/2019 Data Link Layer-Megh
21/93
Byte stuffing or character stuffing.
The senders DLL insert a special escape byte(ESC) just before each accidental flag byte inthe data.
The Data Link Layer on the receiving endremoves the escape byte before the data aregiven to the network layer.
A framing flag byte can be distinguished fromone in the data by the absence or presence ofan escape byte before it.
When an escape byte occurs in the middle ofthe data, it too is stuffed with an escape byte .
-
8/9/2019 Data Link Layer-Megh
22/93
Framing with byte stuffing
(a) A frame delimited by flag bytes.
(b) Four examples of byte sequences
before and after stuffing.
-
8/9/2019 Data Link Layer-Megh
23/93
Framing with byte stuffing
Problem : fixed character size : assumes
character size to be 8 bits : cant handle
heterogeneous environment.
-
8/9/2019 Data Link Layer-Megh
24/93
Framing with bit stuffing
Bit stuffing(a) The original data.
(b) The data as they appear on the line.
(c) The data as they are stored in receivers memoryafter destuffing.
-
8/9/2019 Data Link Layer-Megh
25/93
Encoding Violations:
Send an signal that doesn't conform to any legalbit representation.
In Manchester encoding, for instance, 1-bits
are represented by a high-low sequence, and 0-bits by low-high sequences.
The start/end of a frame could be representedby the signal low-low orhigh-high.
Finally, some systems use a combination of these techniques. IEEE 802.3, for instance, hasboth a length field and special frame start andframe end patterns.
-
8/9/2019 Data Link Layer-Megh
26/93
Error Control
Positive and Negative feedback
Timers : what happens when a frame completelyvanishes : receiver neither sends a +ack nor
ack then timer comes to help.
It may result in a frame being sent more than once
and received more than once :
solution : assign sequence numbers to frames
-
8/9/2019 Data Link Layer-Megh
27/93
Error Control
Error control is concerned with insuring
that all frames are eventually delivered
(possibly in order) to a destination. How?Three items are required.
Acknowledgements:
Timers:
Sequence Numbers:
-
8/9/2019 Data Link Layer-Megh
28/93
Acknowledgements:
The receiver returns a special acknowledgment
(ACK) frame to the sender indicating the correct
receipt of a frame. In some systems, the receiver also returns a
negative acknowledgment (NACK) for
incorrectly-received frames.
It can retransmit a frame right away withoutwaiting for a timer to expire.
-
8/9/2019 Data Link Layer-Megh
29/93
Timer
Retransmission timers are used to resend
frames that don't produce an ACK.
When sending a frame, schedule a timer
to expire at some time after the ACK
should have been returned.
If the timer goes off, retransmit the frame.
-
8/9/2019 Data Link Layer-Megh
30/93
Sequence Numbers
Retransmissions introduce the possibility
of duplicate frames.
It suppress duplicates, add sequence
numbers to each frame.
so that a receiver can distinguish between
new frames and old copies.
-
8/9/2019 Data Link Layer-Megh
31/93
Flow Control
Flow control deals with throttling the speed
of the sender to match that of the receiver.
Usually, this is a dynamic process, as the
receiving speed depends on such
changing factors as the load, and
availability of buffer space.
-
8/9/2019 Data Link Layer-Megh
32/93
Two approaches to prevent the sender from
pumping the frames
Feedback based flow control: the receiver
sends back information to the sender giving it
permission to send more data or at least tellingthe senderhow the receiver is doing.
Rate based flow control: the protocol has a
built-in mechanism that limits the rate at which
senders may transmit data, without usingfeedback from the receiver.
-
8/9/2019 Data Link Layer-Megh
33/93
-
8/9/2019 Data Link Layer-Megh
34/93
Types of errors
1. Single- - bit error
2. Burst error
-
8/9/2019 Data Link Layer-Megh
35/93
Redundancy Check
Shorter group of bits may be appended to
the end of each unit. This technique is
called redundancy .
The extra bits are redundant to the
information; they are discarded as soon as
the accuracy of the transmission has beendetermined.
-
8/9/2019 Data Link Layer-Megh
36/93
1.Parity check:
Add a bit to a bit string such that the total
number of 1-bits is even (or odd).
e.g :(even parity) 1011010 ) 10110100.
(odd parity) 1011010 ) 10110101
-
8/9/2019 Data Link Layer-Megh
37/93
Two-dimensional parity check
1 1 0 0 1 1 1 11 0 1 1 1 0 1 1
0 1 1 1 0 0 1 0
0 1 0 1 0 0 1 10 1 0 1 0 1 0 1
11001111 10111011 01110010 01010011
1100111 1011101 0111001 0101001
-
8/9/2019 Data Link Layer-Megh
38/93
Error detecting code
2.Polynomial code or CRC( Cyclic
Redundancy Check )
-
8/9/2019 Data Link Layer-Megh
39/93
CRC generator and checker
Zero, accept; nonzero, reject
Data CRC
Divisor
Remainder
Sender
Data.. 00...0
Divisor
CRC
Data CRC
Receiver
-
8/9/2019 Data Link Layer-Megh
40/93
-
8/9/2019 Data Link Layer-Megh
41/93
Division
Modulo 2 division can be performed in amanner similar to arithmetic long division.
Subtract the denominator (the bottomnumber) from the leading parts of theenumerator (the top number).
Proceed along the enumerator until itsend is reached. Remember that we areusing modulo 2 subtraction.
-
8/9/2019 Data Link Layer-Megh
42/93
Binary division in a CRC generator
Data=100100=x^2+x^5
Divisor = 1101 =x^0+x^2+x^3
111101
Divisor 1101) 100100000 (data plus extra zeros)1101
1000
1101
1010
1101
11101101
0110
0000
1100
1101
0001 (remainder)
-
8/9/2019 Data Link Layer-Megh
43/93
-
8/9/2019 Data Link Layer-Megh
44/93
A sequence of redundant bits, called the CRC
or the CRC remainder, is appended to the end
of a data unit So that the resulting data unit becomes exactly
divisible by a second, predetermined binary
number.
The redundancy bits used by CRC are derivedby dividing the data unit by a predetermined
divisor
-
8/9/2019 Data Link Layer-Megh
45/93
To be valid, a CRC must have two
qualities:
It must have exactly one less bit than thedivisor.
Append it to the end of the data string must
make the resulting bit sequence exactly
divisible by the divisor.
-
8/9/2019 Data Link Layer-Megh
46/93
Three steps:
A string of n 0s is appended to the data unit. Thenumber n is one less that the number of bits inthe predetermined divisor, which is n+1 bits.
The newly elongated data unit is divided by thedivisor, using a process called binary division.The remainder resulting from this division is theCRC.
The CRC of n bits derived in step 2 replaces t
heappended 0s at the end of the data unit. (CRC
may consist of all 0s).
CRC generator: uses modulo-2 division.
-
8/9/2019 Data Link Layer-Megh
47/93
CRC checker:
It functions exactly as the generator does.
After receiving the data appended with the
CRC, it does the same modulo-2 division. If the remainder is all 0s, the CRC is dropped
and the data are accepted
otherwise, the received stream of bits is
discarded and data are sent.
-
8/9/2019 Data Link Layer-Megh
48/93
Error-Detecting Codes
-
8/9/2019 Data Link Layer-Megh
49/93
Withn-bit code words, we have 2 n possible code
words consisting of 2 m data bits (where n = m + r).
This gives us the inequality:
(n + 1) v 2 m e 2 n
Because n = m + r, we can rewrite the inequality
as:
(m
+r
+ 1)v
2
m e
2
m + r
or (m
+r
+ 1)e
2
r
This inequality gives us a lower limit on the number
of check bits that we need in our code words.
2.8 ErrorDetection and Correction
-
8/9/2019 Data Link Layer-Megh
50/93
Suppose we have a set ofn-bit code words
consisting ofm data bits and r(redundant) parity
bits.
An error could occur in any of the n bits, so eac
hcode word can be associated withn erroneous
words at a Hamming distance of 1.
Therefore,we have n + 1 bit patterns for each
code word: one valid code word, and n erroneouswords.
2.8 ErrorDetection and Correction
-
8/9/2019 Data Link Layer-Megh
51/93
Suppose we have data words of lengthm = 8.
Then:
(8 + r+ 1) e 2 r
implies that r must be greater than or equal to 4. This means to build a code with 8-bit data words
that will correct single-bit errors, we must add 4
check bits, creating code words of length 12.
So how do we assign values to these checkbits?
2.8 ErrorDetection and Correction
-
8/9/2019 Data Link Layer-Megh
52/93
Checksum generator
Sender:
The unit is divided into k sections, each of n bits.All sections are added using 1s complement to get the
sum.
The sum is complemented and becomes the checksum.
The checksum is sent with the data
-
8/9/2019 Data Link Layer-Megh
53/93
Checksum checker:
Receiver:
The unit is divided into k sections, eachof n bits.
All sections are added using 1scomplement to get the sum.
The sum is complemented.If the result is zero, the data are
accepted; otherwise they are rejected.
-
8/9/2019 Data Link Layer-Megh
54/93
Checksum calculation-sender
Data=10101001 00111001
10101001+
00111001
11100010
Checksum=00011101
Data sent is 10101001 00111001 00011101
-
8/9/2019 Data Link Layer-Megh
55/93
Checksum calculation-Receiver
Data sent is 10101001 00111001 00011101
Data=10101001 00111001
10101001+
00111001
0001110111111111
Complement=00000000
-
8/9/2019 Data Link Layer-Megh
56/93
Error Correction
Error correction has two most common ways:
Error correction by retransmission: when theerror is discovered, the receiver can have the
sender retransmit the entire data unit.
Forward Error Correction (FEC): a receiver can
use an error-correcting code, which
automatically corrects certain errors.
-
8/9/2019 Data Link Layer-Megh
57/93
To calculate the number of redundancy
bits r required to correct a given number of
data bits m, we must find a relationshipbetween m & r. With m bits of data and r
bits of redundancy added to them, the
length
of th
e resulting code is m+r.
-
8/9/2019 Data Link Layer-Megh
58/93
If the total number of bits in a transmittable unit
is m+r, then r must be able to indicate at least
m+r+1 different states. Of these, one state means no error, & m+r
states indicate the location of an error in each of
the m+r positions.
So m+r+1 states must be discoverable by r bits.Therefore, 2r must be equal to or greater than
m+r+1: 2r>=m+r+1.
-
8/9/2019 Data Link Layer-Megh
59/93
-
8/9/2019 Data Link Layer-Megh
60/93
-
8/9/2019 Data Link Layer-Megh
61/93
Hamming Code
1
1
10 9 8 7 6 5 4 3 2 1
d d d r 8 d d d r 4 d r2 r1
Positions of redundancy bits in hamming code: 7bit ASCII
code with 4 redundancy bits
Redundancy bits are in the position 1, 2, 4 & 8.
-
8/9/2019 Data Link Layer-Megh
62/93
In the hamming code, each r bit is the
parity bit for one combination of data bits,as shown below:
r1 : bits 1,3,5,7,9,11
r2 : bits 2, 3, 6, 7, 10, 11
r4 : bits 4,5,6,7
r8 : bits 8, 9, 10, 11
-
8/9/2019 Data Link Layer-Megh
63/93
Redundancy bits calculation:
r1 will take care of these bits
r2 will take care of these bits
r3 will take care of these bits
r4 will take care of these bits
11 9 7 5 3 1
d d d r 8 d d d r 4 d r2 r1
r
1
r2dr4dddr8ddd
236710
11
7 6 5 4
d d d r 8 d d d r 4 d r2 r1
11 1
0
9 8
d d d r 8 d d d r 4 d r2 r1
-
8/9/2019 Data Link Layer-Megh
64/93
-
8/9/2019 Data Link Layer-Megh
65/93
11 10 9 8 7 6 5 4 3 2 1
1 0 0 1 1 0 1Data: 1001101
1 0 0 1 1 0 1 1Adding r1
1 0 0 1 1 0 1 0 1 Adding r2
1 0 0 1 1 0 0 1 0 1Adding r4
1 0 0 1 1 1 0 0 1 0 1 Adding r8
-
8/9/2019 Data Link Layer-Megh
66/93
The use of error correcting code is often referred to asforward error correction.
Received Data: 1 0 0 1 0 1 0 0 1 0 1
Redundancy bits: 0 1 1 1
(the bit position 7 is in error)
-
8/9/2019 Data Link Layer-Megh
67/93
Using our code words of length 12, number each
bit position starting with 1 in the low-order bit.
Each bit position corresponding to an even
power of 2 will be occupied by a check bit.
These check bits contain the parity of each bit
position for which it participates in the sum.
2.8 ErrorDetection and Correction
-
8/9/2019 Data Link Layer-Megh
68/93
Since 2 (= 21) contributes to the digits, 2, 3, 6, 7, 10,
and 11. Position 2 will contain the parity for bits 3,
6, 7, 10, and 11.
When we use even parity, this is the modulo 2 sum
of the participating bit values.
For the bit values shown, we have a parity value of
0 in the second bit position.
2.8 ErrorDetection and Correction
What are the values for the other parity
bits?
-
8/9/2019 Data Link Layer-Megh
69/93
The completed code word is shown above. Bit 1checks the digits, 3, 5, 7, 9, and 11, so its
value is 1. Bit 2 checks digits 2, 3, 6, 7, 10, and 11. Bit 4
checks the digits, 5, 6, 7, and 12, so its value is 1. Bit 8 checks the digits, 9, 10, 11, and 12, so its
value is also 1.
Using the Hamming algorithm, we can not onlydetect single bit errors in this code word, but alsocorrect them!
2.8 ErrorDetection and Correction
-
8/9/2019 Data Link Layer-Megh
70/93
Suppose an error occurs in bit 5, as shown above.
Our parity bit values are: Bit 1 checks digits, 3, 5, 7, 9, and 11. Its value is 1,
butshould be zero.
Bit 2 checks digits 2, 3, 6, 7, 10, and 11. The zero is
correct.
Bit 4 checks digits, 5, 6, 7, and 12. Its value is 1, but
should be zero.
Bit 8 checks digits, 9, 10, 11, and 12. This bit is
correct.
2.8 ErrorDetection and Correction
-
8/9/2019 Data Link Layer-Megh
71/93
-
8/9/2019 Data Link Layer-Megh
72/93
Hamming codes can correct burst errors:
Arrange k consecutive codewords in a
single matrix.
Transmit the data one column at a time(normally the data would be transmitted
one row at a time).
-
8/9/2019 Data Link Layer-Megh
73/93
-
8/9/2019 Data Link Layer-Megh
74/93
CRC contd..
At the receiving end, receiver again divides the
polynomial corresponding to the received bits by
G(x) and accepts it iff the remainder is zero.
Now let E(x) denote the polynomial
corresponding to the errored bits. Then receiver
receives
T(x) = T(x) + E(x) G(x) divides T(x) iff it divides E(x)
-
8/9/2019 Data Link Layer-Megh
75/93
CRC
Detecting single bit errors
E(x) = x^i
Choose G(x) = any polynomial with at least
two terms
-
8/9/2019 Data Link Layer-Megh
76/93
Detecting 2 single bit errors
E(x) = x^i + x^j = x^i (x ^ (j-i) + 1)
Choose G(x) s.t it neither divides x nor
divides x^k + 1 for any k
-
8/9/2019 Data Link Layer-Megh
77/93
Detecting odd number of single bit errors
E(x) cant be of the form (x + 1) Q(x)
Choose G(x) of the type (x + 1) Q(x)
-
8/9/2019 Data Link Layer-Megh
78/93
G(x) = a general polyn of degree r
Will detect single burst of length
-
8/9/2019 Data Link Layer-Megh
79/93
Detecting single burst of length k
-
8/9/2019 Data Link Layer-Megh
80/93
Hamming Codes : for ED n EC
m data bits together with r error check bits forman n = (m + r) bit codeword
The number of bits two codewords differ in iscalled the hamming distance between the twocodewords
Significance : If two codewords are at HD d thenit requires d single bit errors to convert one intothe other
-
8/9/2019 Data Link Layer-Megh
81/93
HD of a coding scheme
For m bit data .. All the 2^m possiblecombinations are legal
But not all the 2^n codewords are used
-- in a coding scheme (algorithm to compute thecheck bits) some of these codewords are legaland others are illegal
For eq .. Consider parity : 1(r = 1) parity bit isappended with value so that the total number of1s in the codeword is even ..
Th
en 11011 is a legal codeword in th
is sch
eme but
-
8/9/2019 Data Link Layer-Megh
82/93
HD of a list of legal codewords
Minimum HD between any pair of legal
codewords in the list
Remember : Each algorithm to compute the
check bits create a different list of legalcodewords
-
8/9/2019 Data Link Layer-Megh
83/93
Use of HD for error detection
To detect d single bit errors , we need (an
algorithm that creates) a code list with HD
at least d + 1
For eg . For the parity scheme .. HD is 2
..hence it can be used to detect single biterrors (d=1)
-
8/9/2019 Data Link Layer-Megh
84/93
Continued
If the recvd codeword is legal .. We accept it ,
And if it is illegal we report (detect) an error
Q1 : Can ithappen t
hat we recv a legalcodeword when d single bit errors have ocurred
this is eqwt to saying can we get a legal codefrom another legal code by d single bit errors?
A1 : No, since the HD of the code is at least d +1. So a legal CW can be genearted from anotherLCW by inerting at least d + 1 bits and not byinverting d or less bits.
-
8/9/2019 Data Link Layer-Megh
85/93
Continued
Q2 : Can we get an illegal CW when no
errorhas occurred ?
A2 : Obviously not ..since the legal CWwas sent by the sender and if no errorhas
occurred then the recver must recv a legal
CW
-
8/9/2019 Data Link Layer-Megh
86/93
Use of HD for error correction
To correct d single bit errors , we need (analgorithm that creates) a code list with HD atleast 2d + 1.
For eg. Consider the following legal CWs:
0000000000,0000011111,1111100000,1111111111
HD is 5 .. It can be used to correct 2 single biterrors
-
8/9/2019 Data Link Layer-Megh
87/93
Continued..
Claim : Suppose we recv an illegal code C .. Then
there is a unique legal code which is at a
distance d or less from C
Proof : Suppose there are 2 codes C1 and C2 at
distance d (or less) from C .. Then C1 can be
obtained from C2 by 2d (or less) inversions .. Acontradiction to (code has HD at least 2d + 1)
-
8/9/2019 Data Link Layer-Megh
88/93
Hamming Code to correct one bit
-
8/9/2019 Data Link Layer-Megh
89/93
Hamming Code to correct one bit
errors
The bits of the CW are numbered left to
right , starting from 1 the bits that are
powers of 2 are check bits (1,2,4,8 ) andthe remaining are data bits.
Expand the position of each data bit in
powers of 2 ..for eg. 11 = 1 + 2 + 8 .. So11th bit contributes to the computation of
value of these check bits I.e. 1,2, 8
-
8/9/2019 Data Link Layer-Megh
90/93
Continued
We do this for each data bit ..
The value of a check bit is computed so
that the parity of the all the data bits thatcontribute to it together with the check bititself is even.
For eg .
data bits 1001000 will be sent as thecodeword 00110010000
Hamming Code to correct burst
-
8/9/2019 Data Link Layer-Megh
91/93
Hamming Code to correct burst
errors
-
8/9/2019 Data Link Layer-Megh
92/93
IEEE 802 LANs use
For eg.
X^32 + x^26 + x^2
3+ x^22 ..x^2 + x + 1
Detects single burst of length
-
8/9/2019 Data Link Layer-Megh
93/93
I Acknowledge
Help from the following site
http://www.cs.vu.nl/~ast/
In preparing this lecture.