cis341_week06_ch05
Transcript of cis341_week06_ch05
-
7/27/2019 cis341_week06_ch05
1/8
WEEK 6 CIS288: Securing the Network Services and Protocols
Slide 1 Introduction Welcome to week 6 of C-I-S 288: Security Design in aWindows 2003 Environment.
In the previous lesson we discussed securing the networkmanagement process.
In this week we will discuss securing the network services
and protocols.
Next Slide:
Slide 2 Objectives When you complete this lesson you will be able to:
Design network infrastructure security;
Design an I-P Sec policy;Design I-P filtering;
Specify the required protocols for a firewall configuration;
Secure a D-N-S implementation;
Design security for data transmission;Use segmented networks;
Design security for wireless networks;
Design public and private wireless Lans; AndDesign eight-zero-two-point-eleven-X authentication for
wireless networks.
Next Slide:Slide 3 DesigningNetwork
Infrastructure
Security
Designing a secure T-C-P I-P based network begins withthorough planning. The network infrastructure is
comprised of hardware and software elements and has
both a physical and logical structure. Hardware clearly
includes servers, hosts, and gateways, as well as printers,mobile devices, and even the network cabling
specifications. The software side includes operating
systems applications, and services such as D-H-C-P, andother network protocols, and the N-T-F-S file format, to
name a few.
The elements involved with designing a secure network
infrastructure are:
Plan network security; Create secure boundaries; Deploy
network security technologies; Deploy server, application,and user security technologies; and deploy network
monitoring and auditing.
-
7/27/2019 cis341_week06_ch05
2/8
Next Slide:
Slide 4 Designing
NetworkInfrastructure
Security
(continued)
After developing your overall security plan, you need to
drill down to design the security for the networkinfrastructure. Network infrastructure includes those
services and protocols used to run network services. As
with any security model, you must find a workablebalance between security and usability.
Finding this balance requires that you take several logicalsteps to implement the best solution for your firm. These
steps include:
Assess the risk to your network and system data anddetermine the appropriate level of security.
Identify valuable information;
Define security policies based on risk;
Determine how security policies can best be implemented
in an enterprise;Ensure security management and technology requirements
are available and in place;And provide users with an easy and secure method of
accessing the appropriate resources.
Next Slide:
Slide 5 Common
Types ofAttacks
We will now list some common types of attacks.
Understanding attacks clearly is the key to implementingneeded security technologies for your network.
Many types of attacks can occur, and it seems someone isfiguring out another way to attack a secure computer
system almost every day. Some of the common methods
are eavesdropping, data modification, I-P addressspoofing, password-based attacks, brute force attacks,
denial-of-service attacks, man-in-the-middle attacks,
compromised key attacks, sniffer attacks, application-layerattacks, and social engineering.
Next Slide:
-
7/27/2019 cis341_week06_ch05
3/8
Slide 6 IPSec
Overview
I-P Sec is a suite of protocols that provides protection of
data integrity, and authentication. It can also provideoptional privacy and replay protection. The I-P Sec
protocols are defined by the Internet Engineering Task
Force, or IE-T-F.
I-P Sec provides security services at the transport layer of
the T-C-P I-P stack. The I-P Sec driver interfaces with theT-C-U U-D-P transport layer and the Internet layer,
making it transparent to users and applications. It can
receive network communication and, through the use of
filters and rules, it can:Select required security protocols; Determine algorithms
to use for a particular service; And Use cryptographic keys
required by any of the services.
IP-Sec is used to secure the communication channelbetween computers and to secure the data flowing acrossthat channel.
IP-Sec secures data by signing the packet and encryptingdata. You can choose to use one or the other, or both.
Signing the packet involves using a hash value to make
sure the packet has not been tampered with. Encrypting
the data involves an encryption algorithm as well as keysfor encrypting and decrypting the data.
Next Slide:Slide 7 IPSec Policies
Overview
I-P-Sec policy consists of several elements: filter lists,
filter actions, and rules. Its critical to understand howthese work together to enforce security across the
enterprise. Its important for you on the job and will
certainly be one of the key topics on the exam.
I-P-Sec policies are applied based on rules. A rule
provides the ability to create secure communication based
on the source, destination, and type of I-P traffic. Eachrule contains a list of I-P filters and a set of security
actions to take.
Each I-P-Sec rule consists of these elements:
A selected filter list; A selected filter action; Selected
authentication methods; A selected connection type; andSelected tunnel settings.
Next Slide:
-
7/27/2019 cis341_week06_ch05
4/8
Slide 8 Designing IP
Filtering
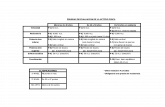
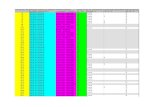
When designing I-P filtering, there are a few design
suggestions that will make your task easier. These aredelineated on the table shown on this slide and describe
recommendations for both filter and filter actions.
For configuring secure servers, including firewalls andcomputers in perimeter networks, you can review the
common list of T-C-P and U-D-P ports and ensure youblock or permit traffic as needed for the correct function
of the computer in question. The Internet Assigned
Numbers Authority, or I-A-N-A, provides a full list of T-
C-P and U-D-P ports from zero through sixty-five-thousand-five hundred-thirty-five.
Next Slide:
Slide 9 Configuration
a FirewallConfiguration
Firewalls can be used between segments of a network or
to protect the corporate network from the Internet. Sincethe firewall by definition provides a security boundary,
configuring I-P-Sec for a firewall makes sense.
To configure a firewall between I-P-Sec computers, it
must be configured to:
Forward inbound and outbound I-P-Sec traffic on U-D-P
source and destination port 500. This allows Isak-M-Ptraffic to be forwarded;
And Forward inbound and outbound I-P protocol fifty, E-
S-P;
Forward inbound and outbound I-P protocol fifty one, A-H;
Forward inbound and outbound U-D-P source anddestination port forty-five-hundred.
I-P-Sec can be routed as normal I-P traffic, although the
forwarders do not have the ability to examine the packet ifit is encrypted with E-S-P.
Next Slide:
-
7/27/2019 cis341_week06_ch05
5/8
Slide 10 Securing a
DNS
D-N-S is the method of resolving I-P addresses to domain
names or domain names to I-P addresses. This vitalnetwork service is a target of interest to hackers because
access to this data provides valuable data for attacking the
network and gaining unauthorized access.
There are a number of common threats to D-N-S that must
be considered and mitigated when planning security forthe enterprise. The table on this slide shows the common
threats and how hackers can exploit these threats.
Next Slide:
Slide 11 Securing aDNS
(continued)
There are a number of ways the D-N-S Server Service canbe configured to reduce the risk of and exposure to attack.
The first step is to examine the configuration of the D-N-S
Service to review settings that affect security. The secondstep is to manage the discretionary access lists on D-N-S
servers that are running on domain controllers. Finally,
implementing the N-T-F-S file system on D-N-S servers
running any operating system that supports N-T-F-Sprotects the files on the server.
Next Slide:
Slide 12 Designing
Security for
Data
Transmission
There are a number of other methods for securing data
being transmitted in a number of different scenarios. I-P
Sec works well in some instances, but other options are
more viable and appropriate in other instances. We willnow review some of these options.
The first is S-S-L T-L-S which stands for Secure SocketsLayer Transport Layer Security. This protocol is typically
used to secure H-T-T-P or H-T-T-P-S traffic on Web sites.
However, it works below the application layer in the T-C-P I-P stack and can be used transparently by applications
that require security for application layer protocols such as
F-T-P, L-D-A-P, or S-M-T-P.
The other option is S-Mime. S-Mime is used to secure e-mail traffic from one end to the other. As mentioned
earlier, S-S-L can be used to secure server-to-servertraffic, but S-Mime is best suited for end-to-end security.
S-Mime is an extension of Mime that supports e-mail by
enabling the e-mail originator to digitally sign an e-mail toprovide proof of both origin and message integrity. It also
enables e-mail to be encrypted to provide confidential
-
7/27/2019 cis341_week06_ch05
6/8
communication via the Internet.
Next Slide:
Slide 13 UsingSegmented
Networks
One of the most common methods of securing networkdata is to segment the network into smaller sections.
Switches, routers, gateways, or firewalls can beconfigured in between these network segments to manage
traffic between and among various network segments.
Segmenting a network improves the efficiency of the
network because multicast and broadcast traffic is kept onthe local segment, preventing it from being transmitted
across the entire network. By segmenting a network, local
traffic stays local and remote traffic is forwarded to thegateway. The gateway can be configured to block or
permit different types of traffic to protect network
segments from either receiving or sending data tounauthorized networks, segments, or hosts.
Next Slide:
Slide 14 Designing
Security for
WirelessNetworks
Now that we have reviewed how to protect data across the
network; we will now discuss how to protect the wireless
network.
There are four different types of wireless networks, based
on their range or scope. They include:Wireless personal area networks;
Wireless local area networks;Wireless metropolitan area networks; And
Wireless wide area networks.
Wireless personal area networks connect wireless personal
devices such as cellular phones, personal digital assistants,laptops, or wireless printers.
Wireless local area networks are designed to provideconnectivity to a local area, typically defined as a building
or office.
Wireless metropolitan area networks connect buildingswithin a campus or city through infrared or radio
frequency. The infrared implementation has limitations
due to the requirement to have line-of-site forconnectivity.
And wireless wide area networks have existed for a while
-
7/27/2019 cis341_week06_ch05
7/8
and are most commonly implemented via cell phones.
The current technology is not standardized and there areseveral companies and technologies vying for their place
in the standard.
Next Slide:Slide 15 Threats to
Wireless
Networks
Before going into the technologies any further, you need
to look at some of the threats to wireless networks.
Clearly, some of the threats are the same as on a wired
network, but there are threats that are specific to wirelessnetworks. Youll look at each threat and find out the best
current solution for mitigating that threat.
Shown on this slide is a table listing all the different typesof threats.
Next Slide:
Slide 16 Designing
WirelessLANs
Designing a secure wireless network takes planning and
integration with existing infrastructure. Some industryanalysts believe that wireless networking will become the
de facto standard, so understanding how to design a
wireless network will help you both on the job and on theexam.
The elements of designing a wireless network include:Designing W-Lan network infrastructure;
Designing wireless authentication;
And designing wireless access infrastructure.
Next Slide:
Slide 17 DesigningAuthenticatio
n for Wireless
Networks
The security mechanisms available for securing a wirelessnetwork are the following:
Eight-zero-two-point-eleven identity verification andauthentication;
Eight-zero-two-point-eleven Wired Equivalent Privacy
encryption;
Eight-zero-two-point- one-X authentication;And I-A-S support for Eight-zero-two-point- one-X
authentication.
Since each of these security mechanisms differ among
their security solutions, it is important to analyze each
mechanism in detail.
Next Slide:
-
7/27/2019 cis341_week06_ch05
8/8
Slide 18 Summary We have reached the end of this lesson. Lets take a look
at what we have covered.
The first half of this lesson was focused on designing
network infrastructure security. Designing a secure T-C-P
I-P based network begins with thorough planning. Theelements involved with designing a secure network
infrastructure are: Plan network security; Create secureboundaries; Deploy network security technologies; Deploy
server, application, and user security technologies; and
deploy network monitoring and auditing.
The second half of this lesson focused on Security for
wireless networks. There are four different types of
wireless networks, based on their range or scope. Theyinclude: Wireless personal area networks; Wireless local
area networks; Wireless metropolitan area networks; AndWireless wide area networks. Each of these wirelessnetworks has its set of threats. Some of the threats are the
same as on a wired network, and others are specific to
wireless networks.