Chaiyakorn
-
Upload
narinrit-prem-apiwathanokul -
Category
Documents
-
view
257 -
download
2
description
Transcript of Chaiyakorn

Aligning IT Security Solutions with Business Justification
Chaiyakorn ApiwathanokulCISSP,GCFA,IRCA:ISMS
Chief Security Officer, PTT ICT Solutions

Aligning IT Security Solutions with Business Justification
• Risk-base security investment (ROSI: Return on Security Investment)
• Global Perspective• Beside security solutions, investing in
human resource is essential KEY to success– Your user: need awareness– Your IT staff: need education– Your management: need understanding

The Challenges– Organization using IT has associated RISK– Vendors want to sell new stuff – Organization doesn’t want to be outdated– Security solution is expensive– Limited budget– Technology moves fast forward– Security prof. is too techy (no business language)
– Where enough is enough?– Requirement base vs. Technology base
Risk-base Security Investment

• Understand your business - Yourself
• Understand the surrounding THREATs – Your ENEMY
• Understand the PROTECTION requirement, limitation and readiness – Your STRATEGY
“If you know your enemies and know yourself, you will not be imperiled in a hundred battles; if you do not know your enemies but do know yourself, you will win one and lose one; if you do not know your enemies nor yourself, you will be imperiled in every single battle.”, Sun Tzu – The Art of War 6th century BC
Sun Tzu – The Art of War

• Risk-base = Requirement-base• Risk Assessment• Quantify – money figure
Risk-base Security Investment

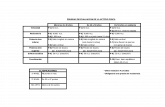
Recent Standards/Guidelines
Topic Business ICTGovernance GRC, COSO (ERM)CG CobiT4.1 (ITG)
ISO 38500:2008 (ITG)ISO 27014 (ISG)ISO 27001:2005 (ISMS)
Risk BS31100:2008 (RM)
ISO31000:2008 (RM)
BS7799-3:2006 (ISRM)ISO13335-3,4:1998ISO27005:2008 (ISRM)NIST SP800-30:2002 (ITRM)
ContinuityCrisis
FEMA141:1993 (EM)PAS 56:2003 (BCI:BCMGPG)BS 25999:2006 (BCM)ISO/PAS 22399:2007 (Societal security)
PAS 77:2006 (ITSCM)BS 25777:2008 (ICTCM)ISO 24762:2008 (ICT DR)NIST SP800-34:2002 (ITSC:DRP)
Others PAS 99:2006 (Integrated Management)
ITILv3ISO 20000 (ITSMS)
By A. Chaiyakorn Apiwathanokul

Identifying assets
• Tangibles– Computers, communications equipment, wiring– Data– Software– Audit records, books, documents
• Intangibles– Privacy– Employee safety & health– Passwords– Image & reputation– Availability– Employee morale

1
Identify Asset Value
• Cost to acquire or develop the asset • Cost to maintain and protect the asset • Value of the asset to owners and users • Value of the asset to adversaries • Value of intellectual property that went into developing
the information • Price others are willing to pay for the asset • Cost to replace the asset if lost • Operational and production activities that are affected if
the asset is unavailable • Liability issues if the asset is compromised • Usefulness and role of the asset in the organization

Identifying threats
– Earthquake, flood, hurricane, lightening– Structural failure, asbestos– Utility loss, i.e., water, power, telecommunications– Theft of hardware, software, data– Terrorists, both political and information– Software bugs, virii, malicious code, SPAM, mail
bombs– Strikes, labor & union problems– Hackers, internal/external– Inflammatory usenet, Internet & web postings– Employee illness, death – Outbreak, epidemic, pandemic

1
Calculating (quantifying) Risks
• Single Loss Expectancy (SLE)SLE = Asset Value x EF
• Annual Lose ExpectancyALE = SLE x ARO
• Single Lose Expectancy (SLE)– Amount of lose occur once the threat is realized
• Exposure Factor (EF)– A measure of the magnitude of loss or impact on the value of an asset
• Annualized rate of occurrence (ARO)– On an annualized basis, the frequency with which a threat is expected to occur
• Annualized loss expectancy (ALE)– Single loss expectance x annualized rate of occurrence = ALE

Cost/benefit Analysis forCountermeasure Valuation
• Cost of a loss– Often hard to determine accurately
• Cost of prevention– Long term/short term– Refer as Safeguard Cost
(ALEno.SG) – (ALEwith.SG) – (Cost of SG) = Value of SG to the company
This value is always referred to when determining Security ROI or ROSI

Global Perspective

From Global Workforce Study by (ISC)2




Information Technology (IT) SecurityEssential Body of Knowledge (EBK)
A Competency and Functional Frameworkfor IT Security Workforce Development
September 2008United States Department of Homeland Security

DoD 8570.01-MInformation Assurance
Workforce Improvement ProgramDecember 19, 2005

DoD 8570.01-MInformation Assurance
Workforce Improvement ProgramMay 15, 2008

Why was the EBK established?
• Rapid evolution of technology• Various aspects and expertise are
increasingly required• Standard or common guideline in
recruiting, training and retaining of workforce
• Knowledge and skill baseline• Linkage between competencies and job
functions• For public and private sectors

Key Divisions
• 4 functional perspectives• 14 competency areas• 10 roles

Functional Perspectives
1. Manage2. Design3. Implement4. Evaluate

IT Security Roles
1. Chief Information Officer2. Digital Forensics Professional3. Information Security Officer4. IT Security Compliance Officer5. IT Security Engineer6. IT Security Professional7. IT Systems Operations and Maintenance
Professional8. Physical Security Professional9. Privacy Professional10.Procurement Professional

Competency Areas (MDIE in each)
1. Data Security2. Digital Forensics3. Enterprise Continuity4. Incident Management5. IT Security Training and
Awareness6. IT System Operations and
Maintenance7. Network and
Telecommunication Security
8. Personnel Security
9. Physical and Environmental Security
10. Procurement
11. Regulatory and Standards Compliance
12. Security Risk Management
13. Strategic Security Management
14. System and Application Security


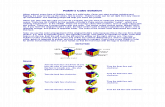
IT Security Roles
Executive Functional Corollary
IT Security EBK:A Competency and
Functional Framework
Functional PerspectivesM - ManageD - Design
I - ImplementE - Evaluate
Chief Information Officer
Information Security Officer
IT Security Compliance Officer
Digital Forensics Professional
IT Systems Operations and Maintenance Professional
IT Security Professional
IT Security Engineer
Physical Security Professional
Privacy Professional
Procurement Professional
M11 12 0 1 2 1 0 1 3 1 D 2 7 1 3 4 6 4 2 6 1 I 0 1 2 5 8 3 4 4 4 1
E 3 10 14 3 5 7 2 3 5 1
Total Competency Units16 30 17 12 19 17 10 10 18 4
TISA EBK Analysis
Entry Level
Professional Level
Managerial Level

Your Competency Scorecard

Enterprise Infosec Competency Profile
* Organization assess Infosec competency
requirement against EBK* Assess current
competency within the enterprise
* Identify competency gap training requirement,
recruitment
Infosec training provider maps
training courses to EBK
EBK
EnterpriseCapability
TrainingProvider

http://www.TISA.or.th

CDIC 2009
www.cdicconference.com
10th – 11th November, 200908:00 – 17:30 Hrs.
QUEEN SIRIKIT NATIONAL CONVENTION CENTER
0-30

Thank You