Application of Quantum Cryptography Nov. 2, 2010 Speaker: Chia-Hung Chien 簡嘉宏 Advisor: Sy-Yen...
-
Upload
stephany-nash -
Category
Documents
-
view
233 -
download
0
Transcript of Application of Quantum Cryptography Nov. 2, 2010 Speaker: Chia-Hung Chien 簡嘉宏 Advisor: Sy-Yen...

Application of Quantum Cryptography
Nov. 2, 2010Speaker: Chia-Hung Chien 簡嘉宏
Advisor: Sy-Yen Kuo
1

Outline
• Quantum Cryptography in Network– BBN, SECOQC, Tokyo
• Application– Indirect QKD, Cloud Computing– Commercial product– Real application
2

BB84
• Alice sends Bob a stream of photons which have been randomly polarized to one of four states (0o,45o,90o,135o).
• Bob measures the photons in a random sequence of basis.• Alice and Bob publicly announces the sequence of basis they
used.• Alice and Bob discard the results that have been measured
using different basis, the results left can be used to derive a secret key.
3

SARG v.s. BB84
• Encoding basis– BB84:– SARG:– Quantum phases are the same
• Strong against PNS attack– non-orthogonal basis
{ } , { } , { } , { } ,
{ }, { } ,
4

Quantum Cryptography in Network
• Build up a network for distributing secrets out of single point-to-point QKD-Links.
• Quadratic scaling: O(n2) links for n users
5
Alice Bob
Charlie
Single QKD-link
Additional two QKD-link

DARPA Quantum Network
• First quantum encrypted functional network
6

Network Architecture
7Source Suite Source Suite
DetectorSuite
SourceSuite
IPsec-ProtectedSessions
QKD Protocols
Single Photons
IPsecSA Keys(Per Session)
QKD SharedSecret Bits(Per QKD Peer)Bob
AliceCharlie
DetectorSuite
DetectorSuite
QKD
IPsec IPsec

SECOQC QKD Network
• Quantum-Back-Bone (QBB) Network– Deployed for test purposes in Vienna
• Quantum Access Networks (QAN)– Free space link allows connectivity
8

QKD-Link Devices
• Attenuated Laser Pulses (Id Quantique)• Coherent-One-Way (University of Geneva)• One-way, decoy states (Toshiba UK)• Entangled photons (University of Vienna)• Continuous Variables (Prof. Grangier)• Access Free Space Link (LMU of Munich)
– The “last mile“ (80 m, >10kbit/s)
9

Quantum Point-to-Point Protocol
• The interface to ensure seamless integration and interoperation between different QKD-Links and node module
• Quantum Point-to-Point Protocol (Q3P) offers– Authentication and encryption services– Point-to-Point protocol between QBB nodes– Manage key storage
10

QKD-RL and QKD-TL
• The QKD Routing Layer (QKD-RL) Protocol– Manage the routing information– Sensitivity and relative scarceness of key material
• The QKD Transport Layer (QKD-TL) Protocol– Dealing with highly congested networks– Exchange confidential and authentic information
across the network
11

Examples
12

Tokyo QKD Network• NEC, Mitsubishi Electric, NTT, NICT, Toshiba Research Europe Ltd. (UK),
ID Quantique (Switzerland) All Vienna (Austria)
13

Network Layout
• Make use of JGN2plus• Star network
Koganei
Hakusan
Otemachi
Hongo
14

Network Layer Structure
15

Network Layer• Quantum Layer
– QKD Devices generate quantum keys via a point-to-point connection
• Key Management (KM) Layer– KM agents collect and store the key– KM server monitors the amount of key in each agent
and supervises the overall key distribution
• Communication Layer– Using distributed keys for encryption and decryption
of text, audio or video data16

Secure Video Conference
17

Experiments in Chunghwa Telecom
18
F棟
C棟
7
6
5
2
1
ST Con.
ST Con.FC Con.
ST Con.
LC Con.
T.L Fiber
5m.
35m.
1.5m.
5m.
35m.
50m.
A
B
C
跳接線ST<->ST
FC<->ST
LC<->ST
SDH/DWDM實驗室
量子實驗室
各 3對
50m.
ST Con.
ST<->ST
1.5m.
D

id Quantique Clavis
19

id Quantique Clavis2 Architecture
20

A Typical Example
21

Phase Coding
22

Interferometer with “base” phase shifters
23

Other Network Topology
• Node1 and Node2 can share secret key by QKD channel A
• Node2 and Node3 can share secret key by QKD channel B
• Can Node1 and Node3 share a theoretical-secure secret key?
• Node2 can be trusted or non-trusted
24
channel A channel B channel C channel D

Quantum Indirect Sharing Key
• Topology: a quantum mobile device network.• Problem: An unsafe routing path for indirect
communication.• Difference: The deriving process is in the indirect
communication.
25
Alice Bob
Eve
Trusted Third Party

The Deriving Procedure0. Alice and Bob initially share a testing table for verifying the key1. Dick generates and distributes entangled qubits
a) N EPR pairs for deriving keyb) N GHZ triplets for verifying key
2. Dick announces a random selection of the bases3. Alice and Bob can generate
a secret key by measurementwith the same bases
4. Alice, Bob and Dick verify thekey with GHZ triplets
26Fig. 1: Distribute B, EPR pairs and GHZ states.
Bob
1 2
Alice
Dick: Third Party
3
4 5
GHZ state
EPR Pair
Block Transmission
B B
Charlie
Different locationon the routingpath.

Notation• First N EPR pairs are denoted
by |E={|e1,12, |e2,12,…|en,12}
• The N GHZ states are denotedby |G={|g1,345, |g2,345…|gn,345}
• The measurement bases isdenoted by B=[b1, b2, .., bn],where bi{0, 1}.0 means z-basis1 means x-basis
• Alice and Bob obtain C=[c1, c2, .., cn] and D=[d1, d2, .., dn] by using B to measure |E
• According to the no-deterministic theorem, the measurement process is random so the condition C=D is satisfied
27
Fig. 1: Distribute B, EPR pairs and GHZ states.
Bob
1 2
Alice
Dick: Third Party
3
4 5
GHZ state
EPR Pair
Block Transmission
B B
Charlie

The measurement of GHZ Triplet
• correlationIf Alice, Bob and Dick measure their qubit in GHZ triplet with thex-basis, they will get a deterministic result |+xa |+xb |+xd
• anti-correlation If Alice and Bob measure with the x-basis but Dick measure with the y-basis, they will not get a deterministic result
28
Dick Alice
Bob
+x -x +y -y
+x |0 + |1 |0 - |1 |0 - i|1 |0 + i|1
-x |0 - |1 |0 + |1 |0 + i|1 |0 - i|1
+y |0 - i|1 |0 + i|1 |0 - |1 |0 + |1
-y |0 + i|1 |0 - i|1 |0 + |1 |0 - |1
Table 1: Correlation and anti-correlation of quantum secret sharing

Verify the Key
Alice measure with x-basis if ci=0, but Bob measure with y-basis if di=0
• For ci=0 and di=0, the measurement bases of Alice, Bob and David are corresponding to x-basis, y-basis and y-basis. Four possible results are 001,111, 010 and 100.After Alice and Bob announce their measurement outcome, Dick accumulates the outcome to verify the key.
29
Condition Alice Bob Dick Results Odd Verify
ci=0 & di=0 x y y 001,111,010,100 yes Correct
ci=1 & di=1 y x y 001,111, 010,100 yes Correct
ci=0 & di=1 x x y 00x,11x,01x,10x x Error
ci=1 & di=0 y y y 00x,11x, 01x,10x x Error
Table 2: Testing table for GHZ state
C=D
CD
adb)111000(2
1

30
Summary• To generate a quantum key is random, because the
measurement outcome of EPR pairs is random.• We do not need to transmit classical information and
quantum information for generating a quantum key. • The topology is indirect communication that can
satisfy with the mobility of the quantum mobile devices.

Quantum TransmissionMechanism for Detection
• Quantum information may be attacked by eavesdroppers and malicious nodes on the routing path.
• This new mechanism can transmit quantum message and detect malicious node at the same time.
31
Alice BobCharlie
Detection Mode
Message Mode
Honest?

The Mechanism
1. Initially, Alice and Bob share a quantum verification table.
32
|123 N1N2N3 Sequence
|000 b1b2b3 01010011
|001 b1b2b1 01100101
|010 b1b2b1 11001010
|011 b1b3b2 01101010
|100 b2b1b3 11110000
|101 b2b3b1 01100110
|110 b3b1b2 10100101
|111 b3b2b1 00001111
|123 denotes index for handshakingbetween Alice and Bob
N1N2N3 denote the measurement basescorresponding to Alice, Charlie and Bob
The sequence denotes the mode ofqubits transmitted to Bob0 represents for detection mode1 represents for message mode

The Mechanism
2. In detection mode, Alice will generate three entangled qubits denoted by |123, and send |23 to Charlie. Charlie pass |3 to Bob.
3. In message mode, Alice will encode message in |5 and send |45 to Charlie. Charlie pass |5 to Bob.
33
Alice BobCharlie
Quantum Verification Table
1 2 3
4 5
Detection mode
Message mode
Symbos 1, 2 and 3 denote entangledqubits for detection mode
Symbos 4 and 5 denote superpositionqubits for message transmission

The Mechanism
4. According to the content of N1N2N3, Bob sends the measurement basis to Charlie
5. Charlie sends his measurement outcomes to Alice and Bob
6. Alice and Bob perform the verification on the bits of detection mode to check whether Charlie is honest or not
7. If Charlie is honest, Bob can accepts the message encoded in the bits of message modeOtherwise, the transmission is stopped.
34

35
Detection and message modes123)111000(
2
1
|123 N1N2N3 Sequence
|000 b1b2b3 01010011
|001 b1b2b1 00001111
|010 b1b2b1 11001010
|011 b1b3b2 01101010
|100 b2b1b3 11110000
|101 b2b3b1 01100110
|110 b3b1b2 10100101
|111 b3b2b1 00001111
Quantum Verification Table
1 3
4 5
2
Alice BobCharlie
Quantum Verification
Table
1.Send qubits 2.Announce Bases 3.Announces outcomes 4.Verify Result
101001101010 10101100
01010110

36
Summary
• The intermediate node has no capability to differentiate which qubit belongs to quantum superposition or quantum entanglement.
• The intrusive behavior from malicious node can be detected.
• So the security of transmission integrity can be achieved.

Quantum Private Queries
• Problem: Symmetrically Private Information Retrieval• Protect Alice’s privacy and Bob’s information
– prevent him from reading her queries without risking capture– prevent her from obtaining more than a few answers for each
database query
37

Quantum Encrypted Computation
• Alice needs data f(y), and Bob is the server providing the service.
• Hermition Matrixis OK
• Unitary Matrixnot sure
38
zzzyfyfxfxfyxfxf )()()()()()(

Obstacles of Quantum Cryptography• The point-topoint paradigm
– Quadratic scaling with the number of users– Dedicated fiber optic line with NO repeaters– Short distance quantum channel– Free air transmission require a clear line of sight
• The integrability in existing networks– Price and reliability of QKD, missing standards
• QKD appears to be restricted toa relatively narrow niche market– SmartQuantum in France is bankrupt
39

QKD in application
• Even in applications in which it can be used, it may not be the preferred option for establishing secure communication due to its cost, size, inconvenience and limitation
• More serious problem– How to deal with side channel attacks in its
theoretical proofs of security
40Adi Shamir’s talk in UQCC 2010

QKD for Cloud Computing?
Data has to be securely sent for remote processing
• On an unknown computer• At an unknown location• Which is typically at a far away location• That changes frequently
41Adi Shamir’s talk in UQCC 2010

Today’s Encrypted Networks
42
RedLink
RedPhysical
RedIP
BlackIP
BlackLink
BlackPhysical
Crypto
IPsecProtocol Suite
Traffic inthe Clear
Encrypted &Authenticated Traffic(via IPsec)
Traffic inthe Clear
Encrypted &Authenticated Traffic(via IPsec)
VPNEndpoint
VPNEndpoint
PrivateEnclave
PrivateEnclave
End-to-End Key Distributionby Courier or Mathematics
End-to-End Encrypted Traffic
BlackLink
BlackPhysical
BlackIP
RedIP
RedLink
RedPhysical
Crypto
IPsecProtocol Suite

Major Cryptosystems• RSA-512
– Invented in 1977, broken by NFS developed 1990
• DES– Standardized in 1977, broken by Diff’l Cr in 1990
• SHA-1– Developed in 1992, broken by Wang in 2005
• AES-256– Developed in 1996, broken at Asiacrypt 2009
• KASUMI– Proposed at FSE 1997, broken at Crypto 2010
43

Future Secure Communication
• Dedicated high-end symmetric encryptors with frequent key change
• Fresh key being constantly generated by QKD devices
44
Information is physical -- Rolf Landauer

Commercial QKD
45
MagicQ

id Quantique
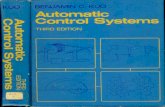
• id Quantique (IDQ) created in Geneva in 2001• Product
– Centauris: high-speed layer 2 encryption– Cerberis: high-speed encryption based on the
proven Advances Encryption Standard (AES)– Clavis2: QKD devices
46Centauris Cerberis Clavis2

MagiQ
• Founded in 1999, U.S. owned and private• Spectrum: 10 Tech Companies for the Next 10
Years
• Customers
47

Swiss election in Geneva
• First real-world use of quantum cryptography(Oct 2007)
• Using Commercial Quantum Cryptography System (Cerberis ) by id Quantique
• Secure the relay of sensitive election data
48

2010 FIFA World Cup
• Durban, South Africa – The first use of ultra secure quantum encryption at a world public event
49

Quantum Key in Mobile
50

Satellite Communication
51

Conclusion
• The cost for QKD is high, but it is worth• Short-term challenges and long-term challenge
are quite different– Short-term: integrate QKD in classical networks– Long-term: quantum repeaters, apply in outer space
• Quantum cryptography can be combined with modern cryptography to realize a sound and practical security
52

53
Thank you for your attention

• A target market of quantum based communication solutions for organizations with distributed subsidiaries/facilities such as governmental institutions, companies and banks is envisaged
54

• Network nodes are considered to be situated in secure locations and are connected by QKDLinks.
55

Reference
• SARG04: V. Scarani et al., PRL 92, 057901 (2004)
• Peev M et al 2009 The SECOQC quantum key distribution network in Vienna New J. Phys. 11 075001
56

DARPA Quantum Network
• First quantum encrypted functional network
57
BBN lab
Harvoard U
Boston U

Outline
• Quantum Cryptography Protocol– BB84, SARG
• Quantum Cryptography in Network– Tokyo, SECOQC, BBN
• Commercial Product– IdQuantique, MagiQ, Smart Quantum
• Application– Indirect, Cloud Computing, Real Application
58