Www.netbenefit.com PCI: As complicated as it sounds? Gerry Lawrence CTO...
-
Upload
grant-fields -
Category
Documents
-
view
220 -
download
0
Transcript of Www.netbenefit.com PCI: As complicated as it sounds? Gerry Lawrence CTO...

www.netbenefit.com
Background
► Experts in business critical hosting► Wide range of customers► …including many e-commerce sites

www.netbenefit.com
Growth of e-commerce
2004 2005 2006 2007 2008 2009 20100
100
200
300
400
500
600
-5%
0%
5%
10%
15%
20%
25%
30%
£billions % over Internet estimated %
Inte
rnet
Sal
es (
£ b
illi
on
s)
Source: UK National Statistics Office

www.netbenefit.com
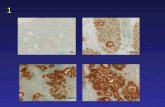
Card fraud
1999
2000
2001
2002
2003
2004
2005
2006
2007
2008
2009
0
100
200
300
400
500
600
700
£ m
illi
on
s
Source: UK Card Association
Reduction due to:
• Sophisticated fraud screening
• Cardholder authentication
• Awareness campaign
• PCI compliance improvements

www.netbenefit.com
Card fraud
Source: Home Office statistics (534 businesses polled)
At some point every business website will suffer an attempted attack in a year.
In 2008 75600 burglary's took place in the UK according to Home Office statistics yet the number of hacks that occur far outweigh this figure.
According to Information Security Breaches survey 2010 94% of business respondents suffered a security breach

www.netbenefit.com
Card fraud
Source: Home Office statistics (534 businesses polled)
► PCI awareness increased
► PCI standards more organised more specific and tougher
► Banks now following through on non-compliance

www.netbenefit.com
Time/resource► Many skills only needed
some of the time
► Monitoring is very time consuming
► Monitoring needs to happen 24x7

www.netbenefit.com
Skills► Deep understanding of the compliance
and regulatory framework
► Secure network design
► Systems design
► Detailed log analysis
► Incident response

www.netbenefit.com
Typical systemInternet
Primary datacentre Secondary datacentre
Firewalls Firewall
Webservers
Databaseservers
Backupserver
Webserver
Databaseserver
Backupserver
SAN
Load balanced

www.netbenefit.com
Choosing the right partner
Selection criteria:
► Security industry expertise to compliment our own
► Specific PCI compliance experience
► Pro-active 24 hour monitoring and response service
► Cultural fit and great attitude

www.netbenefit.com
Build and Maintain a Secure Network
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
12 steps to achieve PCI Compliance

www.netbenefit.com
Build and Maintain a Secure Network
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
Protect Cardholder Data
Requirement 3: Protect stored cardholder data
Requirement 4: Encrypt transmission of cardholder data across open, public networks
12 steps to achieve PCI Compliance

www.netbenefit.com
Build and Maintain a Secure Network
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
Protect Cardholder Data
Requirement 3: Protect stored cardholder data
Requirement 4: Encrypt transmission of cardholder data across open, public networks
Maintain a Vulnerability Management Program
Requirement 5: Use and regularly update anti-virus software
Requirement 6: Develop and maintain secure systems and applications
12 steps to achieve PCI Compliance

www.netbenefit.com
Build and Maintain a Secure Network
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
Protect Cardholder Data
Requirement 3: Protect stored cardholder data
Requirement 4: Encrypt transmission of cardholder data across open, public networks
Maintain a Vulnerability Management Program
Requirement 5: Use and regularly update anti-virus software
Requirement 6: Develop and maintain secure systems and applications
Implement Strong Access Control Measures
Requirement 7: Restrict access to cardholder data by business need-to-know
Requirement 8: Assign a unique ID to each person with computer access
Requirement 9: Restrict physical access to cardholder data
12 steps to achieve PCI Compliance

www.netbenefit.com
Build and Maintain a Secure Network
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
Protect Cardholder Data
Requirement 3: Protect stored cardholder data
Requirement 4: Encrypt transmission of cardholder data across open, public networks
Maintain a Vulnerability Management Program
Requirement 5: Use and regularly update anti-virus software
Requirement 6: Develop and maintain secure systems and applications
Implement Strong Access Control Measures
Requirement 7: Restrict access to cardholder data by business need-to-know
Requirement 8: Assign a unique ID to each person with computer access
Requirement 9: Restrict physical access to cardholder data
Regularly Monitor and Test Networks
Requirement 10: Track and monitor all access to network resources and cardholder data
Requirement 11: Regularly test security systems and processes
12 steps to achieve PCI Compliance

www.netbenefit.com
Build and Maintain a Secure Network
Requirement 1: Install and maintain a firewall configuration to protect cardholder data
Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
Protect Cardholder Data
Requirement 3: Protect stored cardholder data
Requirement 4: Encrypt transmission of cardholder data across open, public networks
Maintain a Vulnerability Management Program
Requirement 5: Use and regularly update anti-virus software
Requirement 6: Develop and maintain secure systems and applications
Implement Strong Access Control Measures
Requirement 7: Restrict access to cardholder data by business need-to-know
Requirement 8: Assign a unique ID to each person with computer access
Requirement 9: Restrict physical access to cardholder data
Regularly Monitor and Test Networks
Requirement 10: Track and monitor all access to network resources and cardholder data
Requirement 11: Regularly test security systems and processes
Maintain an Information Security Policy
Requirement 12: Maintain a policy that addresses information security
12 steps to achieve PCI Compliance

www.netbenefit.com
12 steps to achieve PCI Compliance
PCI compliance…
Does it apply to me?
No, because I use a 3rd party payment provider….
?

www.netbenefit.com
12 steps to achieve PCI Compliance
PCI compliance…
Does it apply to me?
No, because I use a 3rd party payment provider….
….ever heard of ‘Man in the Middle’?
?

www.netbenefit.com
12 steps to avoid Snakes & Hackers
What are the risks?
► Huge Fines► Banks may refuse your
business► More expose to repeat
hacking attacks► Brand reputation
?

www.netbenefit.com
12 steps to avoid Snakes & Hackers
How can NetBenefit help?

www.netbenefit.com
NetBenefit is located at Stand 930
► Pick up our PCI whitepaper► Speak to our PCI experts► Happy to answer any questions

www.netbenefit.com
Working together