€¦ · Web viewSensor can be added to the device that would only require the user to swipe their...
Transcript of €¦ · Web viewSensor can be added to the device that would only require the user to swipe their...

MOBILE COMMERCE
Data Management Strategies & Technologies
DR. Abdullah Alshboul
BY
Helal Al-subagh

Abstract
Advances in e-commerce have resulted in significant progress towards strategies, requirements
and developments of e-commerce applications. However, nearly all e-commerce applications
envisioned and developed so far assume fixed are stationary users with wired infrastructure. A
new e-commerce application that will be possible and significantly benefit from emerging
wireless and mobile networks is envisioned. To allow designers, developers and researchers to
strategize and create mobile commerce applications, a four level integrated framework for
mobile commerce is proposed. Since there are potentially an unlimited number of mobile
commerce applications, several important classes of applications such as mobile financial
applications, mobile inventory management, proactive service management, product location and
search and wireless re-engineering are attempted to be identified. It is discussed how to
successfully define, architect and implement the necessary hardware/software infrastructure in
support of mobile commerce. Also, to make mobile commerce applications a reality, networking
requirements is addressed, support from wireless carriers is discussed, and some open research
problems is presented.
E-commerce, or the buying and selling of goods and services on the Internet, has become a part
of daily life for many people. The use of the Internet to purchase goods and services has grown
along with the popularity of the Internet. Businesses are increasingly turning to the Internet to
increase revenue and profits. As the Internet expands to every corner of the globe, it is becoming
easier and easier to access it from a wide variety of devices. Cell phones, PDAs, and other
mobile devices can now access the Internet from across the globe. Many E-commerce companies
have attempted to exploit this rapidly growing segment of the Internet. E-commerce over mobile
devices has now been termed M-Commerce. M-Commerce by definition is E-commerce that
occurs through the use of wireless solutions such as cell phones, pocket PC's, and PDAs. It
allows a user to purchase goods and services on the move, anytime, and anywhere.
In today’s E-commerce world, security has become a major issue that needs to be constantly
monitored and improved. By expanding E-commerce to mobile devices it is also necessary to

ensure that these devices are protected against security threats. M-Commerce faces the same
security threats that E-commerce faces plus many other due to the mobile nature of the products.
This paper will discuss the security challenges and weaknesses of M-Commerce and varying
ways to correct and overcome them. It will focus on security issues that arise when M-
Commerce devices connect and communicate over the Internet. Security challenges, risks, and
security implementations within M-Commerce will be discussed in detail. By describing the
current state of security within M-Commerce this paper will show the pitfalls that need to be
corrected. The paper will then propose an ideal M-Commerce system that will overcome these
pitfalls and provide optimal security without degrading the new technology to the point of
uselessness.

M-Commerce summary
Electronic commerce has attracted significant attention in the last few years. Advances in e-
commerce have resulted in significant progress towards strategies, requirements and
development of e-commerce applications. Nearly all the applications envisioned and developed
so far assume fixed or stationary users with wired infrastructure, such as browser on a PC
connected to the Internet using phone lines or a Local Area Network. A new e-commerce
application such as Wireless e-commerce or Mobile e-commerce will benefit one to reach the
consumer directly, regardless of where he is.
M-Commerce occurs through the use of wireless devices such as cell phones, pocket PC's, and
PDAs. It allows a user to purchase goods and services on the move, anytime, and anywhere. M-
Commerce is becoming a larger part of the Internet commerce experience. Juniper Research
performed a study that predicted that by 2009, global M-Commerce revenue will exceed 88
billion dollars. A Morgan Stanley report found that in 2005 there was 19.5 billion dollars in M-
Commerce transactions. These included revenue from people buying ring tones, cell phone
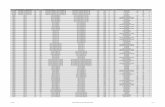
personalization, games, and services. The following chart was obtained from that Morgan
Stanley report and shows revenue generated between 2004 till 2008.
Courtesy of Morgan Stanley
With this large amount of revenue potential, companies are quickly moving into the mobile
marketplace. The M-Commerce marketplace includes many new customers that may not own a

computer or purchase goods over the Internet. In many countries of the world it is more likely
that an individual will have a cell phone then a computer with Internet connectivity. McKinsey
research firm reported that in 2005 there was an estimated 85% penetration rate for mobile phone
usage in Europe and a study in Asia by Data monitor reported that there were over 310 million
mobile devices in Asia. The Morgan Stanley research report mentioned earlier shows that in
many areas of the world the number of mobile users exceeds the number of PC users. For
example in China the ratio of cell phones to computers is 3.6 to 1, in Japan its 1.1 to 1, and in the
UK its 1.5 to1. The report also showed that more emails in Japan were sent by mobile phones
then by PC. These scenarios are highly attractive to companies because it provides an
opportunity to expand their customer bases. This means there is a potential to reach millions of
new customers and expand on revenues.
The biggest benefit that M-Commerce provides to consumers is mobility. There is no need to be
sitting at an office desk or at a home PC to perform M-Commerce. Customers can be on the
beach, in a car, or hundreds of other locations and connect to the Internet. As long as their
mobile device network is in range then M-Commerce transactions can be made. In order to meet
these demands, cell phone companies across the world are continually upgrading their networks
and increasing the speed and bandwidth of these networks.
European and Asian cell phone companies have utilized high bandwidth cell services for many
years. This technology is often referred to as 3G. American cell phone companies are beginning
to bring 3G to the US. A few examples of these are AT&T’s Broadband Connect (HSDPA),
Sprint PCS Wireless High Speed Data (EV-DO), and Verizon Wireless Broadband Access EV-
DO. These upgrades to cell services allow users to access more and more types of high
bandwidth Internet content. The ability to access a wide variety of Internet sites opens a whole
new business model. The evolving technology allows people to make productivity out of
otherwise idle time. People can buy movie tickets, make financial transactions such as
purchasing stocks or checking a bank balance, read email, or purchase other goods. And with
these increased cell services people now expect to be connected at any time, any place, without
being tied to an office or home computer.

As can be seen from the statistics and scenarios mentioned above, M-Commerce has enormous
potential to generate revenue and allow new people to access the Internet. But along with the
potential it also has a large amount of risk, limitations, and challenges. In the near future a great
deal of money and data will be transferred utilizing M-Commerce systems. And as always seems
to be the case, someone will try and exploit the system and steal this money and information. For
this reason it is necessary to ensure that current and future mobile devices that will be utilizing
within M-Commerce implement security mechanisms. M-Commerce faces the same security
threats that e-commerce faces plus many others due to the mobile nature of the products. Will
discuss the challenges and weaknesses of M-Commerce and then will present security
mechanisms that currently exist. The paper will close by discussing methods to improve current
systems for the future and what should be contained in an optimal and secure M-Commerce
security protocol.
Mobile Advertising
Mobile advertising is also a very important class of mobile commerce applications. Using
demographic information collected by wireless service providers and information on the current
location of mobile users, much targeted advertising can be done. The advertising messages sent
to the user can be location-sensitive and can inform a user about various on-going specials
(shops, malls and restaurants) in surrounding areas as shown in figure. This type of advertising
can be performed using Short Messaging Service (SMS) or by using short paging messages to
mobile users. The messages can be sent to all users located in a certain area, a user-specific
message can be sent independent of the user current location. Since the services need the current
location information of a user, a third party may be needed to provide location services. However
this may require a sharing of revenues between the network service provider and location service
provider. As more wireless bandwidth becomes available, content rich advertising involve audio,
pictures and video clips can be produced for individual users with specific needs, interests, and
inclinations. It is also possible that direct advertising to users may be performed without much
control from the wireless service providers. Mobile Inventory Management (MIM) This class of
application involves location tracking of goods, services and even people. The tracking of goods
may help service providers in determining the time of delivery to customer, thus improving
customer service and obtaining a competitive edge over other business. One very interesting

application is rolling inventory-which may involve multiple trucks carrying a large amount of
inventory while on move. Whenever a store needs certain goods/items, it can locate a truck
(preferably in nearby area) and just-in-time delivery of goods can be performed. The rolling
inventory and delivery application can reduce the amount of inventory space and cost for both
vendors and stores and may reduce the time between when an order is placed and the goods are
delivered. Location tracking of components can be broken into two components: indoor and
outdoor. Indoor tracking can be performed by a chipset (TX/RX) and location information may
be transmitted over a satellite or cellular/PCS system to the component supplier where such
information is needed. Product Location and Search (PLS) this class of application includes
locating an item in a particular area or location. This is concerned with finding an item with
certain specifications and whether it is available in a specified area or not. Potentially, there
could be multiple places where such an item or items of similar attributes are located. Currently
many people are going to several stores to find an item (certain brand/size of TV, VCR or an
automobile) and compare prices and features. Using a mobile device and centralized/distributed
database containing information on products, a user should be able to find the exact location of
the store where a certain item is located. After that the user can buy online using a browser on
his/her mobile devise. In the case of multiple stores/vendors carrying an item desired by a user,
they could compete to get customer by real time manipulation of prices or by offering instant
discounts. From the technological point of view, a mobile user can send a query message to a
centralized location (shown in figure), which in turn can interface several different stores/dealers
and decide if the item is available or not.
M-Commerce Security Challenges
M-Commerce, like E-commerce, faces formidable security hurdles. As identity theft, phishing,
and other attacks on the Internet become more prevalent, consumer trust in Internet technologies
seems to be falling. In order for M-Commerce to be successful the security weaknesses and
concerns need to be addressed and solved. The key to widespread usage of M-Commerce is to
gain the trust of users so that they will be willing to perform transaction on their mobile devices.
As previously mentioned M-Commerce has the same security problems that occur within e-

commerce plus it has its own set of unique challenges. M-Commerce has the problem of viruses
and malware, data theft, Denial of Service attacks, phishing, insecure default settings,
inexperienced users and sniffing that seem to affect all Internet technologies. M-Commerce also
has some unique problems such as limited computer power, loss or theft of the mobile device,
varying standards, the broadcast nature of wireless transmissions, immature technologies, lack of
authentication, and weak device operating systems. In order to reach its full potential these
challenges and weaknesses must be addressed.
M-Commerce has two major security challenges that differentiate it from normal Internet
commerce. The first challenge is that the devices are small and portable which can result in loss
or theft of the device. Mobile devices are by design small and portable. While this is good for
day to day usability and convenience it is not a good then when it comes to security. Modern
mobile devices contain more and more sensitive information. In recent years there has been an
abundance of instances where companies have lost personal data by losing laptops or backup
tapes. This same type of incident could occur with a mobile device. Mobile devices often contain
phone book entries, journal entries, calendars, etc. that can contain valuable personal or
corporate information. In a corporate setting the theft of this data could lead to financial losses or
loss of a company’s trade secrets. Today Pocket PCs and Smart Phones can contain full
documents or spreadsheets that could contain sensitive data. Loss of this data could harm an
individual or company more than just the disclosure of a phone book or date book. The challenge
with mobile devices is that we need to be able to protect the sensitive data on the phone even if it
is lost or stolen.
The second challenge is that mobile devices are not as powerful as modern computers. This
makes security a challenge because the same security mechanisms that may work on a desktop or
laptop PC may not work on a mobile device. The capabilities of Mobile devices often lag behind
PCs because they typically lack in processor power, memory, storage space, display capabilities,
and input capabilities. This causes problems when trying to use PC security protocols on a
mobile device. For example many encryption standards used on the Internet today use a large
amount of processing power to perform the mathematical computations required by
cryptography. Mobile devices may not have the processing power necessary to perform these
computations and therefore certain types of encryption may not be able to be used. Mobile
Devices are becoming more and more powerful but they will always be a step or two behind the

power of PCs. Because of this lag there will probably always be protocols and standards that
function on a PC that cannot be used on a mobile device.
M-Commerce Security Weaknesses
The challenges listed in the previous section cause many weaknesses within M-Commerce
systems. These weaknesses are lack of user awareness, limited computing power, possible loss or
theft of device, incomplete authentication schemes, the use of wireless transmissions, vulnerable
operating systems, and the use of unsecured technologies.
User Awareness: A major security weakness that occurs in both e-commerce and M-Commerce
is the lack of user awareness. The typical user is not aware that their actions have security
implications. A typical user will not worry about securing their phone through a locking
mechanism, or they will not ensure that transactions are secure before proceeding. This can lead
to the spread of viruses or the leaking of sensitive data.
A possible solution for overcoming the lack of user awareness is to have the wireless carriers
offer security training or provide a security awareness pamphlet when a user purchases a mobile
device. There will always be people who refuse to read a pamphlet or pay attention to security
training but the more people that are away of the risks the more likely the risks will be reduced.
Also, the mobile device manufacturers should be held responsible for making the devices a
secure as possible by default. Currently many security features are either disabled by default or
are set to the lowest security setting. If manufacturers set their device security defaults to a
secure setting then users will always have some level of protection even if they decide not to
further configure the phone.
Limited Computing Power: As mentioned in the previous section, mobile devices do not have
the same computing abilities as PCs. Mobile devices by nature need to be small and portable for
functionality and therefore cannot contain the same technology as larger PCs. A major
disadvantage of not having the same computer power is that certain security related tasks require
heavy processing in order to be accomplished successfully. The lack of CPU power makes some
of these tasks impractical within a mobile device. The best example of this is encryption. A
powerful processor is required to perform the complex mathematical calculations that are used in
modern encryption schemes. Performing complex mathematical calculations on a mobile device

can overwhelm the devices processor and cause the device to function extremely slow and
possibly crash the system. In order to get encryption to work properly on these devices
manufactures are required to either rework existing encryption algorithms to function on the
slower processor or remove the encryption all together.
As technology advances inside the mobile devices it is becoming more and more possible to
implement today’s encryption standards. The problem is that the mobile device industry needs to
increase their processor speeds at the same rate that the encryption standards change. Current
encryption methods will not work in the future. Attackers will have more powerful machines at
their disposal that can be utilized to crack current encryptions. In order for M-Commerce to stay
secure it will need to evolve with the encryption standards to ensure that the newest standards
can be utilized on mobile devices. The best circumstance would be if mobile device processors
advance at a rate that allows them to perform typical PC encryption standards. This would reduce
the amount of work that is currently necessary to rework existing encryption algorithms.
Possible Loss or Theft of Device: As stated earlier a major challenge and weakness of M-
Commerce is that the devices are small and easily lost or stolen. The loss of a device can lead to
financial losses or identity theft. The cost of a lost or stolen device goes well beyond the cost of
just replacing the device. Along with the cost of the phone a user also loses the intangible costs
associated with loss of data. It is not really possible to prevent the loss of theft of a device. But it
is possible to secure the device so that if it is lost or stolen it is useless. The best ways to do this
is to encrypt data on the devices and/or to implement a secure authentication scheme. This will
be talked about next.
Lack of Complete Authentication: One of the major weaknesses that exist within M-Commerce
is the lack of complete authentication. Currently cell phone service providers authenticate the
devices they have on their network through the use of a SIM card within the user’s mobile
device. This enables the service provider to be reasonably sure they are communicating with the
proper device. The problem occurs because there is a lack of authentication in the system
between the user and the phone. Currently most cell phones have no method in place to prove
that the user making Internet transactions on the phone is the rightful owner of the phone. This
means an attacker can use the phone to make fraudulent purchases without ever needing to crack
any authentication scheme. On most devices it is possible to enable a lock function on the phone
to secure the device but this is typically only a 4 digit code that has a small range of possibilities.

It would be relatively easy for a determined attacker to break the code through trial and error or
the use of a computer. Even with the ability to use a security code, the majority of users do not
implement it. It is seen as an inconvenience and not necessary. Even the default mode for most
devices does not implement the pass code. By not requiring the user to authenticate to the phone
anyone can access the contents of the phone and possibly impersonate the legitimate user in
order to purchase goods or services online.
There a many ways being proposed to add user authentication to mobile devices. The most basic
is to use a password scheme instead of the typical 4 digit pin. A password can be more complex
and would expand the range of possibilities by allowing numeric and alphanumeric characters. It
would also allow the password to be over 4 characters. This functionality is currently being
implemented on some Smart Phones and PDAs.
Another proposed solution is to use signature or handwriting recognition. This would require that
the device have a touch screen and stylus that would allow a user to sign their signature. The
device would then compare this to a sample signature that was entered into the device during
setup. If the signatures match then the user would be authenticated and allowed into the system.
The problem with this system is that it requires additional hardware be added to the phone. The
touch screen and stylus would add to the cost of the phone. This may make it impractical for
most mobile devices.
Yet another proposed Authentication scheme is biometrics. The most feasible biometric
technology that could be implemented in a mobile device is fingerprint recognition. A fingerprint
Sensor can be added to the device that would only require the user to swipe their thumb over a
sensor to grant access to the phone or access to specific applications on the phone. The system
could be similar to the fingerprint sensors that Lenova is implementing in their Think Pad
laptops. Many popular cell phone manufacturers, such as LG, have begun implementing
fingerprint sensors into special models of their phones. Most of these phones are currently
unavailable in the US but will be available in the future. Unfortunately biometrics have some
significant problems. For one, if the fingerprint sensor fails or reads a false negative, even with
the correct finger, then the user cannot gain access to their phone. This is a common problem in
all biometric systems, not just mobile devices. In order for biometrics to become a widespread
reasonable authentication option for mobile devices a method needs to be created to bypass the
fingerprint reader in the case it’s failing and also a more reliable scanner must be developed.

Currently the biometric sensors are not used to lock and unlock a phone. They are instead used to
authenticate the user when they are performing specific online transactions. Before the biometric
sensors can be used to log a user into their phone the false negative situation needs to be
resolved. The other downside of adding biometrics to a cell phone is that it adds a significant
hardware cost to the device and may not be reasonable on lower end mobile devices.
Vulnerability of Wireless Transmissions: Like WiFi, mobile transmissions are broadcast through
the air and because of this the transmissions are able to be captured by anyone in the vicinity of
the device sending the transmission. An ambitious attacker could sniff the air and attempt to
collect packets. Transmission technology typically encrypts all data but an attacker can still
attempt to crack the encryption. And if for some reason a transmission is not encrypted, due to an
unsecured protocol or a flaw, then the attacker can read the contents of the data. Currently the
wireless transmissions used for mobile devices are relatively secure and flaws are relatively few.
To overcome those few instances where vulnerabilities may exist, carriers and mobile device
manufacturers need to ensure that their devices use secure protocols and that the protocol is used
throughout an entire communication session so that no data is transmitted in plaintext at any
time.
Vulnerable Operating Systems: Most mobile devices have simplified operating systems. In the
past there was no need to make the OS complicated. Now devices are beginning to become more
sophisticated and have more and more applications running on them. Smart phones and PDAs
may run Microsoft Windows Mobile 5.0 OS or a Palm OS. These OS are vulnerable to coding
flaws like any PC OS. The major problem that occurs with these mobile OSs is that they do not
have the same update functionality that desktop PCs currently enjoy. For example, Microsoft
Windows Mobile does not have the Windows Automatic Update service. So if a hot fix or patch
is released to update security vulnerability within the OS then it will not be automatically pushed
to the device. In order to receive the update the user would need to be proactive and get it
themselves. This is not an efficient way to update vulnerabilities on an OS. A typical user will
not be aware of new hot fixes being released and chances are they will never apply the necessary
hot fixes. Therefore the OS is left vulnerable which could allow an attacker to gain access and
circumvent any other security features that have been implemented, such as authentication.

The solution to correcting the vulnerable Operating System problem is to create an automatic
update system like the ones that are used on PCs. The OS vendors need to create a way that will
allow carriers to push the updates to the mobile devices when the devices are online and also
have the updates installed silently in the background. The Microsoft Automated update system
could be a good model to follow.
Another weakness that seems to appear more and more in today’s technically advanced phones is
the implementation of unsecured technologies. For example many phones are beginning to
implement infrared and Bluetooth sensors into their phones. These protocols can be very helpful
for a user by allowing them to remotely connect other devices to their mobile device in order to
transfer files, date books, addresses, etc. Unfortunately, these protocols are also susceptible to
exploitation. Both Bluetooth and Infrared ports give an attacker a backdoor to gain access to the
device. An Attacker may be able to gain access to the device while never getting within 20 feet
of it. Bluetooth has also been the primary source of viruses on mobile devices. While these
viruses are not yet widespread they are becoming a bigger and bigger threat. With the lack of
virus software running on mobile devices there is reason to worry. A device that is infected by a
virus could potentially infect everyone in their address book. Bluetooth is also susceptible to
“Blue Snarfing”. Blue Snarfing is when an attacker gains access to your device through the
Bluetooth port. Once the attacker gains access to the phone the attacker can change appointments
and/or steal address books, photos, and files. Even worse an attacker may be able to make calls
through your phone or possibly crash the device OS.
Device manufacturers often implement the newest technologies because they are in a race to be
the first to market. The security issue arises when the manufacturers do not ensure these
technologies are secure or they do not disable the insecure technologies by default. In order to
correct this problem, manufacturers need to spend more research time to determine if
technologies are secure. If they are not secure the manufacturers should determine a way to make
them secure or at least disable them by default on a device so that novice users do not leave
themselves susceptible to attacks.

M-Commerce Technologies
Mobile devices typically connect through the Internet using one of two technologies, either the
Wireless Application Protocol or iMode. Which technology is used depends on location and
carrier. Both protocols have security protocols in place to protect data that is transferred. They
each also have methods to authenticate the device to the carrier. The following sections will
briefly discuss each protocol and then detail the security implementations for each protocol.
Wireless Application Protocol
The Wireless Application Protocol, or WAP, is one of the most widely used standards within M-
Commerce. It is a standard created by the WAP forum that dictates a common method for
accessing and viewing web content through wireless mobile devices, primarily mobile phones. It
has been designed to function on mobile devices that do not have the CPU power, memory,
bandwidth, or display abilities that desktop or laptop computers have. The WAP protocol details
everything from how the mobile device needs to function when accessing and viewing Internet
content, to how the data must be transferred. Every protocol within WAP is optimized for low
bandwidth and low power devices. WAP was also developed to be bearer independent. That
means that it was designed to work on a variety of mobile network types for example GPRS,
EDGE, and CDMA.
WAP allows a user to utilize very basic browser software called a “micro-browser” to visit web
pages that are designed specifically for mobile devices. These sites are usually designed with text
and minimum graphics. WAP has also been designed to be flexible and allow devices with
varying display abilities, for example screen size or resolution, to all work properly when
accessing the same sites.
WAP was initially release in 1998. [10] WAP Version 1.0, as it was called, utilized its own set of
wireless protocols in order to communicate with the carrier and remote websites. The following
figure shows the different layers of the WAP 1.0 network stack and the stacks utilized by the
carrier and a remote web server. The WAP Device is the mobile device, the WAP Gateway is the
carrier, and the Web Server is a remote website server. For information on the specific protocols
see the WAP Forum documentation for WAP 1.0.

This protocol stack was functional for the first incarnation of WAP but it was not very secure
and it was not fully functional with all Internet sites. Security in WAP 1.0 was provided through
WTLS. WTLS is a scaled down version of the popular TLS protocol. The major security
weakness of WAP 1.0 came from a problem called the “Gap Problem”. When a mobile device
attempts to connect to a website it must first connect to the carrier and then the carrier will pass
the web request to the remote web site. When using WTLS and WAP 1.0 the mobile device
would make a secure connection with the carrier and the carrier would use TLS to make a
separate secure connection to the remote website. In the figure above you can see that the
Gateway transforms the WTLS connection into a TLS connection with the remote website. The
security vulnerability, or Gap Problem, arose when the carrier had to take the data from the
mobile device and pass it to the remote server. As a middleman, the carrier would decrypt the
data from the mobile device and then encrypt it using TLS to pass the data to the remote carrier.
After the data is unencrypted and before it is passed to the remote website, the data is stored
entirely in plain text and visible to anyone who gains access to the carrier’s server. The preferred
work around to the Gap problem in WAP 1.was to not save any transactions to disk and/or, if
you were a corporate customer, move the WAP Gateway within the company network so that the
data can be better protected.[11] This solution was not thorough enough and is one of many
reasons that WAP 2.0 was developed.
WAP 2.0 was released in late 2001 and is fully backwards compatible with WAP 1.0. WAP 2.0
added support for TLS, HTTP, and TCP and introduced the ability to push data from a carrier to
a WAP enabled mobile device. WAP 2.0 is also able to support more powerful mobile devices
over higher bandwidth connections. From a security perspective the most important addition was
the ability to utilize the TCP\IP network stack. The reason being is that TLS could now be used
instead of WTLS and common PC Internet technologies could be utilized. The use of TLS
instead of WTLS allows a mobile device to make a secure tunnel from the device all the way to
the remote website. There is no longer a need to decrypt and encrypt the data at the carrier’s
server (WAP Gateway). Therefore there is no longer a Gap Problem. The figure below shows the
protocol stack for WAP 2.0 and the stacks utilized in a typical web connection. The WAP device

is the mobile device, the WAP Proxy is the carrier, and the Web Server is the remote website’s
server.
According to the WAP Forums documentation of WAP 2.0, the WAP Gateway from version 1.0
was removed and replaced by the WAP proxy. The Proxy does not perform translation like the
WAP Gateway but instead assists by speeding up communications and it can provide services to
a mobile device through a WAP push.
Besides the ability to use TLS and make a secure connection from device to website, another
major security feature of WAP is the ability to use a WAP Identity Module (WIM). The WIM is
a tamper resistant chip that is typically embedded on a users SIM card. The WIM is often
referred to as the security module of the SIM chip. The chip contains the user’s digital certificate
and private key information and it stores the cryptographic functions that can be used with
security protocols. The private keys on the WIM can be utilized for authentication and for
creating digital signatures. The chip was also designed to be tamper resistant in order to prevent
attackers from modifying or extracting the certificates or keys from the chip.
The WIM chip can be utilized within a Wireless Public Key Infrastructure (WPKI). WPKI is the
wireless version of typical PKI systems. It allows the use of private and public keys in a M-
Commerce environment. WPKI provides confidentiality through cryptography, authentication
through digital certificates, integrity through digital signatures, and non-repudiation through the
use of digital signatures and certificates. The primary difference between a PKI and WPKI
environment is that WPKI has been modified to function with lower powered mobile devices and
on lower bandwidth networks. WPKI takes full advantage of the WIM chip by using the user’s
private keys that are stored within the WIM. The same x.509 certificates that are utilized within
standard PKI are also utilized within WPKI and are stored on the WIM.
iMode
iMode is a protocol similar to WAP that allows mobile devices to connect to the Internet.
Whereas WAP was developed by a forum of vendors and researchers, iMode is a proprietary
technology and was developed by NTT DoCoMo, a Japanese telecommunications company. It is
extremely popular in Japan and is spreading to Europe and other parts of Asia. At the end of
2004 there were over 35 million users.[8] Many Japanese users send email, access websites,

purchase tickets and perform many other online transactions through iMode. Unfortunately, due
to the proprietary nature of iMode there does not seem to be the same growth potential that WAP
has. iMode requires a user to connect to a NTT DoCoMo owned server in order to access the
web. In order for iMode to grow NTT DoCoMo would need to invest a significant amount of
money into their infrastructure in order to have enough servers for a larger user base. This differs
from WAP.
Where separate vendors can share the cost by implementing their own WAP systems and
interconnecting them through the Internet.
Since iMode is proprietary, very little is known about the way security is implemented in the
system. It is known that the protocol uses standard HTTP security protocols like TLS and SSL
but lower level protocols are all proprietary so no security information is available. It is also
known that iMode phones come pre-configured with root CA keys from VeriSign or other
certificate authorities. This allows for the SSL connection between the device and the remote
web sites. As for authentication, iMode uses basic HTTP authentication.
There is reason to worry about the security of iMode because the initial implementation was
designed with security as an afterthought and the current implementation is vague. The primary
goal upon introduction of the product was to provide Internet access and make a profit. Since the
initial implementation security features have been added but it is not known exactly how secure
the devices really are. I believe in order for iMode to remain competitive with WAP more
information about its implementation must be made available to the general public. This is the
same debate that exists within the computer world of Open Source vs. Proprietary. While
Proprietary may be good for making a profit it
Model M-Commerce Security protocol
By now you can see that there are many weaknesses that exist within devices that utilize M-
Commerce. In order for M-Commerce to grow these issues must be addressed. The following
section details and ideal M-Commerce security protocol. The protocol has been categorized into
three areas: Device Security, User Security, and Network Security. These three categories cover
the three main areas that require security within an M-Commerce environment.

Device Security
Of all components of an M-Commerce system the one that should be the most secure is the
mobile device. The device is where data originates, resides, and is received. If the information
can be secured on the device then there is a better chance it will be secure throughout an entire
M-Commerce transaction. A model mobile device would be secure by default. All technologies
utilized on the phone should be locked down. The technologies utilized should not be locked
down so tightly that they are no longer functional or so much that they become a burden but
enough that a typical user will be relatively secure without the need to manually configure the
device. An example of this is that Bluetooth and Infrared sensors should be disabled by default.
If a user wishes to use the technologies then they can enable them manually on the device. When
the user enables the technologies they should be warned of the possible security risks. By making
the customer aware of possible security threats they will be more aware of their actions. They
will be more likely to disable the technology when they are finished using it.
Also, in order to provide security upon initial use of the device, the customer should be walked
through a set of configuration steps where they will be asked to provide a password and set other
security settings. This will force a user to have some level of authentication on their device and
by requesting that the user set a password there is a better chance that the feature will be utilized.
While this may be seen as a nuisance at first it is more likely that a user will be accustomed to
the feature if it is used from the very first time they power on the device.Along with prompting
the user to configure a password the manufacturer should configure the device to use
alphanumeric passwords that are greater than 4 digits. This would make the password more
difficult to crack if the device was lost or stolen.
On more sophisticated and costly phones, biometrics should be implemented. A fingerprint
scanner should be embedded within the phone. When a call is to be made or a web transaction is
to be performed the user need only to rub their finger over the sensor to be authenticated. This
will prohibit any attacker to utilize the phone if they steal the phone. At the same time it is not
overly burdensome on the user because it only requires a simple finger swipe. If Biometrics are
implemented then the password feature mentioned in the previous paragraphs can be disabled.

A model M-Commerce device should also use a mobile web protocol that has the ability to
perform secure internet transactions. This protocol should use standard TCP\IP security features
and protocols that are commonly utilized on the Internet. The implementation of proprietary
technologies or differing protocols can increase complexity and reduce the level of security
within the system. An example can be seen with the WAP 1.0 Gateway problem. The Gateway
problem was caused because WAP 1.0 utilized WTLS instead of the Internet Standard TLS. In
order to function properly the Carrier had to translate the WTLS into TLS for the Internet. This
created security vulnerability. By utilizing a standard TCP\IP protocol suite, a mobile device will
be able to use TSL\SSL to create secure tunnels for all secure transactions and communications.
WAP 2.0 is a good example of a protocol that satisfies these requirements and it would make a
good choice when implementing a secure M-Commerce model.
A model M-Commerce device should also be able to utilize private keys and digital certificates.
These would be utilized to provide authentication, confidentiality, integrity, and non-repudiation.
These private keys on the device should be unique for every individual and they should be stored
securely on the mobile device. They should also be registered with a Certificate Authority so that
their public key is available. The WIM chip within WAP is a good example of an
implementation of storing private keys. The WIM chip is tamper resistant and contains a users
private keys and certificates. The method used by a model device to store the keys and
certificates should also portable. This means that a user should be able to be take the keys with
them if they switch phones. This will allow a user to always have the same keys. If the device is
stolen, other devices on the network should be able to quickly revoke the certificate so that it is
no longer valid. This could be implemented through certificate revocation lists or other methods.
A model device should be able to implement all encryption methods that home PCs are capable
of today. This would either require that the CPUs on these devices become more powerful or a
separate chip may need to be developed that is solely responsible for performing encryption
routines. This could reduce the workload on the device CPU and prevent it from being
overloaded or crashing. By allowing mobile devices to use the same encryption standards that
PCs use we would be ensuring that the devices could interact on the Internet like they were a PC.
This is one of the overriding goals. We want the device to seem like it is a fully fledged PC that
can be stored in your pocket.

In order to prevent loss of data if the device is lost or stolen all data stored on the device should
have the option of being encrypted. This includes address books, calendars, journal entries, and
other documents stored on the phone. If the data is encrypted a lost or stolen device will not
result in the loss of data that could lead to large financial losses. There should be an option to
encrypt data so that the phone is not overly burdened by performing constant encryption routines
on all data.
The mobile device should utilize a secure mobile OS. This mobile device should have the ability
to be updated through a push function provided by the vendor or carrier. A good model to follow
for this is Microsoft’s Automatic Update function. This application allows a home computer to
receive updates without being requested by a user. The only interaction required by the user is to
Approve the installation of the security patches. A similar functionality should be utilized within
a mobile OS. It is impossible to develop a perfect OS. There will always be flaws and there
should be an efficient and effective method implemented to fix these flaws as they appear.
A model device will also not implement new technologies just for the sake of being first to
market with the technology. The manufacturer should research technologies that they implement
within their devices and they should ensure that they will not create security vulnerability on the
device. If vulnerability is found then the manufacturer should find a way to secure the
vulnerability or at the least disable the technology by default so that the security hole is not
enabled without the knowledge of the consumer. Again an example of this is Bluetooth and
Infrared sensors.
User Security
User security is also necessary within a model M-Commerce system. Users must be made aware
of the repercussions of their actions when utilizing their mobile devices. They must understand
the losses that they may incur if proper precautions are not followed. The best method to provide
this is by providing guidance to the user when they purchase the device. One method of
providing guidance would be to provide a pamphlet or booklet along with the device that details
all the security features on the phone and what settings should be utilized. The booklet should
also detail what a user should be aware of when making transactions on their phone. For example

they should be shown how to verify that they are making secure connections and they are not
being tricked by an attacker. This method of providing guidance may not be followed by all
users. In order to ensure that all users receive some sort of guidance, the mobile device should
also have warnings appear on screen when a user performs a potentially harmful action. For
example, if the user attempts to disable the password feature then the phone should make them
aware of the repercussions by displaying a warning on the screen that the user must agree to
before continuing on.
Network Security
Of all components of an M-Commerce system the network is currently the most secure. Carriers
utilize modern encoding and encryption techniques to ensure that their data is secure when
traveling through the air. In order to ensure that this security remains at all times, carriers should
ensure that encryption occurs from end to end in a transaction. This means the data is encrypted
on the device and is never unencrypted until it arrives at its destination. There should not be a
middle man that can read the data.
Conclusion
In conclusion, Wireless carriers can play a very active and important role in the mobile
commerce applications and services due to the fact that a mobile user is going through their
network to perform all mobile transactions. Service providers can also act as content aggregators
but are likely to act as a clearing house for content and application providers in advertising and
distributing their products to its customers. Wireless carriers are also to face challenges involving
how to price mobile commerce services, and because several carriers are likely to be involved in
completing a mobile commerce transaction, another issue is how to divide revenues among
multiple carriers.
There are many important issues that need to be addressed before mobile commerce applications
can be widely deployed. These include the development of new business models for charging
wireless customers and for revenue division among providers, maturity of application software,
middleware support, vendor support and user trust necessary for conducting mobile transactions.
There are some important issues for developers of m-commerce applications.

Aas you can see there are currently many security challenges and weaknesses that exist within
M-Commerce systems. In order to expand the usage of M-Commerce manufacturers, developers,
and wireless carriers need to gain consumer trust by implementing security features into their
devices. They also need to ensure that adding this security features is not overly burdensome to
the consumer. If so the devices and features will never be utilized. If Manufacturers and
Developers develop more secure devices, implement more secure protocols, and ensuring that
users are aware of potential ramifications of their actions then consumer trust will come.
This paper described many of the challenges and weaknesses that need to be overcome. But this
is by no means an all inclusive list. This paper also listed possible suggestions for overcoming
these weaknesses and it detailed what items a model secure M-Commerce system should include.
It is now up to the manufacturers, developers, and carriers to pay attention to the security aspects
of M-Commerce and resolve the issues that exist today.

References
[1] – Peat, Graham “The Promise of M-Commerce: Is it Worth the Risks?”, SafeNet
http://www.safenet-inc.com/library/2/business_brief_mcommerce.pdf
[2] – ePayNews “Statistics for Mobile Commerce”, TrinTech Group
http://www.epaynews.com/statistics/mcommstats.html
[3]- T. Karygiannis, “Wireless Network Security 802.11, Bluetooth, and Handheld Devices”,
HPCC
http://www.hpcc-usa.org/pics/03-pres/karygiannis.pdf
[4]- Yeun, Chan Yeob, “Secure M-Commerce with WPKI”, Toshiba Telecommunications
Research Laboratory
http://www.iris.re.kr/iwap01/program/download/G07.pdf
[5] -Jansen, Wayne A., “Authenticating Users on Handheld Devices”, NIST
http://csrc.nist.gov/mobilesecurity/Publications/PP-AuthenticatingUsersOnPDAs.pdf
[6]- Saarinen, Markku-Juhani “Attacks against the WAP WTLS Protocol”, University of
Jyvaskyla
http://www.freeprotocols.org/harmOfWap/wtls.pdf
[7] – WAP Forum, “Wireless Identity Module”, The WAP Forum
http://www.wapforum.org
[8] - “The Unofficial Independent iMode FAQ”, EuroTechnology
http://www.eurotechnology.com/imode/faq-gen.html
[9] – “Wireless Application Protocol Architecture Specification”, WAP Forum, July 12, 2001
http://www.wapforum.org
[10] – “WAP 2.0 Technical White Paper”, WAP Forum, January 2002
http://www.wapforum.org
[11] – Jeffs, Tamzin Z “Wireless Application Protocol 2.0 Security”, SANS Institute November
2001
http://www.sans.org/rr/papers/download.php?id=159&c=0b2c6c52463249a3c525ab7c2a7b2b3b
[12] - Meeker, Mary “Global Technology Internet Trends” Morgan Stanley, November 15,2005
http://www.morganstanley.com/institutional/techresearch/pdfs/GSB112005.pdf
[13] – Soto, Carlos A , “Hacking Bluetooth” GCN 7/25/05

http://www.gcn.com/print/24_20/36432-1.html
[14] Juul and Jorgensen, “Security Issues in Mobile Commerce Using WAP”, Roskilde
University June 19, 2002
http://medusa.sdsu.edu/network/security/wap-bled.pdf

[15] “iMode Technology”, NTT DoCoMo
http://www.nttdocomo.com/technologies/present/imodetechnology/index.html
[16] Grosche and Knospe, “Secure M-Commerce” Royal Holloway University
http://www.isg.rhul.ac.uk/~scarlet/documents/Secure%20m-commerce%20ECEJ.pdf
[17] Ashley, Hinton, and Vandenwauver “Wired versus Wireless Security: The Internet, WAP,
and I-Mode for E-Commerce” IBM Software Group – Tivoli
http://www.acsac.org/2001/abstracts/thu-1030-b-ashley.html