Using a bioinformatics approach to generate accurate exploit-based signature for polymorphic worms...
-
Upload
mervin-nelson -
Category
Documents
-
view
221 -
download
0
Transcript of Using a bioinformatics approach to generate accurate exploit-based signature for polymorphic worms...

Using a bioinformatics approach to generate accurate exploit-based signature for polymorphic worms
Computers & Security, Vol. 20, Page 827-842, Nov. 2009Authors : Yong Tang, Bin Xiao and Xicheng LuPresent : Jheng-Hen Jiang
2010/10/21 1

Outline
Introduction Related Work Proposed Scheme Experiment Result Conclusions
2010/10/21 2

Introduction
Currently available signature generation approach may fail to create accurate signatures from polymorphic worms. Some invariant parts in polymorphic
worms cannot be extracted. No approach takes into account all
distance restriction between invariant parts.
2010/10/21 3

Related Work
Polymorphic Invariant bytes / Wildcard bytes
Signature Exploit-based / Vulnerability-base
Deployment Network-based / Host-based
2010/10/21 4

Proposed Scheme(1/5)
2010/10/21 5
Multiple Sequence Alignment(MSA) – Primary library
A F E C D M O U G E X
F Q C S M R D O U GK
F Q C S M R D O U GK
A F E C D M O U G E X
3
3
X 1
X 1
X 0
X 0
X (-1)
X (-1)
7
6
2
4
+ ∑ enc |s|
3 X (S - 1)
3 X (S - 1)
1 =
-1 =
1 =
5 =

Proposed Scheme(2/5)
2010/10/21 6
MSA – Library extension

Proposed Scheme(3/5)
2010/10/21 7
MSA – Guide tree construction and progressive alignment
X A B
B 0.12 -
C 0.23 0.32
A
B
C

Proposed Scheme(4/5)
2010/10/21 8
Noise elimination

Proposed Scheme(5/5)
2010/10/21 9
Simplified Regular Expression(SRE) signature transformation
‘\x08’
‘\x25’
‘\x00’
‘\xFF’
‘\xAC’
‘\xAE’
‘\x2F’
‘\x5E’
‘\x3C’
‘\x64’
‘\xCB’
‘\x2A’
‘\x6F’
‘\x08’
‘\xFF’
‘\xAC’
‘\x2F’
‘\x5E’
‘\x3C’
‘\x64’
‘\x7A’
‘\x26’
‘\xEB’
‘\x68’
‘\x5C’
‘\x08’
‘\xFF’
‘\xAC’
‘\x2F’
‘\x5E’
‘\x3C’
‘\x64’
‘\x8B’
‘\xBA’
.* ‘\x08’ .[2] ‘\xFF\xAC’ .[1] ‘\x2F\x5E\x3C\x64’ .*

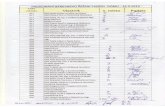
Experiment Result(1/4)
2010/10/21 10
Signature quality

Experiment Result(2/4)
2010/10/21 11
Worm sample needed

Experiment Result(3/4)
2010/10/21 12
Noise toleration

Experiment Result(4/4)
2010/10/21 13

Conclusions Provided a more powerful method to
accurately analyze the intrinsic similarities of worm samples.
IDS can locally generate signatures and can be distributed to others to circumvent further worm damage.
This approach is noise-tolerant and the signatures are more accurate and precise than other method.
2010/10/21 14