USER DEFINED OBJECTS€¦ · These UDOs can be very process-intensive on the E1 servers. Test and...
Transcript of USER DEFINED OBJECTS€¦ · These UDOs can be very process-intensive on the E1 servers. Test and...

We make JD Edwards work better for people and harder for business
GENERAL SECURITY RECOMMENDATIONS
USER DEFINED OBJECTS - UDOS

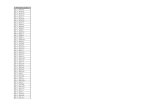
Contents
03
04
05
05
06
06
07
08
08
TABLE OF
Section 01
Section 02
Section 03
Section 04
Section 05
Section 06
Section 07
Section 08
Section 09
INTRODUCTION
UDO SECURITY PLANNING
ASSIGN UDOS OWNER(S)
UNDERSTAND UDOS CREATION AND APPROVAL PROCESS
DEFINE UDOS ACTIONS, VIEWS AND CONTENT
DEFINE ROLE REQUIREMENTS FOR UDOS
MANAGE UDOS THROUGH OMW WEB
TEST UDOS
UDOS SECURITY SET UP

Most Companies face the challenge of managing many E1 security types with various levels of complexity. Unlike any other security types, UDOs have their own action security and approval processes which require a certain level of attention in the way they are implemented in Production.
This document outlines some key information and general recommendations on UDO security which might assist you in securing your own UDOs effectively.
Is your organization ready to embrace UDOs?
Do you have a plan in-place to secure them?
Since the introduction of User Defined Objects (UDOs) with release 9.1, UDOs have evolved and multiplied in the JD Edwards’ objects landscape:• Interest in UDOs has grown quite significantly in the JD Edwards End
Users’ community.• Additional security layers have been added to manage UDOs specifically.
01Introduction
General Security Recommendations 3

There are currently 18 types of UDOs in E1 that can be secured.
CORE UDOs:Without a well-defined security framework in-place, UDOs could become challenging to manage over time. E1 System Performance could potentially be impacted in a Production Environment.
• Identify and assign UDOs’ Owners
• Define key players in the creation and approval process
• Define roles and UDOs Actions
• Define all roles requirements for UDOs
• Test and Manage UDOs through OMW Web
02UDO Security Planning
START DEFINING UDO SECURITY WITH THE FOLLOWING APPROACH:
E1 Pages
CafeOne
Queries
Composed Pages
Personal Forms
E1 Search
Task Search
Images
OneView Reports
Grid Formats
Watch Lists
ORCHESTRATION STUDIO UDOs:
Orchestrator
Service Requests
Rules
White Lists
Notifications
Scheduler
4 General Security Recommendations

Assign UDOs owner(s) within each department or across departments. His/her role is to control, assess and approve UDOs created by users to be shared with others, either publicly or specifically at a role or user level.
Delegate UDOs administration to UDO owners (typically super user or managers who are best equipped to manage UDOs efficiently).Grant UDOs Owners access and permissions to the UDO application administration management P98220U.
03
04
Assign UDOs Owner(s)
Understand UDOs Creation and Approval Process• Understand the steps to approve and share UDOs in P98220U
• Identify the players and define the roles involved in the creation and approval process
• Access P98220U for:
• Approving/Rejecting UDOs for sharing and promotion
• Accessing UDO Content in Composite Application Framework or Composed Pages
CREATE / EDITS()
REQUEST TO SHARE(pending approval)
REFUSED(rework)
RE-EDIT Already Shared(reserved)
APPROVED(share)
WORKFLOW ACTIONS (STATUS)
General Security Recommendations 5

UDOs are personalized objects that users can create for their own use, and share with others, depending on the permissions they and others have been granted.
• Grant the appropriate UDO security permissions to the role(s) by defining who can:
• Create UDOs for personal use
• Create and Publish UDOs for sharing with other users
• Modify Shared UDOs create by other users
• View UDOs
• Access Content in an E1 Composite Application Frame
• Access P00950UO (UDO Security) through P00950/ Form / UDOs: Chose Action, View or Content
• Enable UDOs Features through P00950/ Form / UDOs: Features
05
06
Define UDOs Actions, Views and Content
Define Role requirements for UDOs
• Understand clearly what your role requirements are and define a list of specific “Must Haves” UDOs to include in each role. Define also a list of common UDOs to be shared at a global level (*Public)
• Be selective in what needs to be shared Publicly or at a role level. A common mistake is to grant too many UDOs to a Role or even *Public which can be overwhelming to End Users and somewhat counter-productive
• Stick to the “20/80” Rule. Fewer UDOs assigned to roles is better than too many. Focus on what really matters to users for performing their jobs
• Share /grant UDOs permissions at a Role Level rather than at a user level.
• Manage user exceptions tightly.
6 General Security Recommendations

07Manage UDOs through OMW Web
It is somewhat easy to fall into the trap of creating, approving and publishing most UDOs in Production and ignoring the basic rules and purpose of an “Object Management Cycle”
• Leverage Object Management Workbench for Web (P98220W) and keep your UDOs consistent across all your environments
• UDOs can be packaged and promoted between path codes through OMW Web
• Follow a certain discipline in testing UDOs in lower environments before deploying them to Production. The process takes longer but the results are worth it, and safer.
Create, Share and Modify UDOs Approve UDOs
Secure UDOsShare UDOs across Path Codes
DV
Import/Export
PDPY
OMW Web UDO Project Promotion
STANDARDIZED PROCESS USING WEB BASED TOOLS
General Security Recommendations 7

Certain types of UDOs could have a negative performance impact on an E1 System if they are not defined and tested properly.
• Focus especially on Queries, Watch Lists, E1Searches and One View Reports. These UDOs can be very process-intensive on the E1 servers. Test and validate their performance on a non-production E1 system.
• Set up threshold parameters in the JAS.INI of the E1 Web Server to limit the amount of data returned to the end users through the Web.
• Use an alternative business data source for processing certain UDOs such as OneView Reports if real-time data access is not a mandatory requirement. This will avoid any performance issues caused by the intense data retrieval process generated by ie OneView Reports in Production
• Test UDOs before sharing them. Understand the Object Life cycle management for UDOs to safely test them and deploy them in Production.
08
09
Test UDOs
UDOs Security Set up9.1. High-Level Process
Verify UDOs In P9000 UDCs
Activate UDOFeatures
Verify UDOs In P98230 OMW Config
Verify UDOs In P9800022 Web Objects
Grant UDOAction to Roles/Users
Grant UDOView to Roles/Users
Grant UDO Content ***to Roles/Users
UDOS VERIFICATION:
UDO SECURITY SET-UP IN P00950/FORM/UDOS:
*** Content is Only Valid for E1Composite Application frames with the following content: OBIEEs, URLs, Embedded E1 Forms, OVR
%
8 General Security Recommendations

9.2. Detailed Level Process
9General Security Recommendations

• Verify UDOs in UDC – P9000
• From the home menu, Go to Fast Path and UDC
• Check all UDCs for UDOs exists under Product Code “95” and UDC “UF”
10 General Security Recommendations

• Verify UDOs in Web Object Application – P9800022
• Ensure that UDOs are listed in P0900022
General Security Recommendations 11

• Verify UDOs in OMW Configuration – P98230
• Go to Fast Path – P98230
• Select Allowed Actions
• Verify that “Delete” Action is granted to all appropriate roles and all UDOs
12 General Security Recommendations

• Activate UDOs Features
• Activate UDO Feature in your environment
• From the home menu, Go to Fast Path and enter P00950
• In P00950, Select Feature
General Security Recommendations 13

• Click on the Access Radio Button to Activate or Deactivate UDOS
• Grant the appropriate UDO Action(s) to Roles or Users
14 General Security Recommendations

• For any existing Action entries in the Grid, modify a UDO action for Role(s) by Clicking on one of the Radio Buttons “Create”, “Publish” or “Modify” and activate or de-activate the desired UDO(s)
General Security Recommendations 15

• For Adding a new UDO Action, Click on the Add Button
16 General Security Recommendations

• For Adding a new UDO Action, Click on the Add Button
• Select the appropriate Object Type, Application and Users shown below
• Grant the appropriate Access Level to the Role and validate the permissions
General Security Recommendations 17

• Grant View Access to Roles or Users
• For any existing View entries in the Grid, activate or de-activate a UDO for a Role by Clicking on one of the “View” radio button of the role to be modified
18 General Security Recommendations

• For adding a new “View” Entry, Click on ADD
• Type or Select the Appropriate UDO, Application and Role(s)
General Security Recommendations 19

• Activate “View” Access by clicking on the “View” Radio Button
• Grant the appropriate UDO Content(s) to Roles or Users
20 General Security Recommendations

• For any existing “Content” entries in the Grid, activate or de-activate a UDO for a Role by Clicking on one of the “Access ” radio buttons of the role to be modified
• For Adding a new UDO “Content” Access Permission, Click on the Add Button
General Security Recommendations 21

• Click on the ‘Access” Radio button to Active or De-Activate a content for a specific role
22 General Security Recommendations

• UDO Tables by UDO Type:
9.1. UDO Tables
TABLE Description
F952400 User Generated Contents Detail
F952410 Composite Page
952415 Image
F952420 OneCenter Watchlists Detail
F952425 Notification
F952430 Advance Query
F952435 Dynamic Form Personalization
F952440 Grid Formats Detail
F952445 EnterpriseOne Search
F952450 CafeOne Layout Table
F952455 Scheduler
F952460 Default UDO Detail
F952471 Modified Web Object Metadata
F9524810 Orchestrations
F9524820 Cross Reference
F9524830 Rule
F9524840 Service Requests
F9524850 Whitelist
• UDO Object Librarian tables:
• UDO Repository Tables:
TABLE Description
F9860W Web Object Master Table
F986OWD Web Object Language Descriptions Table
TABLE Description
F98700D Object Dependencies
F98700H Object Acrhive History
F98700R Object Archive Repository
General Security Recommendations 23

ONE COMPANY.ONE SOLUTION.
ERP-ONE.