PacketViper: Addressing the Hidden Killer in Network Security
The Hidden Network Killer
-
Upload
francesco-trama -
Category
Internet
-
view
9 -
download
0
Transcript of The Hidden Network Killer

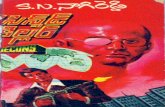
THE HIDDEN NETWORK KILLERFRANCESCO TRAMA / CO-FOUNDER

AGENDA▸ Traffic Volume, Velocity, and Variety
▸ How Traffic Volume Supports Threats
▸ Network Security Practices Today
▸ Decreasing Volume Improves Security
▸ Challenges in today’s security paradigm
▸ PacketViper

TRAFFIC VOLUME, VELOCITY, AND VARIETY

INTERNET WAS BUILT ON A SHARED PLATFORM

TRAFFIC TRENDS EST BY 2020 ‣ Global IP traffic will reach 2.3 ZB per year, or 194 EB
per month
‣ Global IP traffic will increase nearly threefold
‣ Smartphone traffic will exceed PC traffic
‣ IP traffic in North America will reach 59.1 EB per month
‣ IP traffic in Western Europe will reach 28.0 EB per month
‣ IP traffic in Asia Pacific will reach 67.8 EB per month
‣ IP traffic in Latin America will reach 11.6 EB per month
‣ Devices connected to IP networks will be 3X as high as the global population.
Reference: Cisco VNI™ Forecast June 2016

NETWORK SECURITY TODAY
THERE PLENTY OF SECURITY TOOLS. EACH PROVIDE THEIR OWN EXPERTISE TO SECURITY. NO ONE ALONE SOLVES THE SECURITY
PROBLEM!
EACH IMPROVED BY LESS TRAFFIC VOLUME

How Traffic Volume Supports Threats

THIS IS THE REALITY
‣ Protection has always been a short term fix ‣ Software has breadcrumbs to its origins ‣ Upgrades and Patching not equally done ‣ Short term memory ‣ We are all connected!
LET’S SAY IT OUT LOUD! THREATS WILL ALWAYS BE

A New Zero-Day Vulnerability Discovered Each Week In 2015, the number of zero-day vulnerabilities discovered more than doubled to 54, a 125 percent increase from the year before. Or put another way, a new zero-day vulnerability was found every week (on average) in 2015.
Source Symantec: 2016 Internet Security Threat Report

APPLICATION LAYER DDOS AND BOTS
▸ 18 BOTNET INFECTIONS PER SECOND According to the director of FBI’s cyber division, Joseph Demarest,
▸ 2016 perpetrators could slip through standard security challenges, commonly used to filter out attack traffic.
▸ In Q1 2016, the number of such bots mushroomed to 36.6 percent of total bot traffic
▸ Such capabilities, when combined with a legitimate looking HTTP fingerprint, make malicious bots impervious to most common detection methods.
Source: Q1 2016 Global DDoS Threat Landscape Report Mad Skills

500 MILLION Compromised computers per year.
196 COUNTRIESAs stated by the FBI in a recent Senate statement,
“Botnets have caused over $9 Billion in losses to US victims and over $110 Billion in losses globally. Approximately 500 Million computers are infected globally each year, translating into 18 Victims per second”
Source: Global Security, Safety, and Sustainability

DELIVERY PLATFORMS▸ 2 Million + Apple Apps
▸ 2.2 Million + Android Apps
▸ 669,000 Microsoft Apps
▸ 1.1 Billion Websites
▸ 130+ Billion Emails per day
▸ 3 + Billion Users
▸ 7.2 Billion Mobile Devices
▸ Billions Of USB sticks
▸ 6.4 Billion IoT Devices
Sources: Radicati, Windows Central, Statista, US Census

PITFALLS THAT HURT NETWORK SECURITY
‣ Failure to recognize security is about humans
‣ You believe your are seeing all threats
‣ Believing “Top Anything” reports is the complete picture.
‣ Believe Garbage in not Garbage Out
‣ You Have Clear Visibility
‣ You are prepared for the inevitable breach
‣ OPEX Budgets do not determine your network security strength, viability, and effectiveness.

ATTACKERS ARE AWARE OF YOUR NETWORK CHALLENGES!
Stay Small, Nimble, and Humble

NOT UNDERSTANDING OR OVER THINKING THE GLOBAL REACH OF NETWORKS
▸ CDN and ADN’s provide businesses with content and application everywhere capabilities
▸ Low rent cloud providers provide business and hackers global capabilities.
▸ Applications and business are borderless
Forces security teams to loosen perimeter security and nearly abandoned large scale IP prevention

Security devices do not consider the Business of the Internet, rather the Application of the Internet.
Windows Firewall and Port Settings for Client Computers in Configuration Manager
For the management point to notify client computers about an action that it must take when an administrative user selects a client action in the Configuration Manager console, such as download computer policy or initiate a malware scan, add the following as an exception to the Windows Firewall:
Outbound: TCP Port 10123
Remote Control: To use Configuration Manager remote control, allow the following port:
Inbound: TCP Port2701
Wake-Up Proxy: For System Center 2012 Configuration Manager SP1 and later:
Outbound: UDP Port 25536 Outbound: UDP Port 9

‣ Complexity of today’s internet business.
‣ Services provide live data of the latest malicious IP Traffic via cloud or other wise
‣ Management of such large list become cumbersome and weigh security devices down.
‣ Firewalls would reach their limits attempting to handle a large rule base.
ABANDONMENT OF LARGE SCALE IP PREVENTION FACTORS

‣ Softening perimeter rules, ‣ Exposure of portals (VPN, OWA, FTP, ETC) ‣ To restrictions could introduce latency and complexity ‣ Logging is vague and difficult to understand who or what ‣ Inspect everything cause drag on the team, systems, and
causes logging whiteouts
RESULTS

Network Security Practices Today

NETWORK SECURITY TODAY
▸ Deep Packet Inspection ▸ Stateful Inspections ▸ Application Identification ▸ Protocol Analysis and Detection ▸ Blacklist, AutoShun, Honeypot ▸ Content Inspection ▸ Algorithmic Detection ▸ Operational Behavioral Detection ▸ Logging, Alerting

WWW
SSH
TELN
IMAP
FI
RE
WA
LL
IDS
IPS
SSL
APP
SPI
Rule
s
Con
tent
Insp
ectio
ns
Auth
APP
ID
RBL
ID
LOG
/
Aler
t
Mal
war
e In
spec
tions

LOG ANALYZE ALERTTRAFFIC
24X7X365Monitoring and Management Required

Limits Visibility, Accuracy, Dependability
Increases Latency
Hampers threat identification and remediation
Increases Logging, Alerting, False Positives
Increase costs
Adds Complexity, Management time, and Fatigue
VOLUMETRAFFIC
ITS EFFECT TO NETWORK SECURITY

Decreasing Volume Improves Security

REDUCING TRAFFIC VOLUME REDUCES NETWORK SECURITY INSPECTIONS
TSA▸ Less Deep Packet Inspection ▸ Less Stateful Inspections ▸ Less Application Identification ▸ Less Protocol Analysis and Detection ▸ Less Blacklist, AutoShun, Honeypot ▸ Less Content Inspection ▸ Less Algorithmic Detection ▸ Less Operational Behavioral Detection ▸ Less Logging, Alerting

COMMON SENSE APPLICATION USE
IDENTIFYING YOUR INTERNET BUSINESS
VPN
FTP
OWA
CONNECTION
ChinaItalyRussia
Canada

IDENTIFYING YOUR INTERNET BUSINESS
ChinaItalyRussia
Canada
COMMON SENSE APPLICATION USE

IDENTIFYING YOUR INTERNET BUSINESS
Italy
Canada
AmazonBusiness AGoogle
Business DGoogle
COMMON SENSE APPLICATION USE

IDENTIFYING YOUR INTERNET BUSINESS
Italy
Canada
AmazonBusiness AGoogle
Business DGoogle
COMMON SENSE APPLICATION USE

APPLICATION LOCATION PROBABILITY
▸ Does traffic need to come from high risk areas of the world?
▸ What are your operating areas?
▸ Which businesses are within those high risk areas?
▸ What public services are being offered to customers and employees:
▸ VPN, FTP, WEB, MAILINSPECTION
COUNTRYPORT, PROBABILITY
BUSINESSPORT, PROBABILITY
APPLICATION USEPORT, PROBABILITY
LOCATION THREAT FACTORS
NETWORKPORT, PROBABILITY

BUSINESSKEY FACTORS TO REDUCING TRAFFIC
▸ Business Operating Space
▸ Country
▸ Business
▸Network
▸ Threat probability
COLOCATION CLOUD
CN
UK
IT
RU
AU
OPERATING NETWORK
PERMITTED SERVICES
SERVICES
Targeting probability areas of expected traffic vectors eliminates unwanted traffic and reduces perimeter noise.

WWW
VPN
SSH
TELN
IMAP
FTP
HTTP
VPN
SSH
TELNET
IMAP
Less Activity

V
S
T
I
FTPMAIHTVPSSTELIMA
LOG ANALYZE ALERTTRAFFIC
Connections

Challenges in today’s security paradigm

NETWORK SECURITY TODAY
UNFORTUNATELY SECURITY IS NOT ALL UNICORNS AND RAINBOWS
‣ The belief this can be done with existing firewalls (FW/NGFW)
‣ Rules and management efforts would be tremendous
‣ Can not effectively identify the business factors of the traffic
‣ firewalls have limited global sight
‣ There are limits to the amount of rules
‣ Firewalls have limits on the amount of objects and rules
‣ The effort needed within existing firewalls would make it latent
‣ Firewalls are great inspection point, but lack global business perspective
Nuts!

THREAT INTELLIGENCE CONUNDRUM! “WE MUST HAVE THREAT INTELLIGENCE!”▸ “Threat of the Day”
▸ Many threats go unannounced for months and years
▸ Threat intelligence can not look into the future. Many assumption lead to many false positives.
▸ To many threat intelligence sources can/will be overwhelming.
▸ Does your team understand proper key indicators to new or unannounced threats?
▸ Fact is: You have little control over threats
Coming
Off Radar
Cultivating

FRANCESCO TRAMA - CO-FOUNDER
PACKETVIPER - BASED IN PITTSBURGH PA
▸ Advanced IP-Filtering Solution
▸ Address traffic at the perimeter before it enters the security environment
▸ Inline device that replaces nothing, no latency
▸ 5 min install
▸ Patented Advanced IP filtering that addresses the country, company, network space, and threats bi-directionally by network port

WHAT IS PACKETVIPER?
Geo Location Data
Rules Management
Logging & Reporting Engine

REDUCE THE VOLUMEIMPROVE SECURITY
with
www.packetviper.com
855-758-4737