Take Control of the Endpoint Threat Defense Lifecycle
Transcript of Take Control of the Endpoint Threat Defense Lifecycle
Speaker
2
Nathan JennigesHead of Product Management, Endpoint ClientIntel Security5 years in Endpoint and Security Management
Agenda
• Taking Control Of The Endpoint
• Dynamic Endpoint Threat Defense‒ Adaptive Protection
‒ Active Response
• Conclusion
3
The ultimate challenge facing practitioners
Security’s Perfect Storm
5
Increasing Complexity
Threats continue to risewhile mobility and
cloud erode control.
Time Imperative
Comprehension and response cannot
happen fast enough.
Resource Constraints
There’s not enough people or $$$ to throw
at the problem.
Growing need to resolve more threats, faster and with fewer resources
Two prevailing schools of thought
Divided Perspectives On The Solution
6Source: Penn Schoen Berland, 2016
Best-in-Breed
Integrated Platform
Addressing the talent pipeline
Self-integration of proprietary systems
Best-in-Breed
Embracing automation
Open ecosystem-driven integration
Integrated Platform
Source: Penn Schoen Berland, 2016
Better Outcomes With Integrated Platforms
7Decision makers with platforms indicate better outcomes than their counterparts
Integrated Platform
Are more confident, sleep better at night
lose sleep weekly, compared to 57%
zzz 30%
Have faster response times
discover threats in 8 hours, versus 54% 80%
Are better protected
suffered under 5 breaches last year, compared to 55%
78%
7
With integrated endpoint threat defense lifecycle approach
How Can You Minimize Security Risk?
8
Minimize likelihood of breach in first place
Protect
Limit exposure and discover patient zero
faster
Detect101001110101010101101110001010110100111010101
01011
Reduce human effort, time, and cost to fix
Correct
Automatically learn and update protections in real time Adapt
No longer just about threat protection
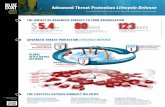
Endpoint Security Evolving….To Threat Defense
10
Traditional Endpoint Protection Platforms
New Behavioral Signature-Less
Protections
Endpoint Detect and Response
(EDR)
Dynamic Endpoint Threat Defense Lifecycle
• Shifts to behavioral models• EDR informed by behaviors• Dynamically learns & adapts
McAfee Global Threat Intelligence
McAfee Threat Intelligence Exchange
Local Cached Intelligence
Classification and Heuristics
Firewall
Web Control
Threat Prevention
Leading the industry with integrated Threat Defense Lifecycle
Dynamic Endpoint Threat Defense
11
Pre-Execution Behavior
Execution Containment
Execution Behavior
Deep Tracing
Remediation
Adapt
Dynamic Endpoint Platform
AdaptiveProtection
Active Response
McAfee ePolicy Orchestrator (ePO)
Broad threat protection with optimized performance
Behavioral machine learning and application containment
Proactively find, investigate, and correct what is missed
Arms threat defense with global insights and powers machine learning intelligence
Foundation: McAfee Global Threat Intelligence
14
We see more, we protect more, and we offer the strongest dedicated 24x7 security threat intelligence.
100 million global threat sensors in over 120 countries
More than 500 researchers
100% uptime services
45+ billion queries/day
Over 1.5 million files and 1 million URLs analyzed per day
500,000 virtual machine sandboxes a day for behavior
Adaptive Protection: Dynamic Application Containment
• Reduces ability of greyware to make malicious changes to the system
• Saves “Patient zero” and thwarts spread
• Minimizes end-user impact as it does not use or require heavy sandbox/VM or app virtualization
• Works online or offline
• Protects without compromising business continuity
15
Containment = Limit or eliminate the ability of greyware to make changes on the endpoint while running endpoint detection analysis
Detects zero-day malware without signatures
Adaptive Protection: Real Protect
1616
What we “think” it is going to do…
Ransomware: CTB-Locker (pre-execution)
Classification is done against an offline Machine Learning model on endpoint.
Ransomware: CTB-Locker (post-execution)
File system, registry and network actions before encryption
What it is “actually” doing
Adaptive Protection In Action
17
Behavioral protections instantly and automatically protect all endpoints
Known Good Likely Good Unknown Suspicious Likely Bad Known Bad
Risk Rating
Social engineeringURL exploit
Real Protect Real ProtectUnknown file tries to execute Static, Local
App ContainmentBlock Bad Behaviors Dynamic, Cloud
Block Download Delete Latent Kill Active Threat Intelligence
Exchange
Find and Convict OnceProtect EverywhereSeconds Not Weeks
No Human Effort Required
Other Endpoints Across the Enterprise
Pre-Execution During Execution During Execution
Active Threat Defense (ATD)File also sent for parallel sandbox analysis
We learn a lot if as a potential threat goes through Protection layers
Intelligence Informs Detect and Response
• It is an unknown app or an unusual behavior of a trusted app
• It did not match any known behavior or exploit filters
• It hid behaviors to avoid static analysis
• It deviated just enough from machine learning algorithms
• It evaded off-box sandbox analysis
• It may have behavior that deviated across endpoints
The protection knowledge informs what we should proactively watch….
19
See, investigate, and respond in seconds, not days or weeks
Dynamic Endpoint with McAfee Active Response
20
• McAfee® ePO™
• Single screen
• Workflow experience
• See the “unknowns”
• Investigate details
• 1 click action
Visibility to potentially malicious activity
Understand suspect activity and impact
1
2
One-click to action on all endpoints3
* Requires McAfee Active Response Cloud Services
1. Find a Threat
• Filter by behavior risk
• View, filter, or search
• Sort by prevalence / age
• Select to investigate
21
2. Investigate a Threat
• Threat intelligence
• Endpoint analytics cloud service
- Unknown processes
- Process relationships
- Commonly abused apps
- File, registry, & IP events
- Login/logout events
• Live search across all endpoints in seconds
22
Risk identification• Persistence• Exfiltration• Injection• Self Protection• Recon• Infiltration• Stealth
3. Taking Action
Action at Three Levels
1. Investigating Action
• Delete files, kill processes
2. Endpoint Action
• Kill & cleanup
3. Global Action
• Kill & cleanup everywhere
• Adapt protection everywhere
23
Take Control Of Your Endpoint Threat Defense
VisibilityTo all defenses in one place
One console, one screen
25Sources: 1) Internal Test Validation on efficacy. 2) 3rd Party Test Validation, AV Comparatives
Take Control Of Your Endpoint Threat Defense
Detect The eye of the threat fasterIn 10 seconds*
26* Based on internal and private testing, subject to network and other environmental latencies
Take Control Of Your Endpoint Threat Defense
Coordinate Automated actionJust 10 seconds*
27* Based on internal and private testing, subject to network and other environmental latencies
Take Control Of Your Endpoint Threat Defense
Increase Total security effectivenessby 30% or more*
29* Based on internal and private testing
Key Takeaways
1. Improved Outcomes With Integrated Threat Defense
2. McAfee Endpoint Security: Innovation, Behavioral, Signature-Less
3. McAfee Active Response: Integrated, 1 Click to Correct & Adapt
30
Resolve more threats …
… with fewer resources.
… faster …
Questions & Answers
Upcoming Webinars:Stop Targeted Attacks with Endpoint Security Adaptive ProtectionTake Corrective Action In Seconds with McAfee Active Response
Learn More at:www.mcafee.com/endpoint-protectionwww.mcafee.com/movetoENSwww.mcafee.com/ETDR
31
Intel and the Intel and McAfee logos are trademarks of Intel Corporation in the US and/or other countries. Other marks and brands may be claimed as the property of others. The product plans, specifications and descriptions herein are provided for information only and subject to change without notice, and are provided without warranty of any kind, express or implied. Copyright © 2016 Intel Corporation.
New Endpoint Suites Overview
Endpoint Threat Protection
Complete Endpoint Threat Protection
ePolicy Orchestrator
Threat Prevention Module (OAS / ODS, Access Protection, Exploit Protection, Intrusion Prevention)
Firewall Module(Application Aware Firewall, Domain and DNS Blocking, Access Control)
Web Control Module (Site Ratings / Categorization, Browser Control, URL Filtering)
Device Control
Email Security
Application Control for Desktop
Adaptive Threat Protection Module (Dynamic Application Containment, Real Protect)
Threat Intelligence Exchange
McAfee Active Response
Licensing Perpetual, Per Node Perpetual, Per Node
Protection Suites Add-On Suites
Endpoint Threat Defense
Endpoint ThreatDefense and Response
Perpetual, Per Node Perpetual, Per Node 76