Ramnish Singh IT Advisor Microsoft Corporation. Agenda Managing IT Infrastructure Heterogeneous...
-
date post
18-Dec-2015 -
Category
Documents
-
view
227 -
download
2
Transcript of Ramnish Singh IT Advisor Microsoft Corporation. Agenda Managing IT Infrastructure Heterogeneous...

Ramnish SinghRamnish SinghIT AdvisorIT AdvisorMicrosoft CorporationMicrosoft Corporation

AgendaAgenda
Managing IT InfrastructureManaging IT Infrastructure
Heterogeneous managementHeterogeneous management
InteroperabilityInteroperability


Source: IDC 2002, Microsoft Primary Quantitative Research. 400 30-minute phone surveys of IT professionals in data centers with 25 Source: IDC 2002, Microsoft Primary Quantitative Research. 400 30-minute phone surveys of IT professionals in data centers with 25 or more serversor more servers
Over 60% of TCO over a 5-Over 60% of TCO over a 5-year period driven by year period driven by peoplepeople costs costs
00
1010
2020
3030
4040
5050
6060
7070
Staff CostsStaff Costs DowntimeDowntime TrainingTraining SoftwareSoftware HardwareHardware
Lack of automation Lack of automation impacts all facets of IT impacts all facets of IT
Degree of Automation:Degree of Automation:
53%53% 24%24% 23%23%
54%54% 17%17% 29%29%
56%56% 17%17% 28%28%
58%58% 18%18% 24%24%
60%60% 16%16% 24%24%
62%62% 14%14% 25%25%
0%0% 10%10% 20%20% 30%30% 40%40% 50%50% 60%60% 70%70% 80%80% 90%90% 100%100%Percent of ResponsesPercent of Responses
Security MgmtSecurity Mgmt
NetworkNetwork
Event Event
Performance Performance
Storage Storage
Change/ConfigChange/Config
ManualManual ScriptsScripts Automated ToolsAutomated Tools

Infrastructure Optimization ModelInfrastructure Optimization Model
ManualManualadministration,administration,
UncoordinatedUncoordinateddesktopsdesktops
Full automationFull automation
Business-Business-linked SLAslinked SLAs
LimitedLimitedInfrastructure/Infrastructure/just desktopsjust desktops
Antivirus onAntivirus ondesktopsdesktops
Centralized Centralized firewallfirewall
Internal DNS Internal DNS and DHCPand DHCP
Remote Remote AccessAccess
IpSec server IpSec server isolationisolation
Monitoring Monitoring of serversof servers
Firewall on Firewall on servers and servers and desktopsdesktops
Secure Secure wireless wireless networkingnetworking
Service level Service level monitoring monitoring on desktopson desktops
Active Active Directory for Directory for AuthenticatioAuthentication and n and Authorization Authorization onlyonly
Directory tools Directory tools for central for central administration administration of configur-of configur-ations and ations and securitysecurity(Group Policy)(Group Policy)
Centrally Centrally manage users manage users provisioning provisioning across across heterogeneouheterogeneous systesms systesm
LimitedLimitedInfrastructure/Infrastructure/just desktopsjust desktops
LimitedLimitedInfrastructure/Infrastructure/just desktopsjust desktops
Automated Automated patch Mgmnt patch Mgmnt (WU, SUS, (WU, SUS, SMS)SMS)
Defined set of Defined set of standard standard basic imagesbasic images
Primary desk-Primary desk-top OS istop OS isWinXP orWinXP orWin2kWin2k
Automated Automated software software distribution, distribution, Mgmnt Mgmnt and trackingand tracking
Manual Manual Application Application Compatibility Compatibility testingtesting
Manual Manual reference reference image systemimage system
Automated Automated patch Mgmnt patch Mgmnt for serversfor servers
Automated Automated application application compatibility compatibility testingtesting
Automated Automated reference reference image systemimage system
LimitedLimitedInfrastructure/Infrastructure/just desktopsjust desktops
Backup/Backup/restore on all restore on all serversservers
Backup/restore Backup/restore on all servers on all servers plus SLAplus SLA
Backup Backup restore on all restore on all servers and servers and desktop data desktop data plus SLAplus SLA
Security of Security of mobile mobile devices devices
Run AV on Run AV on serversservers
SPAM SPAM blocking on blocking on serversservers
• Real-time Real-time connection connection filteringfiltering
• Secure Secure anywhere mail anywhere mail accessaccess
• Unified Unified directory for directory for email & accessemail & access
Secured MessagingSecured Messaging
Managed IT Managed IT Infrastructure Infrastructure with some with some automationautomation
Managed Managed and and consolidated consolidated ITITInfrastructurInfrastructuree
Backup and RestoreBackup and RestoreDesktop LifecycleDesktop LifecycleSecurity, Networking and MonitoringSecurity, Networking and MonitoringIdentity and Access MgmntIdentity and Access Mgmnt

Uninterrupted AccessUninterrupted Access Active DirectoryActive Directory Group PolicyGroup Policy Offline FoldersOffline Folders Synchronization ManagerSynchronization Manager Enhancements to the Windows ShellEnhancements to the Windows Shell Redirected FoldersRedirected Folders Disk Quotas Disk Quotas
Intellimirror TechnologiesIntellimirror TechnologiesConsistent EnvironmentConsistent Environment Active DirectoryActive Directory Group PolicyGroup Policy Offline FoldersOffline Folders Roaming User ProfilesRoaming User Profiles Redirected FoldersRedirected Folders Enhancements to the Windows ShellEnhancements to the Windows Shell Group Policy Software Installation Group Policy Software Installation
Minimized User DowntimeMinimized User Downtime Active DirectoryActive Directory Group PolicyGroup Policy Windows Installer ServiceWindows Installer Service Add/Remove Programs in Control Add/Remove Programs in Control
PanelPanel Group Policy Software Installation Group Policy Software Installation
Minimized Data LossMinimized Data Loss Active DirectoryActive Directory Group PolicyGroup Policy Roaming User ProfilesRoaming User Profiles Redirected FoldersRedirected Folders Offline Folders Offline Folders

Group PolicyGroup Policy
Enable one-to-many management of Enable one-to-many management of users and computers throughout the users and computers throughout the enterprise.enterprise.
Automate enforcement of IT policies.Automate enforcement of IT policies. Simplify administrative tasks, such as Simplify administrative tasks, such as
system updates and application system updates and application installations.installations.
Consistently implement security Consistently implement security settings across the enterprise.settings across the enterprise.
Efficiently implement standard Efficiently implement standard computing environments for groups computing environments for groups of users.of users.

Group Policy – CapabilitiesGroup Policy – Capabilities
Registry-based PolicyRegistry-based Policy Security Settings Security Settings Software RestrictionsSoftware Restrictions Software Distribution and InstallationSoftware Distribution and Installation Computer and User Scripts Computer and User Scripts Roaming User Profiles Roaming User Profiles Redirected Folders Redirected Folders Offline Folders Offline Folders Internet Explorer MaintenanceInternet Explorer Maintenance

Shared Computer Toolkit for Windows Shared Computer Toolkit for Windows XP XP
Defend shared computers from Defend shared computers from unauthorized changes to the hard unauthorized changes to the hard diskdisk
Restrict untrusted users from system Restrict untrusted users from system settingssettings
Enhance the user experienceEnhance the user experience

SMS 2003 CapabilitiesSMS 2003 Capabilities
Application Application DeploymentDeployment
AssetAssetManagementManagement
SecuritySecurityPatchPatch
ManagementManagement
LeveragingLeveragingWindows Windows
Management Management ServicesServices
Support forSupport forthe Mobile the Mobile WorkforceWorkforce

Application Application DeploymentDeployment
SMS 2003 SMS 2003 DeliversDelivers
Delivery of large-scale projects in a Delivery of large-scale projects in a timely and inexpensive mannertimely and inexpensive manner
Provisioning of the right services and Provisioning of the right services and applications to end-usersapplications to end-users
Quickly and easily - in support of Quickly and easily - in support of business requirementsbusiness requirements
Comprehensive solution for critical Comprehensive solution for critical application deliveryapplication delivery Plan, test, deploy and analyze applicationsPlan, test, deploy and analyze applications Reliably and easily Reliably and easily To the right place and at the right timeTo the right place and at the right time
Business Business DemandsDemands

Reduction in hardware and software Reduction in hardware and software asset costsasset costs
Software license complianceSoftware license compliance
Reduced software costs throughReduced software costs through Ability to track and report on compliance Ability to track and report on compliance Application installation and Application installation and
usage informationusage information
Asset ManagementAsset Management
SMS 2003 SMS 2003 DeliversDelivers
Business Business DemandsDemands

Security Patch ManagementSecurity Patch Management
Tools and processes toTools and processes to Identify critical patchesIdentify critical patches Determine vulnerable systemsDetermine vulnerable systems Deliver patches reliably and quicklyDeliver patches reliably and quickly Accurately report delivery statusAccurately report delivery status
A secure Windows environment through A secure Windows environment through Collection of critical patch information Collection of critical patch information Vulnerability assessment of existing environmentVulnerability assessment of existing environment Quick and easy deployment of patchesQuick and easy deployment of patches Targeted delivery of patchesTargeted delivery of patches Verification and reporting on patch deployment Verification and reporting on patch deployment
SMS 2003 SMS 2003 DeliversDelivers
Business Business DemandsDemands

MobilityMobility
Capability to meet mobile Capability to meet mobile workforce needsworkforce needs Provides critical IT business servicesProvides critical IT business services Extends asset management to mobile devicesExtends asset management to mobile devices Delivers relevant business applications Delivers relevant business applications
to mobile devicesto mobile devices
Support for roaming and infrequently Support for roaming and infrequently connected mobile usersconnected mobile users
Delivery of critical business services Delivery of critical business services and applications—reliably and timelyand applications—reliably and timely
SMS 2003 SMS 2003 DeliversDelivers
Business Business DemandsDemands

Windows Management Windows Management Services IntegrationServices Integration
Windows compliance Windows compliance Windows XP and Windows Server 2003 CertificationWindows XP and Windows Server 2003 Certification
Optimal integration of Windows management services Optimal integration of Windows management services Active Directory simplifies SMS planning and deploymentActive Directory simplifies SMS planning and deployment Core Windows Services Integration Core Windows Services Integration
Windows Installer Service (MSI) Windows Installer Service (MSI) Windows Management Instrumentation (WMI)Windows Management Instrumentation (WMI)
Reduces costs through leveraging existing Reduces costs through leveraging existing infrastructure and capabilitiesinfrastructure and capabilities
Reduced operational costs for Reduced operational costs for managing ITmanaging IT
Leveraging of existing infrastructureLeveraging of existing infrastructure
SMS 2003 SMS 2003 DeliversDelivers
Business Business DemandsDemands

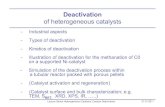
AgendaAgenda
Managing IT InfrastructureManaging IT Infrastructure
Heterogeneous managementHeterogeneous management
InteroperabilityInteroperability

Operation Management Operation Management IssuesIssues
““I need an I need an enterprise-ready enterprise-ready
solution.”solution.”
““Help meHelp merealize my IT realize my IT
investments.”investments.”
““Help me Help me reduce reduce incident incident
management management costs.”costs.”
““Help me Help me protect my IT protect my IT environment.”environment.”
““Help me Help me understand what understand what
events are events are priority.”priority.”
““Help me Help me monitor monitor
applications applications reliably.”reliably.”
Microsoft Operation Manager 2005 delivers

Microsoft Operations Manager Microsoft Operations Manager 20052005
36 Product Connectors36 Product Connectors
48 Microsoft Applications48 Microsoft Applications
15 SMS Add-ins15 SMS Add-ins
189 Management Packs189 Management Packs
157 3157 3rdrd Party Solutions Party Solutions

MOM 2005 CapabilitiesMOM 2005 CapabilitiesStay AwareStay Aware
EffectivelyEffectivelyRespondRespond
Be Be AccountaAccounta
bleble

Identifying IT health issues before Identifying IT health issues before they become problemsthey become problems
Provide visibility to critical resourcesProvide visibility to critical resources Quick DeploymentQuick Deployment
Out of the box expertise with minimal Out of the box expertise with minimal configurationconfiguration
Consoles provides proactive health Consoles provides proactive health understandingunderstanding
Rapidly deploy to identify issues Rapidly deploy to identify issues fasterfaster
Stay AwareStay Aware
MOM 2005 MOM 2005 DeliversDelivers
Business Business DemandsDemands

Effectively RespondEffectively Respond
Improvement in operational Improvement in operational efficiencyefficiency
Accurate and effective response to Accurate and effective response to issuesissues
In-the-box application expertise In-the-box application expertise and operational knowledgeand operational knowledge
Actionable best practicesActionable best practices
MOM 2005 MOM 2005 DeliversDelivers
Business Business DemandsDemands

Be AccountableBe Accountable
Robust ReportingRobust Reporting Connectivity into Management Connectivity into Management
FrameworksFrameworks Information delivery vehicleInformation delivery vehicle
Value from ITValue from IT Accountability from ITAccountability from IT Meeting and exceeding of Meeting and exceeding of
Service Level AgreementsService Level Agreements
MOM 2005 MOM 2005 DeliversDelivers
Business Business DemandsDemands

Heterogeneous Heterogeneous managementmanagement

AgendaAgenda
Managing IT InfrastructureManaging IT Infrastructure
Heterogeneous managementHeterogeneous management
InteroperabilityInteroperability

The Need for InteroperabilityThe Need for Interoperability Heterogeneity is the standard. Heterogeneity is the standard.
The reality is that mixed UNIX/Windows environments The reality is that mixed UNIX/Windows environments are a fact of lifeare a fact of life
Interoperability is a key concern.Interoperability is a key concern. The increased existence of UNIX and Windows-based The increased existence of UNIX and Windows-based
environments requires a greater need and demand environments requires a greater need and demand for interoperabilityfor interoperability
Need to leverage existing investmentsNeed to leverage existing investments Although IT spending is slowly gaining momentum, IT Although IT spending is slowly gaining momentum, IT
managers continue to need to do more with less. managers continue to need to do more with less.

Services for Services for NetWareNetWare
ServicesServicesforfor
MacintoshMacintosh
ActiveActiveDirectoryDirectory
Host Host IntegrationIntegration
ServerServer
Services forServices forUNIXUNIX
AppAppservices:services:OLE DB,OLE DB,ADO,ADO,ODBC,ODBC,XML,XML,SOAPSOAP
Meta-Meta-directorydirectoryServicesServices
IPXIPX
TCP/IPTCP/IP
PKIPKI
LDAPLDAPDHCPDHCP
DNSDNS
WBEMWBEM
XMLXML
HTTPHTTP
KerberosKerberos
MacintoshMacintosh
IBM,IBM,Amdahl,Amdahl,
HitachiHitachi
Sun Solaris, HP/UX,Sun Solaris, HP/UX,Linux, Tru64, IBM AIXLinux, Tru64, IBM AIX
SQL Server,SQL Server,Oracle,Oracle,Informix,Informix,IBM DB2IBM DB2XML/SOAP web XML/SOAP web servicesservices
NetWareNetWare
Novell NDS,Novell NDS,Exchange,Exchange,UNIX NIS,UNIX NIS,iPlanet,iPlanet,NovellNovellGroupwise,Groupwise,Lotus NotesLotus Notes
BizTalkBizTalk
WindowsWindowsBuilt onBuilt on
InteroperabilityInteroperabilityStandardsStandards
Broad InteroperabilityBroad Interoperability

Windows Services For Windows Services For UNIXUNIX
Windows Windows FilesFiles
Windows Windows FoldersFolders
Windows Windows ServerServer
Windows Windows WorkstationWorkstation
PC LaptopPC Laptop
SQL ServerSQL ServerDatabaseDatabase
WindowsWindowsApplicationApplicationUNIXUNIX
FilesFiles
UNIXUNIXDatabaseDatabase
UNIXUNIXServerServer
UNIXUNIXWorkstationWorkstation
UNIXUNIXFoldersFolders
UNIXUNIXApplicationApplication
UNIXUNIXWorkstationWorkstation
(Interix SDK, .NET Framework)(Interix SDK, .NET Framework)
ExtensibilityExtensibility
InteroperabilityInteroperability(NFS, NIS, (NFS, NIS,
Active DirectoryActive Directory
Integration)Integration)
IntegrationIntegration(Interix Subsystem)(Interix Subsystem)

Services For UNIX 3.5 Services For UNIX 3.5 Focused on two major “pain” areasFocused on two major “pain” areas
Seamless UNIX / Windows InteroperabilitySeamless UNIX / Windows Interoperability
UNIX to Windows Application PortabilityUNIX to Windows Application Portability UNIX Tools: C, C++, Fortran, scripts, build toolsUNIX Tools: C, C++, Fortran, scripts, build tools Interix UNIX subsystemInterix UNIX subsystem
Leverage existing UNIX skills, methods and Leverage existing UNIX skills, methods and codecode
””Best System Integration” Award - Best System Integration” Award - LinuxWorld 2003LinuxWorld 2003
NFS Client, Server, NFS Client, Server, GatewayGateway
User Name Mapping User Name Mapping ServerServer
Bi-directional Password Bi-directional Password SyncSync
NIS ServerNIS Server
Korn, Bourne, C ShellKorn, Bourne, C Shell Over 350 UNIX UtilitiesOver 350 UNIX Utilities Telnet Server and Telnet Server and
ClientClient

NFSNFS
File Sharing with UNIXFile Sharing with UNIX Server for NFS Server for NFS
UNIX Clients Using Windows Shared FilesUNIX Clients Using Windows Shared Files Client for NFSClient for NFS
Windows Client Using UNIX Shared FilesWindows Client Using UNIX Shared Files Gateway for NFSGateway for NFS
Serve UNIX Shared Files as Serve UNIX Shared Files as Windows SharesWindows Shares

NFSNFS
NFS enables access to shared files and folders NFS enables access to shared files and folders between UNIX and Windowsbetween UNIX and Windows
UNIXUNIXServerServer
Windows Windows ServerServer
Windows Windows WorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows ServerServer
UNIXUNIXServerServer
UNIXUNIXWorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows WorkstationWorkstation
Windows Windows WorkstationWorkstation

Server For NFSServer For NFS
Server for NFS allows a UNIX network access to shared files Server for NFS allows a UNIX network access to shared files and folders on a Windows serverand folders on a Windows server
UNIXUNIXServerServer
Windows Windows ServerServer
Windows Windows WorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows ServerServer
UNIXUNIXServerServer
UNIXUNIXWorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows WorkstationWorkstation
Windows Windows WorkstationWorkstation
Server for Server for NFSNFS
Server for Server for NFSNFS

Client For NFSClient For NFS
Client for NFS allows a Windows network access to shared files Client for NFS allows a Windows network access to shared files and folders on a UNIX serverand folders on a UNIX server
UNIXUNIXServerServer
Windows Windows ServerServer
Windows Windows WorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows ServerServer
UNIXUNIXServerServer
UNIXUNIXWorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows WorkstationWorkstation
Windows Windows WorkstationWorkstation
Client for Client for NFSNFS
Client for Client for NFSNFS
Client for Client for NFSNFS
Client for Client for NFSNFS
Client for Client for NFSNFS

Gateway For NFSGateway For NFS
Gateway for NFS translates NFS to SMB, eliminating the need Gateway for NFS translates NFS to SMB, eliminating the need for Client for NFS on many computersfor Client for NFS on many computers
UNIXUNIXServerServer
Windows Windows ServerServer
Windows Windows WorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows ServerServer
UNIXUNIXServerServer
UNIXUNIXWorkstationWorkstation
UNIXUNIXWorkstationWorkstation
Windows Windows WorkstationWorkstation
Windows Windows WorkstationWorkstation
NFS NFS GatewayGateway

Mapping ServerMapping Server
Map Windows User and Group Accounts Map Windows User and Group Accounts to UNIXto UNIX
Performance ImprovementsPerformance Improvements Cluster AwareCluster Aware Group Membership Limit Group Membership Limit
Dynamically setDynamically set Redundant Mapping ServerPoolRedundant Mapping ServerPool .maphost support.maphost support

Server For NISServer For NIS
NIS ClientsNIS Clients
UNIX NIS ServersUNIX NIS Servers
MasterMaster SlaveSlave
Windows ServersWindows Servers
Makes a Windows 2000 or Windows Server Makes a Windows 2000 or Windows Server 2003 AD a NIS master server2003 AD a NIS master server
SlaveSlave

Server For NISServer For NIS
UNIX NIS ServersUNIX NIS Servers Windows ServersWindows Servers
NIS ClientsNIS Clients
SlaveSlave SlaveSlave SlaveSlave MasterMaster

Password SynchronizationPassword Synchronization
Two-way between Windows and UNIXTwo-way between Windows and UNIX Support PlatformsSupport Platforms
HP-UX 11iHP-UX 11i Sun Solaris 7, Solaris 8Sun Solaris 7, Solaris 8 IBM AIX 5L 5.2IBM AIX 5L 5.2 Red Hat Linux 6.2 and higherRed Hat Linux 6.2 and higher
BenefitsBenefits LoggingLogging DebuggingDebugging MD5 SupportMD5 Support Supports 65,000 usersSupports 65,000 users Improved data migration timesImproved data migration times Reduced administration leading to lower TCOReduced administration leading to lower TCO

UNIX Sign-On AuthenticationUNIX Sign-On Authentication /etc/passwd, /etc/shadow/etc/passwd, /etc/shadow NIS, NIS+NIS, NIS+ iPlanet, other LDAP-compatible iPlanet, other LDAP-compatible
directoriesdirectories Kerberos v5 (MIT, Heimdal)Kerberos v5 (MIT, Heimdal) PKI Certificates, smart cardsPKI Certificates, smart cards All enabled through PAM (Pluggable All enabled through PAM (Pluggable
Authentication Modules)Authentication Modules)
Integrating UNIX with ADIntegrating UNIX with ADauthentication (AuthN) and authorization (AuthZ)authentication (AuthN) and authorization (AuthZ)
Windows Sign-On Authentication Windows Sign-On Authentication Kerberos v5Kerberos v5 Public Key Infrastructure (PKI) andPublic Key Infrastructure (PKI) and
certificatescertificates Smart cardsSmart cards NTLMv2NTLMv2
UNIX AuthorizationUNIX Authorization Based on UID, GIDBased on UID, GID No embodiment; directly retrieved viaNo embodiment; directly retrieved via
getpwnam(), getpwuid(), getpwnam(), getpwuid(), getgrnam(), getgrgid()getgrnam(), getgrgid()
Many stores:Many stores: /etc/passwd and /etc/group/etc/passwd and /etc/group NIS, NIS+NIS, NIS+ iPlanet, other LDAP directoryiPlanet, other LDAP directory
No centralized AuthZ mechanism No centralized AuthZ mechanism (SRM)(SRM)
ACL structures, capabilities vary ACL structures, capabilities vary between platformsbetween platforms
Windows Authorization Windows Authorization Based on SIDsBased on SIDs AuthZ data embodied in Security AuthZ data embodied in Security
TokenToken Win2K and up: Authorization store is Win2K and up: Authorization store is
ADAD Windows PAC attached to Windows PAC attached to
Kerberos ticketKerberos ticket Securable objects possess an ACLSecurable objects possess an ACL
Fine-grained access rightsFine-grained access rights Granted or revoked by SIDGranted or revoked by SID
Security Reference Monitor (SRM) Security Reference Monitor (SRM) performs authorizationperforms authorization

Integrating UNIX and Integrating UNIX and Windows Sign-On Windows Sign-On AuthenticationAuthentication Ideal: Kerberos integration using ADIdeal: Kerberos integration using AD
Single mechanism, store for AuthNSingle mechanism, store for AuthN Unifies policy for passwords, account Unifies policy for passwords, account
lockoutlockout Windows PAC available everywhereWindows PAC available everywhere
Kerberos peer realm trustKerberos peer realm trust Windows uses AD KerberosWindows uses AD Kerberos Unix systems use UNIX KerberosUnix systems use UNIX Kerberos Trust relationship establishedTrust relationship established But… UNIX tickets have no Windows PACBut… UNIX tickets have no Windows PAC

Integrated Sign-On cont’dIntegrated Sign-On cont’d
What about LDAP Authentication?What about LDAP Authentication? LDAP itself doesn’t do authenticationLDAP itself doesn’t do authentication Performance, scalability limitationsPerformance, scalability limitations No Windows PACNo Windows PAC Windows requires AD as LDAP providerWindows requires AD as LDAP provider
Password SynchronizationPassword Synchronization MIISMIIS SFU Password SyncSFU Password Sync Not really single sign-on anymoreNot really single sign-on anymore

Integrating UNIX and Integrating UNIX and Windows Authorization via Windows Authorization via ADAD RFC 2307 or SFU 3.5 schema to hold RFC 2307 or SFU 3.5 schema to hold
UNIX-specific authZ infoUNIX-specific authZ info Single location for user, group dataSingle location for user, group data Simplified provisioning, Simplified provisioning,
deprovisioningdeprovisioning Unified policyUnified policy Can enable application authZ Can enable application authZ
scenariosscenarios

Integrated AuthZ cont’dIntegrated AuthZ cont’d
LDAP Directory synchronizationLDAP Directory synchronization Multiple policiesMultiple policies Synchronization delaysSynchronization delays Increased complexity of config, opsIncreased complexity of config, ops Provides infrastructure for LDAP-enabled Provides infrastructure for LDAP-enabled
application authZ scenariosapplication authZ scenarios UNIX-specific directory may be better UNIX-specific directory may be better
tuned for UNIX behaviorstuned for UNIX behaviors

More SolutionsMore Solutions
LDAP directoriesLDAP directories Use MIIS or other products to Use MIIS or other products to
synchronize attributes, e.g. passwordssynchronize attributes, e.g. passwords Each new directory increases costs for Each new directory increases costs for
management, hardware, etc.management, hardware, etc. Database, flat fileDatabase, flat file
MIIS, other products typically have MIIS, other products typically have adapters that can do thisadapters that can do this

The Ideal WorldThe Ideal World
IT ProIT Pro All users are managed in Active DirectoryAll users are managed in Active Directory AD has strong user policy enforcementAD has strong user policy enforcement User passwords safe in ADUser passwords safe in AD
DeveloperDeveloper Kerberos 5 available on most enterprise platformsKerberos 5 available on most enterprise platforms Secure authenticationSecure authentication Protect application dataProtect application data AD is single source of authorization dataAD is single source of authorization data
User ExperienceUser Experience Authentication based on one user account in ADAuthentication based on one user account in AD Transparent authentication to applications (SSO)Transparent authentication to applications (SSO)

Kerberos config the hard Kerberos config the hard wayway Step 1:Step 1: Create UNIX user accounts in Create UNIX user accounts in
Active DirectoryActive Directory Step 2:Step 2: Create UNIX workstation Create UNIX workstation
accounts in Active Directoryaccounts in Active Directory Step 3:Step 3: Create Keytab files for the UNIX Create Keytab files for the UNIX
workstationsworkstations Step 4:Step 4: Transfer & install the keytab file Transfer & install the keytab file
on the UNIX Workstationon the UNIX Workstation Step 5:Step 5: Configure the pam.conf fileConfigure the pam.conf file Step 6:Step 6: Configure the krb5.conf fileConfigure the krb5.conf file

LDAP config the hard wayLDAP config the hard way
Step 1: Extend AD schema to hold Step 1: Extend AD schema to hold UNIX authZ informationUNIX authZ information
Step 2: Provision UNIX users and Step 2: Provision UNIX users and groupsgroups
Step 3: Configure UNIX ldap client to Step 3: Configure UNIX ldap client to connect to ADconnect to AD
Step 4: Configure nss_ldap to use Step 4: Configure nss_ldap to use appropriate attributes in ADappropriate attributes in AD

What you getWhat you get User can logon with AD account and get User can logon with AD account and get
Kerb ticketsKerb tickets Use klist to see TGTUse klist to see TGT TGT used to authenticate to appsTGT used to authenticate to apps UNIX uid and gid values retrieved from ADUNIX uid and gid values retrieved from AD No longer need most of /etc/passwd, No longer need most of /etc/passwd,
/etc/group/etc/group

What you What you don’t don’t getget
No access to Windows PACNo access to Windows PAC No off-line TGT cacheNo off-line TGT cache No off-line cache of authZ dataNo off-line cache of authZ data No on-line cache of authZ dataNo on-line cache of authZ data
Serious issue due to UNIX behaviorSerious issue due to UNIX behavior Heavy load on DC, networkHeavy load on DC, network

Vintela Authentication ServicesVintela Authentication Services UNIX/Linux security systems UNIX/Linux security systems
integrated into Active Directoryintegrated into Active Directory No synchronization between systems, all No synchronization between systems, all
credentials reside within Active Directorycredentials reside within Active Directory Authentication through KerberosAuthentication through Kerberos UNIX IdM using RFC 2307 schemaUNIX IdM using RFC 2307 schema
Single login and password for Single login and password for Windows, UNIX and Linux applications, Windows, UNIX and Linux applications, resourcesresources
All LDAP communication secured All LDAP communication secured through Kerberos – no SSL overheadthrough Kerberos – no SSL overhead
Single point of account management Single point of account management through Active Directory – MMC snap-through Active Directory – MMC snap-inin
http://www.vintela.comhttp://www.vintela.com


© 2005 Microsoft Corporation. All rights reserved.This presentation is for informational purposes only. Microsoft makes no warranties, express or implied, in this summary.