IPv6 for Cert Nuts
description
Transcript of IPv6 for Cert Nuts


IPv6 for Cert Nuts BRKCRT-9344
Scott Morris & Keith Barker

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Tour Guide
Scott Morris, CCIEx4 #4713, CCDE #2009::13, JNCIEx2 – CCIE Route & Switch, ISP/Dial, Security, Service Provider
– Cisco Certified Design Expert
– Juniper Networks JNCIE-M #153 and JNCIE-ER #102
– CISSP, CCVP and several other random things!
– Email: [email protected]
– Twitting: @ScottMorrisCCIE
3

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Tour Guide
Keith Barker, CCIEx2 #6783, CCDP, CCSI – CCIE Route & Switch, Security – Cisco Certified Design Professional – CISSP and several other random things! – Email: [email protected] – Twitting: @KeithBarkerCCIE
4

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Journey
IPv6 Certification Agenda Addressing & Formats Configuration Basics Headers Neighbor Discovery Transition & Deployments Routing Advanced Stuff
5

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Agenda
Setting the stage – Why the mastery of IPv6 skills is so important in the real world – What we know…or think we know, can be a factor in our mastery Key elements in successful execution out knowledge
– What is important for certification? – Where do certs end and the real world begin? Implementing the protocol(s) that we know and love already Extending our IPv6 knowledge
– How a network will work start to finish
6

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Certification Agenda
CCNA Describe the technological requirements for running IPv6 in conjunction with
IPv4 (including: protocols, dual stack, tunneling, etc.). Describe IPv6 addresses
7

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Certification Agenda CCNP Implement an IPv6 based solution, given a network design and a set of requirements
– Determine network resources needed for implementing IPv6 on a network – Create an IPv6 implementation plan – Create an IPv6 verification plan – Configure IPv6 routing – Configure IPv6 interoperation with IPv4 – Verify IPv6 solution was implemented properly using show and debug commands – Document verification results for an IPv6 implementation plan
Implement an IPv4 or IPv6 based redistribution solution
– Create a redistribution implementation plan based upon the results from a redistribution analysis – Create a redistribution verification plan – Configure a redistribution solution – Verify that a redistribution was implemented – Document results of a redistribution implementation and verification plan – Identify the differences between implementing an IPv4 and IPv6 redistribution solution
8

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Certification Agenda
CCIE Implement IPv6
Implement IP version 6 (IPv6) addressing and different addressing types Implement IPv6 neighbor discovery Implement basic IPv6 functionality protocols Implement tunneling techniques Implement OSPF version 3 (OSPFv3) Implement EIGRP version 6 (EIGRPv6) Implement filtering and route redistribution Implement IPv6 multicast, PIM, and related multicast protocols, such as
Multicast Listener Discovery (MLD)
9

IPv6 Overview

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Short History Of IP
11
1990 1991 1992 1993 1994 1995 1996 1997 1998 1999 2000
Prediction of the exhaustion of IPv4 Class B by 1994. ROAD group formed to address routing. Prediction of the exhaustion of IPv4 addresses by 2005-2011. IPng Proposals solicitation (RFC 1550). CATNIP, SIPP, TUBA analyzed. SIPP+ chosen. IPng wg started. First specification: RFC 1883.
First attempt for provider-based address format. First IPv6 exchange: 6tap. Registries assign IPv6 prefixes. IPv6Forum formed. Major vendors bundle IPv6 in their mainstream product line.
6bone started.

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 Versus IPv6 - Ringside
12
IPv4 IPv6 32-bit (4-byte) address supports 4,294,967,296 addresses
128-bit (16-byte) address supports 2128 (about 3.4×1038) addresses
NAT can be used to extend address space limitations
Does not support NAT by design
Administrators must use DHCP or static configuration to assign IP addresses to hosts
Hosts use stateless address autoconfiguration to assign an IP address to themselves
IPsec support is optional IPsec support is necessary
Options are integrated into the base header Improved support for options using extension headers and overall simplification of the header format

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Addressing IPv4 32-bits
IPv6 128-bits
232 = 4,294,967,296 2128 = 340,282,366,920,938,463,463,374,607,431,768,211,456 (340 undecillion IPv6 addresses) 2128 = 232 * 296
296 = 79,228,162,514,264,337,593,543,950,336 times the number of IPv4 addresses (79 octillion addresses, or 79 trillion trillion for the arithmophobes)
13

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
340,282,366,920,938,463,374,607,432,768,211,456 (IPv6 Address Space – 340 Undecillion)
vs.
4,294,967,296 (IPv4 Address Space - 4 Billion)
So How Big Is The IPv6 Address Space?
14
Let’s assume that an atom represents 4 Billion Addresses
You would need 80,000 Kgs of Atoms to represent IPv6!!!!
.
An Atom
An 80 Tonne Whale (Lots of Atoms)

IPv6 Addressing

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Addresses IPv6 addresses are 128 bits long
– Segmented into 8 groups of four HEX characters – Separated by a colon (:) – 50% for network ID, 50% for interface ID – Network portion is allocated by Internet registries 2^64 (1.8 x 1019) – Still leaves us with ~ 3 billion network prefixes for each person on earth
16
nnnn:nnnn:nnnn: xxxx:xxxx:xxxx:xxxx
Global Routing Prefix n <= 48 bits
Subnet ID 64 – n bits
Host
ssss:
2001:1A6E:134A: 0000:0000:0000:1E2A 00A1:
Network Portion Interface ID
Global Unicast Identifier Example
2001:0:0: ::1E2A A1:
Full Format
Abbreviated Format

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Address and Simplification
17
• Base format (16-byte)
• Compact Format:
• Literal representation (e.g. used when browsing to IPv6 address directly and not through the DNS name) – [2001:660:3003:2:a00:20ff:fe18:964c]
2001:0660:3003:0001:0000:0000:6543:210F
2001:0660:3003:0001:0000:0000:6543:210F 2001:0660:3003:0001:0000:0000:6543:210F 2001:660:3003:1:0:0:6543:210F 2001:660:3003:1:0:0:6543:210F 2001:660:3003:1::6543:210F
6DISS Courtesy Slide

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Address Representation
Example: – Address: 2001:0DB8:0000:0000:FFFF:0000:0000:0ADC
– The following are correct representations: 2001:db8::FFFF:0:0:ADC 2001:db8:0:0:FFFF::ADC
– The following is an incorrect representation: 2001:db8::FFFF::ADC
18
Important to identify good vs. bad for exams!

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Comparison of Address Type Syntax (CATS)
IPv4 Address
HOST: 156.50.20.1 NET: 156.50.0.0/16
IPv6 Address
FE80::20B:60FF:FEA7:D81A 2001:0:0:A1::/64
Network Operator
I need some Catnip… HEX is a curse…
19

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Required Host Addresses
An IPv6 host interface requires the following IPv6 addresses for proper operation: – A link-local address – Loopback address – All-nodes multicast address – Any additional unicast and anycast addresses (configured automatically or manually) – Solicited-node multicast address for each of its unicast and anycast addresses – Multicast addresses of all other groups to which the host belongs
20

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Required Router Addresses
An IPv6 router interface is required to identify the following IPv6 addresses for proper operation: – All valid host addresses – All-Routers multicast addresses – Subnet-router anycast addresses for all interfaces for which it is configured to act as a
router (prefix:: ; interface id=0) – Other unicast or anycast configured addresses – All other Anycast addresses with which the router has been configured. – All-Routers Multicast Addresses – Multicast Addresses of all other groups to which the router belongs.
21

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Address Types Summary
22
Binary Prefix IPv6 Notation
Unspecified 00 … 0 (128 bits) ::/128
Loopback 00 … 1 (128 bits) ::1/128
Multicast 1111 1111 FF00::/8
Link-local unicast 1111 1110 10 FE80::/10
Unique local unicast 1111 110 FC00::/7
Global unicast Everything else
Currently allocated space is
2000::/3

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Allocated Real World Usage
So, let’s look at things: – 2^128 addresses total – 2000::/3 is actually allocated – That means 2^125 addresses for Global Unicast Addressing All networks are at least /64’s per standard 125 – 64 = 61. So 2^61 possible networks in the currently allocated global space.
2^61 = 2,305,843,009,213,693,952 or 2.3 QUINTILLION networks.
/48 is typical allocation to enterprise customer 2^45 = 35,184,372,088,832 or 35 TRILLION enterprises
Current IPv4 BGP table is ONLY 400,000 routes and people complain
23
!

IPv6 Addressing: Formats

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
PI and PA Allocation Process
25
Registries
Level Four Enterprise
IANA
ISP Org
Provider Assigned
http://www.ripe.net/ripe/policies/proposals/2006-01.html http://www.ripe.net/ripe/policies/proposals/2006-05.html
2000::/3
/48
2000::/3
/48
/12
/32
/12
Provider Independent

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Link-Local Addresses
Link-local addresses: – Have a limited scope of the link – Are automatically configured with the interface ID
Interface ID 0 128 bits
1111 1110 10
FE80::/10
10 bits
64 bits
EUI-64 Format
26

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
EUI-64 Format Addressing
27
EUI-64 address is formed by inserting "FFFE" and OR’ing a bit identifying the uniqueness of the MAC address.
U/L bit always inverts from what it was
00 90 27
00 90 27
00 90 27
02 90 27
17 FC 0F
17 FC 0F
17 FC 0F
17 FC 0F FF FE
FF FE
FF FE
000000X0 where X= 1 = unique
0 = not unique X = 1
Ethernet MAC address (48 bits)
64 bits version
Uniqueness of the MAC
Eui-64 address

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Privacy Extensions (RFC 3041/4941)
IEEE 24 bits OUI can be used to identify hardware – http://standards.ieee.org/regauth/oui/oui.txt Temporary addresses for IPv6 host client application,
e.g. web browser – Inhibit device/user tracking – Random 64 bit interface ID, then run Duplicate Address Detection
before using it – Rate of change based on local policy
2001 /32 /48 /64 /23
Interface ID
Recommendation: Use Privacy Extensions for External Communication but not for Internal
Networks (Troubleshooting and Attack Trace Back) RFC4941
28

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Site-Local Addresses
29
Site-local addresses: – Have a limited scope of the site – Contain the inside topology of the site with the subnet ID – Subnet ID may contain octets 2 & 3 of IPv4 address!
Deprecated, but still reserved space, and still potential in exams!
Interface ID 0
1111 1110 11
FEC0::/10 Subnet id
128 bits
10 bits 16 bits

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Unique Local Addresses
There are two types of Unique Local Address (ULA) ranges – Local self-assigned ranges FD00::/8 No centralized control, the “ID” field is randomized (“almost unique”)
– Centrally-assigned (global) ranges FC00::/8 Assigned to entity by RIR’s
30

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Unique-Local Addresses
31
Unique-local addresses (RFC4193): – Have a limited scope of the site – Contain the inside topology of the site with the subnet ID – 40-bit Global ID is assigned to company for unique identification – Subnet ID may contain octets 2 & 3 of IPv4 address!
Interface ID Global ID
1111 1100
FC00::/7 Subnet id
128 bits
8 bits 16 bits
http://www.sixxs.net/tools/grh/ula/

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Generating Unique Local Prefixes
32

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Aggregated Global Unicast Addresses
33
Aggregatable Global Unicast addresses are: – Addresses for generic use of IPv6 – Structured as a hierarchy to keep the aggregation
Interface ID TLA NLAs SLA
001
64 bits 3 13 24 bits 16 bits 8
Provider Site Host
RES
NLA1 NLA2 NLAn
RFC 2374 RFC 3587
http://www.sixxs.net/tools/grh/dfp/ http://www.sixxs.net/tools/grh/dfp/arin/

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Aggregation
34
– Larger address space enables: – Aggregation of prefixes announced in the global routing table – Efficient and scalable routing
ISP
2001:0410::/35 Customer
no 2 IPv6 Internet
2001::/16 2001:0410:0002:/48
2001:0410:0001:/48
Customer no 1
Only announces the /35 prefix

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Allocation Strategies
We wish to allocate /48’s out of the /35. Which are available:
– 2001:0468:0000 through – 2001:0468:1fff Recall the the bit structure is:
– 0010 0000 0000 0001: 0000 0100 0110 1000: 000 | 0:0000:0000:0000 – 0010 0000 0000 0001: 0000 0100 0110 1000: 000 | 1:1111:1111:1111 So there are 8,192 /48’s in a /35 Same thought process as IPv4 subnetting!
35

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
How Would Allocations Work?
Suppose you wish to give out /40’s in the /35. – 2001:0468:000 | 0 0000 | or 2001:0468::/40 – 2001:0468:000 | 1 1111 | or 2001:0468:1f00::/40 Thus there are 32 /40’s in the /35 each of which has 256 /48’s.
– 5 bits – 8 bits
36

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
How Would Allocations Work?
The same idea holds for /41’s or /42’s. – 2001:0468:000 | 0:0000:0 | or 2001:0468::/41 – 2001:0468:000 | 1:1111:1 | or 2001:0468:1f80::/41 – 2001:0468:000 | 0:0000:00 - :000 | 1:1111:11 – 2001:0468::/42 – 2001:0468:1fd0::/42
37

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Mixed Allocations
The interesting case is how to handle mixed allocations. Some sites need a /40 others a /42. How can you handle this case. See
– draft-ietf-ipngwg-ipaddressassign-02 – A flexible method for managing the assignment of bits of an IPv6 address block – A perl script is included.
38

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Example
A TLA has been assigned the 3ffe:0b00/24 prefix and wants to assign prefixes to its connected networks. Assume 8 bits for NLA’s. NLA2, will use 10 bits for subNLA’s. – TLA assigning to NLAs using lefmost bits: 10000000 : assigned to NLA1 01000000 : assigned to NLA2
– NLA2 assigning to its subNLAs using centermost bits: 0000010000 : assigned to subNLA1 0000100000 : assigned to subNLA2
– subNLAs use centermost bits and site nets assigned using rightmost bits. Putting all bits together for subNLA3:
– TLA |NLA2 |subNLA3 – 0011 1111 1111 1110 0000 1011 0100 0000 0000 1100 00
» <-------> <------> 39

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Mixed Allocations
Here is the assignment: – Take 3ffe:3700::/32. Out of that allocate 34 = 2 37 = 3 38 = 5
40

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Multihoming
41

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Multicast
42
Interface ID 0
1111 1111
128 bits
8 bits
Flag
8 bits
Scope F F Flag =
0 if permanent
1 if temporary
Scope =
1 = node 2 = link 5 = site 8 = organization E= global

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Multicast MAC Address Conversion
43
IPv6 Multicast Address
Corresponding Ethernet Address
Multicast Prefix for Ethernet
Multicast
• IPv6 multicast address to MAC address: – 33:33:(least significant 32 bits from IPv6)
FF22 DEAD
FF 22 DE AD 33 33
FF02 0000 0000 0000 0000 0001

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Group ID
Multicast Addresses
44
Multicast is used in the context of one-to-many. A multicast scope is new in IPv6.
1111 1111
8 Bits
Flags
8 Bits
Scope F F Flags = 4 Bits = “0”, “R”, “P”, ”T”
Scope =
1 = interface-local 2 = link-local 3 = subnet-local 4 = admin-local 5 = site-local 8 = organization E = global
112 Bits

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Multicast Assigned Addresses
Meaning Scope
FF02::1 All nodes Link-local
FF02::2 All routers Link-local
FF02::9 All RIP routers Link-local
FF02::1:FFXX:XXXX Solicited-node Link-local
FF05::101 All NTP servers Site-local
FF05::1:3 All-DHCP servers Site-local
45
FF0x:: is reserved (x = 0..F). Inside this range, the following are assigned:

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 over Ethernet
– IPv6 has a specific Ethernet protocol ID – Different from the IPv4 one
Destination Ethernet Address IPv6 header and payload 0x86DD Source Ethernet
Address
46

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Addresses – Examples
cat6500-1>sh ipv6 int vlan 200 Vlan200 is up, line protocol is up IPv6 is enabled, link-local address is FE80::2D0:D3FF:FE81:9000 Description: --- To Core --- Global unicast address(es): 2001:DB8:12::1, subnet is 2001:DB8:12::/64 Joined group address(es): FF02::1 FF02::2 FF02::5 FF02::D FF02::16 FF02::1:FF00:1 FF02::1:FF81:9000
All nodes
All routers
OSPF Routers
All PIM Routers
All MLDv2 capable Routers
Global
Link-Local
47

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Interface Identifier
48
CR-IT-SW3#sh int gi 1/0/3 | in bia GigabitEthernet1/0/3 is up, line protocol is up Hardware is Gigabit Ethernet, address is 000c.3a3e.82de (bia 000c.3a3e.82de) CR-IT-SW3#
CR-IT-SW3#sh ipv6 interface gi 1/0/3 GigabitEthernet1/0/3 is up, line protocol is up IPv6 is enabled, link-local address is FE80::20C:3aFF:FE3E:82DE [TEN] Global unicast address(es): 2001:DB8:24:0:20C:3aFF:FE3E:82DE, subnet is 2001:DB8:24::/64 [EUI/TEN] Joined group address(es): FF02::1 FF02::2 FF02::1:FFAE:84C7 CR-IT-SW3#
CR-IT-SW3#sh run int gi 1/0/3 ! interface GigabitEthernet1/0/3 no switchport ip address 10.149.24.1 255.255.255.0 ipv6 address 2001:DB8:24::/64 eui-64 !

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Interface Identifier
49
CR-IT-SW3#sh int gi 1/0/3 | in bia GigabitEthernet1/0/3 is up, line protocol is up Hardware is Gigabit Ethernet, address is 000c.3a3e.82de (bia 000c.3a3e.82de) CR-IT-SW3#
CR-IT-SW3#sh ipv6 interface gi 1/0/3 GigabitEthernet1/0/3 is down, line protocol is down IPv6 is enabled, link-local address is FE80::20C:3AFF:FE3E:82DE [TEN] Global unicast address(es): 2006:149:24:0:20C:3AFF:FE3E:82DE, subnet is 2006:149:24::/64 [EUI/TEN] 2006:149:25::1, subnet is 2006:149:25::/64 [TEN] Joined group address(es): FF02::1 FF02::2 CR-IT-SW3#
CR-IT-SW3#sh run int gi 1/0/3 ! interface GigabitEthernet1/0/3 no switchport ip address 10.149.24.1 255.255.255.0 ipv6 address 2006:149:24::/64 eui-64 ipv6 address 2006:149:25::1/64 !

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Windows 7 – Interface Identifier
50
C:\>netsh int ipv6 sh addr Interface 1: Loopback Pseudo-Interface 1 Addr Type DAD State Valid Life Pref. Life Address --------- ----------- ---------- ---------- ------------------------ Other Preferred infinite infinite ::1 Interface 12: isatap.{7218C71C-E509-4EF9-AB57-C08863056588} Addr Type DAD State Valid Life Pref. Life Address --------- ----------- ---------- ---------- ------------------------ Other Deprecated infinite infinite fe80::5efe:10.109.109.6%12 Interface 13: Local Area Connection* 9 Addr Type DAD State Valid Life Pref. Life Address --------- ----------- ---------- ---------- ------------------------ Public Preferred infinite infinite 2001:0:5ef5:73bc:a2:3ac1:f592:92f9 Other Preferred infinite infinite fe80::a2:3ac1:f592:92f9%13 Interface 11: Local Area Connection Addr Type DAD State Valid Life Pref. Life Address --------- ----------- ---------- ---------- ------------------------ Temporary Preferred 6d23h49m31s 6d23h49m31s 2001:db8:9:cafe:a133:5fb8:31df:864a Public Preferred 29d23h59m49s 6d23h59m49s 2001:db8:9:cafe:b407:e685:fb14:c12d Other Preferred infinite infinite fe80::b407:e685:fb14:c12d%11
Windows 7 doesn’t use the EUI-64 technique by default when forming its interface identifier, but uses their randomly-generated interface identifiers

IPv6 Addressing: Scoping

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Types of Addresses
Unicast Multicast Anycast
52

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Unicast Addresses
Unicast addresses are used in a one-to-one context. IPv6 unicast addresses:
– Global unicast addresses – Unique local addresses – Link-local addresses
53

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Address Types Three types of unicast address scopes
54
FC00:GGGG:GGGG:
xxxx:xxxx:xxxx:xxxx ssss:
FE80:0000:0000:0000: xxxx:xxxx:xxxx:xxxx
2000:GGGG:GGGG:
xxxx:xxxx:xxxx:xxxx ssss:
FFfs: xxxx:xxxx:xxxx:xxxx:xxxx:xxxx:xxxx
• Interface “expected” to have multiple addresses and life-time parameters
Link-Local – Non routable exists on single layer 2 domain (FE80::/64)
Unique-Local (ULA) – Routable with an administrative domain (FC00::/7)
Global – Routable across the Internet (2000::/3)
• Multicast addresses begin with FF00::/8
• Other address types have come and gone (deprecated)

IPv6 Addressing: Special Addresses

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Special Use IPv6 Addresses
Examples – Can you identify? – FF02:0:0:0:0:0:0:1 => FF02::1 – FF15:0:0:0:0:0:1:c001 => FF15::1:c001 – 0:0:0:0:0:0:0:1 => ::1 – 0:0:0:0:0:0:0:0 => ::
56

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Special Use IPv6 Addresses
Other examples: 2001:0000::/29 through 2001:01F8::/29 are reserved
– 2001::/32 is used for Teredo tunneling – 2001:2::/48 is used for the Benchmarking Methodology Working Group of the IETF – 2001:10::/28 is used for the Overlay Routable Cryptographic Hash Identifiers
(ORCHID) – 2001:db8::/32 is the official range designated for training and documentation 2002::/16 is set aside for Automatic 6to4 Tunneling
57

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 Addresses As IPv6 Addresses
Format: – IPv4-compatible (deprecated) 0:0:0:0:0:0:192.0.2.100 = ::192.0.2.100 = ::C000:0264
– IPv4-mapped (used often in MBGP for Next-Hop information) 0:0:0:0:0:FFFF:192.0.2.100 = ::FFFF:C000:0264
58

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Representing IPv6 Addresses in URLs
59
In a URL, the address is enclosed in brackets: –http://[2001:DB8:1003::E]:8080/index.html Cumbersome for users
–Mostly for diagnostic purposes Use fully qualified domain names
RFC 2732 - Format for Literal IPv6 Addresses in URLs http://www.faqs.org/rfcs/rfc2732.html

IPv6 Addressing: Anycast

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Anycast Addresses
Anycast: – Used in the context of one-to-nearest – Assigned to more than one interface – Allocated from the unicast address space
Interface ID Prefix
128-n Bits n Bits
61

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Addressing: Anycast Addresses
BGP Announces 2001:100:100:100::/64
SA = 2001:200:200:200::1 DA = 2001:100:100:100::1
2001:100:100:100::1 Host 1
2001:200:200:200::1
2001:100:100:100::1
2001:100:100:100::1
BGP Announces 2001:100:100:100::/64
BGP Announces 2001:100:100:100::/64
R1
R4
R2 R3
62

IPv6 Addressing: Configuration

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Basic IPv6 Commands
R1(config)# ipv6 unicast-routing R1(config-if)# ipv6 address (#) R1(config)# ipv6 route (net/vlsm) (node#)
– Ipv6 route ::/0 3ffe:b00:c18:1:260:3eff:fe47:1530 Show ipv6 neighbors Ping (ipv6-addr)
64

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
L2 to L3 Mapping
Don’t forget that this is another protocol! – Any interface using manual mapping needs to be updated – Frame-relay map ipv6 …… – Dialer map ipv6 …… – Etc.
65

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Static Name to Host Address Entries
Name to address resolution just like IPv4 – Ipv6 host (name) (ipv6-address) Can specify up to four addresses You can run DHCP server and DNS server in IPv6 No concept of secondary addresses in IPv6, all are valid options
66

IPv6 Headers: Packet Headers

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
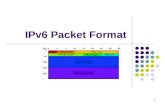
IPv6 Structure
The IPv6 header has the following improvements: – Fixed length of 40 bytes – Simple, more efficient processing – Extension headers handle additional options – Several IPv4 fields have been removed: Header length, identification, flags, fragment offset, and header checksum
Version (4) Traffic Class Flow Label (20)
Payload Length (16) Next Header (8) Hop Limit (8) Source Address (128)
Destination Address (128)
40 bytes
(8)
68

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 Header Versus IPv6 Header IPv4 Header
IPv6 Header Version Traffic
Class Flow Label
Payload Length Next Header Hop Limit
Source Address Destination Address
Version IHL TOS Total Length
Identification Flags Fragment Offset
Time to Live Protocol Header Checksum
Source Address Destination Address Options Padding
Key Fields the same in IPv4 and IPv6 Fields removed in IPv6 Name and position changed in IPv6 New field in IPv6
69

IPv6 Headers: Extension Headers

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Extension Headers
Simple packet headers provide faster processing – IPv6 deals with IP options using extension headers IPv6 defines six extension headers:
– Hop-by-hop options header – Routing header – Fragment header – Destination options header – Authentication header – Encrypted security payload header
71

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Header Manipulation
Unlimited size of header chain (spec-wise) can make filtering difficult Potential DoS with poor IPv6 stack implementations
– More boundary conditions to exploit – Can I overrun buffers with a lot of extension headers?
72
Perfectly Valid IPv6 Packet According to the Sniffer
Destination Options Header Should Be the Last
Header Should Only Appear Once
Destination Header Which Should Occur at Most Twice
See also: http://www.cisco.com/en/US/technologies/tk648/tk872/technologies_white_paper0900aecd8054d37d.html

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Parsing the Extension Header Chain
Finding the layer 4 information is not trivial in IPv6 – Skip all known extension header – Until either known layer 4 header found => SUCCESS – Or unknown extension header/layer 4 header found... => FAILURE
73
IPv6 hdr HopByHop Routing AH TCP data
IPv6 hdr HopByHop Routing AH Unknown L4 ???
IPv6 hdr HopByHop Unk. ExtHdr AH TCP data

IPv6 Domain Naming System

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Basic Ideas
DNS in IPv6 is much like DNS in IPv4 Keep files and delegations as simple as possible. Can use IPv4 as transport for DNS for now. Modern versions of Bind will work – Bind9 is stable and works with IPv6. There is work on dynamic DNS in progress, but we don’t need to worry about
that for now.
75

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 IPv6
Hostname to IP address
A record: www.abc.test. A 192.168.30.1
IPv6 and DNS
AAAA record: www.abc.test. AAAA 2001:db8:C18:1::2
IP address to hostname
PTR record: 2.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.1.0.0.0.8.1.c.0. 8.b.d.0.1.0.0.2.ip6.arpa. PTR www.abc.test.
PTR record: 1.30.168.192.in-addr.arpa. PTR
www.abc.test.
76

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS server
Router A
B
DNS Query in IOS
77
DNS resolver picks IPv6 AAAA record first
IPv6 stacks on Windows XP, Linux, FreeBSD, etc. also pick IPv6 address before IPv4 address if both exist
Query=“www.example.org” TYPE=“AAAA”
Resp=“2001:db8:1::1” Type=“AAAA”
OR
Resp=“NONE”
Query=“www.example.org” TYPE=“A”
Resp=“192.168.0.3” Type=“A”

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS Example – AAAA Queries
78
A and AAAA Queries for www.google.com
IPv6 Transport Preferred
Response IPv4 and IPv6 Addresses

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS Extensions for IPv6
DNS has been extended to support IPv6 – RFC 3363—Representing Internet Protocol version 6 (IPv6) Addresses in the Domain
Name System (DNS) – RFC 3596—DNS Extensions to Support IP version 6 Extensions include:
– New record types for IPv6 addresses have been proposed (A6, AAAA) – New domain for reverse name resolution (IPv6.ARPA) – Hierarchical method to support easy network renumbering
79

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS Example (IPv4-Only)
DNS Request (h.root-servers.net) (QTYPE=A)
IPv4 A Response (128.63.2.53)
H.ROOT-SERVERS.NET. 210892 IN A 128.63.2.53
Sample DNS Response
IPv4-Only Host DNS Server
80

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS Example (IPv6-Only)
DNS Request (h.root-servers.net) (QTYPE=AAAA)
IPv6 AAAA Response (2001:500:1::803f:235 )
IPv4-Only Host DNS Server
H.ROOT-SERVERS.NET. 210892 IN AAAA 2001:500:1::803f:235
Sample DNS Response
81

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS Example (Dual-Stack)
DNS Server
Dual-Stack Host DNS Request (h.root-servers.net) (QTYPE=AAAA, A)
I prefer IPv6 addresses
IPv6 AAAA Response (2001:500:1::803f:235 ) IPv4 A Response (128.63.2.53)
H.ROOT-SERVERS.NET. 210892 IN AAAA 2001:500:1::803f:235 H.ROOT-SERVERS.NET. 210892 IN A 128.63.2.53
Sample DNS Response
82

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
DNS Issues
Upgrade DNS servers to support IPv6 Adding AAAA record for a specific server to the DNS Server requires ALL
services to be IPv6 aware – LDAP or AD IPv6 Aware – All Services running on the Server Interim solution is to use a temporary name (see Google IPv6 start in 2008)
– ipv6.google.com vs. www.google.com
83

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Forward Lookups
Uses AAAA records for assign IPv6 addresses to names. Multiple addresses possible for any given name – for example, in a multi-
homed situation. Can assign A records and AAAA records to a given name/domain. Can also assign separate domains for IPv6 and IPv4. Don’t be afraid to experiment!
84

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Sample Forward Lookup File
85
;; domain.net (use your favorite naming scheme) $TTL 86400 @ IN SOA ns1.domain.edu. root.domain.edu. ( 2011061101 ; serial - YYYYMMDDXX 21600 ; refresh - 6 hours 1200 ; retry - 20 minutes 3600000 ; expire - long time 86400) ; minimum TTL - 24 hours ;; Nameservers IN NS ns1.domain.net. IN NS ns2.domain.net. ;; Hosts with just A records host1 IN A 100.100.100.1 ;; Hosts with both A and AAAA records host2 IN A 1.100.100.2 IN AAAA 2001:468:100:1::2 :: Separate domain $ORIGIN ip6.domain.net host1 IN AAAA 2001:468:100:1::1

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Reverse Lookups
Reverses should be put in for both ip6.int and ip6.arpa domains. The ip6.int domains has been deprecated, but some hosts still use them. Can use same file for both – use the @ notation and point to the same file in
the named.conf file. File uses nibble format – see examples on next slide.
86

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Sample Reverse Lookup File
87
;; 1.0.0.0.0.0.1.0.8.6.4.0.1.0.0.2.rev (use your favorite naming scheme ;; These are reverses for 2001:468:100:1::/64) ;; File can be used for both ip6.arpa and ip6.int. $TTL 86400 @ IN SOA ns1.domain.net. root.domain.net. ( 2011061101 ; serial - YYYYMMDDXX 21600 ; refresh - 6 hours 1200 ; retry - 20 minutes 3600000 ; expire - long time 86400) ; minimum TTL - 24 hours ;; Nameservers IN NS ns1.domain.net. IN NS ns2.domain.net. 1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0 IN PTR host1.ip6.domain.net 2.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0 IN PTR host2.domain.net ;; ;; Can delegate to other nameservers in the usual way ;;

IPv6 Host Addressing

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Auto-Configuration
• Larger address space enables: the use of link-layer addresses inside the address space auto-configuration with "no collisions" offers "plug and play"
Sends network-type information (prefix, default route, …)
Host autoconfigured address is: prefix received + link-layer address
Mac address: 00:2c:04:00:FE:56
89

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Renumbering
– Larger address space enables: renumbering, using auto-configuration and multiple addresses
Sends NEW network-type information (prefix, default route, …)
Host auto-configured address is: NEW prefix received + SAME link-layer address
Mac address: 00:2c:04:00:FE:56
90

IPv6 Neighbor Discovery

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Neighbor Discovery Parameters
92
Router advertisements • Default router
• IPv6 network prefix
• Lifetime of advertisement
Autoconfiguring IPv6 hosts

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Types of Discovery
Router Discovery: How hosts locate routers that reside on an attached link. Prefix Discovery: How hosts discover the set of address prefixes that define
which destinations are on-link for an attached link. (Nodes use prefixes to distinguish destinations that reside on-link from those only reachable through a router.) Parameter Discovery: How a node learns such link parameters as the link MTU
or such Internet parameters as the hop limit value to place in outgoing packets.
93

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
What do you Do with that?
Address Autoconfiguration: How nodes automatically configure an address for an interface. Address resolution: How nodes determine the link-layer address of an on-link
destination (e.g., a neighbor) given only the destination's IP address. Next-hop determination: The algorithm for mapping an IP destination address
into the IP address of the neighbor to which traffic for the destination should be sent. The next-hop can be a router or the destination itself.
94

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
What About Changes?
Neighbor Unreachability Detection: How nodes determine that a neighbor is no longer reachable. For neighbors used as routers, alternate default routers can be tried. For both routers and hosts, address resolution can be performed again. Duplicate Address Detection: How a node determines that an address it wishes
to use is not already in use by another node. Redirect: How a router informs a host of a better first-hop node to reach a
particular destination.
95

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
ND Summary
Neighbor Discovery defines five different ICMP packet types: A pair of Router Solicitation and Router Advertisement messages, a pair of Neighbor Solicitation and Neighbor Advertisements messages, and a Redirect message. The messages serve the following purpose: Router Solicitation: When an interface becomes enabled, hosts may send out
Router Solicitations that request routers to generate Router Advertisements immediately rather than at their next scheduled time.
96

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Types and Comparison
Router Advertisement: Routers advertise their presence together with various link and Internet parameters either periodically, or in response to a Router Solicitation message. Router Advertisements contain prefixes that are used for on-link determination and/or address configuration, a suggested hop limit value, etc. (Like SAP in IPX) Neighbor Solicitation: Sent by a node to determine the link-layer address of a
neighbor, or to verify that a neighbor is still reachable via a cached link-layer address. Neighbor Solicitations are also used for Duplicate Address Detection. (Like ARP in IPv4) Neighbor Advertisement: A response to a Neighbor Solicitation message. A
node may also send unsolicited Neighbor Advertisements to announce a link-layer address change. (Like gratuitous ARP in IPv4) Redirect: Used by routers to inform hosts of a better first hop for a destination.
(Like ICMP Redirect in IPv4) 97

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Neighbor Discovery Configuration
98
LAN1: 3000:b00:c18:1::/64
LAN2: 3000:b00:c18:2::/64
RA
RA
Fa0/0
Fa0/1
Fa0/0
interface FastEthernet0/0 ipv6 nd prefix 3000:b00:c18:1::/64 43200 43200 ipv6 nd ra-lifetime 0 interface FastEthernet0/1 ipv6 nd prefix 3000:b00:c18:2::/64 43200 43200
interface FastEthernet0/0 ipv6 nd prefix 3000:b00:c18:1::/64 43200 43200
R2
R1
IPv6 Internet

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Prefix Renumbering
99
NEW network prefix: 3ffe:b00:c18:2::/64 Deprecated prefix: 3ffe:b00:c18:1::/64
Hosts:
Autoconfigured IPv6 hosts
deprecated address 3ffe:b00:c18:1:260:8ff:fede:8fbe preferred address 3ffe:b00:c18:2:260:8ff:fede:8fbe
Router configuration after renumbering:
Router advertisements with expiration dates
OR:
interface FastEthernet0/0 ipv6 nd prefix 3ffe:b00:c18:1::/64 43200 0 ipv6 nd prefix 3ffe:b00:c18:2::/64 43200
interface FastEthernet0/0 ipv6 nd prefix 3ffe:b00:c18:1::/64 at Sep 1 2012 23:59 Sep 1 2012 23:59 ipv6 nd prefix 3ffe:b00:c18:2::/64 43200 43200

IPv6 & ICMPv6

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
ICMP
Completely Changed – note new header type
Now includes IGMP
Types organized as follows – 1 – 4 Error messages – 128 – 129 Ping – 130 – 132 Group membership – 133 – 137 Neighbor discovery
General Format
101

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
ICMP Type Description 1 Destination Unreachable 2 Packet Too Big 3 Time Exceeded 4 Parameter Problem 128 Echo Request 129 Echo Reply 130 Group Membership Query 131 Group Membership Report 132 Group Membership Reduction 133 Router Solicitation 134 Router Advertisement 135 Neighbor Solicitation 136 Neighbor Advertisement
137 Redirect
102

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
ICMPv6
Not compatible with IPv4 ICMP – Completely new protocol specification Incorporates the IPv4 IGMP functionality Identified by a new protocol code: next-header type
– IPv4 ICMP is protocol code 1 – IPv4 IGMP is protocol code 2 – IPv6 ICMP is next-header type 58 RFC 2463—Replaced by RFC 4884
103

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
HSRP for v6 First Hop Router Redundancy
104
Modification to Neighbor Advertisement, Router Advertisement, and ICMPv6 redirects
Virtual MAC derived from HSRP group number and virtual IPv6 link-local address
HSRP Standby
HSRP Active
GLBP for v6 Modification to Neighbor Advertisement, Router
Advertisement—GW is announced via RAs
Virtual MAC derived from GLBP group number and virtual IPv6 link-local address
GLBP AVF, SVF
GLBP AVG, AVF
Neighbor Unreachability Detection (NUD) For rudimentary HA at the first HOP
Hosts use NUD “reachable time” to cycle to next known default gateway (30s by default)
RA Sent Reach-time = 5,000 msec

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Neighbor Discovery
Neighbor Discovery
DAD
NUD
Redirects
Address Resolution (~ARP)
Router Discovery
Neighbor Discovery Types
105

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Neighbor Discovery
IPv4 uses ARP to resolve local addresses – Relies on broadcasts IPv6 does not have the concept of broadcasts
– Still need a method to resolve local addresses – Use solicited-node multicast instead IPv6 uses ICMPv6 the following types of message:
– Neighbor solicitation – Neighbor advertisement – Router solicitation – Router advertisement
106

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Neighbor Solicitation
107
I need to reach IPv6 address FEC0::2003:210:A4FF:FEA6:69D0
Neighbor solicitation (ICMP Type 135) to solicited node multicast address
I have that address! Neighbor advertisement
(ICMP Type 136) to neighbor solicitation
source address
Solicited node multicast address allows the host to reach all nodes with matching last 24 bits (derived from DA)
Host 1 Host 2

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Solicited Node Multicast Address
Layer 3 multicast group derived from the IPv6 address Minimizes the number of hosts that see the neighbor solicitation Fixed prefix (FF02:0:0:0:0:1:FF00:0/104) + last 24 bits of the host’s IPv6
address
108
FEC0::2003:210:A4FF:FEA6:69D0 Unicast address
FF02:0:0:0:0:1:FFA6:69D0 Solicited multicast address
• All nodes with the same final 24 bits of their IPv6 addresses receive packets to this multicast address

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Duplicate Address Detection
109
Send NS
I have that address! NA to all-nodes multicast
Select new address or display error and do not participate on the network (RFC2462)
Host 1 Host 2

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Autoconfiguration
IPv6 hosts can configure their own addresses automatically Similar in function to IPv4 DHCP Two methods:
– Stateless autoconfiguration – Stateful autoconfiguration Common ICMPv6 messages to both:
– Router advertisements – Router solicitations
110

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Router Advertisement
111
Used to configure hosts Periodically sent to the all-nodes multicast group Also sent in response to a router solicitation message Options can contain:
– MTU – On-link prefixes and lifetimes – Layer 2 address of the advertising router
32 bits
Type=134 Code Checksum
Reachable Time Hop Limit M O RSV Router lifetime
Retransmit Timer Options

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Type Length Prefix Length L A Reserved Valid Lifetime
Preferred Lifetime Reserved
Prefix
Router Advertisement—Prefix Option
112

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Router Solicitation
113
Sent by hosts to locate on-link routers
Usually sent to the all-routers multicast group
Source address can be: – Unspecified – Local address
Router solicitation message consists of five fields
Type=133 Code Checksum Reserved Options 32 bits

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless Autoconfiguration
Basic host address configuration IPv6 Stateless Address Autoconfiguration
– RFC 4862—September 2007
114

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless Autoconfiguration
115
Generate a link local address
Verify this tentative address Is ok. Use a neighbor solicitation
with the tentative address as the target. ICMP type 135
If the address is in use
a neighbor advertisement Message will be returned.
ICMP type 136
If no response Assign the address to the Interface. At this point the Node can communicate
On-link.
Fail and go to manual Configuration or choose A different interface token

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless Autoconfiguration
116
Assign address to Interface.
Node joins the All Routers Multicast group. FF02::1
Sends out a router Solicitation message to That group.
ICMP type 133
Router responds with a Router advertisement.
ICMP type 134

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless Autoconfiguration Look at the “managed address
configuration" flag
If M= 0 proceed with Stateless configuration
If M=1 stop and Do statefull config.
Look at "other stateful configuration" flag
If O = 0 finish
If O= 1 use statefull Configuration for other information
117

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless Autoconfiguration
118
Build link-local address Join all-nodes multicast group Join solicited node multicast group Send NS My address is unique! Send RS No routers!
Try stateful configuration
Link-local only
Host 1

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless Autoconfiguration
119
Build link-local address
Join all-nodes multicast group
Join solicited node multicast group
Send NS
My address is unique!
Send RS
Send RA
Build on-link addresses

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Router Solicitation Options
Valid Lifetime – 32-bit unsigned integer. The length of time in seconds before an address is
invalidated. Preferred Lifetime
– 32-bit unsigned integer. The length of time in seconds before an address is deprecated.
120

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateless autoconfig
Routers are to send out router advertisements at regular intervals at the all hosts address. – This should update lifetimes. Note that stateless autoconfig will only configure addresses.
– It will not do all the host configuration you may well want to do.
121

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateful Autoconfiguration
IPv4 DHCP does more than manage addressing… Provides optional services:
– DNS – WINS server – Boot server – NETBIOS node type – Many others… Stateful autoconfiguration and Dynamic Host Configuration Protocol for IPv6
(DHCPv6) meet the demand – draft-ietf-dhc-dhcpv6-28.txt
122

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateful Autoconfiguration (1 of 2)
123
Build link-local address
Join all-nodes multicast group
Join solicited node multicast group
Send NS
My address is unique!
Send RS
Send RA (M bit = 0, O bit = 1)
Build on-link addresses

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateful Autoconfiguration (2 of 2)
124
Send DHCP request to FF05::1:3 (All DHCP Servers)
Send DHCP reply (Unicast)
Read options and configure parameters

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateful Autoconfiguration (1 of 2)
125
Build link-local address
Join all-nodes multicast group
Join solicited node multicast group
Send NS
My address is unique!
Send RS
Send RA (M bit = 1)
Can’t build addresses!

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Stateful Autoconfiguration (2 of 2)
126
Send DHCP request To FF02::1:2 (All DHCP Agents)
Send DHCP reply (Unicast—can be relayed)
Read options and configure addresses and parameters

IPv6 Neighbor Discovery: Configuration

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Router Advertisement
R3
R2
FEC0:0:0:2003::/64
FEC0:0:0:2000::/64
fe-0/0/0
::1
fe-0/0/1
::1
fe-0/0/1
::2
Enable router advertisement on this network
Host Host R1
fe-0/0/1
::2
128

IPv6 Transition Mechanisms

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 is a Floating Process
Always watch the IPv6 Working Group of the IETF http://tools.ietf.org/wg/ipv6/ Currently revisions to over 30 different RFC standards Great place to see current status listing 16 current draft standard versions as well Nice doc for SPs at:
– https://cisco-support-vm-prod.hosted.jivesoftware.com/docs/DOC-13985
130

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
A Transition Plan for the Internet
Transition is expected to take several years – Estimates for IPv4 address exhaustion: 2011–2012 IPv4 will not disappear
– Legacy protocol support issues – Protocols rarely disappear completely Transition enablers
– Vendors must provide IPv6 features and functionality comparable to IPv4 – Application vendors must add support for IPv6 – Customers must drive the transition Moving to IPv6 will not be painless
– Any attempt at a complete cutover date is doomed to fail! – Gradual transition schemes are necessary
131

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IETF Transition Schemes
IETF Network Working Group has several suggestions – IP Next Generation Transition Working Group (ngtrans) – http://www.ietf.org/html.charters/ngtrans-charter.html Basic Transition Mechanisms for IPv6 Hosts and Routers (RFC 4213) Suggested methods include:
– Dual-stack approach – Tunneling Static Dynamic
– Network Address Translation–Protocol Translation (NAT-PT) – (RFC 2766)
132

IPv6 Deployments: Dual Stack Deployment

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Dual Stack
Both IPv4 and IPv6 stacks are enabled.
Applications can talk to both.
Choice of the IP version is based on name lookup and application preference.
134

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Host Running Dual Stack
In a dual stack case, an application that: – Is IPv4- and IPv6-enabled – Asks the DNS for all types of addresses – Chooses one address and, for example, connects to the IPv6 address
DNS Server
www.xyz.com A and AAAA = * ?
2001:DB8:CAFE::1 2001:DB8:CAFE::1 10.1.1.1
IPv6
IPv4
135

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 using Dual Stack Backbone
All P + PE routers are capable of IPv4+IPv6 support Two IGPs supporting IPv4 and IPv6 Memory considerations for larger routing tables Native IPv6 multicast support All IPv6 traffic routed in global space Good for content distribution and global services (Internet)
IPv4/IPv6 Core
CE
IPv6 IPv4
PE P P PE CE IPv4
IPv6
IPv6 configured interface
IPv4 configured interface
Some or all interfaces in cloud dual configured
IPv6 + IPv4 Core IPv4 + IPv6 Edge IPv4 and/or IPv4 edge Dual Stack App
136

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Dual Stack Configuration
IPv4/IPv6 Core
CE
IPv6 IPv4
PE P P PE CE IPv4
IPv6
IPv6 + IPv4 Core IPv4 + IPv6 Edge IPv4 and/or IPv4 edge Dual Stack App
ipv6 unicast-routing interface Ethernet0 ip address 192.168.99.1 255.255.255.0 ipv6 address 2001:db8:213:1::1/64
137

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Dual-Stack Approach
Most devices are already configured with IPv4 As IPv6 is deployed:
– IPv6 software will be installed as a second Network Layer stack – IPv6 addresses will be configured on all devices Host will be responsible for deciding:
– When to use the IPv4 address – When to use the IPv6 address DNS has been updated to help! RFC 3363—Representing Internet Protocol Version 6 (IPv6) Addresses
in the Domain Name System (DNS)
138

IPv6 Multicast

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 and IPv6 Multicast Comparison Service IPv4 Solution IPv6 Solution
Addressing Range 32-bit, Class D 128-bit (112-bit Group)
Routing Protocol Independent, All IGPs and MBGP
Protocol Independent, All IGPs and MBGP with v6 mcast SAFI
Forwarding PIM-DM, PIM-SM, PIM-SSM, PIM-bidir, PIM-BSR
PIM-SM, PIM-SSM, PIM-bidir, PIM-BSR
Group Management IGMPv1, v2, v3 MLDv1, v2
Domain Control Boundary, Border Scope Identifier
Interdomain Solutions MSDP across Independent PIM Domains
Single RP within Globally Shared Domains
Static RP, BSR, No Auto-RP
Embedded RP 140

IPv6 Quality of Service

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Quality of Service IPv6 QoS
– Same architectural models as IPv4 – Differentiated Services (Traffic Class field) – Integrated Services (RSVP)
IPv6 traffic class – Value defined per applications, same DSCP for
applications over both IPv4 and IPv6 – decision to differentiate per protocol is an operational one
IPv6 flow label (RFC 3697) – A new 20-bit field in the IPv6 basic header – Its value cannot be changed by intermediate devices – No RFC regarding flow label usage yet
Transition – Mapping between IPv6 DSCP & IPv4 ToS or MPLS EXP
Version Traffic Class Flow Label
Payload Length Next Header Hop Limit
Source Address
Destination Address
142

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Exercise with QoS
IPv6 QoS This is an excellent opportunity to look at QoS as it stands currently within your
network What will change with IPv6 deployment? What needs to change with IPv6 deployment? All of life is merely a matter of perspective!
143

IPv6 Security: Differences to IPv4

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Security
145
SHARED ISSUES
IPv4 Vulnerabilities IPv6 Vulnerabilities

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Measuring the Length of a /64 Subnet…
…it will take almost 2 years for this light to reach the other end of the line
This line will be 1.2 million times longer than the distance from Earth to Sun
If we put all the available addresses in a line, with a density of one address per millimeter… …and turn on a flashlight on one end of this line…
2 years
146

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Reconnaissance in IPv6
Public servers will still need to be DNS reachable – More information collected by Google... Increased deployment/reliance on dynamic DNS
– More information will be in DNS Using peer-to-peer clients gives IPv6 addresses of peers Administrators may adopt easy-to-remember addresses (::10,::20,::BAD:F00D,
::C5C0 or simply IPv4 last octet for dual stack) By compromising hosts in a network, an attacker can learn new addresses to
scan Transition techniques (see further) derive IPv6 address from IPv4 address
– can scan again
147

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Remote Scanning Happens *Today*
Ports: 22/tcp, 25/tcp, 53/udp, 443/tcp and 9511/tcp, protocol 128. “Easy” host IDs: :: to ::2ff, ::1000 to ::10ac, ::2000 to ::2111 ::1:0 to ::1:1ff, ::500, ::aaa, ::fff ::1337, ::3128, ::2525, ::5353, ::6667, ::8000, ::aaaa, ::abcd, ::babe, ::café, ::beef, ::ffff ::[0-9]:25, ::[0-9]:53, ::[0-9]:80
148
Source: http://lists.cluenet.de/pipermail/ipv6-ops/2010-November/004367.html

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Scanning: Lessons Learned
Use infrastructure ACLs to protect the routers – iACL on the edge to deny packets to your routers – Implies having a good addressing plan Secure the hosts that have easy to guess addresses
– Avoid running unnecessary services – Regularly scan your hosts to check – Temporarily block unknown addresses with failed SSH logins
149

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Reconnaissance in IPv6? Easy with Multicast!
No need for reconnaissance anymore 3 site-local multicast addresses
– FF05::2 all-routers, FF05::FB mDNSv6, FF05::1:3 all DHCP servers Several link-local multicast addresses
– FF02::1 all nodes, FF02::2 all routers, FF02::F all UPnP, ... Some deprecated (RFC 3879) site-local addresses but still used
– FEC0:0:0:FFFF::1 DNS server
150
2001:db8:2::50
2001:db8:1::60
2001:db8:3::70
Attacker FF05::1:3
Source Destination Payload
DHCP Attack
http://www.iana.org/assignments/ipv6-multicast-addresses/

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Preventing Reconnaissance with IPv6 Multicast
The site-local/anycast addresses must be filtered at the border in order to make them unreachable from the outside ACL block ingress/egress traffic to
– Block FEC0::/10 (deprecated site-local addresses) – Permit mcast to FF02::/16 (link-local scope) – Permit mcast to FF0E::/16 (global scope) – Block all mcast
151
Organization A
Organization B ipv6 access-list NO_RECONNAISSANCE deny any fec0::/10 permit any ff02::/16 permit any ff0e::/16 deny any ff00::/8 permit any any

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Finding Some Hosts on the Local LAN…
152

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Virii and Worms in IPv6
Viruses and email, IM worms: IPv6 brings no change Other worms:
– IPv4: reliance on network scanning – IPv6: not so easy (see reconnaissance) => will use
alternative techniques
153
Worm developers will adapt to IPv6 IPv4 best practices around worm detection and mitigation
remain valid

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
He Only Wanted Some Free Smilies…
Users tricked to click on deceptive links “Free IQ test” Social networks are explored by
miscreants Social engineering and XSS are protocol-
independent
154

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
L3 Spoofing in IPv6
155
uRPF Remains the Primary Tool for Protecting Against L3 Spoofing
Access Layer
Spoofed IPv6 Source Address
X IPv6 Intranet/Internet
No Route to Src Addr prefix => Drop
Access Layer
Spoofed IPv6 Source Address
X IPv6 Intranet/Internet
No Route to Src Addr prefix out the packet inbound interface => Drop
uRPF Loose Mode
uRPF Strict Mode ipv6 verify unicast source reachable-via rx
ipv6 verify unicast source reachable-via any

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Preventing Routing Header Attacks
Apply same policy for IPv6 as for Ipv4: – Block Routing Header type 0 Prevent processing at the intermediate nodes
– no ipv6 source-route – Windows, Linux, Mac OS: default setting At the edge
– With an ACL blocking routing header RFC 5095 (Dec 2007) RH0 is deprecated
– Default IOS changed in 12.4(15)T to ignore and drop RH0 – ASA drops RH0 by default
156

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 Broadcast Amplification: Smurf
157
ICMP REQ D=160.154.5.255 S= 172.18.1.2
160.154.5.0
Attempt to Overwhelm Destination
ICMP REPLY D=172.18.1.2 S=160.154.5.19
ICMP REPLY D=172.18.1.2 S=160.154.5.18
ICMP REPLY D=172.18.1.2 S=160.154.5.17
ICMP REPLY D=172.18.1.2 S=160.154.5.16
ICMP REPLY D=172.18.1.2 S=160.154.5.15
ICMP REPLY D=172.18.1.2 S=160.154.5.14
172.18.1.2
Belgian Schtroumpf

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 and Broadcasts
There are no broadcast addresses in IPv6 Broadcast address functionality is replaced with appropriate link local multicast
addresses – Link Local All Nodes Multicast—FF02::1 – Link Local All Routers Multicast—FF02::2 – Link Local All mDNS Multicast—FF02::FB
– Note: anti-spoofing also blocks amplification attacks because a remote attacker cannot
masquerade as his victim
158
http://iana.org/assignments/ipv6-multicast-addresses/

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 and Other Amplification Vectors
IOS implements correctly RFC 4443 ICMPv6 – No ping-pong on a physical point-to-point link Section 3.1 – No ICMP error message should be generated in response to a packet with a multicast
destination address Section 2.4 (e.3) – Exceptions for Section 2.4 (e.3) – packet too big message – the parameter problem message
159
•Rate Limit egress ICMP Packets •Rate limit ICMP messages generation •Secure the multicast network (source specific multicast) •Note: Implement Ingress Filtering of Packets with IPv6 Multicast Source Addresses

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Attacks with Strong IPv4 Similarities
Sniffing – IPv6 is no more or less likely to fall victim to a sniffing attack than IPv4 Application layer attacks
– The majority of vulnerabilities on the Internet today are at the application layer, something that IPSec will do nothing to prevent
Rogue devices – Rogue devices will be as easy to insert into an IPv6 network as in IPv4 Man-in-the-Middle Attacks (MITM)
– Without strong mutual authentication, any attacks utilizing MITM will have the same likelihood in IPv6 as in IPv4
Flooding – Flooding attacks are identical between IPv4 and IPv6
160

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
By the Way: It Is Real IPv6 Hacking Tools
Sniffers/packet capture – Snort – TCPdump – Sun Solaris snoop – COLD – Wireshark – Analyzer – Windump – WinPcap
Scanners – IPv6 security scanner – Halfscan6 – Nmap – Strobe – Netcat
DoS Tools – 6tunneldos – 4to6ddos – Imps6-tools
Packet forgers – Scapy6 – SendIP – Packit – Spak6
Complete tool – http://www.thc.org/thc-ipv6/
161
Let the Games Begin

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Privacy Extensions (RFC 3041)
Temporary addresses for IPv6 host client application, e.g. web browser
– Inhibit device/user tracking – Random 64 bit interface ID, then run Duplicate Address Detection
before using it – Rate of change based on local policy
2001
/32 /48 /64 /23 Interface ID
Recommendation: Use Privacy Extensions for External Communication but not for Internal Networks (Troubleshooting and Attack Trace Back)
162

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
The IPsec Myth: End-to-End will Save the World
IPv6 mandates the implementation of IPsec IPv6 does not require the use of IPsec Some organizations believe that IPsec should be used to secure all flows...
– Interesting scalability issue (n2 issue with IPsec) – Need to trust endpoints and end-users because the network cannot secure the traffic:
no IPS, no ACL, no firewall – IOS 12.4(20)T can parse the AH – Network telemetry is blinded: NetFlow of little use – Network services hindered: what about QoS?
163
Recommendation: do not use IPsec end to end within an administrative domain. Suggestion: Reserve IPsec for residential or hostile environment or high profile targets.

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv4 to IPv6 Transition Challenges
16+ methods, possibly in combination Dual stack
– Consider security for both protocols – Cross v4/v6 abuse – Resiliency (shared resources) Tunnels
– Bypass firewalls (protocol 41 or UDP) – Can cause asymmetric traffic (hence breaking stateful firewalls)
164

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Dual Stack Host Considerations
Host security on a dual-stack device – Applications can be subject to attack on both IPv6 and IPv4 – Fate sharing: as secure as the least secure stack... Host security controls should block and inspect traffic from both IP versions
– Host intrusion prevention, personal firewalls, VPN clients, etc.
165
Dual Stack Client
IPv4 IPsecVPN with No Split Tunneling
Does the IPsec Client Stop an Inbound IPv6 Exploit?
IPv6 HDR IPv6 Exploit

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
No IPv6 Network = No Problem? Wrong!
IPv6 enabled by default on all modern OSes Applications prefer IPv6 addresses “Blackhat” may not be malicious (Windows with ICS) Time to think about deploying IPv6
166
IPv4 Internet
Client Dualstack Server
IPv4-only segment
Inject RA
IPv6 I have IPv6 ! Let’s use it !

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Tunneling Summary
RFC 1933/2893 configured and automatic tunnels
RFC 2401 IPSec tunnel
RFC 2473 IPv6 generic packet tunnel
RFC 2529 6over4 tunnel
RFC 3056 6to4 tunnel
RFC 5214 ISATAP tunnel
MobileIPv6 (uses RFC2473)
RFC 4380 Teredo tunnels
RFC5569 6RD
Only allow authorized endpoints to establish tunnels
Static tunnels are deemed as “more secure,” but less scalable
Automatic tunneling mechanisms are susceptible to packet forgery and DoS attacks
These tools have the same risk as IPv4, just new avenues of exploitation
Automatic IPv6 over IPv4 tunnels could be secured by IPv4 IPSec
167

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 in IPv4 Tunnel
L3-L4 Spoofing in IPv6 over IPv4 Tunnels
Most IPv4/IPv6 transition mechanisms have no authentication built in => an IPv4 attacker can inject traffic if spoofing on IPv4 and
IPv6 addresses
168
Public IPv4 Internet
Server B Server A
Tunnel Termination
Tunnel Termination
IPv6 Network IPv6 Network
IPv6 ACLs Are Ineffective Since IPv4 & IPv6 Is Spoofed Tunnel Termination Forwards the Inner IPv6 Packet
IPv4
IPv6

IPv6 Security: Access-List Filtering

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Cisco IOS IPv6 Extended Access Control Lists
Very much like in IPv4 – Filter traffic based on Source and destiion addresses Next header presence Layer 4 information
– Implicit deny all at the end of ACL – Empty ACL means traffic allowed – Reflexive and time based ACL Known extension headers (HbH, AH, RH, MH, destination, fragment) are scanned
until: – Layer 4 header found – Unknown extension header is found Side note for 7600 & other switches:
– No VLAN ACL – Port ACL on Nexus-7000, Cat 3750 (12.2(46)SE), Cat 4K (12.2(54)SG), – Cat 6K (12.2(33)SXI4)
170

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IOS IPv6 Extended ACL Can match on
– Upper layers: TCP, UDP, SCTP port numbers – TCP flags SYN, ACK, FIN, PUSH, URG, RST – ICMPv6 code and type – Traffic class (only six bits/8) = DSCP – Flow label (0-0xFFFFF)
IPv6 extension header – routing matches any RH, routing-type matches specific RH – mobility matches any MH, mobility-type matches specific MH – dest-option matches any, dest-option-type matches specific destination options – auth matches AH – Can skip AH (but not ESP) since IOS 12.4(20)T
fragments keyword matches – Non-initial fragments (same as IPv4) – And the first fragment if the L4 protocol cannot be determined
undetermined-transport keyword matches (only for deny) – Any packet whose L4 protocol cannot be determined: fragmented or unknown extension header
171

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Cisco IOS IPv6 ACL
172
Filtering Inbound Traffic to one Specific Destination Address
Prefix: 2001:db8:2c80:1000::/64
IPv6 Internet
2001:db8:2c80:1000::1
others
Serial 0
ipv6 access-list MY_ACL remark basic anti-spoofing permit any 2001:db8:2c80:1000::1/128 deny 2001:db8:2c80:1000::/64 any interface Serial 0 ipv6 traffic-filter MY_ACL in

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 ACL Implicit Rules - RFC 4890
Implicit entries exist at the end of each IPv6 ACL to allow neighbor discovery: Nexus 7000 also allows RS & RA
173
permit icmp any any nd-na permit icmp any any nd-ns deny ipv6 any any

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 ACL Implicit Rules
174
The beginner’s mistake is to add a deny log at the end of IPv6 ACL
Solution, explicitly add the implicit ACE
! Now log all denied packets deny IPv6 any any log ! Hey . . . I forget about these implicit lines permit icmp any any nd-na permit icmp any any nd-ns deny ipv6 any any
. . . ! Now log all denied packets permit icmp any any nd-na permit icmp any any nd-ns deny ipv6 any any log

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Example: Rogue RA & DHCP Port ACL
175
ipv6 access-list ACCESS_PORT
remark Block all traffic DHCP server -> client
deny udp any eq 547 any eq 546
remark Block Router Advertisements
deny icmp any any router-advertisement
permit any any
Interface gigabitethernet 1/0/1
switchport
ipv6 traffic-filter ACCESS_PORT in
Note: Nexus-7000 and Cat 3750 12.2(46)SE, Catalyst 6500 12.2(33)SXI4, Catalyst 4500 12.2(54)SG

IPv6 Security: Prefix-List Filtering

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Creation of Prefix Lists
Like many things, from a command-line perspective the only thing that changes is “ip” changes to “ipv6” Cisco = ipv6 prefix-list (name) (prefix) (modifiers) At a binary level, IPv6 works the same as IPv4 does Same rules, different protocol!
177

IPv6 Routing Protocols

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Routing: The IPv4 – IPv6 Parallel RIP
RIPv2 for IPv4 RIPng for IPv6 Distinct but similar protocols with RIPng taking advantage of IPv6 specificities
OSPF OSPFv2 for IPv4 OSPFv3 for IPv6 Distinct but similar protocols with OSPFv3 being a cleaner implementation that takes advantage of IPv6 specificities
IS-IS Extended to support IPv6 Natural fit to some of the IPv6 foundational concepts Supports Single and Multi Topology operation
EIGRP Extended to support IPv6 (IPv6_REQUEST_TYPE, IPv6_METRIC_TYPE, IPv6_EXTERIOR_TYPE) Some changes reflecting IPv6 characteristics
BGP New MP_REACH_NLRI, MP_UNREACH_NLRI, AFI=2 with SAFI for Unicast/ /Label/VPN Peering over IPv6 or IPv4 (route maps)
For all intents and purposes, IPv6 IGPs are similar to their IPv4 counterparts
IPv6 IGPs have additional features that could lead to new designs 179

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Routing Protocols Static Routes
– BFD
RIPng – Graceful Restart and NSR
OSPFv3 – IPv6 EH authentication – IPSec encryption (ESP Header) – Overloading – Graceful Restart and NSR – BFD (9.3) – P2P interface (9.4) – OSPF Rib-group for IPv6 – Realm support (IPv4 support) but without TE support
IS-IS – Authentication – Unicast Mesh Groups – Multicast Mesh Groups – Graceful Restart and NSR – BFD for dual stack interface (not for v6-only) – ISIS Rib-groups for ipv6
Multitopology IS-IS – Unicast – Multicast
BGP – Authentication – BGP peering to IPv6 endpoints – IPv6 routes over IPv4 peering – IPv6 Prefix Limits – Interface counters – Graceful Restart and NSR
BGPv6 supported families: – family inet6 unicast – family inet6 multicast – family inet6 labeled-unicast – Inet4 unicast (not supported)
Routing Policy – IPv6 multicast scoping – IPv6 address family – IPv6 prefixes – IPv6 route destination address
180

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Routing Protocols
IPv6 PIM – Multicast Address Support – PIMv2 – PIM Anycast RP – Statically Defined RP – Embedded RP Addresses – Source-Specific Multicast (SSM) – Multicast Listener Discovery (v1 and
v2) – Bootstrap Router (BSR) for IPv6 – Disable IPv6 PIM independently from
IPv4 (9.6)
L3VPN Multicast – NG MVPN: IPv6 multicast (2H2009)
MPLS Protocols • IPv6 Tunneling over MPLS LSPs • RSVP-TE for IPv6 (not scheduled
yet) • LDP for IPv6 (not scheduled yet)
MPLS VPNs • 6PE, 6VPE • VRF Table-label
181

IPv6 Routing Protocols: Static Routes

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Static Route Example
R1(config)# ipv6 route fde7:0e06:ef31::/48 null0 R1#sh ipv6 route static IPv6 Routing Table - Default - 2 entries Codes: C - Connected, L - Local, S - Static, U - Per-user Static route B - BGP, M - MIPv6, R - RIP, I1 - ISIS L1 I2 - ISIS L2, IA - ISIS interarea, IS - ISIS summary, D - EIGRP EX - EIGRP external O - OSPF Intra, OI - OSPF Inter, OE1 - OSPF ext 1, OE2 - OSPF ext 2 ON1 - OSPF NSSA ext 1, ON2 - OSPF NSSA ext 2 S FDE7:E06:EF31::/48 [1/0] via Null0, directly connected R1# R1(config)# ipv6 route 2300:0106:aa23::/48 fa0/0 R1(config)#do sh ipv6 route static | begin ^S S 2300:106:AA23::/48 [1/0] via FastEthernet0/0, directly connected S FDE7:E06:EF31::/48 [1/0] via Null0, directly connected R1(config)#
183

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Static Options All static parameters are optional
Parameters are like any other static route
R1(config)#ipv6 route 2300:0106:aa23::/48 fa0/0 ?
<1-254> Administrative distance
X:X:X:X::X IPv6 address of next-hop
multicast Route only usable by multicast
nexthop-vrf Nexthop IPv6 VRF
tag Tag value
unicast Route only usable by unicast
<cr>
184

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Routing Policy
Configured in the same way as routing policy for IPv4 – Similar match conditions and actions – Create policy first… – …then apply to inteface (PBR), neighbor (BGP), or routing protocol One new match condition
– Match protocol ipv6 Routing table built the same as always! Nothing new to learn for IPv6 though process
185

IPv6 Routing Protocols: OSPFv3

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Changes from OSPFv2 – Per Link Processing – Addition of flooding scope – New Link LSA – Handling of unknown LSA types – Virtual Link Changes – Authentication changes
187

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Per Link Processing – IPv6 uses the term “link” instead of network or subnet to indicate communication Interfaces connect to links Adjacencies are formed on link local addresses
– Multiple IPv6 subnets can be assigned to a single link Two nodes can talk directly over a single link, even if they do not share a common IPv6 subnet Network address and mask do not impact the formation of adjacencies
188

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Flooding Scope – Each LSA now contains two bits indicating the flooding scope AS scope, LSA is flooded throughout the AS Area scope, LSA is flooded only within an area Link-local scope, LSA is flooded only on the local link
– These changes also impact the names of the LSAs Type 3 (Summary LSA) is now called the inter-area-prefix-LSA Type 4 (Autonomous System Border LSA) is now called the inter-area-router-LSA Other new LSAs have been added
189

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
LSA Name LS Type code Flooding scope LSA Function code
Router LSA 0x2001 Area scope 1
Network LSA 0x2002 Area scope 2
Inter-Area-Prefix-LSA 0x2003 Area scope 3
Inter-Area-Router-LSA 0x2004 Area scope 4
AS-External-LSA 0x4005 AS scope 5
Group-membership-LSA 0x2006 Area scope 6
Type-7-LSA 0x2007 Area scope 7
Link-LSA 0x0008 Link-local scope 8
Intra-Area-Prefix-LSA 0x2009 Area scope 9
Flooding Scope
190

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Link LSA – Announces the IPv6 link local address to all the router(s) attached to the link This is needed for the next hop calculation
– Announce a list of IPv6 prefixes associated with the link This is used for a router attached to a LAN to announce its prefix to the DR so DR can include
this IPv6 address in its intra-area-prefix-LSA
– Announce the router’s options capability router to the DR The DR will then perform an “OR” operation on the options received from all the attached routers The final option field set in the network LSA
191

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Link LSA – Generated for every link that has two or more routers – Not be originated for virtual links – May be suppressed
192

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Handling Unknown LSA Types – Each LSA now contains an “unknown LSA” bit 0: Treat this LSA as a link local 1: Store and flood this LSA even if you don’t understand it
– This allows the deployment of new features in the future Routers that don’t understand the new feature will simply store and forward the LSA Features can be deployed at edges, within a flooding domain, etc., without the need to upgrade
all routers
193

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Virtual Link Requirements – At least one global/unique local IPv6 address in the transit area OSPFv3 normally sends LSAs with a link local source address This won’t work over a virtual link –the packet needs to be forwarded through the intervening area
– Advertisement of a /128 prefix If no /128 is available in the table, a /128 from within an existing prefix space will be used This provides most-specific reachability between the endpoints of the virtual link
194

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Authentication – OSPFv3 currently only supports IPsec for authentication Group keying is painful for IPsec There is current work in GDOI and other spaces to make group keying work better for this space
– There is current work in the OSPF working group to allow HMAC-SHA and other forms of “in packet” authentication
195

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
196
Router1# interface POS1/1 ipv6 address 2001:410:FFFF:1::1/64 ipv6 enable ipv6 ospf 100 area 0 interface POS2/0 ipv6 address 2001:B00:FFFF:1::2/64 ipv6 enable ipv6 ospf 100 area 1 ipv6 router ospf 100 router-id 10.1.1.3 Router2# interface POS3/0 ipv6 address 2001:B00:FFFF:1::1/64 ipv6 enable ipv6 ospf 100 area 1 ipv6 router ospf 100 router-id 10.1.1.4
Configuration & Show Example
POS 3/0 2001:b00:ffff:1::1/64
2001:b00:ffff:1::2/64 POS 2/0
Area 1
Area 0
POS 1/1 2001:410:ffff:1::1/64
A
B

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Router2#sh ipv6 ospf int pos 3/0 POS3/0 is up, line protocol is up Link Local Address FE80::290:86FF:FE5D:A000, Interface ID 7 Area 1, Process ID 100, Instance ID 0, Router ID 10.1.1.4 Network Type POINT_TO_POINT, Cost: 1 Transmit Delay is 1 sec, State POINT_TO_POINT, Timer intervals configured, Hello 10, Dead 40, Wait 40, Retransmit 5 Hello due in 00:00:02 Index 1/1/1, flood queue length 0 Next 0x0(0)/0x0(0)/0x0(0) Last flood scan length is 3, maximum is 3 Last flood scan time is 0 msec, maximum is 0 msec Neighbor Count is 1, Adjacent neighbor count is 1 Adjacent with neighbor 10.1.1.3 Suppress hello for 0 neighbor(s)
Configuration & Show Example
POS 3/0 2001:b00:ffff:1::1/64
2001:b00:ffff:1::2/64 POS 2/0
Area 1
Area 0
POS 1/1 2001:410:ffff:1::1/64
A
B
197

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Router2#sh ipv6 ospf neighbor detail Neighbor 10.1.1.3 In the area 1 via interface POS3/0 Neighbor: interface-id 8, link-local address FE80::2D0:FFFF:FE60:DFFF Neighbor priority is 1, State is FULL, 12 state changes Options is 0x630C34B9 Dead timer due in 00:00:33 Neighbor is up for 00:49:32 Index 1/1/1, retransmission queue length 0, number of retransmission 1 First 0x0(0)/0x0(0)/0x0(0) Next 0x0(0)/0x0(0)/0x0(0) Last retransmission scan length is 2, maximum is 2 Last retransmission scan time is 0 msec, maximum is 0 msec
Configuration & Show Example
POS 3/0 2001:b00:ffff:1::1/64
2001:b00:ffff:1::2/64 POS 2/0
Area 1
Area 0
POS 1/1 2001:410:ffff:1::1/64
A
B
198

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
199
Router2#sh ipv6 route IPv6 Routing Table - 5 entries Codes: C - Connected, L - Local, S - Static, R - RIP, B – BGP, U - Per-user Static route I1 - ISIS L1, I2 - ISIS L2, IA - ISIS interarea O - OSPF intra, OI - OSPF inter, OE1 - OSPF ext 1, OE2 - OSPF ext 2 OI 2001:410:FFFF:1::/64 [110/2] via FE80::2D0:FFFF:FE60:DFFF, POS3/0 C 2001:B00:FFFF:1::/64 [0/0] via ::, POS3/0 L 2001:B00:FFFF:1::1/128 [0/0] via ::, POS3/0 L FE80::/10 [0/0] via ::, Null0 L FF00::/8 [0/0] via ::, Null0
Configuration & Show Example
POS 3/0 2001:b00:ffff:1::1/64
2001:b00:ffff:1::2/64 POS 2/0
Area 1
Area 0
POS 1/1 2001:410:ffff:1::1/64
A
B

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3
Routing Considerations – New Routing Protocol New training, show commands, troubleshooting procedures Must run “dual stack” in the control plane
– Consider design carefully Be intentional about flooding domain boundaries Don’t just deploy “one big area” because you can, it’s simple, it’s a test, etc… Probably best to place ABRs in the same places as OSPFv2 just to facilitate management and
troubleshooting – IPv6 rollout must be contiguous Just like with the other IGPs…
200

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Differences to OSPFv2 (1 of 2)
Differences: – Protocol processing per link, not per subnet – Removal of addressing semantics Router and network LSAs have no addressing Uses intra-area-prefix LSA
– Flooding scope is generalized Encoded in the LSA type
– Support for multiple instances per link Instance ID in OSPF header
201

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Differences to OSPFv2 (2 of 2)
Differences (contd.): – Use of link-local addresses Used to originate packets
– Authentication removed Done at the IP (IPv6) layer
– LSA format changes New LSAs + renaming old ones
– Unknown LSA handling – Options field expanded V6 bit and R bit added
202

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
OSPFv3 LSA Types
LSA Function LS type Description Like OSPFv2
1 0x2001 Router LSA Type 1 Router LSAs
2 0x2002 Network LSA Type 2 Network LSAs
3 0x2003 Inter-Area-Prefix LSA Type 3 Summary LSAs
4 0x2004 Inter-Area-Router LSA Type 4 ASBR-Summary
5 0x4005 AS-External-LSA Type 5 AS-External LSA
6 0x2006 Group Membership LSA Type 6 Multicast
7 0x2007 Type-7 LSA Type 7 NSSA External
8 0x0008 Link LSA None
9 0x2009 Intra-Area-Prefix LSA Types 1 and 2
LSA Function U S2 S1
LS type field:
203

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
LSA Flooding Scope: Link-Local
Link LSAs are flooded on the local link only – Used to advertise link-local addresses to directly attached routers – Used to advertise IPv6 subnets on the link – Used by DR to collect option bits to associate with the network LSA
204
Link LSA

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
LSA Flooding Scope: Area
All LSAs, except link and AS-external, have area scope flooding – Router LSAs and intra-area-prefix LSAs are originated by each router – Network LSAs and intra-area-prefix LSAs are originated by each DR – Inter-area-prefix and inter-area-router are originated by ABR
205
Router LSA Network LSA Intra-Area-Prefix LSA
Inter-Area-Prefix Inter-Area-Router
ABR
Area 0 Area 1

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
LSA Flooding Scope: AS
AS-external LSAs are flooded throughout the entire OSPF AS – Originated by ASBR
206
Area 0
ASBR
Area 1 AS External LSA
OSPF routing domain RIP

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Same As OSPFv2
Similarities: – One of the similarities is the RID – OSPFv3 maintains a 32-bit RID that represents the router in the link-state database – The RID is not related to an IPv6 address like it is in IPv4 – Requires explicit configuration (assuming no IPv4 addresses are present) because
IPv6 addressing cannot be used
207

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Cisco IPv6 and OSPF
Customized globally – R1(config)# ipv6 router ospf (#) – R1(config-router)# area (#) range …….. Enabled on an interface
– R1(config-if)# ipv6 ospf (#) area-id (#) – R1(config-if)# ipv6 ospf (#) neighbor (addr)
208

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 and OSPF
Authentication is interesting – Requires IPSec be used by OSPF – Authentication fields are no longer part of OSPF packet, but signaled to IPv6 security
209

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 and OSPF - Security
Two methods, AH or ESP – Ipv6 ospf authentication – Ipv6 ospf encryption Examples (interface config)
– Ipv6 ospf authentication ipsec spi 500 md5 1234567890abcdef1234567890abcdef – Ipv6 ospf encryption ipsec spi 1001 esp null sha1
123456789A123456789B123456789C123456789D Examples (area config – encryption same format)
– Area 0 authentication ipsec spi 422 md5 1234567890abcdef1234567890abcdef
210

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Router ID Selection
Router ID selection: – IPv6 networks preserve the 32-bit router ID This is not an IPv4 address, it just looks like one!
– You can set RID manually under routing-options, although an existing IPv4 address can be used The Junos OS uses the first non-127/8 address it finds as the RID lo0 is the first interface activated, so a non-127/8 configured here serves as the RID If the Junos software does not find a suitable address on lo0, it examines the next interface
activated (normally fxp0) – IPv6 functionality should not depend on another protocol being configured, so set RID
manually!
211

IPv6 Routing Protocols: MBGP

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
MP-BGP Basics
Path Vector Protocol – Carries sequence of AS numbers indicating path
Ties Autonomous Systems together via Peering
Multiple address families: ipv4, ipv6, unicast, multicast
SiSiSiSi
SiSi SiSi
SiSi
AS 101 AS 201
AS 301
Peering
213

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
BGP-4 Extensions for IPv6
TCP Interaction – BGP-4 runs on top of TCP – This connection could be setup either over IPv4 or IPv6 Router ID
– When no IPv4 is configured, an explicit bgp router-id needs to be configured – This is needed as a BGP Identifier, this is used as a tie breaker, and is send within the
OPEN message
214

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Non Link Local Peering
Router A router bgp 1 no bgp default ipv4 unicast bgp router-id 1.1.1.1 neighbor 2001:db8:ffff:2::2 remote-as 2 address-family ipv6 neighbor 2001:db8:ffff:2::2 activate network 2003:3:2::/64 network 2003:3:3::/64
AS 1
AS 2
2001:db8:ffff:2/64
:1
:2
network 2003:3:2::/64 network 2003:3:3::/64
B
A
215

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
BGP-4 Extensions for IPv6 (RFC 2545)
BGP-4 carries only 3 pieces of information which is truly IPv4 specific: – NLRI in the UPDATE message contains an IPv4 prefix – NEXT_HOP path attribute in the UPDATE message contains a IPv4 address – BGP Identifier is in the OPEN message & AGGREGATOR attribute To make BGP-4 available for other network layer protocols, RFC 2858
(obsoletes RFC 2283) defines multi-protocol extensions for BGP-4 – Enables BGP-4 to carry information of other protocols e.g MPLS,IPv6 – New BGP-4 optional and non-transitive attributes: – MP_REACH_NLRI – MP_UNREACH_NLRI – Protocol independent NEXT_HOP attribute – Protocol independent NLRI attribute
216

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
BGP-4 Extensions for IPv6
Address Family Information (AFI) for IPv6 – AFI = 2 (RFC 1700) – Sub-AFI = 1 Unicast – Sub-AFI = 2 (Multicast for RPF check) – Sub-AFI = 3 for both Unicast and Multicast – Sub-AFI = 4 Label – Sub-AFI= 128 VPN
217

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
BGP-4 Extensions for IPv6
Next-hop contains a global IPv6 address or potentially a link local (for iBGP update this has to be changed to global IPv6 address with route-map) The value of the length of the next hop field on MP_REACH_NLRI attribute is
set to 16 when only global is present and is set to 32 if link local is present as well Link local address as a next-hop is only set if the BGP peer shares the subnet
with both routers (advertising and advertised)
218
AS1 AS2
B A C

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
BGP Overview
Path-vector EGP that uses multiple path attributes to select the active route – Originally designed for IPv4 – Extended to carry additional information Multicast VPNs IPv6
MBGP specifications – Multiprotocol extensions for BGP-4 RFC 4760—January 2007
– Use of BGP-4 multiprotocol extensions for IPv6 interdomain routing RFC 2545
219

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
MP-BGP and IPv6
Multiprotocol extensions for BGP4: – Adds new fields to identified the type of route being advertised – Make it possible to carry IPv6 routes on top of IPv4 BGP sessions IPv6-specific extensions:
– Scoped addresses: NEXT_HOP contains a global IPv6 address and potentially a link-local address (only when there is link-local reachability with the peer)
– NEXT_HOP and NLRI are expressed as IPv6 addresses and prefixes in the multiprotocol attributes
220

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Address-Families are new RIBs
Address families began with MBGP to separate RIB entries Common address-families are
– IPv6 (unicast | multicast) – Nsap – IPv4 Multicast – Vpnv4 – Vpnv6 – Ipv4 unicast vrf (name) Default is IPv4 Unicast
221

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Prior to Address Families
Router bgp 1001
– Neighbor 10.1.1.4 remote-as 1001 – Neighbor 10.1.1.4 update-source loopback 0
– Neighbor 10.1.1.4 route-map Bob in
– Neighbor 10.1.1.4 send-community – Network 10.1.100.0 mask 255.255.255.0 – Network 10.1.101.0 mask 255.255.255.0 – Redistribute static
222

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Way to Think About the “Old” Way
Router bgp 1001 – [Connections] – Neighbor 10.1.1.4 remote-as 1001 – Neighbor 10.1.1.4 update-source loopback 0 – [address-family ipv4] – Neighbor 10.1.1.4 route-map Bob in – Neighbor 10.1.1.4 activate – Neighbor 10.1.1.4 send-community – Network 10.1.100.0 mask 255.255.255.0 – Network 10.1.101.0 mask 255.255.255.0 – Redistribute static
223

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Activate Each Neighbor
Multiple neighbors can carry some or all of the supported families Activate each one Each RIB filters separately Each RIB name is important for NLRI information to be kept correctly Each RIB/Family information is separate Useful for running separate info over separate links/peering information
224

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
MBGP Configuration
AS 65001 AS 65002 Router2 Router1
Router1# interface FastEthernet0/0 ipv6 address 3FFE:B00:C18:2:1::F/64 router bgp 65001 no bgp default ipv4-unicast neighbor 3FFE:B00:C18:2:1::1 remote-as 65002 address-family ipv6 neighbor 3FFE:B00:C18:2:1::1 activate neighbor 3FFE:B00:C18:2:1::1 prefix-list bgp65002in in neighbor 3FFE:B00:C18:2:1::1 prefix-list bgp65002out out exit-address-family
3ffe:b00:c18:2:1::F 3ffe:b00:c18:2:1::1
225

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
MBGP Prefix Bidirectional Filtering
226
– Filtering BGP routing updates
3FFE:0B00:0001::/48 3FFE:0300::/32
3FFE:0B00::/24
Router2 Router1
3ffe:b00:c18:2:1::F 3ffe:b00:c18:2:1::1 Router1# router bgp 65001 no bgp default ipv4-unicast neighbor 3FFE:B00:C18:2:1::1 remote-as 65002 address-family ipv6 neighbor 3FFE:B00:C18:2:1::1 activate neighbor 3FFE:B00:C18:2:1::1 prefix-list bgp65002in in neighbor 3FFE:B00:C18:2:1::1 prefix-list bgp65002out out network 3FFE:B00::/24 exit-address-family ipv6 prefix-list bgp65002in seq 5 permit 3FFE::/16 le 24 ipv6 prefix-list bgp65002out seq 5 permit 3FFE::/16 le 24
3ffe:b00::/24

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
MBGP Config with Inbound Filtering
Configure BGP to accept legal prefixes only (prefix-list)
227
3ffe:b00:c18:2:1::f 3ffe:b00:c18:2:1::1
AS 65002
AS 65003 AS 65001
3ffe:b00:c18:2:1::2
router bgp 65001 no bgp default ipv4-unicast neighbor 3FFE:B00:C18:2:1::1 remote-as 65002 neighbor 3FFE:B00:C18:2:1::2 remote-as 65003 address-family ipv6 neighbor 3FFE:B00:C18:2:1::1 activate neighbor 3FFE:B00:C18:2:1::2 activate neighbor 3FFE:B00:C18:2:1::1 prefix-list Legal in neighbor 3FFE:B00:C18:2:1::2 prefix-list Legal in network 3FFE:B00::/24 exit-address-family ipv6 prefix-list Legal seq 5 permit 2001::/16 le 35 ipv6 prefix-list Legal seq 10 permit 3FFE::/17 ge 24 le 24 ipv6 prefix-list Legal seq 15 permit 3FFE:8000::/17 ge 28 le 28 ipv6 prefix-list Legal seq 20 permit 2002::/16

Appendices:
Additional Pseudo-Useful, but not Required Information

IPv6 ISP Deployments: General

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Static NAT
230
Fa0/0 IPv4 IPv6
network 172.18.30.1 3000:b00:ffff:1::1 192.168.199.1
A D
nat-pt# ipv6 unicast-routing interface FastEthernet0/1 ip address 192.168.199.1 255.255.255.0 ipv6 nat interface FastEthernet0/0 ipv6 address 3000:b00:ffff:1::/64 eui-64 no ip address ipv6 nat ipv6 nat prefix 3ffe:b00:ffff:ffff::/96 ipv6 nat v4v6 source 172.18.30.1 3000:b00:ffff:ffff::a ipv6 nat v6v4 source 3000:b00:ffff:1::1 192.168.199.2
NAT-PT
Fa0/1
Static NAT-PT configuration: 3000:b00:ffff:ffff::a 172.18.30.1
3000:b00:ffff:1::1 192.168.199.2

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
IPv6 Dynamic NAT
231
Fa0/0 IPv4 IPv6
network
3000:b00:ffff:1::1 192.168.199.1 A NAT-PT
Fa0/1 DNS D
172.18.31.1
ipv6 unicast-routing interface FastEthernet0/1 ip address 192.168.199.1 255.255.255.0 ipv6 nat interface FastEthernet0/0 ipv6 address 3000:b00:ffff:1::/64 eui-64 no ip address ipv6 nat ipv6 nat prefix 3000:b00:ffff:ffff::/96 ipv6 nat translation timeout 3600 ipv6 prefix-list v6-list permit 3000:b00:ffff::/48 ipv6 nat v6v4 pool v4-pool 192.168.199.50 192.168.199.100 prefix-length 24 ipv6 nat v6v4 source list v6-list pool v4-pool ipv6 nat v4v6 source 172.18.31.1 3000:b00:ffff:ffff::53

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Questions & Answers
232

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Recommended Reading
Continue your Networkers at Cisco Live learning experience with further reading from Cisco Press Check the Recommended Reading flyer for
suggested books
233
Available Onsite at the Cisco Company Store

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Final Thoughts
Get hands-on experience with the Walk-in Labs located in World of Solutions, booth 1042 Come see demos of many key solutions and products in the main Cisco booth
2924 Visit www.ciscoLive365.com after the event for updated PDFs, on-demand
session videos, networking, and more! Follow Cisco Live! using social media:
– Facebook: https://www.facebook.com/ciscoliveus – Twitter: https://twitter.com/#!/CiscoLive – LinkedIn Group: http://linkd.in/CiscoLI
234

© 2013 Cisco and/or its affiliates. All rights reserved. BRKCRT-9344 Cisco Public
Maximize your Cisco Live experience with your free Cisco Live 365 account. Download session PDFs, view sessions on-demand and participate in live activities throughout the year. Click the Enter Cisco Live 365 button in your Cisco Live portal to log in.
Complete Your Online Session Evaluation
Give us your feedback and you could win fabulous prizes. Winners announced daily. Receive 20 Cisco Daily Challenge
points for each session evaluation you complete. Complete your session evaluation
online now through either the mobile app or internet kiosk stations.
235