Information Resources Management College National Defense University EA Development and Authority...
Transcript of Information Resources Management College National Defense University EA Development and Authority...

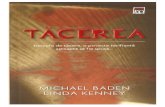
Information Resources Management CollegeNational Defense University
EA Development and Authority
Con Kenney3 August 2010
“A global learning community for government’s most promising information leaders.”

2
Agenda
Useful applications of EA Simple Lifecycle Model To apply EA the agency must align, integrate, and
informate its controls Controls Many IT Investments Don’t Deliver Reducing IT Investment Failure Where to Start? It Depends.

3
Useful applications of EA
Performance of IT Investments (Portfolio ROI) Cost and efficiency of IT infrastructure (TCO) Service-enablement of information systems (Reuse) Business process reengineering (Process cost) Delivery of new offerings (Public value) Reorganization (Clarity of message rated by
employees) Strategy-making and testing (Executive
participation)

4
Simple Lifecycle Model
Vision/Mission
Strategy
Portfolio
ProblemsSolutions
MatchesSponsors
Candidate Solutions
Rating & Ranking Candidate Solutions
Recommended Solutions
Approved Solutions
Budgeted SolutionsImplementation
Operations
Enterprise Architecture, Program Performance and Financial Performance Management

5
To apply EA the agency must align, integrate, and informate its controls
Organizational decisions depend on controls – EA is one of many
To support decisions EA has to be part of the controls EA depends on other controls such as asset inventory or IT
standards and supports other controls such as strategic planning or budgeting
Informated Controls can give decision-makers information about the state and performance of organizational processes and tools for intervening to improve performance
If the controls are inconsistent, the information produced by them will be inconsistent, and the EA will be less useful
The absence of certain controls such as data management may prevent EA from delivering much value at all

6
Enterprise
Mission
Business Management
Federal-wide
IT Controls
Federal-wide Controls
Exhibit 300 Exhibit 53 FISMA PMA GPRA OMB PART OMB circulars OPM rules FAR GAO Audits

7
Enterprise
Mission
Business Management
Federal-wide
IT Controls
Enterprise-wide Controls
Strategic Plan Budget and budget
guidance Acquisition policy Personnel policy Enterprise Architecture Certification and
Accreditation Performance reporting Organizational orders Operational policy e.g.
CM

8
Enterprise
Mission
Business Management
Federal-wide
IT Controls
Mission Controls
Mission-specific policy and orders
Instruction manuals Strategic plan Budget Portfolio Operational QC and QA Hiring and training
practices Job design Technical standards

9
Enterprise
Mission
Business Management
Federal-wide
IT Controls
Business Management Controls
Budget guidance Committing Obligating
Acquisitions guidance Initiating Acquiring Deploying Decommissioning
HR personnel management policies
Physical security

10
Enterprise
Mission
Business Management
Federal-wide
IT Controls
IT Controls
IT standards Solution development
lifecycle methodology Logical security Boundary protection Identity management Encryption Approved devices Network access Service desk Change management Asset inventory

11
Many IT Investments Don’t Deliver
Given the scale of government programs, sometimes large IT investments are unavoidable
According to a long-term study of IT investments by the Standish Group Only one-third of all IT investments deliver the
expected functionality about on time and on budget
Evidence suggests that the probability of a failed IT investment rises with its cost

12
Reducing IT Investment Failure
The processes required to conceive of, architect, choose, fund, implement, and operate IT investments span many organizational disciplines (strategy, finance, solution development, etc)
Looking at these processes together as a system helps us see many disconnects
According to the IT literature, the biggest causes of IT investment failure are a lack of business support, inadequate program management, and misunderstood requirements

13
Key Controls for Portfolio Management (PfM)
Enterprise
Mission
Business
Federal
IT
Exhibit 300Exhibit 53FISMAPMAGPRA
OMB PAROMB circularsOPM rulesFAR
GAO Audits
Strategic PlanBudget and budget guidanceAcquisition policyPersonnel policy
Enterprise ArchitectureCertification and Accreditation
Performance reportingOrganizational ordersOperational policy e.g. CM
Mission-specific policy and ordersInstruction manualsStrategic planBudgetPortfolioOperational QC and QAHiring and training practicesJob designTechnical standards
Budget guidanceCommittingObligating
Acquisitions guidanceInitiatingAcquiringDeployingDecommissioning
HR personnel management policiesPhysical security
IT standards
Solution development lifecycle methodologyLogical securityBoundary protectionIdentity managementEncryptionApproved devicesNetwork accessService desk
Change managementAsset inventory

14
Key Steps to FAA PfM over time
“Getting to Green” in the PMA Scorecard Establishing EA policy in our acquisition system Compiling an inventory of IT assets Chartering investment, architecture, and technology review boards Agreeing to IT standards Modeling portfolio management process Strengthening configuration management policy Developing “investment roadmaps” to document our transition
strategy Establishing portfolio management policy Piloting portfolio management

15
Complex mesh of stakeholders and controls
Step Stakeholders Controls
“Getting to Green” Federal, Enterprise PMA, EA
EA in acquisitions Enterprise, Business, IT Acquisition policy, Acquisitions guidance
IT asset inventory IT Asset inventory
Chartering boards Federal, Enterprise, IT PMA, GAO Audits, EA
Modeling PfM Federal, Enterprise GAO Audits, EA
IT standards IT IT standards
Configuration management policy
Mission, IT Operational policy, Change management
“Investment roadmaps” Enterprise, Mission Strategic plan, Budget
PfM policy Federal, Enterprise GAO Audits, Strategic Plan,
Budget, EA
Piloting PfM Mission Strategic plan, Budget,
Portfolio

16
Where to Start? It depends.
Current state of the organization Stable vs. in flux Happy vs. unhappy stakeholders Well-funded vs. subsistence
Strategic challenges facing the organization More of the same vs. transformation Stakeholder support vs. opposition
Concerns of authorizing agencies OMB passback GAO audits IG reports
Strengths of the IT leaders Skills Relationships with key internal and external partners Understanding of the agency’s mission and processes

17
Backup

18
Overview of Changes to Controls over time
Exhibit 300Exhibit 53FISMAPMAGPRAOMB PARTOMB circularsOPM rulesFARGAO Audits
Strategic PlanBudget and budget
guidanceAcquisition policyPersonnel policyEnterprise ArchitectureCertification and
AccreditationPerformance reportingOrganizational ordersOperational policy eg. CM
Mission-specific policy and orders
Instruction manualsStrategic planBudgetPortfolioOperational QC and QAHiring and training practicesJob designTechnical standards
Budget guidance
Committing
Obligating
Acquisitions guidance
Initiating
Acquiring
Deploying
Decommissioning
HR personnel management policies
Physical security
IT standardsSolution development
lifecycle methodology
Logical securityBoundary protectionIdentity managementEncryptionApproved devicesNetwork accessService deskChange managementAsset inventory
Key
Pre-2003 xxxxxxx
2003-5 xxxxxxx
2006-8 xxxxxxx
2009-11 xxxxxxx

19
Key Controls for Cost and efficiency of IT infrastructure
Enterprise
Mission
Business
Federal
IT
Exhibit 300Exhibit 53FISMAPMAGPRAOMB PAROMB circularsOPM rulesFARGAO Audits
Strategic Plan
Budget and budget guidanceAcquisition policyPersonnel policyEnterprise ArchitectureCertification and AccreditationPerformance reportingOrganizational orders
Operational policy e.g. CMMission-specific policy and ordersInstruction manualsStrategic plan
BudgetPortfolioOperational QC and QAHiring and training practicesJob design
Technical standards
Budget guidanceCommittingObligating
Acquisitions guidanceInitiatingAcquiringDeployingDecommissioning
HR personnel management policiesPhysical security
IT standardsSolution development lifecycle methodologyLogical securityBoundary protectionIdentity managementEncryption
Approved devicesNetwork accessService deskChange managementAsset inventory

20
Mechanism/
Benefit
EA Govern-
ance
Standards Method-
ology
Tools Asset
Disco-very
Asset Lifecycle
IT Strategy Pro Forma IT Budget
Search Cost Mod Mod Mod Mod High High High High High
Compliance Cost
Low Mod Mod Mod High High High High High
Non-compliance cost
Low Low Mod Mod High High High High High
Unnecessary & redundant investment
Mod Mod Mod High High High High High High
Lifecycle reuse
Low Low Low Mod High High High High High
IT Optimization
Low Low Low Low Mod Mod High High High
Cumulative Benefits of Controls