Ece seminar 20070927
-
Upload
todd-deshane -
Category
Technology
-
view
1.135 -
download
0
Transcript of Ece seminar 20070927
System Support for Rapid Recovery and Attack Resistance
A Seminar by
Todd Deshane
Advisor: Jeanna Matthews
Overview
Motivation of Technology
Demo
Motivation for This Work
Goals
Background
Prototype Architecture
Evaluation of Prototype
Plan of Work
Terminology
Virtual Machine Monitor (VMM)
Also know as: hypervisor
Thin software layer between the hardware and guest operating system
First to the hardware
Examples of VMMs:
VMware, Xen, Parallels, Z/vm, MS Viridian, Qemu, KVM, ...
VMM with a Picture
VMM in real life - Demo
Xen running Windows and Linux guests
Virtualization Predictions
9 of 10 enterprises will have virtualization by 2007 - Yankee Group (August 2007)
Physical servers growth near zero within 2012 - Bernstein (August 2007)
Over 50% physical servers will be virtualized in 2011 - IDC (July 2007)
Virtualization services market to reach $11.7 billion by 2011 - IDC (July 2007)
Server market to hardly grow over 2% annually through 2011 because of virtualization - IDC (July 2007)
Virtualization Predictions (cont.)
25% of enterprise data center servers to be virtual by 2010 - Intel (July 2007)
A Microsoft hypervisor for Vista expected in mid-2009 - Gartner (July 2007)
Virtualization will be part of nearly every aspect of IT by 2015 Gartner (May 2007)
3 million virtual machines expected in 2009 - Gartner (May 2007)
Virtualization Predictions (cont. again)
Virtualization and multicore will cost $2.4 billion in customer spending between 2006 and 2010 - IDC (March 2007)
OS Virtualization to become mainstream by 2010 - Gartner (December 2006)
Virtualization market to grow to $15 billion worldwide by 2009 - IDC (October 2006)
Our Work
System support for attack resistance and rapid recovery
Virtual Machine Technology
Intrusion Detection System
Virtual Private File Server
Motivation
Computers on the Internet are vulnerable
Even with latest updates and virus definitions
Zero day exploits
Malware effects
User data compromised
System controlled by attacker
Restoration of system and user data
Time-consuming
Difficult for users
Not always possible (i.e. digital photos)
"New methods are being invented, new tricks, and every year it gets worse... We are losing the battle... Most companies don't know they have been attacked." - Bruce Schneier
"The average top executive doesn't understand security, but we have to change that... Security is an imperative. It's no longer just a good idea." - Allen Kerr
"Virus incidences had surged between 2003, when they detected just over 10,000, and 2006, when they found 80,000. Criminal activity accounted for most of that increase." - Kaspersky Labs
"Very sophisticated tools are commercially available in black markets... This has made [the Internet] more attractive for organized crime: [criminals] no longer have to be geeks." - James Lewis
"Although security awareness continues to improve, hackers and malicious code authors are releasing threats faster than ever before, with approximately 200 per cent more malicious threats per day than two years ago." - Stuart McClure
"Over one third [of IT Companies] hit by a denial-of-service attack while over 44 percent had experienced either a pharming or cache poisoning attack." - Recent Secure64 Survey
Goals
Provide attack resistance and rapid recovery from exploits
Isolate and protect user data from attacks
Provide automatic and user-triggered checkpoints of system/application state
Safe testing of system and application updates
Facilitate forensic analysis
Background: Security
Early Internet based on openness/trust
First documented Internet worm 1988
Malware: large scale problem late 1990s
Criminal malware networks (botnets)
DDOS, digital blackmail, account/credit info
Attack defenses
Antivirus software
Firewalls
Intrusion detection systems
Background: Virtualization
Virtual Machine Monitor
Pioneered by IBM
Software/hardware co-evolution
Intel VT-x and AMD-V
Software/hardware co-evolution (again)
Next generation virtualization hardware
Xen hypervisor (VMM)
Paravirtual guests (i.e. Linux, *BSD)
HVM guests (i.e. Microsoft Windows)
Background: Virtualization+Security
VMs used as sandboxes
VMs can be monitored from below
System security and fault tolerance
Replicate system state to a backup VM
Secure logging and replay
Backtracking intrusions
Safe testing/integration of untrusted code
Protection against root kits
Background: System Reset Facilities
DeepFreeze
Restore to trusted checkpoint on each boot
Windows System Restore
Keep checkpoints of system state for rollback
Both of these lack:
User data protection/rollback
Attack prevention/detection
Prototype Architecture
Benefits of Prototype
Intrusion detection and attack prevention
Protection of user data
Checkpoint and restart of virtual machine appliances
Rapid first time installation
Model for software distribution
Complement and enhance backups
Evaluation of Prototype
Resistance/protection against attacks
Categorize attacks
Defense strategies against attacks
Performance overhead
Overhead of virtualization technology
Overhead of file system virtual machine
Evaluation of Prototype: Attacks
Backdoor attacks initiate and listen for connections to send and receive data
Attacks that copy infected executables to shared folders or attempt to destroy data
Attacks that harvest email addresses and other personal data
Attacks that exploit vulnerability in specific server software
Evaluation of Prototype: Defenses
Block unused ports
Detect unexpected behavior and rollback to trusted image
Restrictions on read, write, and/or append access to personal data
Detect unexpected behavior and rollback to trusted image
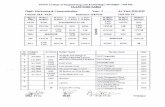
Evaluation of Prototype: Performance
Plan of Work
Construction and integration of a separate NET-VM component
Tight integration of NET-VM and FS-VM into virtual machine support layer of Xen
A comprehensive virtual machine appliance contract system
Evaluation of system
Performance
Functionality
Plan: Construct and Integrate NET-VM
Network Intrusion Detection System (snort)
Firewall (iptables)
Xen driver domain
Plan: Modified Architecture
Plan: Comprehensive Contract System
Virtual machine appliance contracts
Specify the behavior of appliances
Network access
File system access
Use existing NIDS and firewall rules
Build upon existing Xen configuration file
Add file system and network rule support
Plan: Evaluation of Modified System
Performance
I/O: read, write
Network: send, receive
CPU overhead
Functionality
Resistance to attack
Recovery from attack
Construct virtual machine appliances
Related Projects at Clarkson
Log-Structured File System for FS-VM
Enable rollback of writes with LFS
Tools for forensic analysis
Capture/export compromised VM
Recommend defense strategies
Isolation Testing of Virtualization Systems
Power Testing of Virtualization Systems
Recommend/improve power-friendly VMMs
Questions/Comments?
Backup Slides
Evaluation of Prototype: Attacks
Category/Behavior: Backdoor attacks initiate and listen for connections to send and receive data
Examples: W32.MyDoom, W32.Bagel
Defenses:
Block unused ports
Detect unexpected behavior and rollback to trusted image
Evaluation of Prototype: Attacks
Category/Behavior: Attacks that copy infected executables to shared folders or attempt to destroy data
Examples: W32.Netsky, W32.Netad
Defenses:
Restrictions on write access to personal data
Detect unexpected behavior and rollback to trusted image
Evaluation of Prototype: Attacks
Category/Behavior: Attacks that harvest email addresses and other personal data
Examples: W32.Zafi.D, PWSteal.Ldpinch.E
Defenses:
Restrictions on read access to personal data
Detect unexpected behavior and rollback to trusted image
Evaluation of Prototype: Attacks
Category/Behavior: Attacks that exploit vulnerability in specific server software
Examples: MySQL UDF, Blaster, Slammer
Defenses:
Block unused ports (if not running the server software)
Detect unexpected behavior and rollback to trusted image (if running the server software)
Plan: Xen Support for NET-VM/FS-VM
NET-VM already possible (driver domain)
FS-VM granted file system access/control
Xen communicates rules to NET-VM and FS-VM when new domain created
NET-VM and FS-VM detect violations
Violations enforced/communicated to Xen
Appropriate actions taken by Xen
Shutdown/restart/restore guest, notify user, prepare guest for forensic analysis, etc.
Plan: File System Rule Language
# Example file system rule set for an email client.
fs_rule = [ 'id=1, read, 1024, 5' ] # read at most 1024 bytes of data in 5 seconds
fs_rule = [ 'id=2, append, 1024, 3' ] # append at most 1024 bytes of data in 3 seconds.
fs_rule = [ 'id=3, write, 320, 3' ] # write at most 320 bytes in 3 seconds
# The email mount point is accessible to the email client, and
fs_rules # with id=1 and id=2 are applied
disk = [ 'fsvm:/mnt/email, /home/user/mail,fs_rule=1:2' ]
# The email mount point is accessible to the email client, and fs_rules # with id=1 and id=3 are applied.disk = [ 'fsvm:/mnt/email, /home/user/attachments,fs_rule=1:3' ]
Plan: Network Rule Language
#Email client example continued
network_rule = ['id=1, iptables,
file=/etc/iptables/email_client']
network_rule = ['id=2, snort,
file=/etc/snort/rules/email_client']
vif = [ 'rate=2Mb/s, network_rule=1:2' ]
Questions/Comments?
Click to edit the title text format
Click to edit the outline text format
Second Outline Level
Third Outline Level
Fourth Outline Level
Fifth Outline Level
Sixth Outline Level
Seventh Outline Level
Eighth Outline Level
Ninth Outline Level