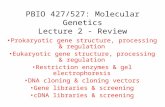
ECE 4450:427/527 - Computer Networks Spring 2014
-
Upload
lareina-gordon -
Category
Documents
-
view
28 -
download
3
description
Transcript of ECE 4450:427/527 - Computer Networks Spring 2014

ECE 4450:427/527 - Computer NetworksSpring 2015
Dr. Nghi TranDepartment of Electrical & Computer Engineering
Lecture 7.1: End-to-end Protocols
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 1

Discussions
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 2
• Up to now, we have learned various technologies to• Connect together a collection of computers/nodes• The collection ranges from simple Ethernet and wireless
networks to much larger scale one, e.g., global scale• Host-to-host packet delivery: logical communication
between hosts• Now, we turn the above host-to-host packet delivery into a
process-to-process communication channel• Logical communication between application processes
running on different hosts – Transport-layer protocols• Because it supports communication between application
program running in the end nodes, it is also called end-to-end protocols

Transport Layer vs. Network Layer
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 3
• Network layer: logical communication between hosts
• Transport layer: logical communication between processes – relies on, enhances,
network layer services
Household analogy:12 kids sending letters to 12
kids• processes = kids• app messages = letters in
envelopes• hosts = houses• transport protocol = Ann
and Bill who demux to in-house siblings
• network-layer protocol = postal service

Transport Layer
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 4
• Ann and Bill do work within respective homes - Protocols live in the end system: move messages from application processes to the network edge
• Assume Ann and Bill are on vacation, younger Susan and Tom substitute for them:• Pick up/deliver mail less frequent, or even lose letters• Susan and Tom do not provide the same service!!!• From network point of view: multiple transport protocols,
each offering a different service to applications.

Transport Layer
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 5
• Common properties that a transport protocol can be expected to provide– Guarantees message delivery– Delivers messages in the same order they were sent– Delivers at most one copy of each message– Supports arbitrarily large messages– Supports synchronization between the sender and the
receiver– Allows the receiver to apply flow control to the sender– Supports multiple application processes on each host

Internet Transport Protocols
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 6
• Simple Demultiplexer (UDP – User Datagram Protocol)– Allow multiple application processes on each host to share the
network • Reliable, in-order delivery (TCP – Transmission Control Protocol)– Connection set-up– Discarding of corrupted packets– Retransmission of lost packets– Flow control– Congestion control
• Remote Procedure Call (RPC): Request/reply service• Real-time Transport Protocol (RTP): real-time applications

UDP
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 7
• Simplest possible protocol: Simple Demultiplexer (UDP)– Allow multiple application processes on each host to share the
network – Aside it, no other functionality
• The only interesting issue: the form of the address used to identify the target process

Addressing Processes: Ports
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 8
• Application processes communicate by exchanging messages across the network• Web: a client browser process exchanges messages with a web
server process.
• We need something to identify receiving and sending processes: Port numbers• A web-server is identified by port 80• A mail server is identified by port 25• Port number is needed, since a host might run many network
applications

Port Discovery
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 9
• Use well-publicized ports for different services– DNS uses port 53– Email uses port 25– HTTP uses port 80
• Alternatively, use one port as a “port-mapper” service– Call 411 to learn the port of any other process– Allows for dynamic allocation of ports to different
services– Allows for the assignment of ports to newly created
services

UDP
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 10
• Processes are identified based on ports• 16 bits for each field yields 64K different identifiers• <IP, port> combination allows de-multiplexing at receiving host

Multiplexing and Demultiplexing
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 11
Host may be running multiple processes at the same timeThese processes
Generate multiple messages for the same hostGenerate multiple messages for multiple hosts
Transport layer multiplexingMultiplex messages from multiple processes Break down messages to segments and pass to network layer
Transport layer de-multiplexingReassemble messages at the receiving host and pass to the communication processes

TCP
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 12
• Connection oriented– Explicit set-up and tear-down of TCP session
• Stream-of-bytes service– Sends and receives a stream of bytes, not messages– Full-duplex
• Reliable, in-order delivery– Checksums to detect corrupted data– Acknowledgments & retransmissions for reliable delivery– Sequence numbers to detect losses and data reordering
• Demultiplexing mechanism• Flow control
– Prevents overflow of the receiver’s buffer: Allow receiver to limit how much data sender can transmit at a given time – End to end issue
• Congestion control– Prevent too much data from being injected into the network

TCP Duplicate Lower Layer Services?
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 13
• How is TCP different?–Runs over a route rather than a single physical link Needs to establish a connection and negotiate parameters (sliding window size)– Adapts to heterogeneous conditions
• RTT varies with connected hosts, time of the day etc, unpredictable• Flow control on computers with different resources
– Reorders and retransmits packets end-to-end•Even if packets are in order on one physical link this does not guarantee end-to-end ordering
– Provides congestion control• No immediate feedback from the link, no knowledge of conditions along
the way• Congestion control based on feedback

TCP
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 14
• Connection oriented– Explicit set-up and tear-down of TCP session
• Stream-of-bytes service– Sends and receives a stream of bytes, not messages– Full duplex
• Reliable, in-order delivery– Checksums/CRC to detect corrupted data– Acknowledgments & retransmissions for reliable delivery– Sequence numbers to detect losses and data reordering
• Demultiplexing mechanism• Flow control
– Prevents overflow of the receiver’s buffer: Allow receiver to limit how much data sender can transmit at a given time – End to end issue
• Congestion control– Prevent too much data from being injected into the network

TCP Segment
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 15
• TCP is a byte-oriented protocol, which means that the sender writes bytes into a TCP connection and the receiver reads bytes out of the TCP connection.
• Although “byte stream” describes the service TCP offers to application processes, TCP does not, itself, transmit individual bytes over the Internet.

TCP Segment
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 16
• Source: TCP buffers enough bytes from sending process to fill a reasonably sized packet and then sends this packet to destination: segment.
• Destination: TCP empties the contents of the packet into a receive buffer, and the receiving process reads from this buffer at its leisure.

TCP Segment
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 17
• IP packet– No bigger than Maximum Transmission Unit (MTU)– E.g., up to 1500 bytes on an Ethernet
• TCP packet– IP packet with a TCP header and data inside– TCP header is typically 20 bytes long
• TCP segment– No more than Maximum Segment Size (MSS) bytes– E.g., up to 1460 consecutive bytes
IP HdrIP Data
TCP HdrTCP Data (segment)

TCP Header
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 18
TCP Header Format

TCP Header
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 19
• The SrcPort and DstPort fields identify the source and destination ports, respectively.
• The Acknowledgment, SequenceNum, and AdvertisedWindow fields are all involved in TCP’s sliding window algorithm.
• Because TCP is a byte-oriented protocol, each byte of data has a sequence number; the SequenceNum field contains the sequence number for the first byte of data carried in that segment.
• The Acknowledgment and AdvertisedWindow fields carry information about the flow of data going in the other direction.
• HdrLen: Length of header in 32-bit words, e.g., 5

TCP Header
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 20
• The 6-bit Flags field is used to relay control information between TCP peers.
• The possible flags include SYN, FIN, RESET, PUSH, URG, and ACK.
• The SYN and FIN flags are used when establishing and terminating a TCP connection, respectively.
• The ACK flag is set any time the Acknowledgment field is valid, implying that the receiver should pay attention to it.

TCP Header
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 21
• The URG flag signifies that this segment contains urgent data. When this flag is set, the UrgPtr field indicates where the nonurgent data contained in this segment begins.
• The urgent data is contained at the front of the segment body, up to and including a value of UrgPtr bytes into the segment.
• The PUSH flag signifies that the sender invoked the push operation, which indicates to the receiving side of TCP that it should notify the receiving process of this fact.

TCP Header
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 22
• The RESET flag signifies that the receiver has become confused, it received a segment it did not expect to receive—and so wants to abort the connection.
• Finally, the Checksum field is used in exactly the same way as for UDP—it is computed over the TCP header, the TCP data, and the pseudoheader, which is made up of the source address, destination address, and length fields from the IP header.

Sliding Window Revisited
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 23
• TCP’s variant of the sliding window algorithm, which serves several purposes: – (1) it guarantees the reliable delivery of data, – (2) it ensures that data is delivered in order, and – (3) it enforces flow control between the sender and the receiver.

Sliding Window Revisited
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 24
Relationship between TCP send buffer (a) and receive buffer (b).
Sending Side– LastByteAcked ≤ LastByteSent– LastByteSent ≤ LastByteWritten
Receiving Side– LastByteRead < NextByteExpected– NextByteExpected ≤ LastByteRcvd + 1

TCP: Flow Control
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 25
• What is Overflow?• Receiver: Set a side a receive buffer for the connection• TCP connection receives bytes, places in the buffer• Application process will read data from buffer, but not
necessarily at the instant data arrives• It might be busy with some other task and might not even
attempt to read data• Therefore, the sender can very easily overflow the receive
buffer by sending to much data. • Flow-control service is needed.

Flow Control - Receiver
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 26
• Receiver advertises window no larger than its buffer size– LastByteRcvd – LastByteRead MaxRcvBufferAdvertisedWindow = MaxRcvBuffer – ((NextByteExpected – 1) – LastByteRead)?orAdvertisedWindow = MaxRcvBuffer – ((LastByteRcvd) – LastByteRead)?
• Example: LastByteRcvd = 5, LastByteRead = 1, NextByteExpected = 6, MaxRcvBuffer = 10– 5 – 1 10 – AdvertisedWindow = 10 - ((6 – 1) – 1) = 10 – 4 = 6– Too busy: go to 0

Flow Control - Sender
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 27
• Sender adheres to the AdvertisedWindow by – LastByteSent – LastByteAcked AdvertisedWindow– EffectiveWindow = AdvertisedWindow – (LastByteSent –
LastByteAcked)– Example: sent 7, ACK 5, EffectiveWindow = 6 – (7 - 5) = 4

Flow Control
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 28
• What if AdvertisedWindow is 0, i.e., when the receive buffer is full?
• A well-recognized protocol design rule to make the receive side as simple as possible: Smart Sender/Dumb Receiver

Connection Establishment/Termination in TCP (extra slide)
Dr. Nghi Tran (ECE-University of Akron) ECE 4450:427/527 Computer Networks 29
Timeline for three-way handshake algorithm