DES Block Cipher Hao Qi
-
Upload
information-security-awareness-group -
Category
Technology
-
view
449 -
download
0
description
Transcript of DES Block Cipher Hao Qi

DESDescription: Feistel, S-box Exhaustive Search, DC and LCModes of Operation
AESDescription: SPN, Branch numberSecurity and EfficiencyModes of Operation
Other CiphersLinear layer Confusion layer
1

2
DES(Data Encryption Standard)
http://en.wikipedia.org/wiki/Data_Encryption_Standard

Confusion: The ciphertext statistics should depend on the plaintext statistics in a manner too complicated to be exploited by the enemy cryptanalyst
Diffusion:Each digit of the plaintext should influence many digits of the ciphertext, and/orEach digit of the secret key should influence many digits of the the ciphertext.
Block cipher: ◦ A repetition of confusion(Substitution) and diffusion(Permutation)◦ Iteration: Weak Strong
3
Claude Shannon

4

Definition: Let Bn denote the set of bit strings of length n. A block cipher is an encryption algorithm E such that EK is
a permutation of Bn for each key K Characteristics
◦ Based on Shannon’s Theorem(1949)◦ Same P => Same C ◦ {|P| = |C|} 64 bit, |P| |K| 56 bit◦ Memoryless configuration◦ Operate as stream cipher depending on mode ◦ Shortcut cryptanalysis (DC, LC etc) in 90’s * DC: Differential Cryptanalysis, LC: Linear Cryptanalysis
5

Provide a high level of security Completely specify and easy to understand Security must depend on hidden key, not
algorithm Available to all users Adaptable for use in diverse applications Economically implementable in electronic
device Efficient to use Able to be validated Exportable * Federal Register, May 15, 1973
6

Based on Lucifer (1972) Developed by IBM and intervened by NSA Adopted Federal Standard by NIST, revised
every 5 years (~’98), 64bit block cipher, 56bit key 16 Round, Nonlinearity : S-box Cryptanalysis like DC, LC, etc. after 1992
* DC:Differential Cryptanalysis, LC : Linear Cryptanalysis
7

If we apply its operation 2 times, it returns to the original value, e.g., f(f(x)) = x.
Type of f-1(x) = f(x)
8
x1 x2
(a) (b)
y1 y2 y1=x1x2
(c)
y1=x1 g(x2)or x1 g(x2,k)
(d)
g
x1 x1 x1x2 x2x2
y2 y2 = x2y1 y2 = x2

9
PK
IP
f
FP
PC-2
C
16 Round
PC-1
Rot RotR0(32)L0(32)
R16 L16
PC-2
64 56
64
Round function
Key Scheduling

10
* Decryption is done by executing round key in the reverse order.

58 50 42 34 26 18 10 260 52 44 36 28 20 12 462 54 46 38 30 22 14 664 56 48 40 32 24 16 857 49 41 33 25 17 9 159 51 43 35 27 19 11 361 53 45 37 29 21 13 563 55 47 39 31 23 15 7
11
cf.) The 58th bit of x is the first bit of IP(x)
40 8 48 16 56 24 64 3239 7 47 15 55 23 63 3138 6 46 14 54 22 62 3037 5 45 13 53 21 61 2936 4 44 12 52 20 60 2835 3 43 11 51 19 59 2734 2 42 10 50 18 58 2633 1 41 9 49 17 57 25
IP & FP have no cryptanalytic significance.
IP FP= IP-1

12

13

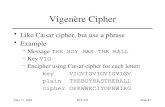
8 S-boxes (6 -> 4 bits) each row : permutation of 0-15 4 rows : choose by MSB & LSB of input some known design criteria
◦ not linear (affine)◦ Any one bit of the inputs changes at least two output
bits ◦ S(x) and S(x 001100) differs at least 2bits◦ S(x) S(x 11ef00) for any ef={00.01.10.11}◦ Resistance against DC etc.◦ The actual design principles have never been
revealed (U.S. classified information)
14

Input values mapping order
15
L R 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 150 0 14 4 13 1 2 15 11 8 3 10 6 12 5 9 0 7
0 1 0 15 7 4 14 2 13 1 10 6 12 11 9 5 3 8 1 0 4 1 14 8 13 6 2 11 15 12 9 7 3 10 5 01 1 15 12 8 2 4 9 1 7 5 11 3 14 10 0 6 13
S1(1 0111 0)=11=(1011)2

S1-box 14 4 13 1 2 15 11 8 3 10 6 12 5 9 0 7 0 15 7 4 14 2 13 1 10 6 12 11 9 5 3 8 4 1 14 8 13 6 2 11 15 12 9 7 3 10 5 0 15 12 8 2 4 9 1 7 5 11 3 14 10 0 6 13
S2-box 15 1 8 14 6 11 3 4 9 7 2 13 12 0 5 10 3 13 4 7 15 2 8 14 12 0 1 10 6 9 11 5 0 14 7 11 10 4 13 1 5 8 12 6 9 3 2 15 13 8 10 1 3 15 4 2 11 6 7 12 0 5 14 9
16
e.g.) S2(010010)= ?

S3-box 10 0 9 14 6 3 15 5 1 13 12 7 11 4 2 8 13 7 0 9 3 4 6 10 2 8 5 14 12 11 15 1 13 6 4 9 8 15 3 0 11 1 2 12 5 10 14 7 1 10 13 0 6 9 8 7 4 15 14 3 11 5 2 12
S4-box 7 13 14 3 0 6 9 10 1 2 8 5 11 12 4 15 13 8 11 5 6 15 0 3 4 7 2 12 1 10 14 9 10 6 9 0 12 11 7 13 15 1 3 14 5 2 8 4 3 15 0 6 10 1 13 8 9 4 5 11 12 7 2 14
17
S4-box is most linear than others.!!!

Short key size : 112 -> 56 bits by NSA
Classified design criteria Revision of standard every 5 yrs after 1977 by NIST
No more standard
18

(P,C) dependency with fixed Key : after 5 round
(K,C) dependency with fixed plaintext : after 5 round
Avalanche effect Cyclic Test : Random function Algebraic structure : Not a group i.e., E(K1, E(K2,P)) E(K3,P)
19

Complementary Prop.If C= E(K,P), C = E(K, P)
Weak Key : 4 keysE(K, E(K,P))=P
Semi-weak Keys : 12 keys (6 pairs)E(K1, E(K2,P))=P
Key Exhaustive Search : 255
20

RSA Data Security Inc’s protest against US’s export control(‘97)◦ $10,000(‘97) award ◦ Key search machine by Internet Loveland’s
Rocker Verser ◦ 60.1 Billion/1 day key search, succeeded in 18
quadrillion operations and 96 days 25% of Total 72 quadrillion (1q=1015 =0.1 kyung)90MHz, 16MB Memory Pentium(700 Million/sec)
◦ http://www.rsa.com/des/
21

Distributed.Net + EFF ◦ 100,000 PC on Network◦ 56hr
EFF(Electronic Frontier Foundation)◦ http://www.eff.org/
DEScracker◦ Specific tools ◦ 22hr 15min◦ 250,000$
22
P. Kocher

Cost-Optimized Parallel Code Breaker Machine by Univ. of Bochum, Germany and Kiel
Commercially available 120 FPGA’s of type XILINX Spartan3-1000 run in parallel
10,000$ of ¼ of EFF project
23

FEAL, GOST, IDEA, LOKI, SKIPJACK, MISTY, SEED
TEA (Tiny Encryption Algorithm) for RFID/USN, XTEA, XXTEA
ARIA, Serpent, Baseking, BATON, BEAR&LION, C2, Camellia, CAST-128,256, CIPHERUNICORN,CMEA, Cobra, Coconut98, Crypton, DEAL, E2, FROG, G-DES, Hasty Pudding Cipher, Hierocrypt,MUITL2, New Data Seal, SAFER-64,128, SHACAL, Square, Xenon, etc….
24

25
Algorithm Year Country Pt/Ct Key Round
DES 1977 USA 64 56 16
FEAL 1987 Japan 64 64 4,8,16,32
LOKI 1991 Australia 64 64 16
SEED 1998 Korea 128
128
16
IDEA 1990 Swiss 64 128 8
MISTY 1996 Japan 64 >8
128
SKIPJACK 1990 USA 64 3280
GOST 1989 Russia 64 256 32

26
AES (Rijndael)
Joan Daemen and Vincent Rijmen, “The Design ofRijndael, AES – The Advanced Encryption Standard”,Springer, 2002, ISBN 3-540-42580-2
FIPS Pub 197, Advanced Encryption Standard (AES),December 04, 2001
Rijndael : variable, AES : fixedVincent

Block cipher ◦128-bit blocks◦128/192/256-bit keys
Worldwide-royalty free More secure than Triple DES More efficient than Triple DES
27

28
◦ Jan. 2, 1997 : Announcement of intent to develop AES and request for comments
◦ Sep. 12, 1997 : Formal call for candidate algorithms◦ Aug. 20-22, 1998 : First AES Candidate Conference and
beginning of Round 1 evaluation (15 algorithms), Rome, Italy
◦ Mar. 22-23, 1999 : Second AES Candidate Conference, NY, USA
◦ Sep. 2000 : Final AES selection (Rijndael !)
Jan. 1997Call for
algorithms
Aug. 1998AES1
15 algorithms
Mar. 1999AES2
5 algorithms selected
Apr. 2000AES3
Announce winner in Sep, 2000

15 algorithms are proposed at AES1 conference
29

After AES2 conference, NIST selected the following 5 algorithms as the round 2 candidate algorithm.
30
Cipher Submitter Structure Nonlinear Component
MARS IBM Feistel structure Sbox DD-Rotation
RC6 RSA Lab. Feistel structure Rotation
Rijndael Daemen, Rijmen SPN structure Sbox
Serpent Anderson, Biham, Knudsen
SPN structure Sbox
Twofish Schneier et. al Feistel structure Sbox

Alg. (Round) Structure Rounds (Key size) Type of Attack Texts Mem.
Bytes Ops
MARS16 Core (C)
16 Mixing (M)Feistel
11C Amp. Boomerang 265 270 2229
16M, 5C16M, 5C
Diff. M-i-MAmp. Boomerang
250
269
2197
273
2247
2197
RC6(20) Feistel14 Stat. Disting. 2118 2112 2122
1215 (256)
Stat. Disting.Stat. Disting.
294
2119
242
2138
2119
2215
Rijndael10 (128)12 (192)14 (256)
SPN
6 Truncated Diff. 232 7*232 272
78 (256)9 (256)
Truncated Diff.Truncated Diff.Related Key
2128~ 2119
2128~ 2119
277
261
2101
NA
2120
2204
2224
Serpent(32)SPN
8 (192,256) Amp. Boomerang 2113 2119 2179
6 (256)6
7 (256)8 (192,256)
9 (256)
Meet-in-MiddleDifferentialDifferentialBoomerang
Amp. Boomerang
512271
241
2122
2110
2246
275
2126
2133
2212
2247
2103
2248
2163
2252
Twofish(16) Feistel 6 (256) Impossible Diff. NA NA 2256
31

32
Proposed by Joan Daemen, Vincent Rijmen(Belgium)Design choices
– Square type – Three distinct invertible uniform transformations(Layers)
Linear mixing layer : guarantee high diffusion Non-linear layer : parallel application of S-boxes Key addition layer : XOR the round key to the intermediate state
– Initial key addition, final key additionRepresentation of state and key
– Rectangular array of bytes with 4 rows (square type)– Nb : number of column of the state (4~8)– Nk : number of column of the cipher key (4~8)– Nb is independent from Nk

33
State (Nb=6) Key (Nk=4)
Number of rounds (Nr)

Block size: 128 Key size: 128/192/256 bit
Component Functions◦ ByteSubstitution(BS): S-
box◦ ShiftRow(SR):
CircularShift ◦ MixColumn(MC): Linear(Branch number: 5) ◦ AddRoundKey(ARK):
Omit MC in the last round.
34
Bit-wise key addition
Shift-Low(SR)
Mix-Column(MC)
Bit-wise key addition
Byte-wise substitution(BS)
BS, SR, ARK
44 bytearray Input
Input whitening
Roundtransformation
Outputtransformation
Output

Substitution-Permutation Network (SPN)◦ (Invertible) Nonlinear Layer: Confusion◦ (Invertible) Linear Layer: Diffusion
Branch Number◦ Measure Diffusion Power of Linear Layer◦ Let F be a linear transformation on n words.◦ W(a): the number of nonzero words in a. ◦ (F) = mina0 {W(a) + W(F(a))}◦ Rijndael: branch number =5
35

K-secure ◦ No shortcut attacks key-recover attack faster than
key-exhaustive search◦ No symmetry property such as complementary in
DES◦ No non-negligible classes of weak key as in IDEA◦ No Related-key attacks
Hermetic ◦ No weakness found for the majority of block
ciphers with same block and key length Rijndael is k-secure and hermetic
36

37
Mode of Operations

38
ECB (Electronic CodeBook) mode
EK
P
C
n
n
DK
C
P
n
n
i) Encryption ii) Decryption
IF Ci = Cj,DK(Ci) = DK(Cj)

CBC (Cipher Block Chaining)
39
P1 P2
IV
E E
C1 C2
E
Pl
Cl
IV
D D
P1 P2
D
Pl
C1 C2 Cl
Ci = EK(Pi Ci-1)
Pi = DK(Ci) Ci-1
IV : Initialization Vector
- 2 block Error Prog.- self-sync- If |Pl| |P|, Padding req’d
K
K
KK
KK

40
m-bit OFB (Output FeedBack)
m-bit
Pi
- No Error Prog.- Req’d external sync- Stream cipher- EK or DK
Ci = Pi O(EK)Pi = Ci O(EK)
I) Encryption II) Decryption
IV
E m-bit
Pi Ci
K
IV
E
Ci
K

41
m-bit CFB (Cipher FeedBack)
IV
E m-bit
Pi Ci
IV
Em-bit
Ci Pi
- Error prog. till an error disappears in the buffer- self-sync- EK or DK
Ci = Pi EK(Ci-1)Pi = Ci EK(Ci-1)
I) Encryption II) Decryption
K K

Counter mode
42
Ci = Pi EK(Ti)Pi = Ci EK(Ti)Ti = ctr+i -1 mod 2m
|P|, |ctr|= m,Parallel computation
P1
ctr
E
C1
C2
P2
Cm-1
K
ctr+1
E
ctr+m-1
EK K
Pm-1
C1
ctr
E
P1 P2
C2
Pm-1
K
ctr+1
E
ctr+m-1
EK K
Cm-1

CCM mode (Counter with CBC-MAC mode) Ctr + CBC Authenticated encryption by producing a
MAC as a part of the encryption process
43

Use of mode◦ ECB : key management, useless for file
encryption ◦ CBC : File encryption, useful for MAC ◦ m-bit CFB : self-sync, impossible to use
channel with low BER ◦ m-bit OFB : external-sync. m= 1, 8 or n◦ Ctr : secret ctr, parallel computation◦ CCM : authenticated encryption◦ Performance Degradation/ Cost Tradeoff
44

45
Differential Cryptanalysis

Introduction◦ Biham and Shamir : CR90, CR92◦ Efficient than Key Exhaustive Search ◦ Chosen Plaintext Attack◦ O(Breaking DES16) ~ 247
◦ Utilize the probabilistic distribution between input XOR and output XOR values Iteratively
◦ Stimulate to announce hidden criteria of DES [Cop92] ◦ Apply to other DES-like Ciphers * E.Biham, A. Shamir,”Differential Cryptanalysis of the Data Encryption Standard”, Springer-
Verlag, 1993
46

Discard linear components(IP, FP) Properties of XOR (X’ = X X* )
◦ {E,P,IP} : (P(X))’=P(X) P(X*)=P(X’)◦ XOR : (X Y)’=(X Y) (X* Y*)=X’ Y’◦ Mixing key : (X K)’=(X K) (X* K)=X’◦ Differences(=xor) are linear in linear operation and in
particular the result is key independent.
47

48
X’ = {0,1,…63}, Y’= {0,1,…15} For a given S-box, pre-compute the number of count of X’ and Y’ in a table * % of entry in DES S-boxes : 75 ~ 80%
X X*
Si-box
Y Y*
Y’
X’
XDTSi-box

49

2-round characteristic in S1 box (0Cx --> Ex with 14/64)
50
F
(00 80 82 00 60 00 00 00x)
F
(60 00 00 00 00 00 00 00x)
a’=60000000x p=14/64A’=00808200x
=P(E0000000x)
b’=0xB’=0x p=1
0110 0C=001100 E=1110

(1) Choose suitable Plaintext (Pt) XOR.(2) Get 2 Pts for a chosen Pt and obtain the
corresponding Ct by encryption (3) From Pt XOR and pair of Ct, get the expected
output XOR for the S-boxes of final round.(4) Count the maximum potential key at the final round
using the estimated key (5) Right key is a subkey of having large number of
pairs of expected output XOR
51

Self-concatenating probability Best iterative char. of DES
52
F
(19 60 00 00 00 00 00 00x)
F
(00 00 00 00 19 60 00 00x)
a’=0x p1=1A’=0x
b’=19 60 00 00x
E(b)=03 32 2C 00 00 00 00 00x
B’=0x p2 =14 x 8 x 10 / 643
= 1/234

53
Linear Cryptanalysis

Introduction◦ Matsui : EC931, CR942
◦ Known Plaintext Attack◦ O(Breaking DES16) ~ 243
12 HP W/S, 50-day operation◦ Utilize the probabilistic distribution between input
linear sum and output linear sum values Iteratively◦ Duality to DC : XOR branch vs.three-forked branch◦ Apply to other DES-like cryptosytems1. M.Matsui,”Linear Cryptanalysis Method for DES Cipher”, Proc. Of Eurocrypt’93,LNCS765, pp.386-397
2. M.Matsui,”The First Experimental Cryptanalysis of the Data Encryption Standard”, Proc. Of Crypto’94,LNCS839, pp.1-11.
54

55
Fi
Y i
X i-1 X i
K i
X i-1 Yi Xi
XOR branch after f-ft. i.e., DC goes downstream through f-ft.Xi = Xi-2 Yi-1 (3 i n)with {i=1}
n pi
Xi : Xi’s Differential value
Xi
Y i
X i
Y i-1
Y i
Y i
K i
Yi-1Xi
3-forked branch before f-ft. i.e.,LC goes upstream through f-ft. Yi = Yi-2 Xi-1 (3 i n)with 2n-1{i=1}
n |pi -1/2| Xi-1 : Xi-1’s Masking value
Fi
DC LC

(Goal) : Find linear approximation P[i1,i2,…,ia] C[j1,j2,…,jb]=K[k1,k2,…,kc]
with significant prob. p ( ½) where A[i,j,…,k]=A[i] A[j] … A[k]
(Algorithm)MLE(Maximum Likelihood Estimation)(Step 1) For given P and C, compute X=P[i1,i2,…,ia] C[j1,j2,…,jb],
let N = # of Pt given,(Step 2) if |X=0| > N/2 K[k1,k2,…,Kc]=0 else 1. if |X=0| < N/2 K[k1,k2,…,kc]=1 else 0.
56

For a S-box Sa,(a=1,2,…,8) of DESNSa(,)= #{x | 0 x < 64, parity(x) = parity(S(x))}
1 63 , 1 15, : dot product (bitwise AND)
Ex) NS5(16,15) =12◦ The 5-th input bit at S5-box is equal to the linear sum of 4 output
bits with probability 12/64. ◦ X[15] F(X,K)[7,18,24,29]=K[22] with 0.19◦ X[15] F(X,K)[7,18,24,29]=K[22] 1 with 1-0.19=0.81
(Note) least significant at the right and index 0 at the least significant bit (Little endian)
57

58

59
F1
F2
[15]
p1=12/64[7,18,24,29]
F3 p3=12/64
PPH
PL
K1
X1
K2
X2
[7,18,24,29] X3
K3[15]
[22]
[22]
C
X2[7,18,24,29] PH[7,18,24,29] PL[15] = K1[22] ---------- (1)
X2[7,18,24,29] CH[7,18,24,29] CL[15] = K3[22] ---------- (2)
CHCL
(1) (2) => X2[7,18,24,29] CH[7,18,24,29] CL[15] X2[7,18,24,29] PH[7,18,24,29] PL[15] = K1[22] K3[22] holding prob. = (p1 * p3 ) + (1 - p1) *(1-p3)* Discard IP and FP like DC

If independent prob. value, Xi ‘s ( 1 i n ) have prob pi to value 0, (1-pi) to value 1, p = {prob(X1 X2 … Xn ) = 0} is
p = 2n-1i=1n(pi - 1/2) +1/2.
The number of known pt req’d for LC with success prob. 97.7% is |p - 1/2|-2
60

Key size expansion◦Double Encryption
ek:E2(K2,E1(K1,P)), dk:D1(K1,D2(K2,C))Meet-in-the-middle attackNo effectiveness
◦Triple Encryption ek:E(K1,D(K2,E(K1,P))), dk:D(K1,E(K2,D(K1,C))) ek:E(K1,D(K2,E(K3,P))), dk:D(K3,E(K2,D(K1,C)))112 or 168 bits
61

62
Side Channel Attack

Traditional Cryptographic Model vs. Side Channel
63
Power Consumption / Timing / EM Emissions / Acoustic
Radiation / Temperature / Power Supply / Clock Rate, etc.
E() D()
Key
Attacker
Ke Kd
C
C=E(P,Ke)P=D(C,Kd)
Insecure channel
Secure channel
P D

☆ J. DAEMEN AND V. RIJMEN. The Design of Rijndael.AES - The Advanced Encryption Standard. Springer, 2002. 배성호 1
PT #1
★ M. E. HELLMAN. A cryptanalytic time-memory trade-off. IEEE Transactions of Information Theory, 26 (1980), 401-406. 임준현 2
☆ E. BIHAM AND A. SHAMIR. Differential cryptanalysis of the full 16-round DES. LNCS 740 (1993), 494-502. (CRYPTO '92) 장래영 3
☆ M. BELLARE AND P. ROGAWAY. Optimal asymmetric encryption. Lecture Notes in Computer Science, 950 (1995), 92-111. (EUROCRYPT '94) 조준희 4
☆ S. GOLDWASSER AND S. MICALI. Probabilistic encryption. Journal of Computer and Systems Science, 28 (1984), 270-299. 황대성 5
★J. H. Moore. Protocol failures in cryptosystems. In Contemporary Cryptology, The Science of Information Integrity, pages 541-558. IEEE Press, 1992.
남궁호 6
PT#2
☆M. BELLARE, J. KILIAN AND P. ROGAWAY. The security of the cipher block chaining message authentication code. Journal of Computer and System Sciences, 61 (2000), 362-399.
장래영 7
★ W. DIFFIE AND M. E. HELLMAN. New directions in cryptography. IEEE Transactions on Information Theory, 22 (1976), 644-654. 조준희 8
★ M. MATSUI. Linear cryptanalysis method for DES cipher. LNCS 765 (1994), 386-397. (EUROCRYPT '93) 배성호 9
☆M. BELLARE AND P. ROGAWAY. Random oracles are practical: a paradigm for designing efficient protocols. In First ACM Conference on Computer and Communications Security, pages 62-73. ACM Press, 1993.
김영삼 10
64

65
☆N. T. COURTOIS AND J. PIEPRZYK. Cryptanalysis of block ciphers with overdefined systems of equations. LNCS 2501 (2002), 267-287. (ASIACRYPT 2002)
조준희 11
PT#3
☆S. C. POHLIG AND M. E. HELLMAN. An improved algorithm for computing logarithms ove GF(p) and its cryptographic significance. IEEE Transations on Information Theory, 24 (1978), 106-110.
황대성 12
☆ M. J. WIENER. Cryptanalysis of short RSA secret exponents. IEEE Transations on Inforamtion Theory, 36 (1990), 553-558. 남궁호 13
★T. ELGAMAL. Apublic key cryptosystem and a signature scheme based on discrete logarithms. IEEE Transactions on Information Theory, 31 (1985), 469-472.
장래영 14
☆ D. CHAUM AND H. VAN ANTWERPEN. Undeniable signature. LNCS 435 (1990), 212-216. (CRYPTO '89) 신지강 15
☆☆P. BEAUCHEMIN AND G. BRASSARD, C. CREPEAU, C. GOUTIER and C. POMERANCE. The generation of random numbers that are probably prime. Journal of Cryptology, 1 (1988), 53-64.
남궁호 16
PT#4
☆☆M. BELLARE AND P. ROGAWAY. The exact security of digital signatures: how to sign with RSA and Rabin. LNCS, 1070(1996), 399-416. (EUROCRYPT '96)
임준현 17
★A. FIAT AND A. SHAMIR. How to prove yourself: practical solutions to identification and signature problems. LNCS 263 (1987), 186-194. (CRYPTO '86)
김영삼 18
☆☆ M. BELLARE. Practice-oriented provable-security. In Lectures on Data Security, pages 1-15. Springer, 1999. 신지강 19
★ A. FIAT AND M. NAOR. Broadcast encryption. LNCS 773 (1994), 480-491. (CRYPTO '93) 황대성 20

66
☆ M. BURMESTER AND Y. DESMEDT. A secure and efficient conference key distribution system. LNCS 250 (1994), 275-286 (EUROCRYPT '94) 김영삼 21
PT#5★ U. FEIGE, A. FIAT AND A. SHAMIR. Zero-knolwedge proofs of identity. Journal
of Cyrptology, 1 (1988), 77-94 신지강 22
☆ C. P. SHNORR. Efficient signature generation by smart cards. Journal of Cryptology, 4 (1991), 161-174. 임준현 23
☆ D. E. DENNING AND G. M. SACCO. Timestamps in key distribution protocols. Communications of the ACM 24 (1981), 533-536. 배성호 24
★ : 필수 , ☆: 난이도 1, ☆☆: 난이도 2( 가산점 )