COBIT 5® 2013 . . . ed oltre - · PDF fileCOBIT 5 for Assurance 318 $ 35 $ 175 COBIT 5 for...
-
Upload
dinhnguyet -
Category
Documents
-
view
238 -
download
10
Transcript of COBIT 5® 2013 . . . ed oltre - · PDF fileCOBIT 5 for Assurance 318 $ 35 $ 175 COBIT 5 for...

COBIT 5® – 2013 . . . ed oltre
Alberto Piamonte
Sessione di Studio 28 novembre 2013 Torino

2
Argomenti della Sessione
COBIT5 Principi ed Enablers Process Assessment 4.1 -> 5 Esempi Information Security Enabling Information Assurance Risk Q&A

3
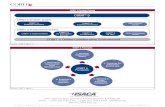
COBIT5® «UNIVERSAL» Framework
Perché
Benefici
Evitare Rischi
Gestione ottimale Risorse
Interventi
Dove operare
• Processi
• Principi – Policies – Frameworks
• Sistemi
• Persone
• Organizzazione
• Informazioni disponibili
• Cultura / etica
Come operare
• Pratiche / Attività Base
•Consolidate e universal- mente accettate
•Riferimento ai principali Standard
•Priorità in funzione obiettivi di business
Quando
Governo
Pianificazione
Organizzazione
Impostazione
Definizione
Soluzioni IT
Erogazione Servizi Supporto
Misura e Controllo
Attori
CDA
Business
IT / IS
Controllo
. . . . . In modo strutturato e connesso. . . . .

4
Frameworks
NIST Cybersecurity Framework The Framework Core is not a checklist of activities to perform; it presents key cybersecurity outcomes that are aligned with activities known to manage cybersecurity risk. These activities are mapped to a subset of commonly used standards and guidelines.
BI : DISPOSIZIONI PRELIMINARI E PRINCIPI GENERALI
1. Premessa
Il sistema dei controlli interni è un elemento fondamentale del complessivo sistema di governo delle banche; esso assicura che l’attività aziendale sia in linea con le strategie e le politiche aziendali ...................
La presente disciplina:
....... rappresenta la cornice generale del sistema dei controlli aziendali
• Chech-box mentatlity
• Tactical & reactive
• Achieve point-in-time Compliance Certification
Compliance Driven Approach
• Proactive & Holistic
• Continous Monitoring
• Proactive mentality
Risk-Based Approach

5
Strumenti Principi Enablers Goals Assessment
Guide Information Security Assurance Enabler Information Risk
Si applica
Si studia
Si adatta
Guida Implementazione
Governance
COBIT5® «UNIVERSAL» Framework
Problem(s) specific Framework based on
COBIT5
• Info Security • Risk • Contesto
Aziendale
• Vendor Mgmt • Privacy EU • .....

6
Principi COBIT 5

7
1 – Meeting Stakeholders needs
1. Capire le esigenze
2. Trasformarle in obiettivi di Business
3. Trasformarli in obiettivi IT
Questa è la nostra area di intervento ed a questo livello dobbiamo individuare e gestire gli obiettivi / rischi IT traducendoli in azioni concrete : in una prospettiva «aziendale»
Stakeholder Drivers (Environment, Technology
Evolution, ...)
Benefits Realisation
Resource Optimisation
Risk Optimisation
Stakeholder Needs
Enabler Goals
IT-related Goals
Enterprise Goals

8
Balanced Scorecard : la «Vision» aziendale «equilibrata» : partire col piede giusto
Financial
• Stakeholder value of business investments
• Portfolio of competitive products and services
• Managed business risks (safeguarding of assets)
• Compliance with external laws and regulations
• Financial transparency
Customer
• Customer‐oriented service culture
• Business service continuity and availability
• Agile responses to a changing business environment
• Information‐based strategic decision making
• Optimisation of service delivery costs
• Optimisation of business process functionality
Internal
• Optimisation of business process costs
• Managed business change programmes
• Operational and staff productivity
• Compliance with internal policies
Learning & Growth
• Skilled and motivated people
• Product and business innovation culture
Stakeholder Drivers (Environment, Technology Evolution,
...)
Benefits Realisation
Resource Optimisation
Risk Optimisation
Stakeholder Needs
Process and Enabler Goals
IT-related Goals
Enterprise Goals
This simple test will give you insights into your strategy, and help you to avoid some of the many pitfalls of poor strategy design, management and implementation.

9
Stakeholder Drivers (Environment, Technology Evolution, ...)
Benefits Realisation
Resource Optimisation
Risk Optimisation
Stakeholder Needs
Enabler Goals
IT-related Goals
Enterprise Goals
Owners and Stakeholders
Accountable Delegate
Governing Body
Monitor Set Direction
Management
Operations and Execution
Instruct and Align Report
Principio 2: Covering the Enterprise End–to–End

10
COBIT 5:
Allineato con gli altri standard e framework oggi disponibili
Coprire tutta l’Azienda
Fornire la base per integrare efficacemente gli altri standard, framework e prassi utilizzate
Integrare tutti i precedent prodotti ISACA
Un’architettura per dare struttura alle regole di governo e produrre un insieme coerente di strumenti pratici
Principle 3: Un’unico Framework Integrato
© 2012 ISACA. All Rights Reserved.

11
Principle 3: Un’unico Framework Integrato

12
12

13
COBIT5® Product Family

14
Pubblicazioni COBIT5 (28/11/2013)
14
Documento Pagg soci (AIEA
MI) non soci
COBIT 5 Framework 94
COBIT 5 Enabling Processes 230 $ 135
COBIT 5 Implementation + tool kit 78 $ 150
COBIT 5 for Information Security 220 $ 35 $ 175
COBIT 5 for Assurance 318 $ 35 $ 175
COBIT 5 for Risk 216 $ 35 $ 175
COBIT Assessment Programme
COBIT Process Assessment Model (PAM): Using COBIT 5 144 $ 40
COBIT Assessor Guide: Using COBIT 5 52 $ 30 $ 80
COBIT Self-Assessment Guide: Using COBIT 5 + tool kit 24 $ 40
COBIT 5: Enabling Information 90 $ 135
COBIT Translations (?)
COBIT 5 Online (4 Q 2013 / 2014)
Vendor Management Using COBIT 5
Configuration Management Using COBIT 5 88 $ 55
Transforming Cybersecurity Using COBIT 5 190 $ 35 $ 60
Securing Mobile Devices Using COBIT 5 for Information Security 138 $ 75
Security Considerations for Cloud Computing 80 $ 75
(Appendix C. Mapping Threats and Mitigating Actions to COBIT 5 for Information Security)
Security-Considerations-Cloud-Computing-Tool-Kit
Advanced Persistent Threats: How To Manage The Risk To Your Business 132 $ 35
Big Data White Paper 18
Totale 2112 $ 170 $ 1.405

15
Chi riconosce COBIT5 ? Regulatory and Legislative Recognition
USA, Canada, India, Giappone,
Brasile, Argentina, Australia,
UAE - Dubai, Colombia, Costa
Rica, Mexico, Paraguay,
Uruguay, Venezuela, Grecia,
Lithuania, Romania
EU riconosce il COBIT come
Framework
Turchia
Sud Africa
Russia ???
PRC ???

16
COBIT 5 definisce un insieme di enablers per la realizzazione di un Sistema integrale di governance e management per l’IT nell’azienda.
COBIT 5 enablers sono: Fattori che , da soli o congiuntamente, influiscono sul
fatto che qual- cosa funzioni
Collegati alla goals cascade
Descritti nel framework COBIT 5 in sette categorie
Principle 4: Consentire un approccio Olistico
© 2012 ISACA. All Rights Reserved.

17
Principio 5 – Separazione tra Governance e Management

18
• Governance garantisce che le esigenze, condizioni ed alternative degli stakeholder siano:
– Valutate per definire gli obiettivi da raggiungere, in modo bilanciato e concordato
– Stabilire la direzione stabilendo indirizzi e priorità
– Monitorare le prestazioni ed i progressi nel rispetto degli obiettivi e delle priorità concordati (EDM)
• Management pianifica, realizza, opera e controlla le attività rivolte al raggiungimento degli obiettivi definiti dalla Governance per raggiungere gli obiettivi aziendali (PBRM)
© 2012 ISACA. All Rights Reserved.
Principio 5 Separazione tra Governance e Management

19
The COBIT 5 Enterprise Enablers

20
Le dimensioni di un qualsiasi Enabler COBIT 5
Ha portato i risultati
attesi ?
Porterà i risultati
attesi ?
Come si gestisce un
enabler ?
Chi ha un ruolo attivo nel
determinare
cosa ci si
attende dall’
enabler

21
Enabler Principi, Policies & Frameworks
Lo scopo di questo enabler è quello di comunicare indirizzi ed istruzioni della Direzione Aziendale.
Sono strumenti per comunicare regole ed istruzioni a supporto degli obiettivi di Governo e dei valori aziendali.
Good practices

22
Enabler Strutture Organizzative
Le “Good Practices” per le strutture organizzative possono venir ragruppate in:
Principi operativi – Assetto pratico di come la struttura opererà,
Span of control – I confini entro i quali si esercita il potere decisionale
Livello di autorità – Le decisioni che la struttura è autorizzata a prendee.
Delega di responsabilità – La struttura può delegare un sottoinsieme di decisioni ad strutture a suo riporto
Procedure di Escalation – Percorsi da seguire in caso di problemi nel prendere decisioni.

23
Enabler : Processi
• COBIT 5 Enablers: Processes
• costituisce il Manuale di riferimento per i 37 Processi COBIT5

24
Life Cycle
Pratiche “generalizzate” (GP) quali
quelle contenute nel COBIT5 Process
Assessment Model (basate sullo
standard ISO/IEC 15504 ) assistono
nella definizione, esecuzione,
monitoraggi ed ottimizzazione di un
processo.
Process Practices: COBIT 5 Enabling
Processes descrive le “internal
Process Practices” in termini di:
pratiche, attività ed attività di dettaglio Come si gestisce il
Processo ?
Porterà i risultati attesi ?

25
COBIT 5 Process Reference Model
25
Processi : Visione olistica
Pianificare ed Organizzare
Realizzare
Erogare
Governare
Gestire

26
Schema di un Processo COBIT5
Pro
cess
o
Descrizione
Purpose
IT Related Goal Related Metrics
Process Goals Related Metrics
Practice
Descrizione
RACI
Input Da
Output a
Attività Dettaglio attività
26

27
Connessione tra Processi COBIT5
27
Pro
cess
o C
Descrizione
Purpose
IT Related Goal Related Metrics
Process Goals Related Metrics
Practice
RACI
Description
Input From
Output To
Activity
Un insieme molto dettagliato (ed esaustivo) di relazioni comprendente, per ogni G/M Practice (210) : Responsabilità (RACI) (25) Work Products ( circa 700) Attività (1112+n) ( + attività di dettaglio ) utilizzabile operativamente
Pro
cess
o B
Descrizione
Purpose
IT Related Goal Related Metrics
Process Goals Related Metrics
Practice
RACI
Description
Input From
Output To
Activity
Pro
cess
o A
Descrizione
Purpose
IT Related Goal Related Metrics
Process Goals Related Metrics
Practice
RACI
Description
Input From
Output To
Activity

28
28
Purpose
IT – Related Goals (primary)
Goals (outcomes)

29
29
Base Practices
RACI
Excel RACI

30
30
Base Practice WP in / out
Activities

31
31

ISO/IEC 15504 (SPICE)
ISACA
Capitolo di Milano

33
ISO/IEC 15504 • SPICE Project 1993 • Esigenza di strumenti di valutazione
forniture per acquisizione di Sistemi (difesa e telecomunicazioni) con alto contenuto di Sw
• 2003 rilascio ISO/IEC 15504 • Focus su :
• Come definire un processo per essere poi in grado di prevederne la capacità (capability vs. maturity) di produrre i risultati attesi (outcomes)
• Come eseguire la misura
33

34
ISO/IEC 15504-2:2003 identifies the measurement framework for process capability and the requirements for:
– performing an assessment; – process reference models; – process assessment models; – verifying conformity of process assessment.
The requirements for process assessment defined in ISO/IEC 15504-2:2003 form a structure which:
– facilitates self-assessment; – provides a basis for use in process improvement and
capability determination; – takes into account the context in which the assessed
process is implemented; – produces a process rating; – addresses the ability of the process to achieve its purpose; – is applicable across all application domains and sizes of
organization; and may provide an objective benchmark between organizations.
The minimum set of requirements defined in ISO/IEC 15504-2:2003 ensures that assessment results are objective, impartial, consistent, repeatable and representative of the assessed processes. Results of conformant process assessments may be compared when the scopes of the assessments are considered to be similar;.
34
ISO/IEC 15504
ASSESSMENT : Objective Impartial Consistent Repeatable Representative Comparable

35
ISO/IEC 15504 – Process Assessment Model (PAM)
35

36
PAM : PRM & MF
36

37

ISACA’s COBIT Assessment Programme

39
What is the new COBIT assessment process?
• The COBIT process programme is described in COBIT® Process Assessment Model (PAM): Using COBIT ® 5.
• PAM brings together two proven ‘heavyweights’ in the IT arena, ISO and ISACA.
• ISACA decided to adopt ISO/IEC 15504-2:2003 Information technology—Process assessment—Part 2: Performing an assessment, that support , among others, both the Committee of Sponsoring Organizations of the Treadway Commission’s Internal Control—Integrated Framework and ITIL Version 3 assessments using the ISO approach.
• The COBIT PAM uses the existing COBIT 5 content : an ISO 15504 compliant process assessment model.
39

40
Assessment Overview
40
Process Assessment Model
Assessment Process

41
The artefacts associated with the execution of a process—defined in terms or process ‘inputs’ and process “outputs”
The high-level measurable objectives of performing the process and the likely outcomes of effective implementation of the process
An observable result of a process—an artefact, a significant change of state or the meeting of specified constraints
The activities that, when consistently performed, contribute to achieving the process purpose

42
Medesimo schema
Pro
cess
o
Descrizione
Purpose
IT Related Goal Related Metrics
Process Goals Related Metrics
Practice
RACI
Description
Input From
Output To
Activity
42
Su
pp
ort
s

43
Process Attributes and Capability Levels
43
This figure is reproduced from ISO 15504-5 2006 with the permission of ISO at www.iso.org. Copyright remains with ISO.
43

44
• It should be noted that WPs for some processes provide higher capability requirements for other processes. This will result in a progressive implementation of processes.
• The initial focus on any process assessment would be the core (sometimes called primary) processes, which are primarily part of the BAI and DSS domains.
• Processes in the APO and MEA domains will be required to support improvement in the capability of these core processes past level 1.
• An example is APO01 Manage the IT management framework, which is required as part of establishing the IT process framework, to document roles and responsibilities required by processes at capability level 2.
Livelli 2-5
44

45
Performance e Capability

46
Setting Target (Cost vs. Benefit)
RISK €
EFFECTIVENESS OF PROTECTION
COST
TARGET
Soldi buttati
Possible
Deviation
from
Business
Objectives
Il punto «ottimale» dipende anche dalla tipologia e dimensione dell’Azienda e quindi posso usare la misura della capability per ottimizzare il ROI

47
Assessment Process
Activities
47
1. Initiation
2. Planning the assessment
3. Briefing
4. Data collection
5. Data validation
6. Process attributes rating
7. Reporting the results
47

COBIT 4.1 ?

49
Where Have All the Control Objectives Gone?
49

50
Erik Guldentops Isaca Journal 4
2011
• COBIT 4.1 Control Objectives – Molto utili
– Manca una chiara distinzione tra obiettivo ed azione
• COBIT 5 (e CobiT 4.1 PAM-med) – Non ci sono più: sostituiti da G&M
Practices e Outcomes
• CobiT 4.1 – Poco sviluppato il concetto di
“sequenza di attività”
• COBIT 5 (e CobiT 4.1 PAM-med) – WP in -> G&M Practices -> WP out
50

51
Vediamo il tutto graficamente
Processo Descrizione
Maturity Model
Control Objectives + PC1÷6
Activities (RACI)
Outputs to
Inputs from
Control Practices
Practices (RACI)
Outcomes (Goals)
PAM
WP out to
WP In from
CobiT 4.1 CobiT 4.1
PAM-med COBIT 5.0
Activities IT-related Goal

52
CobiT 4.1, ValIT, RiskIT
Mapping
Cobit 4.1
Application Controls 6 (mapped)
Control Objectives 210 (207 mapped, 3 deleted)
ValIT Key Management Practice
43 (mapped)
RiskIT Key Management Practice
43 (mapped)
COBIT 5
G/M Practices 210 (177 da CobiT 4.1, 33 new)
52
V. Allegato

53
CobiT 4.1 Control Objective -> COBIT 5 BP + I/O + Activity
53
CobiT 4.1 Control Objective
AI1.4 Requirements and Feasibility Decision and Approval
Verify that the process requires the business sponsor to approve and sign off on business functional and technical requirements and feasibility study reports at predetermined key stages.
The business sponsor should make the final decision with respect to the choice of solution and acquisition approach.
COBIT 5

54
CobiT 4.1 Control Objective -> COBIT 5 BP + I/O + Activity
CobiT 4.1 Control Objective
DS4.6 IT Continuity Plan Training
Provide all concerned parties with regular training sessions regarding the procedures and their roles and responsibilities in case of an incident or disaster.
Verify and enhance training according to the results of the contingency tests.
COBIT 5
54

55
Enabler Cultura, Etica e Comportamenti
Le “Good practices” per creare, favorire e mantenere i comportamenti desiderati sono:
Comunicazione dei comportamenti desiderati e dei valori dell’Azienda ( Codici etici)
Consapevolezza di quali siano i comportamenti desiderati
Incentivi
Regole, norme e sanzioni

56
Enabler Information
... quando le Informazioni costituiscono il fattore (abilitante) principale
... ad esempio

57
Addressing Information Governance and Management Issues Using COBIT 5

58
Information Governance/ Management Issue:
Marketing Situational Awareness
(Big Data Dimension 1: Variety of Information)
4.3.1 Issue Description and Business Context • An enterprise marketing team wishes to
increase its awareness of and capacity to respond to public perceptions of its company’s offerings.
• Data sources include social media postings, such as micro and traditional blogs, social sites, and audio conversations between customers and service representatives.
• The enterprise wishes to correlate the sentiment detected in both online and call centre channels with sales trends in various segments and regions around the world.
• Speech-to-text conversion, web indexing and natural language text processing are required. In big data terms, this is a variety issue.
... COBIT5 : non più solo IT – Function !
Marketing Function Goal Risk ....
....

59
Una nuova dimensione per COBIT5
Stakeholder Drivers (Environment, Technology Evolution, ...)
Benefits Realisation
Resource Optimisation
Risk Optimisation
Stakeholder Needs
IT-Function Goals
Enterprise Goals
Enablers for IT Function Enablers for Marketing and Sales
Marketing and Sales Function Goals

60
Enabler 6 Servizi, Infrastrutture ed Applicazioni
“Good Practices” per l’enabler.
Architettura : principi e regole generali che
guidino l’implementazione e l’utilizzo di risorse
IT. Ad esempio :
Riutilizzo – Componenti comuni da riutilizzare.
Buy vs. build – Regole di decisione (ad es. Le
soluzioni vanno acquistate a meno esista un
preciso razionale per lo sviluppo ionterno, ecc.)
Semplicità – L’architettura va progettata e
mantenuta garantendo la massima semplicità,
compatibilmante con gli obiettivi.
Flessibilità (Agility) – Rispondere a mutate
esigenze in modo efficace ed efficente.
Openness - Utilizzare il più possibile soluzioni
basate su Open Industry Standards.

61
Enabler 7 Persone, Capacità e Competenze
“Good practices” in particolare per :
Descrivere vari livelli di competenza per i var ruoli.
Definire la capacità per ogni ruolo
Mappare le categorie di skill categories per domini dei processi COBIT 5 (APO; BAI etc.) v. prossima slide
In particolare in corrispondenza della attività legate all’IT, e.s. business analysis, information management etc.
Usare fonti esterne per defire le “good practices= come : The Skills Framework for the information age
(SFIA)

62
COBIT 5 Implementation Need for new or improved IT governance organization is usually recognized by pain points and/or trigger events

63
COBIT 5®
Due esempi di utilizzo

64
Esempio 1 Proposta Nuovo Regolamento Europeo Protezione Dati Personali
SECTION 3
RECTIFICATION AND ERASURE
Article 16
Right to rectification
The data subject shall have the right to obtain from the controller the
rectification of personal data relating to them which are inaccurate. The
data subject shall have the right to obtain completion of incomplete
personal data, including by way of supplementing a corrective statement.
È una: «Service request» che richiede una «Service capability», come ?
Area : Management - Domain : Deliver, Service and Support
DSS02 - Manage Service Requests and Incidents
Process Description Provide timely and effective response to user requests and resolution of all types of incidents. Restore normal service; record and fulfill user requests; and record, investigate, diagnose, escalate and resolve incidents.
Valore aggiunto COBIT5 ……
Perché
Benefici
Evitare Rischi
Gestione ottimale Risorse
Interventi
Dove operare
• Processi
• Principi – Policies – Frameworks
• Sistemi
• Persone
• Organizzazione
• Informazioni disponibili
• Cultura / etica
Come operare
• Pratiche / Attività Base
•Consolidate e universal- mente accettate
•Riferimento ai principali Standard
•Priorità in funzione obiettivi di business
Quando
Governo
Pianificazione
Organizzazione
Impostazione
Definizione
Soluzioni IT
Erogazione Servizi Supporto
Misura e Controllo
Attori
CDA
Business
IT / IS
Controllo

65
DSS02 - Management Practices Description
DSS02.01 - Define incident and service request classification schemes.
Define incident and service request classification schemes and models.
DSS02.02 - Record, classify and prioritise requests and incidents.
Identify, record and classify service requests and incidents, and assign a priority according to business criticality and service agreements.
DSS02.03 - Verify, approve and fulfil service requests.
Select the appropriate request procedures and verify that the service requests fulfil defined request criteria. Obtain approval, if required, and fulfil the requests.
DSS02.04 - Investigate, diagnose and allocate incidents.
Identify and record incident symptoms, determine possible causes, and allocate for resolution.
DSS02.05 - Resolve and recover from incidents.
Document, apply and test the identified solutions or workarounds and perform recovery actions to restore the IT-related service.
DSS02.06 - Close service requests and incidents.
Verify satisfactory incident resolution and/or request fulfilment, and close.
DSS02.07 - Track status and produce reports.
Regularly track, analyse and report incident and request fulfilment trends to provide information for continual improvement.
+ RA
CI

66
.... activities
DSS02.01 - Define service request classification schemes (Output)
To Description
Internal • Incident and service request classification schemes and models
Internal • Rules for incident escalation
DSS02.01 - Activities
1. Define incident and service request classification and prioritisation schemes and criteria for problem registration, to ensure consistent approaches for handling, informing users about and conducting trend analysis.
2. Define incident models for known errors to enable efficient and effective resolution.
3. Define service request models according to service request type to enable self-help and efficient service for standard requests.
4. Define incident escalation rules and procedures, especially for major incidents and security incidents.
5. Define incident and request knowledge sources and their use.
1. Define and communicate the nature and characteristics of potential security-related incidents so they can be easily recognised and their impact understood to enable a commensurate response.

67
Solo per un articolo ?
• Ci sono molte «istanze» per le quali è richiesta la capacità di erogare un servizio o gestire un incidente (DSS02)
Service Capabilities / Requests Art EU Cancellazione automatica dati scaduti ( Art. 17) Article 17 - Right to be forgotten and to erasure - 7
Cancellazione dati su richiesta Article 17 - Right to be forgotten and to erasure
Communicate rect / erasure Artt 16 and 17 Article 13 - Rights in relation to recipients
Comunicazione relativa applicazione o meno Art 13, 15, 19
Article 12 - Procedures and mechanisms for exercising the rights of the data subject - 2
Article 12 - Procedures and mechanisms for exercising the rights of the data subject - 3
Confirmation Data are (are not) processed Article 15 - Right of access for the data subject
Consent withdraw Article 7 - Conditions for consent - 3
Data Breach notification to Data Subject Article 32 - Communication of a personal data breach to the data subject
Data breach notification to Supervisory Authority Article 31 - Notification of a personal data breach to the supervisory authority
Inform third parties that Personal Data are to be erased Article 17 - Right to be forgotten and to erasure
Privacy Awareness Article 37 - Tasks of the data protection officer - 1 - (b)
Restrict processing instead of erasure Article 17 - Right to be forgotten and to erasure - 4
Rettifica dati Article 16 - Right to rectification
Richiesta via informatica informazioni da parte interessato (Art 12)
Article 12 - Procedures and mechanisms for exercising the rights of the data subject - 1
Trasmit Copy of Data undergoing processing Article 18 - Right to data portability
…………………. …………….

68
Per le Aziende di qualsiasi dimensione ?
Dimensione
Piccola Si domanda al «Commecialista»
Media COBIT5 – DSS02
Grande COBIT5 – DSS02 +
+ ISO 15504 Capability Assessment

69

70
Uno schema: life cycle !
Setup
•Requisiti
•Call for tender
•Valutazione
•Shortlist
•Negoziazione
Contratto
•Accordo
•Deliverables
•Livelli di Servizio
•Metriche
•Costi
•Legale
Operations
•Avviamento
•Gestione operazioni
•Monitoring
Transition-out
•Phase out operativo
•Trasferimento delle conoscenze e della gestione operativa al nuovo fornitore
modifiche
Lo schema è utilizzabile per : Assegnare responsabilità Identificare minacce e valutare impatti associandole a relative azioni correttive Mappare il Processo sulla realtà aziendale Identificare Strumenti / Documenti di supporto (Enabler Information !)
Cambio contratto Cambio Fornitore

71
Assegnare le responsabilità

72
Recent research reveals that approximately one out of five enterprises (19 percent) does not invest sufficient effort to manage vendors and vendor-provided services effectively.
Minaccia Rischio conseguente Impatto
T1 Vendor selection Financial, operational, reputational and legal/compliance
?
T2 Contract development Financial, operational and legal/compliance ?
T3 Requirements Financial, operational, reputational and legal/compliance
?
T4 Governance Financial, operational and legal/compliance ?
T5 Strategy Financial, operational and legal/compliance ?
Identificare minacce e pesare i rischi conseguenti

73
Per ogni minaccia
Una o più azioni correttive
Una indicazione agli enablers (1) coinvolti
1 - Enablers:
1. Principles, policies and frameworks
2. Processes
3. Organizational structures
4. Culture, ethics and behaviour
5. Information
6. Services, infrastructure and applications
7. People, skills and competencies

74
Identificare minacce e valutare impatti associandole a relative azioni correttive
Azione correttiva Minaccia T1
T2
T3
T4
T5
1 Diversify sourcing strategy to avoid overreliance or vendor lockin x
2 Establish policies and procedures for vendor management x
3 Establish a vendor management governance model x
4 Set up a vendor management organization within the enterprise x
5 Foresee requirements regarding the skills and competencies of the vendor employees x
6 Use standard documents and templates x
7 Formulate clear requirements x
8 Perform adequate vendor selection x
9 Cover all relevant life-cycle events during contract drafting x
10 Determine the adequate security and controls needed during the relationship x x
11 Set up SLAs x
12 Set up operating level agreements (OLAs) and underpinning contracts x
13 Set up appropriate vendor performance/service level monitoring and reporting x x
14 Establish a penalties and reward model with the vendor x
15 Conduct adequate vendor relationship management during the life cycle x
16 Review contracts and SLAs on a periodic basis x
17 Conduct vendor risk management x
18 Perform an evaluation of compliance with enterprise policies x
19 Perform an evaluation of vendor internal controls x
20 Plan and manage the end of the relationship x x
21 Use a vendor management system x x x x
22 Create data and hardware disposal stipulations x x

excel

76
COBIT5 «Vendor Management Framework»

Risk- Based approach ? Cosa manca ?
Olistico !!!

E gli altri enablers ?
21
3
11
4
5
1
4
Process Principles, Policiesand Frameworks
Information Services,Infrastructure and
Applications
OrganisationalStructures
Ethics, Culture andBehaviour
People, Skills andCompetencies

79
Enabler Information
Call for Tender
Vendor Contract
Service Level Agreements
SLAs Defined
How to Create Successful SLAs
SLA Common Pitfalls
Benefits of Effective Service Level Management
OLAs and Underpinning Contracts
Managing a Cloud Service Provider
Excerpt From Security Considerations for Cloud Computing
Appendix A. Vendor Selection Dashboard
Criteri (pesati) di selezione
Appendix B. Call for Tender Template
Appendix C. Call for Tender Checklist
Appendix D. Drafting the Contract: High-level Legal Checklist for Non-legal Stakeholders
Appendix E. Example Contract Template
Appendix F. SLA Template
Appendix G. Service Level Agreement (SLA) Checklist
Appendix H. Example SLA Template
Appendix I. Example Generic SLA
Appendix J. Example SLA Slim Version
Appendix K. Example SLA for Back Office and Local Area Network (LAN) Services
Appendix L. High-level Mapping of COBIT 5 and ITIL V3 for Vendor Management

COBIT® 5 for Assurance

Scope of the Assurance Publication In this publication, two perspectives on assurance are identified:
Assurance function perspective Describes what is needed in an enterprise to build and provide assurance function(s). COBIT 5 is an end-to-end framework, meaning that it considers the provisioning and use of assurance as part of the overall governance and management of enterprise IT.
Assessment perspective Describes the subject matter over which assurance needs to be provided. In this case, the subject matter is enterprise IT, which is described in ample detail in the COBIT 5 framework and COBIT® 5: Enabling Processes and is therefore not covered in detail in the assurance guide itself.

Two Perspectives on Assurance Provided by COBIT 5
Both perspectives are built on the seven common governance and management enablers of the COBIT 5 framework.

83
Assurance Framework

84
Indice di Assurance
• Esempi di Assurance con COBIT5
1. Change management 2. Risk management 3. Bring your own device
(BYOD)
• Assurance utilizzando tutti gli Enablers

20/12/2013 85
Risk Framework

86
COBIT5 for Information
Security
86
Giugno 2012 – 220 pagg

87

1. Principles, Policies and Frameworks
1. Model
2. Information Security Principles
3. Information Security Policies
4. Adapting Policies to the Enterprise’s Environment
5. Policy Life Cycle
2. Processes
1. Process Model
2. Governance and Management Processes
3. Information Security Governance and Management Processes
4. Linking Processes to Other Enablers
3. Organisational Structures
1. Model
2. Information Security Roles and Structures
3. Accountability Over Information Security
COBIT5 for Info Security : Struttura
88
4. Culture, Ethics and Behaviour
1. Model
2. Culture Life Cycle
3. Leadership and Champions
4. Desirable Behaviour
5. Information
1. Model
2. Information Types
3. Information Stakeholders
4. Information Life Cycle
6. Services, Infrastructure and Applications
1. Model
2. Information Security Services, Infrastructure and Applications
7. People, Skills and Competencies
1. Model
2. Information Security-related Skills and Competencies
Appendici
Detailed Guidance Detailed Guidance
Imp
lem
enti
ng
Info
Sec
Init
iati
ves
Detailed Mapping

89
Gruppi di Ricerca
Risk Management
COBIT5 Framework per :
BI - Nuove disposizioni di vigilanza prudenziale per le banche
Nuovo regolamento EU Protezione dei Dati Personali
Sistema di Controlli Interni a presidio del Rischio Riciclaggio
Outsourcing

QUESTIONS &
COMMENTS
© 2013 ISACA. All rights reserved