Cisco Firewall Basics -...
Transcript of Cisco Firewall Basics -...


Cisco Firewall Basics
BRKSEC – 1020
Michael Overstreet
Security Consulting Systems Engineer

Introduction

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Michael Overstreet
• Security Consulting Systems Engineer for Federal
• 16 years Cisco Security
– SPAs, ASA courseware development, Security & Wireless Certification Testing
• 20 years in Security
• Pursuing my CCIE Security (0 for 2 with the v4 Lab)
• South Carolinian residing in Texas
• Passionate about brewing and drinking beer
– Scotches and Bourbons fall under the drinking passion, too
4

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Session Information
• This is an introductory session
– It is not meant those for professionals with deep knowledge of firewalls and Cisco ASA
• If you want
– Deep knowledge of the ASA and details about advanced configuration examples
– This session is not for you
• Note: Session will NOT cover IPv6, IPS, VPN, FWSM or Pricing
• Basic FW Understanding with Simplistic ASA Configuration
5

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Agenda
• Introduction
• Firewalls in General
• ASA Product Family
• CLINet Overview
• ASA Firewall Basics
• Other Cisco Firewalls
• Q&A
6

Firewalls in General

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Securing/Hardening for What Purpose or Need?
Subversion Bots, Viruses, and Worms
Spyware and Adware
Disruption Denial of service attacks
Advanced Persistent Threats (APTs)
Penetration Attempt
Zero-day Attacks
Hacker Attacks
Data Loss Data theft and/or interception
Identity theft
8

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Next Generation Security
BEFORE Control
Enforce
Harden
DURING AFTER Detect
Block
Defend
Scope
Contain
Remediate
Attack Continuum
Visibility and Context
Firewall
NGFW
NAC + Identity Services
VPN
UTM
NGIPS
Web Security
Email Security
Advanced Malware Protection
Network Behavior Analysis
9

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Network Security Components
• Multiple network components are needed by security administrators to combat these threats in an effort to secure the network
– Firewalls with stateful packet inspection and micro application filtering (NGFW)
– Virtual Private Networks (VPNs) for secure communication over an untrusted network
– Intrusion prevention systems (NGIPS) to identity threats and attacks
– Anti-virus and anti-spyware to combat viruses, worms, and other malware
• Firewalls are the core component for defense from the threats to network security
• The firewall often is the conduit from which other defense components combat the threats that face the network
10

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Firewalls
• Stateful packet and application inspection and filtering appliances that working at both the network and application layers
• Provide a platform for the features/functionality needed for network security
– VPNs (remote-access and site to site)
– Anti-malware
– IPS
• Next-generation security should not abandoned proven stateful inspection capabilities in favor of application and user ID awareness by itself
• Comprehensive network security solution needs includes firewalls, next-generation firewalls (application inspection and filtering), next generation intrusion prevention systems (context aware)
What are they?
Add graphics
11

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Firewall Features
• Filtering – Security policy enforcement for network connections inbound and outbound
• Stateful Inspection – Tracking allowed outbound or inbound network connections
• Network Address Translation – Translation of IPs from one network to another
• Application visibility and control – Ability to determine what application is with the packet
• Features and Services Flexibility – Adding functionality to meet security needs
Common Features
ISP Internal
Packet Packet Packet Packet Packet Packet
Packet Packet Packet
Packet Packet Packet
Packet Packet Packet
12

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Filtering
• The genesis of firewalls was initially a means to filter traffic based on the five tuple
– Source IP address – the IP address of the initiator of the IP packet
– Destination IP Address – the IP address of the destination of the IP packet
– Source Port – UDP or TCP port used by initiator to establish communications with destination
– Destination Port – UDP or TCP port used by destination to establish communications with source
– IP Protocol – the specific IP protocol used in the communication • UDP/53 – Domain Name Service (DNS)
• TCP/25 – Simple Mail Transfer Protocol (SMTP)
• TCP/21 – File Transfer Protocol (FTP)
ISP Internal
DMZ Network
(Public Web/DB)
Packet Packet Packet
Src IP – 5.5.5.5
13

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Stateful inspection of traffic
• Most routers and switches can filter based on the five tuple…why a firewall then?
• Stateful firewalls track L3/L4 traffic as it leaves and returns to the network
– Connections are maintained in the connection table tracking five tuple and additional information such as sequence
More than just a filter
ISP Internal
Packet Packet Packet
Src IP – 1.1.1.1
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
Packet Packet Packet
Src IP – 2.2.2.2
Dest IP – 1.1.1.1
Src Port – TCP/80
Dest Port – TCP/35478
Connection Table
TCP outside:2.2.2.2/80 (2.2.2.2/80) inside:1.1.1.1/35478 (1.1.1.1/35478), flags UfIOB, idle 4m39s, uptime 6m16s, timeout 1h0m, bytes 3002
14

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Network Address Translation
• Network address translation (NAT) is the mapping of IP addresses from a private network to a public network
• NAT gives network administrators and security administrators:
– Access to non-publically routable IPv4 space
– Cost savings because addresses are not cheap
– Allows for masquerading of internal network addresses
– IPv4 Address space is exhausted
ISP Internal
Packet Packet Packet
Src IP – 1.1.1.1
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
Packet Packet Packet
Src IP – 10.10.10.10
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80 15

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Next Generation Security
• The ability to security the network has grown beyond stateful packet inspection and filtering based on the five tuple
• Next generation security is a paradigm shift focusing on network security holistically
• Application visibility and control along with context information from network traffic allows security administrators to applying granular controls to traffic flows on the network
• The firewall is the platform to apply next generation security to the network
= Plus Equals
16

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Feature and Service Flexibility
• Threats and our counter-measures to these threats are changing quickly
• The firewall must have the feature richness and service flexibility to allow security administrator to evolve network defense to polymorphic threats faced today
• Stateful firewall inspection coupled next-generation features and services increases security administrators arsenal to defend against today’s and tomorrow’s threats
• Today…Tomorrow…Next Month…Next Year…
17

The ASA Product Family

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Cisco ASA is Available on a Broad Range of Platforms to Meet Different Needs
Edge and Campus
ASA 5505
SOHO and Branch
ASA 5512-X
ASA 5515-X
ASA 5525-X
ASA 5545-X
Data Center and Virtual
ASA 5555-X
ASA 5585-X SSP 10 / 20 / 40 / 60
ASAv*
*Shipping in Q2 CY2014
ASASM
19

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
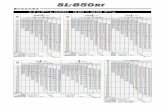
Key Attributes: SOHO and Branch
Metric 5505 5512-X 5515-X Max. FW throughput 150 Mbps 1 Gbps 1.2 Gbps
Max. IPS throughput 75 Mbps 250 Mbps 400 Mbps
Max. NGFW throughput NA 200 Mbps 350 Mbps
Max. VPN throughput 100 Mbps 200 Mbps 250 Mbps
Max. VPN Peers 25* 250*
I/O 8 Fast Ethernet
Switch
Integrated: 6 GE Copper
Extended: 8 GE Copper or SFP
Clustering Not Supported Yes. Requires
Security Plus License Yes
*Site-to-Site VPN is Free. AnyConnect VPN is a Licensed Feature
20

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Key Attributes: Edge and Campus
Metric 5525-X 5545-X 5555-X Max. FW throughput 2 Gbps 3 Gbps 4 Gbps
Max. IPS throughput 600 Mbps 900 Mbps 1.3 Gbps
Max. NGFW throughput 650 Mbps 1 Gbps 1.4 Gbps
Max. VPN throughput 300 Mbps 400 Mbps 700 Mbps
Max. VPN Peers 750* 2500* 5000*
Power Supply Single Dual
I/O Integrated: 8 GE Copper / Extended: 6GE Copper or SFP
Clustering Enabled by default in the base license
*Site-to-Site VPN is Free. AnyConnect VPN is a Licensed Feature
21

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
5585-X
Key Attributes: Data Center
Metric SSP 10 SSP 20 SSP 30 SSP 40 ASASM Max. FW
throughput 4 Gbps 10 Gbps 20 Gbps 40 Gbps 20 Gbps
Max. IPS
throughput 2 Gbps 3 Gbps 5 Gbps 10 Gbps NA
Max. NGFW
throughput 2 Gbps 5 Gbps 9 Gbps 13 Gbps NA
Max. VPN
throughput 1 Gbps 2 Gbps 3 Gbps 5 Gbps 2 Gbps
Integrated I/O 8-port 10/100/1000 and
2-port 10 GE (SFP+)
6-port 10/100/1000 and
4-port 10 GE (SFP+) NA
Extended I/O 4-port or 8-port 10 GE(SFP/SFP+) or
20-port 1 GE (12-port 1 GE SFP and 8-port 10/100/1000) NA
Clustering Enabled by default in the base license NA
22

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Cisco ASA Allows You to Pay-As-You-Grow with ASA Clustering
• 2 unit clustering available on all 5500-X
platforms
• Up to 16* units in 5585-X cluster
• Max. firewall throughput:
640Gbps
• Max. IPS inspection capacity:
160Gbps
• Average IPS inspection capacity:
80Gbps
* Q2 CY2014
23

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
ASAv
Key Attributes: Virtual
Metric ASAv10 ASAv30
Max. FW throughput 1 Gbps 2 Gbps
IPS Stateful FW Only
NGFW Stateful FW Only
Max. VPN Peers 250 750
VLANs 50 250
Max. Concurrent Sessions 100k 500k
Note:
• Performance numbers are indicative and not final until the product is generally available
• Clustering and multi-context are NOT supported in ASAv
24

Case Study Network – CLINet.com

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
CLINet.com
• CLINet is a fictional company created for these use cases in ASA Firewall deployment
– CLINet has embarked on a network/security deployment project entitled
“The Security 10/20 Project” which you will now be a part of
• Company requirements and configuration examples are based upon real-life customer conversations and deployments
– Only designs we have fully certified
– Cisco Validated Design (CVD) approved configuration(s) • i.e. VMDC (Data Center CVD) www.cisco.com/go/vmdc
• Cisco LIVE Information Networking Company
26

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
CLINet Security Priorities for SEC-1020 Project
CLINet network & security team has five requirements for the initial deployment:
1. Initial Deployment
2. Configure Interfaces for inside, outside and DMZ networks
3. NAT DMZ host to external address
4. Apply the initial ACL to the outside interface
5. Monitor connection table
Initialize Interface
Setup
Connection Table
NAT for DMZ ACL for
outside Interface
27

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
CLINet Network Diagram
Deploy Redundant ASA(s) in
Routed Mode for Edge/DMZ
Note: DC security architecture not depicted in this layout, nor will it be discussed
Edge Agg
VDC
Edge
Aggregation
ISP-A ISP-B
DMZ Network
(Public Web/DB)
Internal
Network
28

ASA Firewall Initial Setup

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
ASA Management
• The ASA has a command line interface (CLI) with similar syntax and other conventions to the Cisco IOS CLI, but the adaptive security appliance operating system is not a version of Cisco IOS software
• Do not assume that a Cisco IOS CLI command works with or has the same function on the adaptive security appliance
• The adaptive security device manage (ASDM) is a Java based web user interface that can be used to configure the ASA
• Because ASDM is Java based it allows any operating system that supports Java to be used to configure the ASA
On the Box
30

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
ASA CLI
CLINet-ASA(config)# show interface ip brief
Interface IP-Address OK? Method Status Protocol
GigabitEthernet0/0 10.10.11.2 YES CONFIG up up
GigabitEthernet0/1 172.16.60.1 YES CONFIG up up
GigabitEthernet0/2 unassigned YES unset administratively down down
GigabitEthernet0/3 unassigned YES unset administratively down down
GigabitEthernet0/4 unassigned YES unset administratively down down
GigabitEthernet0/5 unassigned YES unset administratively down down
Internal-Control0/0 127.0.1.1 YES unset up up
Internal-Data0/0 unassigned YES unset up up
Internal-Data0/1 unassigned YES unset up up
Internal-Data0/2 unassigned YES unset up up
Management0/0 192.168.20.236 YES CONFIG up up CLINet-
ASA(config)#
31

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
ASDM
32

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
CLINet Network Diagram
Deploy Redundant ASA(s) in
Routed Mode for Edge/DMZ
Note: DC security architecture not depicted in this layout, nor will it be discussed
Edge Agg
VDC
Edge
Aggregation
ISP-A ISP-B
DMZ Network
(Public Web/DB)
Internal
Network
33

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
CLINet-ASA
– Initial Deployment CLI view
ASDM
– Basic Interface Setup Two legged
Three legged firewall
– NAT Simple NAT for DMZ host
– Filtering via ACLs
Interface ACLs
– Stateful Connection State Table via CLI
ASDM Connection Table
CLINet ASA
Edge
Aggregation
ISP-A ISP-B
DMZ Network
(Public Web/DB)
Internal
Network
34

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Initial ASA Setup
• ASA Bootstrapping – 2 options
– Option 1: (If new) May connect directly to Management interface using a PC (DHCP) and execute: https://192.168.1.1/admin • No username / password needed
• ASDM GUI will be used to run Startup Wizard
• Once complete the ASA configuration guide can be used for further configuration: • http://www.cisco.com/en/US/products/ps6120/products_installation_and_configuration_guides_list.html
– Load desired version of ASA 9x code – may be done via USB (64-bit appliances)
– To use GUI – Make the latest ASDM image available in flash (disk0:/disk1:/,etc)
Valid for Appliance or Module
35

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Initial FW Setup
• ASA Bootstrapping – 2 options
– Option 2: Connect PC to the management interface on ASA, then connect with console cable and execute in terminal
– From a PC configured on the 192.168.1.0/24 subnet, you can launch ASDM and run startup wizard
• Valid for Appliance or Module
ciscoasa# config t
(config)#hostname EDGE-FW
EGDE-FW(config)# int m0/0
(config-if)#nameif management
(config-if)#sec 100
(config-if)#ip address 192.168.1.1 255.255.255.0
(config-if)#no shut
(config-if)#http server enable
(config)#http 0 0 management
(config)#domain-name CLINet.com
(config)#asdm image disk0:/nameofASDMimage.bin
(config)#username admin password cisco priv 15
(config)#crypto key gen rsa gen mod 1024 (use if SSL shows certificate error)
36

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Interface Security Levels
• A security level is a number between 0 and 100 that determines how firewall rules are processed for the data plane
• Security levels are tied to an interface: the inside or private side interface is always 100 (most trusted) and the outside or public interface is always 0 (least trusted)
• All conversations are based only on two interfaces at a time – one will be considered inside, one outside, based on Sec-level that is set
• Traffic on the ASA is allowed by default from a higher security level interface to a lower security level interface
• An ACL must explicitly permit traffic from a lower security level interface to a higher (e.g. outside to inside)
The foundation for passing traffic through an ASA
Inside Network
DMZ Network
Outside Network
G0/0
G0/1
G0/2
ACL Req.
0
100
No ACL Req.
50
37

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Interface Configuration via CLI • Simple Interface Setup
interface GigabitEthernet0/0
nameif outside
security-level 0
ip address 10.10.11.2 255.255.255.0
interface GigabitEthernet0/1
nameif inside
security-level 100
ip address 172.16.60.1 255.255.255.0
interface GigabitEthernet0/2
nameif DMZ
security-level 50
ip address 1.1.1.254 255.255.255.0
interface Management0/0
management-only
nameif management
security-level 100
ip address 192.168.1.1 255.255.255.0
ISP
Internal
Physical Int – g0/0
Name – outside
IP – 10.10.11.2/24
Security-level 0
Physical Int – g0/1
Name – inside
IP – 172.16.60.1/24
Security-level 100
Physical Int – g0/2
Name – DMZ
IP – 1.1.1.254/24
Security-level 50
38

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Interface Configuration via ASDM Configuration > Device Setup > Interfaces > Add > Interface…
39

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
NAT Implementation
– Static NAT – A consistent mapping between a real and mapped IP address. Allows bidirectional traffic initiation
– Dynamic NAT – A group of real IP addresses are mapped to a (usually smaller) group of mapped IP addresses, on a first come, first served basis. Only the real host can initiate traffic. The mapped group could be a single IP address or port address translation (PAT)
– Dynamic Port Address Translation (PAT)—A group of real IP addresses are mapped to a single IP address using a unique source port of that IP address.
– Identity NAT—A real address is statically translated to itself, essentially bypassing NAT. You might want to configure identity NAT to exempt a subset of address from translate a large group of addresses
• The ASA supports four NAT methods:
ISP Internal
Packet Packet Packet
Src IP – 1.1.1.1
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
Packet Packet Packet
Src IP – 10.10.10.10
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
40

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
NAT on the ASA
• The ASA Single translation table
• Access Lists reference the internal (real) IP address and not the global
• Automatic NAT (Auto NAT or Object-based)
– Single rule per object
– Useful for less complex scenarios
ISP DMZ
Packet Packet Packet
Src IP – 1.1.1.1
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
Packet Packet Packet
Src IP – 10.10.10.10
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
41

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
NAT Configuration via CLI CLINet Object Based NAT
ISP DMZ
Packet Packet Packet
Src IP – 1.1.1.1
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
Packet Packet Packet
Src IP – 10.10.10.10
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
CLINet-ASA(config)# object network CLINet-Web-Server
CLINet-ASA(config-network-object)# host 1.1.1.1
CLINet-ASA(config-network-object)# nat (inside,outside) static 10.10.10.10
CLINet-ASA(config-network-object)# exit
CLINet-ASA(config)# sh xlate
1 in use, 1 most used
Flags: D - DNS, e - extended, I - identity, i - dynamic, r - portmap,
s - static, T - twice, N - net-to-net
NAT from inside:1.1.1.1 to outside:10.10.10.10
flags s idle 0:01:03 timeout 0:00:00
CLINet-ASA(config)#
42

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
NAT Configuration via ASDM
Configuration > Firewall > NAT Rules > Add “Network Object” NAT Rule
ISP Internal
Packet Packet Packet
Src IP – 1.1.1.1
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80
Packet Packet Packet
Src IP – 10.10.10.10
Dest IP – 2.2.2.2
Src Port – TCP/35478
Dest Port – TCP/80 43

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Filtering Configuration
• The ASA provides basic traffic filtering capabilities with access control lists to control access in the network by preventing certain traffic from entering or exiting.
• ACLs are made up of one or more access control entries (ACEs)
– An ACE is a single entry in an ACL that specifies a permit or deny rule (to forward or drop the packet) and is applied to the specific five tuple
• ACLs are used in a variety of features such as named or numbered, objects, logging, activation
Access Control Lists (ACL)
ISP Internal
DMZ Network
(Public Web/DB)
Packet Packet Packet
Src IP – 5.5.5.5
44

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Supported ACLs
• Standard ACLs – Identify the destination IP addresses of traffic
– Standard ACLs cannot be applied to interfaces to control traffic
• Extended ACLs – Use one or more access control entries (ACE) in which you can specify the line number to insert the ACE, the source and destination addresses, and, depending upon the ACE type, the protocol, the ports (for TCP or UDP), or the IPCMP type (for ICMP)
• EtherType ACLs – Used to filter traffic at layer when the ASA is in transparent firewall mode
• Webtype ACLs – Used in a configuration that supports filtering for clientless SSL VPN connections
The ASA supports four different types of ACLs
45

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
ACL Configuration via CLI CLINet ACL
CLINet-ASA(config)#
CLINet-ASA(config)# access-list OUTSIDE->DMZ extended deny tcp host 5.5.5.5 host 1.1.1.1 eq www
CLINet-ASA(config)# access-list OUTSIDE->DMZ extended deny tcp host 5.5.5.5 host 1.1.1.1 eq https
CLINet-ASA(config)# access-list OUTSIDE->DMZ extended permit tcp any host 1.1.1.1 eq www
CLINet-ASA(config)# access-list OUTSIDE->DMZ extended permit tcp any host 1.1.1.1 eq https
CLINet-ASA(config)#
CLINet-ASA(config)# access-group OUTSIDE->DMZ in interface outside
CLINet-ASA(config)#
ISP Internal
DMZ Network
(Public Web/DB)
Packet Packet Packet
Src IP – 5.5.5.5
46

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
ACL Configuration via ASDM Configuration > Firewall > Access Rules > Add Access Rule…
47

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Connection Table via CLI
• The show conn command displays the number of, and information about, active TCP connection that are flowing through the ASA
• There are numerous flags and options for the show conn command which allows security administrators to view specific outgoing or incoming TCP traffic
• For more on the various options refer to this URL: – http://www.cisco.com/c/en/us/td/docs/security/asa/asa-command-reference/S/cmdref3/s4.html#pgfId-1437635
What is flowing through the ASA
CLINet-ASA(config)# show conn all
flags UfIOB TCP outside:10.10.10.10/1965 (10.10.10.10/1965) inside:192.168.55.172/4567
(10.10.10.111/4567), flags UfIOB, idle 52m38s, uptime 54m21s, timeout 1h0m, bytes 3063
flags UfIOB TCP outside:10.10.10.201/1485 (10.10.10.201/1485) inside:192.168.55.172/4567
(10.10.10.111/4567), flags UfIOB, idle 41m38s, uptime 43m12s, timeout 1h0m, bytes 3063
flags UB TCP outside:192.168.22.195/16208 (192.168.22.195/16208) inside:192.168.55.172/4567
(10.10.10.111/4567), flags UB, idle 45m6s, uptime 48m17s, timeout 1h0m, bytes 0
flags UB TCP outside:172.16.45.22/24654 (172.16.45.22/24654) inside:192.168.55.172/4567
(10.10.10.111/4567), flags UB, idle 45m54s, uptime 49m4s, timeout 1h0m, bytes 0
CLINet-ASA(config)#
48

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Connection Table via ASDM Monitoring > Properties > Connections
49

Other Cisco Firewalls

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
IOS Zone Based FW
• IOS Zone Based FW offers intuitive policies for multiple-interface routers, increased granularity of firewall policy application, and a default deny-all policy
• Traffic between firewall security zones is prohibited until an explicit policy is applied to allow desirable traffic
• Interfaces are assigned to zones, and inspection policy is applied to traffic moving between the zones
• Inter-zone policies offer considerable flexibility and granularity, so different inspection policies can be applied to multiple host groups connected to the same router interface.
The Other Firewall (IOS)
51

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Meraki MX
• Meraki MX cloud managed security appliance automatically pulls policies and configuration from the cloud
– enabling branch deployments without on-site IT
• The Meraki cloud delivers seamless firmware and security signature updates, automatically establishes site-to-site VPN tunnels, and provides automatic network monitoring and alerts.
• Since the MX is managed entirely through the Cisco Meraki web-based dashboard, configuration and diagnostics can be performed remotely just as easily as they can be performed on-site, eliminating costly field visits.
– Even firmware updates are performed seamlessly, over the web.
Cisco Cloud Managed Security Applicance
52

Conclusion

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Firewalls
• Firewalls are the core component for defense from the threats to network security
• The firewall often is the conduit from which other defense components combat the threat that face the network
• Next-Generation Security such as NGFW and NGIPS require a rock solid stateful inspection firewall at their foundation
54

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Follow on Sessions
• BRKSEC-2020
– Firewall Deployment – Mike Storm
• BRKSEC-2023
– Firewall Architectures – Mason Harris
• BRKSEC-2024
– Deploying Next-Generation Firewall Services on the ASA - Kureli Sankar
• BRKSEC-3020
– Troubleshooting Firewalls – Jay Johnston
• BRKSEC-3021
– Maximizing Firewall Performance – Andrew Ossipov
55

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Participate in the “My Favorite Speaker” Contest
• Promote your favorite speaker through Twitter and you could win $200 of Cisco Press products (@CiscoPress)
• Send a tweet and include
– Your favorite speaker’s Twitter handle @StreetCCIESec
– Two hashtags: #CLUS #MyFavoriteSpeaker
• You can submit an entry for more than one of your “favorite” speakers
• Don’t forget to follow @CiscoLive and @CiscoPress
• View the official rules at http://bit.ly/CLUSwin
Promote Your Favorite Speaker and You Could be a Winner
56

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Complete Your Online Session Evaluation
• Give us your feedback and you could win fabulous prizes. Winners announced daily.
• Complete your session evaluation through the Cisco Live mobile app or visit one of the interactive kiosks located throughout the convention center.
Don’t forget: Cisco Live sessions will be available for viewing on-demand after the event at CiscoLive.com/Online
57

© 2014 Cisco and/or its affiliates. All rights reserved. BRKSEC-1020 Cisco Public
Continue Your Education
• Demos in the Cisco Campus
• Walk-in Self-Paced Labs
• Table Topics
• Meet the Engineer 1:1 meetings
58