Cambridge Technicals Level 3 in IT U01 Lesson Element 2€¦ · Web viewLO5: Understand ethical...
Transcript of Cambridge Technicals Level 3 in IT U01 Lesson Element 2€¦ · Web viewLO5: Understand ethical...

Lesson Element
Unit 1: Fundamentals of IT
LO5: Understand ethical and operational issues and threats to computer systems
Threats and digital security
Instructions and answers for tutors
These instructions cover the learner activity section which can be found on page 12. This Lesson Element supports Cambridge Technicals Level 3 in IT.
When distributing the activity section to the learners either as a printed copy or as a Word file you will need to remove the tutor instructions section.
The activityThis lesson element will provide learners with an opportunity to identify threats to computer systems. They will look at physical and digital security methods and justify which methods are essential to use.
Suggested timingsActivities 1, 2 and 3: 30 minutes
Activities 4, 5 and 6: 30 minutes
Version 1 1 © OCR 2016
WORK – This activity offers an opportunity for work experience.
ABC – This activity offers an opportunity for English skills development.

Activity 1Tutors should print out and cut up the images and keyword cards from the Threats Memory Game below. Tutors spread out the cards, face down, on a table in front of the learners keeping the image and keyword cards separate. Card by card the learners turn over an image card and try and match it to its keyword card. If there is no match then both cards are returned face down to their original positions. The process is repeated until all images and threats are correctly identified.
Version 1 2 © OCR 2016

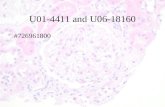
Threats Memory Game
PHISHING
HACKING
VIRUS
TROJAN
Version 1 3 © OCR 2016

INTERCEPTION
EAVESDROPPING
DATA THEFT
SOCIAL ENGINEERING
Version 1 4 © OCR 2016

Activity 2Tutors should ask learners to define the different types of threats. Learners can check their understanding using the web page: http://www.itscolumn.com/2012/03/28-types-of-computer-security-threats-and-risks/.
Learners can also extend their learning by reading and discussing further threats listed on the web page.
Activity 3Tutors should print and cut up the images and keyword cards from the Security Memory Game below. Tutors spread out the cards face down on a table in front of the learners, keeping the image and keyword cards separate. Card by card the learners turn over an image card and try and match it to its security method card. If there is no match then both cards are returned, face down, to their original positions. The process is repeated until all images and security methods are correctly identified.
Version 1 5 © OCR 2016

Security Memory Game
LOCKS
BIOMETRICS
RFID
TOKENS
Version 1 6 © OCR 2016

PRIVACY FILTER
SHREDDING
ANTI-VIRUS
FIREWALL
Version 1 7 © OCR 2016

ANTI-SPYWARE
USERNAMEPASSWORD
PERMISSIONS
ENCRYPTION
Version 1 8 © OCR 2016

Activity 4Tutors should ask learners to organise the identified security methods into two groups: Physical security and digital security.
Expected resultsPhysical security Digital security Locks
Biometrics
RFID
Tokens
Privacy filters
Shredding
Anti-virus
Firewalls
Anti-spyware
Username/password
Permissions
Encryption
Activity 5Tutors should ask learners to give justified reasons for security methods (identified in Activity 3) they would use to combat the threats that they have identified. This could be done as a class discussion, paired work or individually using the table provided in the learner activity.
Version 1 9 © OCR 2016

Example answersThreat Security JustificationPhishing Anti-spyware
Privacy filters
Anti-spyware will prevent unknown applications stealing personal information.
Privacy filters will guard against personal information being read by onlookers.
Hacking Firewalls
Biometrics
Firewalls will protect a network or system from unauthorised access.
Biometrics are more secure than usernames/ passwords as they cannot be guessed.
Virus Anti-virus Anti-virus software will detect and protect against known computer viruses. The anti-virus software must remain up-to-date to provide protection.
Trojan Anti-virus A Trojan is a computer invasion also protected against by anti-virus software. The anti-virus software must remain up to date to provide protection.
Interception Encryption
Shredding
Encryption will prevent access to the data as a decryption key is required.
Shredding prevents unauthorised access to data no longer required.
Eavesdropping Encryption
Locks
Encryption will prevent access to the data as a decryption key is required.
Locks, securely locked doors will prevent public (visitors) use.
Data theft Encryption
Tokens
RFID
Encryption will prevent access to the data as a decryption key is required.
Tokens will only allow people with the token access to the data.
RFID will only allow people with RFID access to secure areas.
Social engineering
Username/passwordBiometrics RFID
Prevent a social engineering attack by using a combination of security methods in order to prevent an attacker persuading a victim to give out all security details.
Version 1 10 © OCR 2016

Activity 6Tutors ask learners to share one threat they have identified, and their justified reasons for using a particular security method, with the rest of the group. Tutors ask the group to vote on whether they agree or disagree with the learner’s decisions. If the group disagrees, the tutor sets up a discussion group to identify alternative methods.
Version 1 11 © OCR 2016
We’d like to know your view on the resources we produce. By clicking on ‘Like’ or ‘Dislike’ you can help us to ensure that our resources work for you. When the email template pops up please add additional comments if you wish and then just click ‘Send’. Thank you.
If you do not currently offer this OCR qualification but would like to do so, please complete the Expression of Interest Form which can be found here: www.ocr.org.uk/expression-of-interest

Version 1 12 © OCR 2016
OCR Resources: the small print
OCR’s resources are provided to support the teaching of OCR specifications, but in no way constitute an endorsed teaching method that is required by the
Board, and the decision to use them lies with the individual teacher. Whilst every effort is made to ensure the accuracy of the content, OCR cannot be held
responsible for any errors or omissions within these resources.
© OCR 2016 – This resource may be freely copied and distributed, as long as the OCR logo and this message remain intact and OCR is acknowledged as the
originator of this work.
OCR acknowledges the use of the following content: Activity 1: 73319470 Lightspring; 81825655 gualtiero boffi; 131448572 Steve Heap; 177250427 tanuha2001;
223094779 wk1003mike; 246319285 Wichy; 248596792 wk1003mike; 258903893 Creativa Images. Activity 3: 9650737 Lou Oates; 9650737 watcharakun;
34835914_Kairos; 42943528 Angela Waye; 47557069 Vladru; 106052978_JMiks; 106865984 Lost Mountain Studio; 136874459 Franck Boston; 211081186
LovePHY; 244816201 kentoh; 279374651_Marcos Mesa Sam Wordley; 285401465 Black Jack. All images courtesy of shutterstock.comPlease get in touch if you want to discuss the accessibility of resources we offer to support delivery of our qualifications: [email protected]

Lesson Element
Unit 1: Fundamentals of IT
LO5: Understand ethical and operational issues and threats to computer systems
Learner ActivityThreats and digital securityThis lesson element will provide you with an opportunity to identify threats to computer systems. You will also look at physical and digital security methods and justify which methods are essential to use.
Activity 1You will be given a number of cards face down. Do not turn them over and look at them until asked to do so. Each player in turn chooses and turns over one card from the image group and then one card from the keywords group. The aim is to match the image card with its keyword card. If there is no match return both cards face down to their original positions. Repeat the process until all images and threats are correctly identified.
Activity 2Write a definition for each of the different types of threats. You can check your understanding using the web page: http://www.itscolumn.com/2012/03/28-types-of-computer-security-threats-and-risks/.
You can also extend your learning by reading and discussing further threats listed on the web page.
Activity 3You will be given a number of cards face down. Do not turn them over and look at them. Spread out the cards face down on the table. Each player in turn chooses one card and turns it over, then chooses another card and turns it over. The aim is to match each image card with its security method card. If there is no match return both cards face down to their
Version 1 13 © OCR 2016

original positions. Repeat the process until all images and security methods are correctly identified.
Activity 4Organise the identified security methods into two groups, Physical Security and Digital Security. Write your results in the table below.
Anti-spywareAnti-virusBiometricsEncryptionFirewallsLocksPermissionsPrivacy filtersRFIDShreddingTokensUsername/password
Physical security Digital security
Version 1 14 © OCR 2016

Activity 5For each threat you have identified in Activity 3, give justifiable reasons for the security methods you would use to prevent or combat the threat. You can use the table provided below to note your answers. The web page https://www.getsafeonline.org/ may also be of assistance with your justifications.
Threats and securityThreat Security JustificationPhishing
Hacking
Virus
Trojan
Interception
Eavesdropping
Data theft
Social engineering
Activity 6Share one threat you have identified and justify your reasons to the rest of the class.
Version 1 15 © OCR 2016