5 ways to stop your business from being hacked
-
Upload
chrisvarnomcom -
Category
Technology
-
view
9 -
download
2
Transcript of 5 ways to stop your business from being hacked

http://chrisvarnom.com/5-ways-that-will-stop-your-business-from-being-hacked/
5 ways that will stop your business from being hacked
Author - Chris Varnom at chrisvarnom.com
To be notified of my latest posts please subscribe to my newsletter and to receive free stuff
at http://chrisvarnom.com/newsletter/
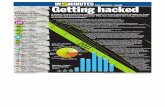
Denial of Service attacks, compromised sites or data breaches being used to distribute
malware will all have a dramatic impact on your business; and more so the small business
sector. In fact, small businesses are more likely to suffer greater consequences as a result of
being hacked than the larger enterprise, which has the financial resources and
organizational technical know-how to bounce back faster.
Ask yourself this question, could your online business survive the website being offline for a
day, two days, a week or even more, your email service not working for days on end or the
reputation and data protection fallout of customer data being compromised? And that doesn’t
even take into account the time – your most precious commodity – wasted, identifying and
resolving the issues.
Unfortunately there’s no 100% guarantee that your business will be hack-free in the
connected world of online business.
However, there are five simple tips that would make life much harder for
the would be hacker...
1. Password management systems
Passwords are at the centre of most businesses security policies, and also the subject of
many successful site compromises.
Larger organizations use expensive password management software solutions to enforce
and manage them, while many consumers are turning to using password 'vaults' to
generate, encrypt/store and access them. Neither of these are solutions for the average
small business, one being too expensive and the other too simplistic.
However, there are alternatives, the enterprise version of LastPass, which is relatively low
cost on a per user basis and also comes with extras, such as the setting of company-wide
minimum password standards to meet your security policy requirements, applying

customized policies to restrict access to specific devices, groups or locations, Active
Directory (AD)/Lightweight Directory Access Protocol (LDAP) integration and real-time
syncing across devices.
2. Two factor authentication is far better than just one
Even with proper management in place, passwords are always still vulnerable to
compromise. For example, if a hacker can get into business email or social media accounts
(by way of social engineering or the use of password resets) then they will likely gain access
to information that will help them hack your business. Put simply, a password alone and
even a complex password is no longer enough and Two Factor Authentication (2FA) or Two
Step Verification should be definitely considered.
With 2FA, if someone tries to access company services from unauthorized devices (that is,
ones that haven’t been used before or haven’t been authorized for continued usage) they
will be asked for a separate authorization code in addition to the typical username/password
login. This can be generated either by a SMS text message sent to a registered smartphone
using an approved code generating app, or, sometimes, with a dedicated hardware token.
2FA is an excellent mitigation against hackers who have got hold of login data from the use
of malware or third party compromises and are trying their luck.
3. Policy matters
Many smaller businesses assume they don’t need a formal security policy and to think that is
totally bonkers, but these documents aren’t just something for enterprises. Even the smallest
SMB will benefit from employing this type of policy, but don’t worry because they are easier
to create and implement than you think. In fact, if done correctly, it will form your overall
security policy.
The security policy should be seen as a mechanism to help you understand what data
security means your business and to form the basis of the structured response to the needs
identified. The best security policy will not only detail how to protect your data, but also how
to react when things go totally pear shaped. Embarking on an incident-response strategy
when you have a clear head is far better than trying to put things right when the proverbial
hits the fan.

4. Education, Education, Education
Social engineering remains a huge threat to large and small businesses and their data
security, whether it’s targeted Trojans or phishing attacks aimed at specific employees,
appearing like a real customer using broad business social-media profiling, or worse still an
attack using a combination of all these methodologies and all of them can be overcome with
employee education.
You must ensure that your staff aren't opening the door to and letting any Tom, Dick or Harry
walk off with your valuable data by teaching them the value that data holds and how security
can be compromised. Once this is understood, staff can mitigate the risk by simply changing
their behaviour. In fact, the smaller the business the easier this is to achieve, as the cost of
maintaining awareness is directly proportionate to the number of staff that you have.
5. Don't forget the simple stuff
The simplest bit of anti-hacking advice to give any small business is to secure your network.
Seriously. It's not something that requires a fully certified geek genius to do.
Ensure you have Business antivirus software installed and make sure that you keep it up to
date, religiously apply operating system and application updates and control who can get at
what data.
The majority of staff don’t need full access to all the data, so apply the “need to know” rule –
if an employee can perform their day to day job without using a certain application or data,
they shouldn’t be given access. The same applies to visitors, do not give them access to the
main network but provide access to a DMZ on the network.
Remember, if you can limit the number of people who have access to your data, you can
successfully limit the opportunity for the bad guys to steal it.