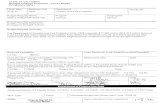
008.itsecurity bcp v1
-
Upload
mohammad-ashfaqur-rahman -
Category
Engineering
-
view
205 -
download
0
Transcript of 008.itsecurity bcp v1

Information System Audit
Presented by
Mohammad Ashfaqur RahmanCompliance Professional
www.linkedin.com/in/ashfaqsaphal

Objective
● Concept of IS / IT Audit● Term and Standard● IT audit process● IT Security Audit

IT Audit
● An information technology audit, or information systems audit, is an examination of the management controls within an Information technology (IT) infrastructure.
– Measure the CIA– systematic, measurable technical assessment on
security policy
Systematic process, independent and documented for obtaining audit evidence and evaluate objectively, in order to establish to what extent are audit criteria met
– ISO 19011

IT Audit● Audit Types (Generic)
– Internal audits (1st party) sponsored by by the organization with the aim of improvement of the ISMS.
– External audit (2nd party) audits carried out by an organisation on its supplier (partners, vendors) using, either internal personnel, or external entity entrusted with doing it.
– Certification audit (3rd party) independent from the organizationwith the aim to release the certificate of conformity with the requirements taken as a audit criteria (ISO 27001).

IT Audit Standard1. Audit charter2. Independence3. Ethics and Standards4. Competence5. Planning6. Performance of audit work7. Reporting8. Follow-up activities9. Irregularities and illegal acts10.IT governance11.Use of risk assessment in audit planning

IT Audit Standard● Audit charter
– Purpose, responsibility, authority and accountability
– Approval● Independence
– Professional independence– Organizational independence
● Professional Ethics and Standards
– Code of Professional Ethics– Due professional care

IT Audit Standard● Competence
– Skills and knowledge– Continuing professional education
● Planning
– Plan IS audit coverage– Develop and document a risk-based audit Approach – Develop and document an audit plan– Develop an audit program and procedures

IT Audit Standard● Performance of audit work
– Supervision– Evidence– Documentation

IT Audit Standard● Reporting
– Identify the organization, intended recipients and any restrictions
– State the scope, objectives, coverage and nature of audit work performed
– State the findings, conclusions and recommendations and limitations
– Justify the results reported– Be signed, dated and distributed according to the
audit charter

IT Audit Standard● Follow-up Activities
– Review previous conclusions and recommendations– Review previous relevant findings– Determine whether appropriate actions have been
taken by management in a timely manner

IT Audit Standard● Irregularities and Illegal Acts
– Consider the risk of irregularities and illegal acts– Maintain an attitude of professional skepticism– Obtain an understanding of the organization and its
environment– Consider unusual or unexpected relationships– Test the appropriateness of internal control– Assess any misstatement

IT Audit Standard● Irregularities and Illegal Acts (Cont.)
– Obtain written representations from management– Have knowledge of any allegations of irregularities
or illegal acts– Communicate material irregularities/illegal acts– Consider appropriate action in case of inability to
continue performing the audit– Document irregularity/illegal act related
communications, planning, results, evaluations and conclusions

IT Audit Standard● IT Governance
– Review and assess the IS function’s alignment with the organization’s mission, vision, values, objectives and strategies.
– Review the IS function’s statement about the performance and assess its achievement
– Review and assess the effectiveness of IS resource and performance management processes

IT Audit Framework● Standards
– Must be followed by IS auditors● Guidelines
– Provide assistance on how to implement the standards
● Procedures
– Provide examples for implementing the standards

IT Audit● IS auditor’s perspectives
– Security (confidentiality, integrity and availability) – Quality (effectiveness, efficiency) – Fiduciary (compliance, reliability) – Service and Capacity

IT Audit Process● Audit planning● Stage 1 audit● Stage 2 audit

IT Audit Process● Audit planning
– define audit objectives– define audit scope– select audit criteria– select sampling method– select audit team– define observers and guides (if necessary)– define resources needed

IT Audit Process● Stage 1 Audit
– Initiation of audit– Auditee’s application (self-assessment document)– Document review– Planning work documents (forms, procedures, etc)– Organisation’s unit and processes to be audited– Estimation of time– Work schedule

IT Audit Process● Another Approach
– Planning– Studying and Evaluating Controls
• Fieldwork and documentation– Issue discovery and issue validation– Solution development– Testing and Evaluating Controls– Report drafting and issuance– Follow up

Example IT Infrastructure Security Audit
● Auditing entity level controls● Auditing Data Centers● Auditing Network Equipment● Operating System Audit● Audit Web Server and Application● Auditing Databases● Auditing Storage

Audit Me